Part 1: Nutanix Xi Frame On-Prem AHV: What Does it Mean to Citrix, VMware and The EUC Community !
Part 2: Deploy & Configure Xi Frame VDI on On-Premises AHV
Part 3: Enhance Nutanix Xi Frame User Experience Domain Settings Optimization On-premises AHV
Part 4: Configure Nutanix Xi Frame Enterprise Profiles For VDI On AHV
Part 5: Configure Nutanix Xi Frame Streaming Gateway Appliance for AHV VDI
Introduction:
The acquisition of Frame by Nutanix last year marked a new era for the company on its journey to become an enterprise cloud platform provider rather continue being labeled as an HCI company. Nutanix CEO Dheeraj Pandey has made it very clear that Nutanix Xi Frame needs to be multi-platform and “ Frame is going to run everywhere ” unlike VMware Horizon which only runs on vSphere platform. IMHO, it is not about the technology per se, Nutanix is building a full stack that would allow it to tackle all kinds of existing VMware products thus opening their target customer base to those that not only have vSphere and vSAN (Nutanix AHV and SDS) but rather use Horizon, NSX, and HCX as well (Nutanix Frame, Flow, and Beam) …
Frame, originally being a pure Desktop as a Service (DaaS) offering that supports public cloud service providers on hosting platforms such as Azure and AWS for running its virtual apps and desktops workloads, now supports Nutanix AHV on-premises thus making Xi Frame a hybrid VDI solution as announced in Nutanix .NEXT 2019. The control plane still lives in the cloud and maintained by Nutanix Xi Frame but the virtual workloads can now be hosted on-premises utilizing Nutanix AHV hypervisor as of now with plans of supporting more hypervisor platforms such as vSphere and Hyper-V in the future.
Politics aside, ever since the support announcement for Frame on on-premises AHV, I have been contemplating how to benchmark performance metrics for Nutanix Xi Frame running on AHV and Citrix Cloud running on AHV both using the same hosting infrastructure variables in an effort to produce a legit comparison. The reason behind this was that I wanted to find out how would Frame Remoting Protocol (FRP) stand against the current VDI protocol champion Citrix Independent Computing Architecture Protocol (ICA) with all its HDX goodies. This is a discussion that is going to rage in the coming months once Xi Frame release their agent and start supporting more on-premises use-cases and features that are currently missing, on top of so much is known about ICA but little is known about FRP.
VDI is all about the protocol, VDI is all about the protocol, and VDI is all about the protocol. This is why I haven’t actually taken the time to test Microsoft coming Windows Virtual Desktop offering (WVD). I am a big fan of RDP having done the first ever production RDS 2012 deployment for a major bank in the region back in my days with Microsoft Consulting but instead of making a big fuss on what WVD can or cannot do from a control and hosting plane, let us know what has been done with the protocol that makes WVD such an interesting offering. Anyhow, I have been meddling around with Xi Frame for the last couple of weeks and I thought its best to start with this blog on how to setup the whole Xi Frame with on-premises AHV environment until I get my benchmarking tests started.
Xi Frame On-Premises
Before starting, let me give a huge shoutout to Xi Frame former CTO and current Technologist Rubin for taking the time to discuss the same and giving some great benchmarking tips and advise. A big thanks also to the Frame team for being such sports on my earlier post and providing the free trial. Last but not least to Frame support for working with me on some obstacles faced during the setting up of the infrastructure and the trial of some Early Access features.
Nutanix Xi Frame was originally designed to work in the cloud utilizing only a compatible browser thus an installable agent was not needed. Many of Frame hosted virtual apps involved graphic intensive applications and all was hosted either on the customer managed cloud or Frame managed cloud both of which hosted on either Amazon AWS or Microsoft Azure. On-premises enterprise VDI is a whole different ball game since local device support, most of which is still USB, is still a core requirement knowing that browser based virtual apps or desktops cannot redirect USB. Another thing for enterprises at minimum is domain-join ( Early Access Feature on Frame currently) and strict security controls for virtual desktops that production users will operate from different departments. Lastly other stuff to consider is thin/zero client support from different vendors which is a big deal on top of support for Skype/Teams and offloading, all of which are enterprise requirements for on-premises.
The reason Xi Frame utilizes the concept of Customers, Organizations, and Accounts is that it was built as a cloud native solution so multi-tenancy is in its DNA. Elastic scaling is another cloud native concept that is built into Xi Frame and can be utilized with on-premises AHV as well. Note that users access their LaunchPad to open virtual apps and desktops using a Frame provided URL, this URL cannot be used with a CNAME since it has multiple sub URLs such as the organization URL name and the Accounts URL name. You can configure a redirect from your own subdomain but it would give an SSL error since the certificate name does not match the provided Frame URL…
This is why Xi Frame team is building an agent which would allow device redirection functionality on top of many other features to support enterprise on-premises VDI. Xi Frame also has another early access feature for profile management incorporated into their current agent which utilizes Liquidware ProfileUnity profile management solution (Utilizes disk-based container technology rather than shared folders profile). To enable this feature, the domain-join needs to be enabled as well as a prerequisite.
