Part 1: Nutanix Xi Frame On-Prem AHV: What Does it Mean to Citrix, VMware and The EUC Community !
Part 2: Deploy & Configure Xi Frame VDI on On-Premises AHV
Part 3: Enhance Nutanix Xi Frame User Experience Domain Settings Optimization On-premises AHV
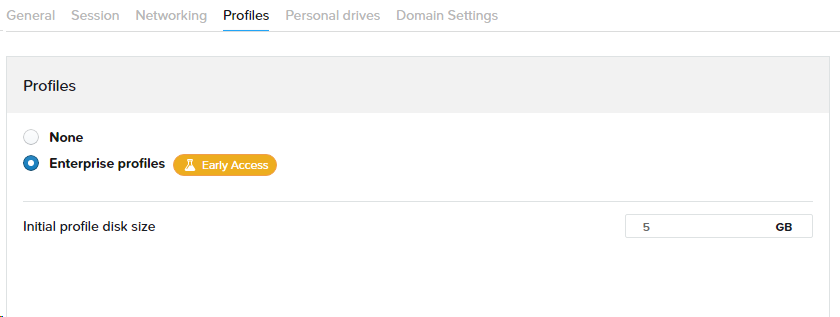
Part 4: Configure Nutanix Xi Frame Enterprise Profiles For VDI On AHV
Part 5: Configure Nutanix Xi Frame Streaming Gateway Appliance for AHV VDI
Introduction
This is a relatively short post on how to optimize the domain login experience for users logging into a domain joined Xi Frame virtual desktop. Xi Frame, as of now, does not support SSO to virtual desktops using domain credentials even when AD ADFS integrated login is configured so the experience is not optimal for end users yet we can optimize it to a certain extent.
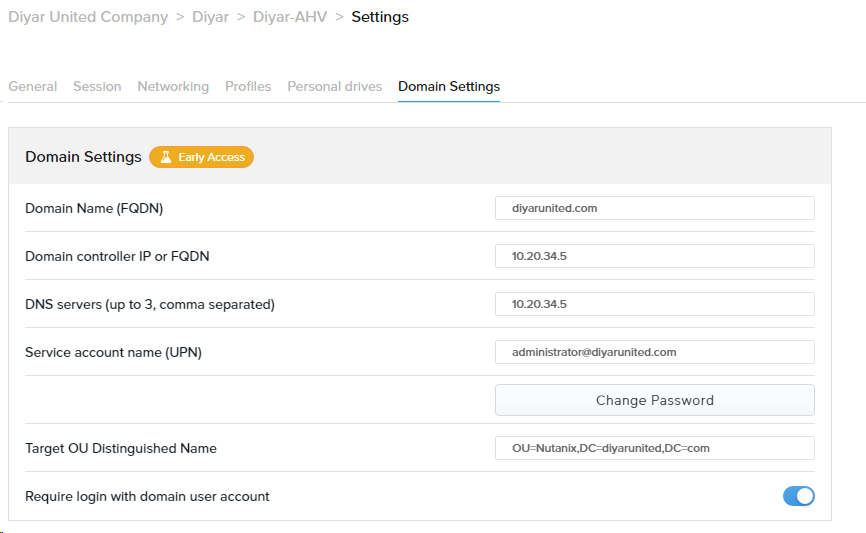
Xi Frame Domain Settings
Without domain settings join configured in Frame account portal settings, Xi Frame uses a local account named “Frame” to login to a virtual desktop or applications session. Now this would not be acceptable at any enterprise organization when thinking of on-premises VDI workloads integration with AHV for security, compliance, audit, management, and operational purposes. Also note that enterprise profiles, also a very important enterprise VDI requirement, which uses a built-in Profileunity agent also requires domain settings to be enabled.
Xi Frame introduced an “Early Access” feature which just means technical preview to join provisioned virtual workloads to a domain. This is a must for any enterprise for obvious reasons and no VDI product would work on the enterprise level without this feature in place. An additional setting within domain integration is require login with domain user account which forces the user to use an AD user account to login rather than default login with “Frame” account. Note here that you cannot set the naming convention for the virtual desktops that join the domain so that is something that needs to be added.