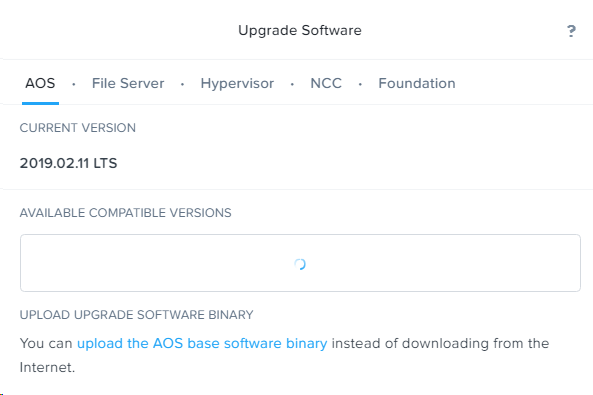
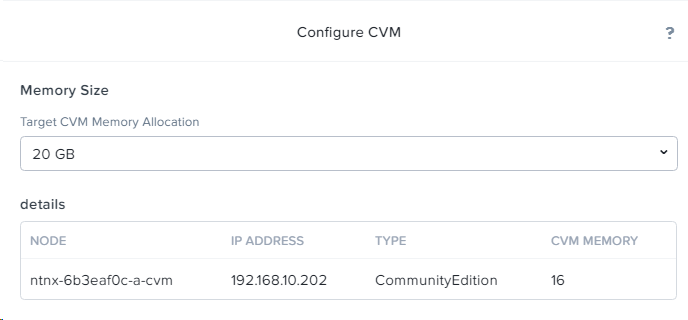
Before starting, I would highly recommend reading the FAQ for Xi Frame on AHV which covers a lot of the most asked questions found here Frame on Nutanix AHV. In a nutshell, as with other VDI vendors that offer cloud based control plane, a minimum of two cloud connectors (CCA) need to be deployed and scaled-up/out based on the size and performance for the VDI environment. For external access, outside the routed network of the virtual workloads, Frame Gateway Streaming Appliance (SGA) needs to be deployed as well. The AHV needs to be an AOS 5.10 or newer and Prism Central is a core requirement for integration with version 5.10 and newer as well. with 5.10, the CCA’s need to be deployed manually while with 5.11 and above, they would be deployed from Prism directly (just like Citrix Cloud Connectors is integrated in Prism). Xi Frame can be integrated with Nutanix CE version 2019.02.11 LTS or newer.
Current supported operating systems for virtual apps and desktops on AHV are Windows 10, Windows Server 2016 and Windows Server 2019 (EA) with Linux support coming soon. Both CCA’s and virtual workload VMs will require outbound secure WebSockets 443 to Frame control plane . The only requirement on the master base image is the Frame agent installation. Sizing virtual desktops is similar to sizing a Horizon infrastructure as per Nutanix !!! so for non-persistent virtual desktops you would need around 15GB of Write Cache per VM in terms of disk and CPU/RAM depends on your sizing. That been said, I haven’t seen any reference disks or identity disks in the created virtual desktops, only the base disk which is in full capacity thin provisioned , so I am not sure if dedup/compression are disabled, how disk sizing would fit accordingly.
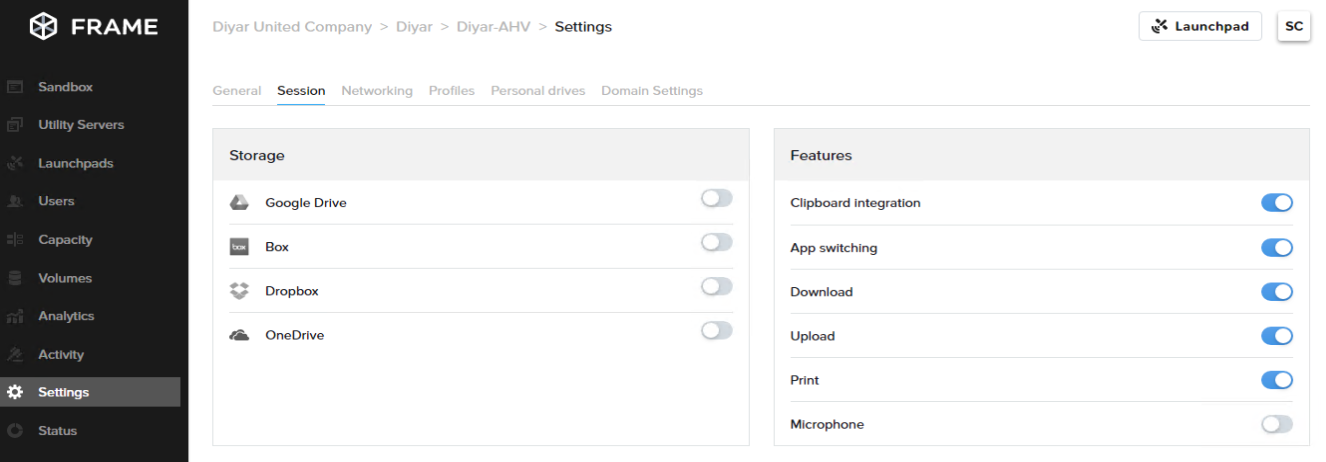
Xi Frame control plane is cloud based so provisioning, entitlements, and settings are all managed from a Frame provided portal online which no other option to run on-premises. The service has many authentication options and can integrate with Active Directory using ADFS SAML integration (Just note without domain join, it would still use the Frame account rather than the logged in domain user). Frame also has the concept of utility servers which can act as file servers or … but that is not required for on-premises since we have access to build the same but rather required when utilizing workloads on the cloud handled by Frame themselves ( not your own cloud environment for hosting workloads). Another interesting early access feature is personal drives most suited for redirecting cache and other settings that require persistence but is not meant to handle long-term retention of files/folders (Frame already integrated with OneDrive, Dropbox,Box, and Google Drive for long-term retention).
Prerequisites:
-
Nutanix Xi Frame subscription.
-
AHV AOS 5.10 + .
-
Prism Central 5.10 + .
-
2 x Cloud Connector Appliances ( 2 vCPUs and 4GB RAM supports 1000 production users, more CCA’s can be deployed for scale ).
-
2 x Streaming Gateway Appliances ( 2 vCPUs and 4GB RAM ). No information available on load handling in terms of scale but I guess load balancing the same should work fine unless it is stateless so connections are load balanced automatically. Also requires a public IP with NAT and creation of public DNS records. After configuration, contact Frame support to enable remote support from their side as well. Outbound firewall rules port 8112 should be opened from virtual desktops to “ 35.173.64.151, 18.232.236.200, 18.214.119.1 ” .
-
Base Images with Windows 10, Windows Server 2016 and/or Windows Server 2019 (EA).
-
Microsoft AD integrated ADFS if login to Frame portal is required through domain credentials ( not to virtual apps and desktop unless domain join is enabled ).
-
Domain-Join requires LDAP AD integration account ( Domain-Join early access feature).
-
Firewall rules open outbound TCP 443.
Lab Environment:
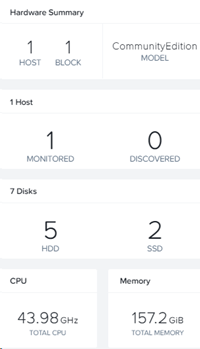
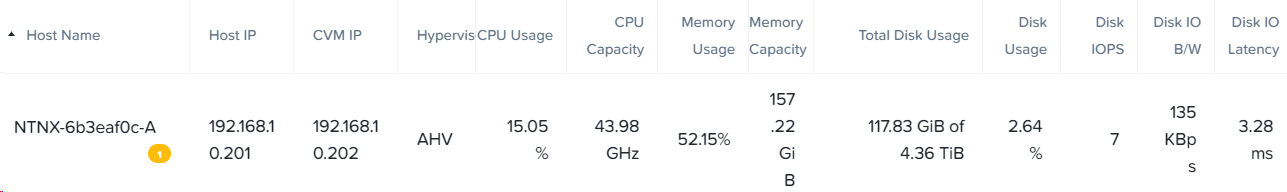
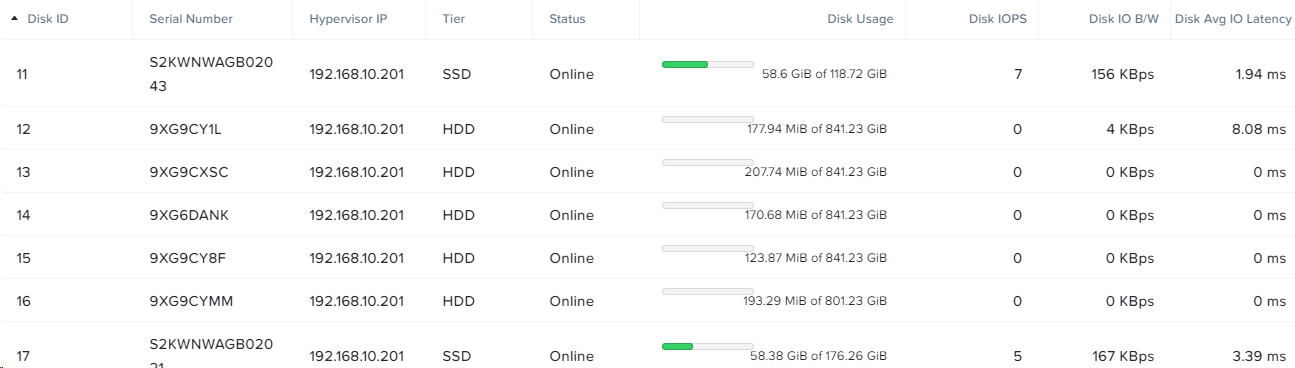