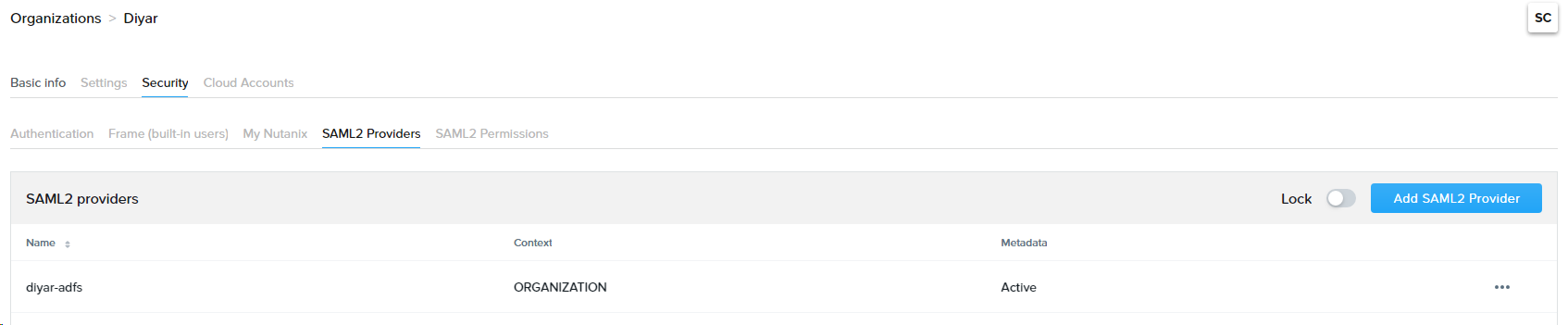
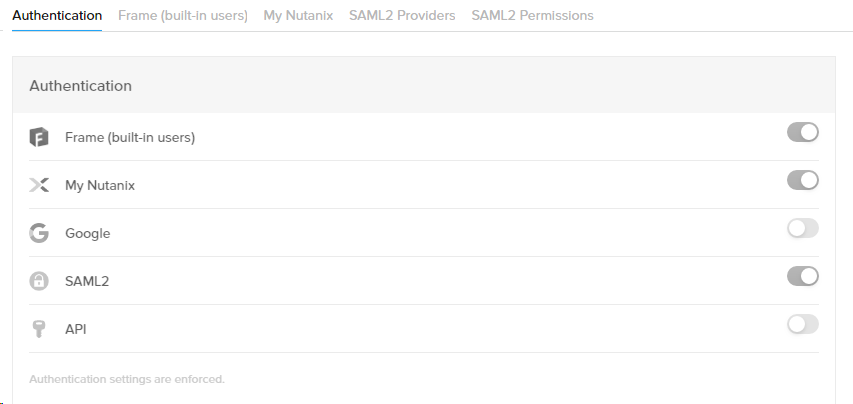
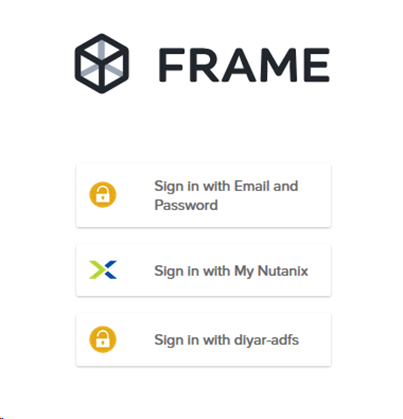
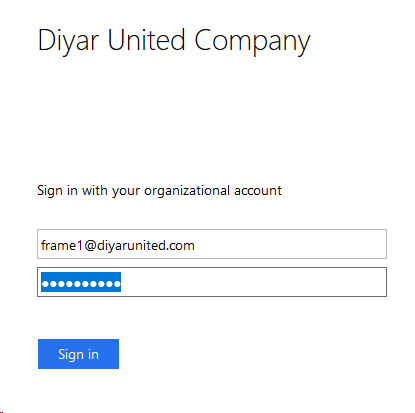
There are multiple ways that a user can login into Xi Frame portal to access virtual desktops and applications so SSO to virtual desktops not being supported is understandable but even with AD ADFS SAML integration which forces the use to login through the ADFS portal and back to the Frame portal, still the user will have to enter the AD credentials again to login to the session when the “require login with domain user account” setting is enabled. To facilitate SSO, which is a must in my opinion going forward, Nutanix Xi Frame team will need to come up with something like Citrix FAS which would use certificates to facilitate the same.