For the sake of this post I have setup Nutanix CE on a single Cisco UCS physical server with the following specs:
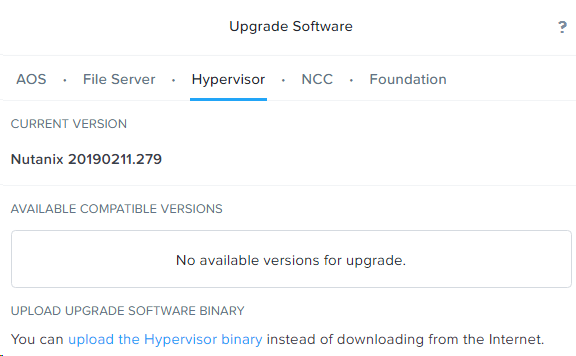
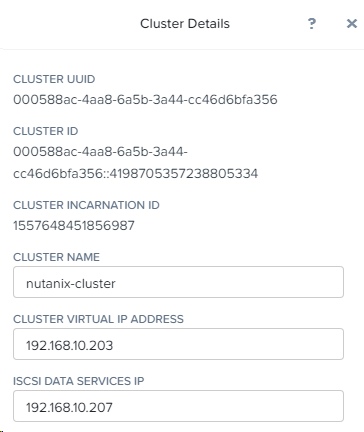
I will provide much more details on the current infrastructure when coming to the benchmarking part in a future post to make all published results reproducible. Note that Nutanix CE versioning is not the same as standard Nutanix versioning but not to worry as the CE 20190211.279 version is compatible with Frame AHV on-premises integration so I assume its the same as the 5.10 version.
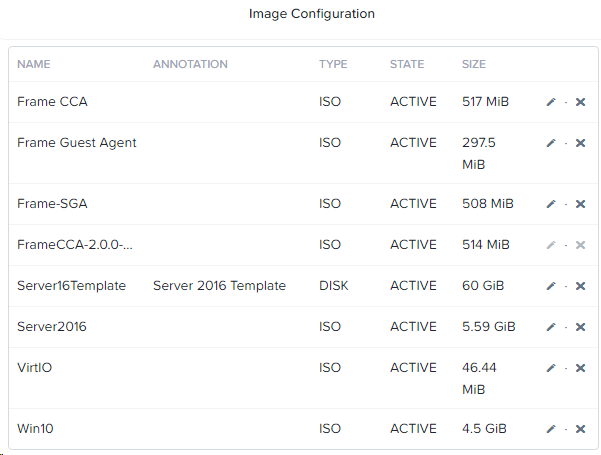
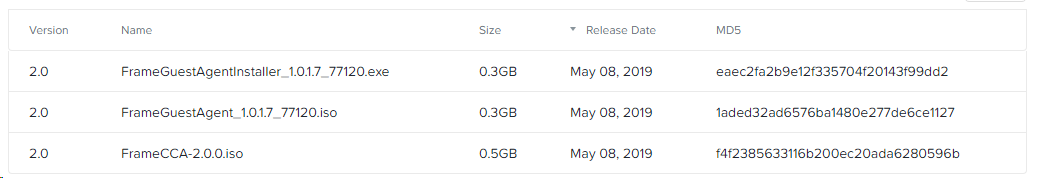
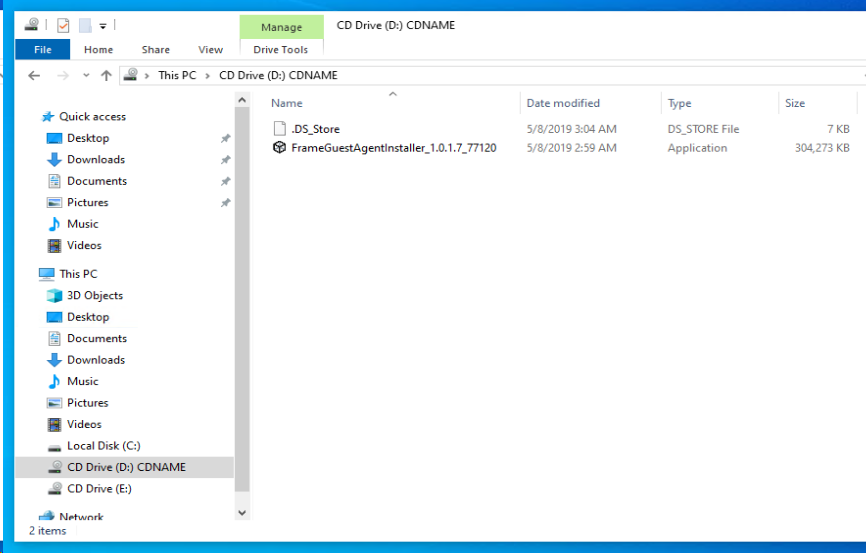
The following software has been added to the image repository on the Nutanix cluster which is required to setup the required infrastructure servers:
The above can be downloaded from My Nutanix Support portal. Just note that the current guest agent available on the portal has a bug with Nutanix AHV CE which would cause provisioning to get stuck and eventually fail so ask support for the guest agent 1.0.1.8 version ( I have the download link but not sure if it can be publicly provided). The SGA as well has a private download link that should be provided by Frame support with the deployment guide.