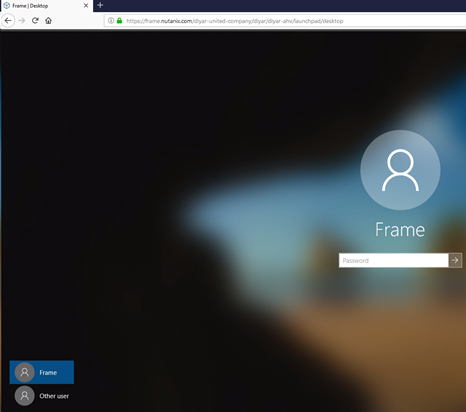
Out-Of-The-Box Login Experience
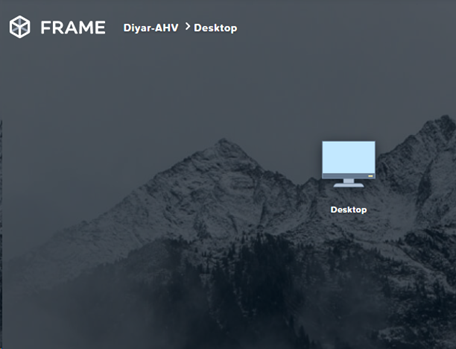
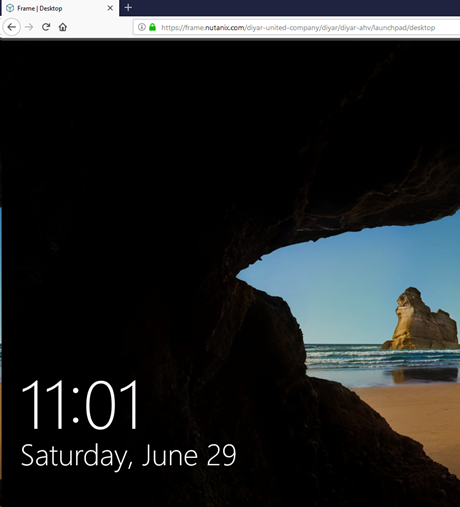
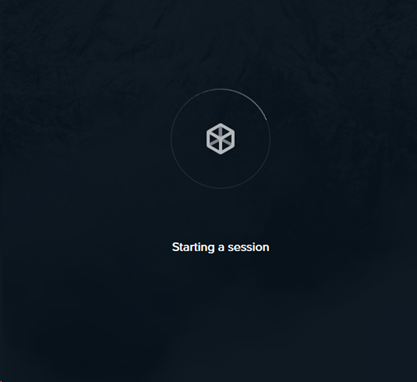
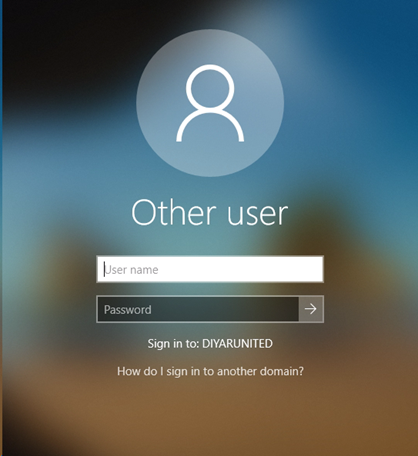
The thing here is that when users are forced to login with their AD credentials and the setting is set in the Domain setting tab, the login experience is really bad because the user has to do at least three manual clicks to reach the point where he/her would have to re-enter their AD credentials which is to begin with an annoying task. The login sequence looks something like this out of the box when AD settings are configured as discussed above:
So the user has to login using his/her AD credentials to ADFS first then click on the desired virtual desktop after which they are represented with the Windows 10 lock screen, clicking any mouse or space click would take the user to the login page which shows the default “Frame” account normally used for login, after which the user has to click on the Other User tab then proceed with logging in with his/her credentials. Now if you have had any experience with VDI and end-users, you know for a fact that this is out of the question and a nightmare to be implemented in production.