Configuration:
Lets start by summarizing the deployment steps required for Xi Frame integration with on-premises AHV and detail each step afterwards.
-
Create and Configure Xi Frame CCA’s (Cloud Connector Appliances).
-
Create and Configure the base images (Server 2016 and Windows 10).
-
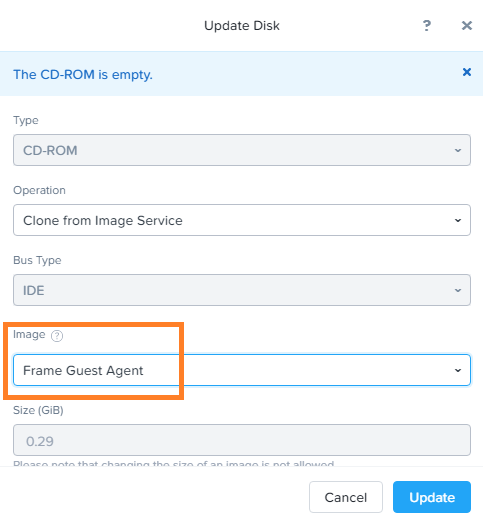
Install Xi Frame Guest Agent on base images.
-
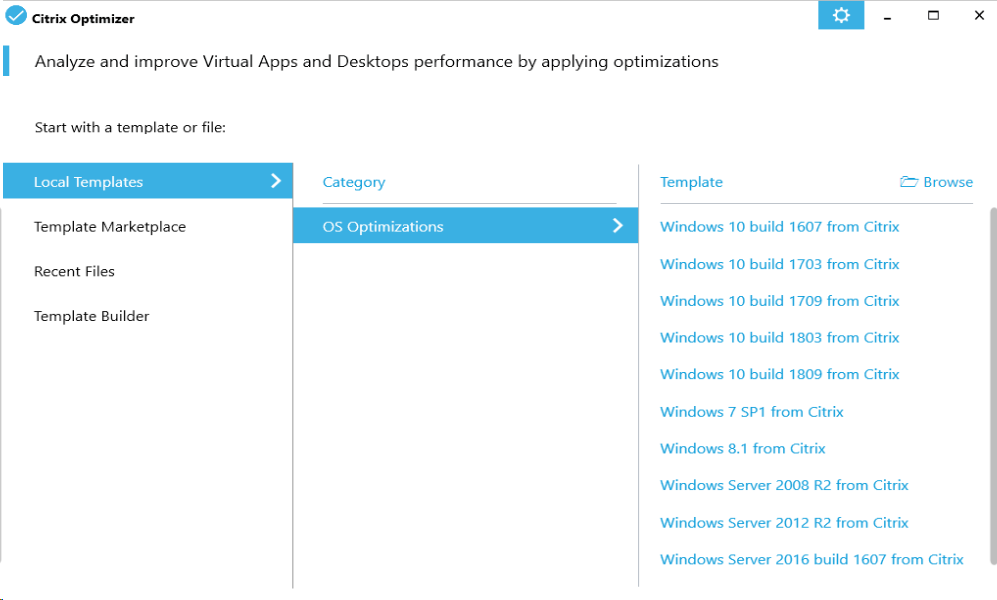
Optimize Base Images and Install required applications.