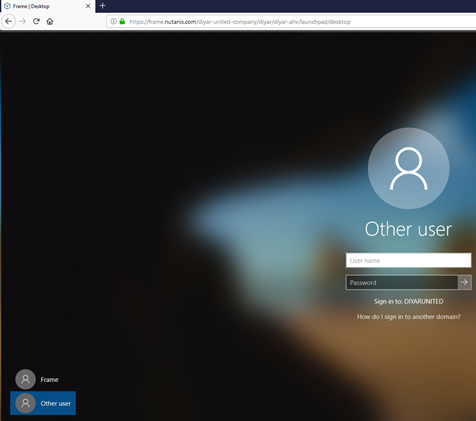
Login Optimization
Fortunately there is a workaround that can help us in facilitating a better user experience in which the user is directly presented with the login box when the virtual desktop is started. This is the best we can do until Xi Frame figure out a way to support SSO. Create a new group policy applied to the OU in which the Frame virtual desktop computer accounts are created and configure the following policies:
Interactive logon: Do not display last user name Enabled
Interactive logon: Do not require CTRL+ALT+DEL Enabled
Do not display the lock screen Enabled
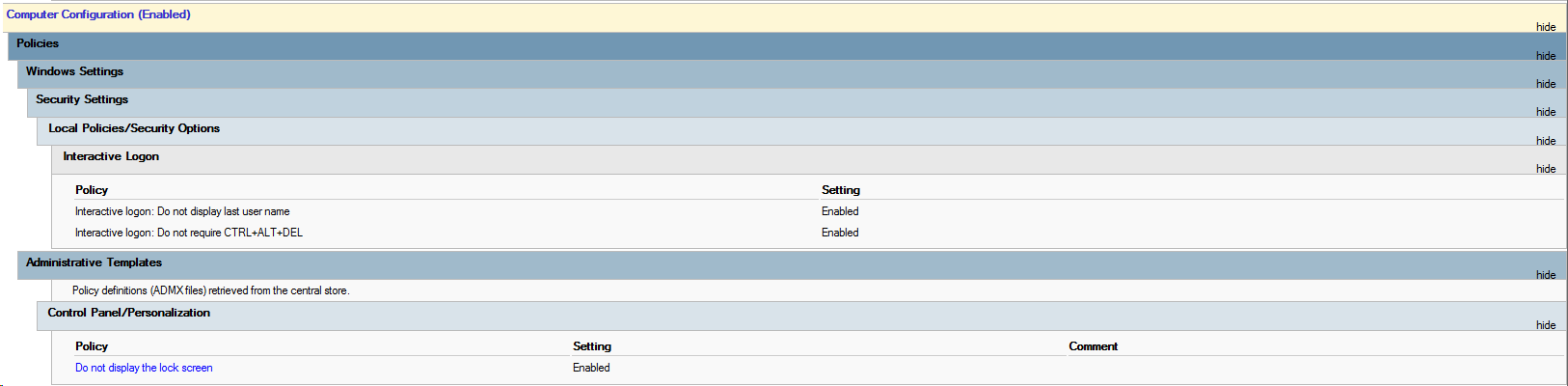
Optimized Login Experience
Doing so would render the user experience usable the least to say and does not require more interaction for the end-user except entering their domain credentials again, the login sequence would look something like this:
Conclusion
This is the best login experience we can get for now until SSO is figured out. Next up I will be exploring the Secure Gateway Appliance and remote connectivity to Xi Frame on-premises AHV deployed virtual desktops.
Part 1: Nutanix Xi Frame On-Prem AHV: What Does it Mean to Citrix, VMware and The EUC Community !
Part 2: Deploy & Configure Xi Frame VDI on On-Premises AHV
Part 3: Enhance Nutanix Xi Frame User Experience Domain Settings Optimization On-premises AHV
Part 4: Configure Nutanix Xi Frame Enterprise Profiles For VDI On AHV
Part 5: Configure Nutanix Xi Frame Streaming Gateway Appliance for AHV VDI
May the Peace, Mercy, and Blessing of God Be Upon You

1) Can we use ARCHICAD, AUTOCAD, SKETCHUP, 3DMAX, RHINO, GIS or any other software? Any special/ free offer for COVID period
2) Do you provide or we have to install?
3) Do you install them or we install remotely?
4) Can you support students of a class size of 50 at a time?
5) any spec of laptop or PC will work at the client end?
6) any specific band width needed?
Yes graphics intensive applications are supported and you install the applications on either your own cloud or a cloud environment provided by Frame in which you pay for the compute charge. Yes you can support 50 concurrent users and any client with a browser would work. Bandwidth depends on the application being used.