-
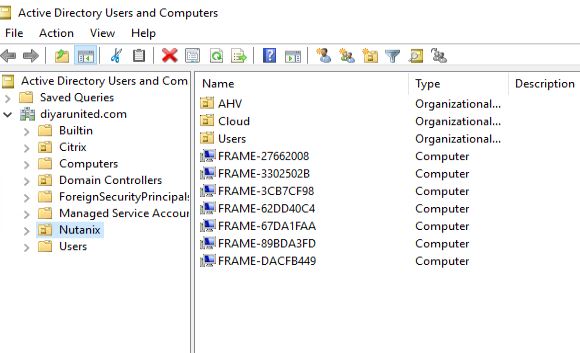
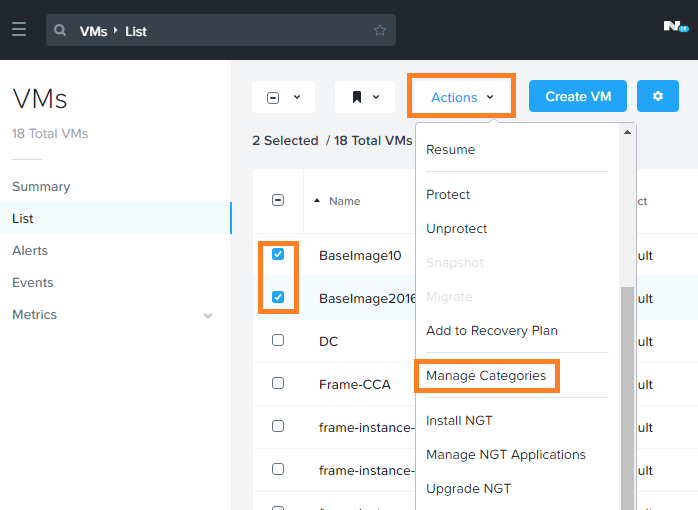
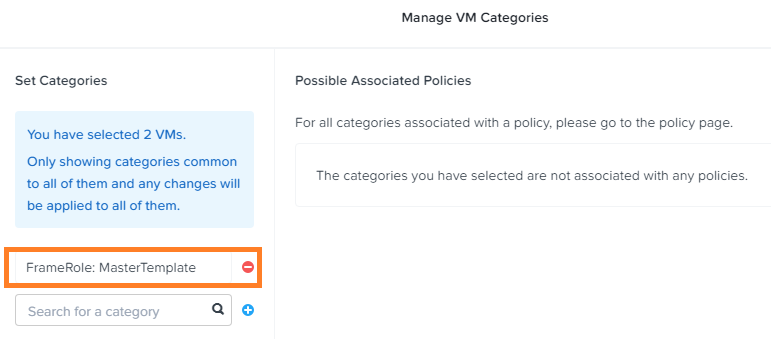
Configure Prism Central Accounts & Categories then add base Images to category FrameRole MasterTemplate.
-
Integrate CCA’s with Nutanix Xi Frame organizations account portal.
-
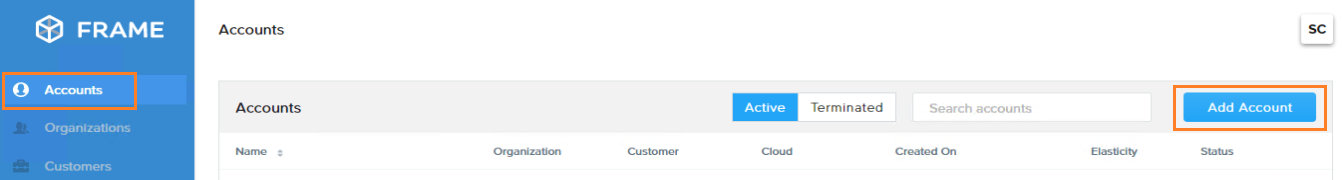
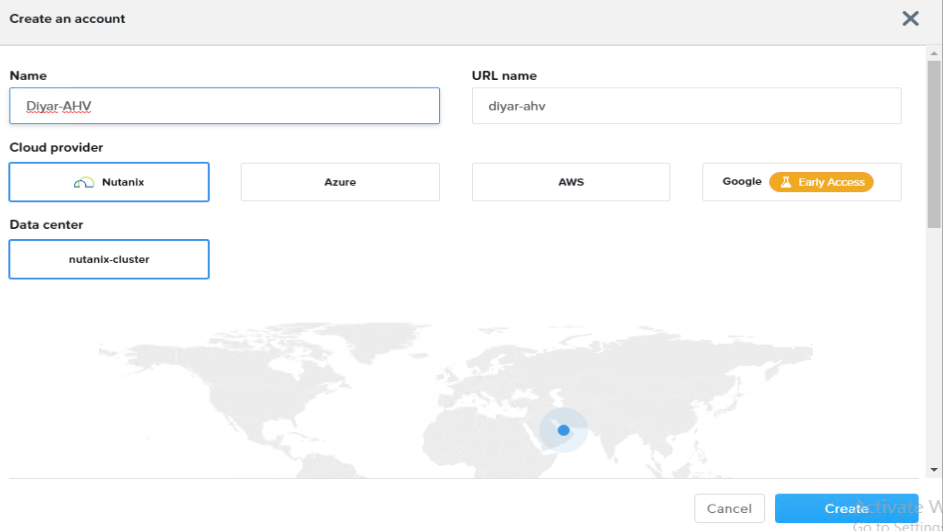
Create an Account with on-premises AHV Nutanix as Cloud Provider.
-
Configure Frame settings and Capacity.
-
Power On sandbox base VM and verify functionality.
-
Publish Sandbox and create launchpads.
-
Configure User Access permissions.
-
Test Virtual Desktops and Apps access internally.
-
Create and Configure Xi Frame SGA(Gateway Streaming Appliance).
-
Test Virtual Desktops and Apps access externally.
Step 1: Create and Configure Xi Frame CCA’s:
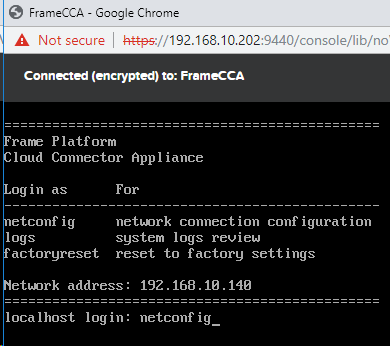
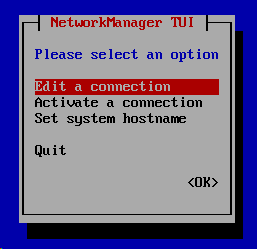
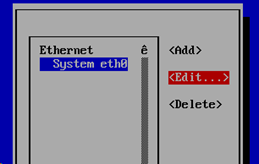
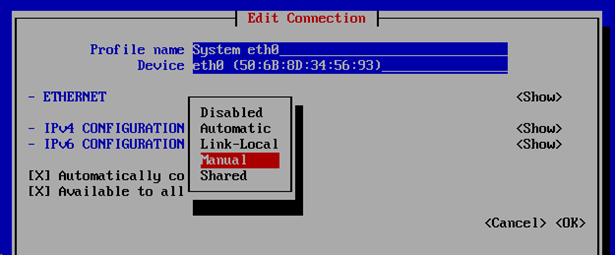
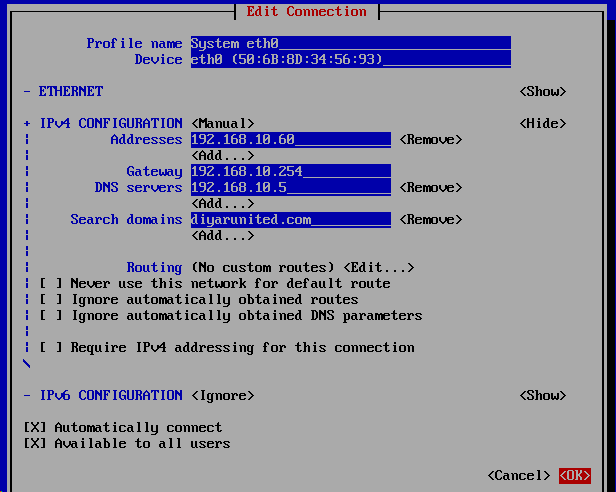
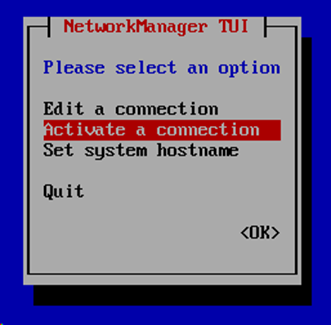
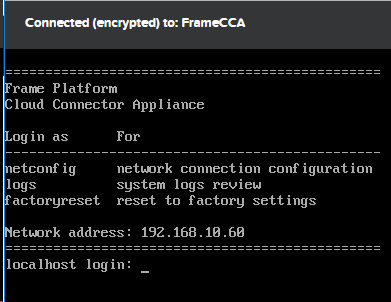
Type netconfig into the localhostlogin of the cloud connector in order to change the DHCP IP into a static IP or just create a reservation on your DHCP and keep everything the same.
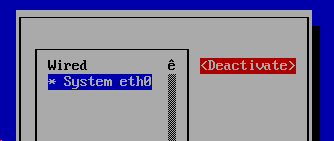
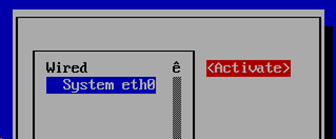
You need to Deactivate then Activate again the network connection for the new manual settings to kick-in.
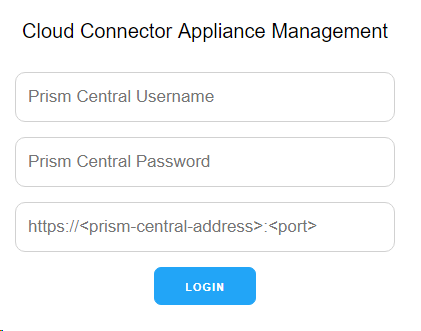
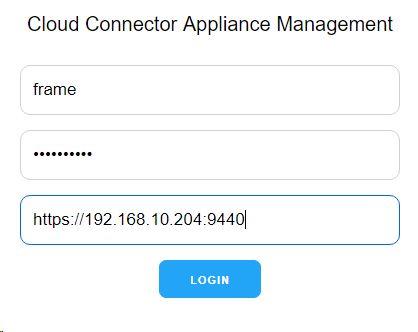
Navigate to https://192.168.10.60 the IP address of the cloud connector and the following screen should be presented. We will continue the CCA configuration in step 5.
Step 2 : Create and Configure the base images (Server 2016 and Windows 10):
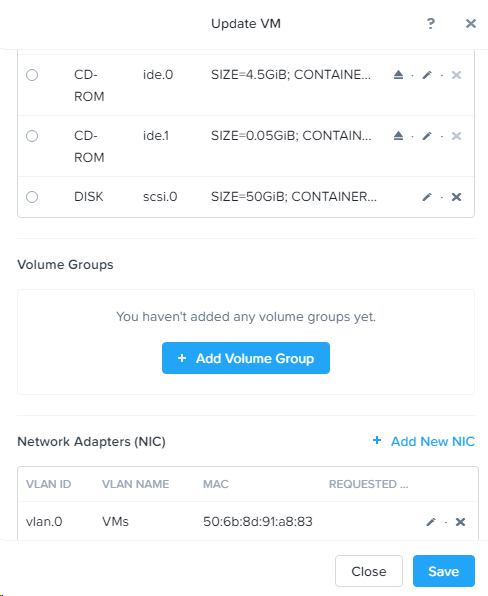
You will need to add an additional CD-ROM to mount the VirtIO tools in order to find the SCSI drives for the disk and install the OS. Remove the secondary CD-ROM once the OS installation is complete and dismount the OS ISO from the CD-ROM as well.
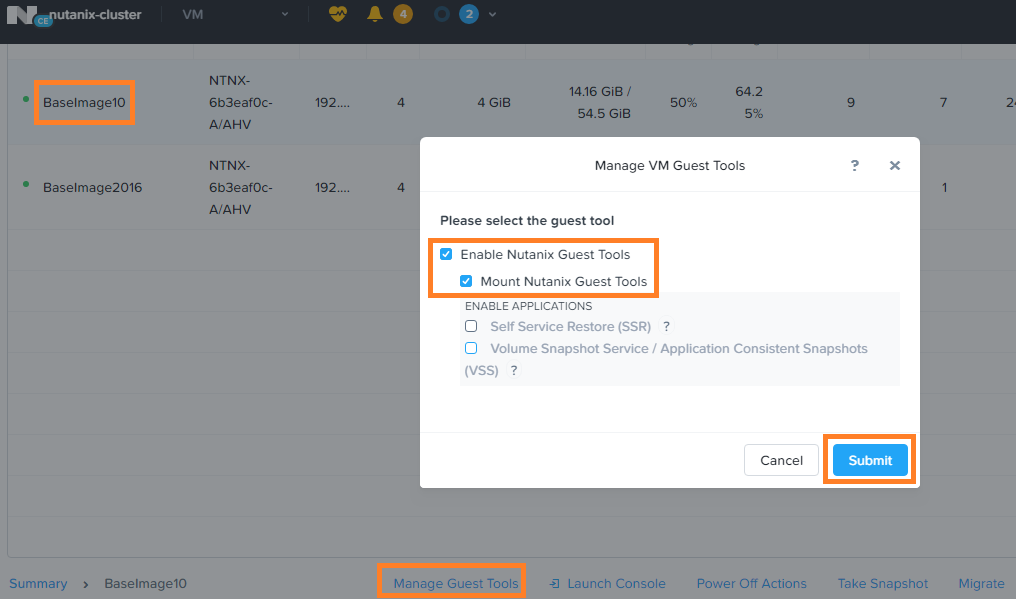
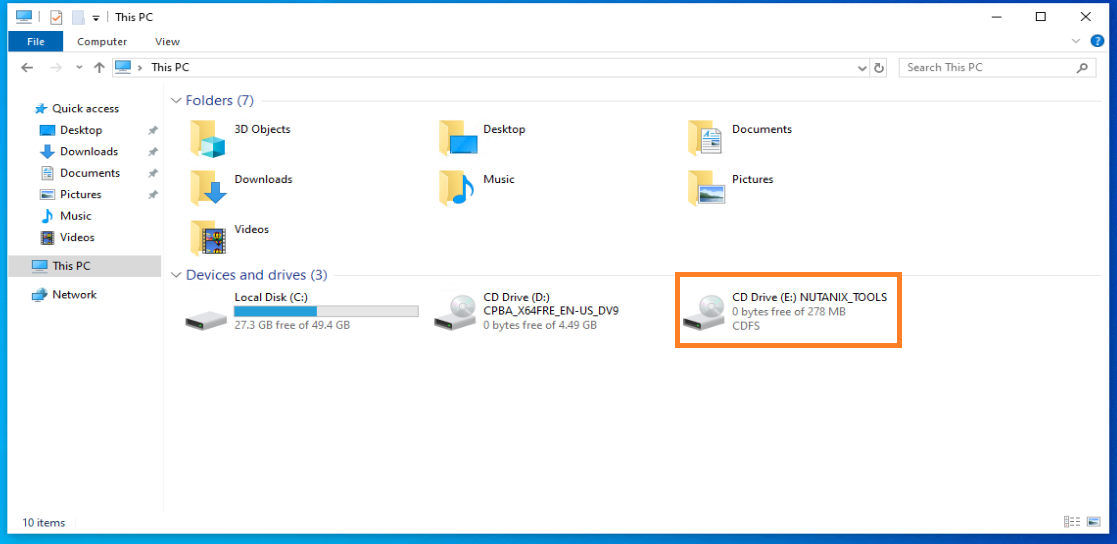
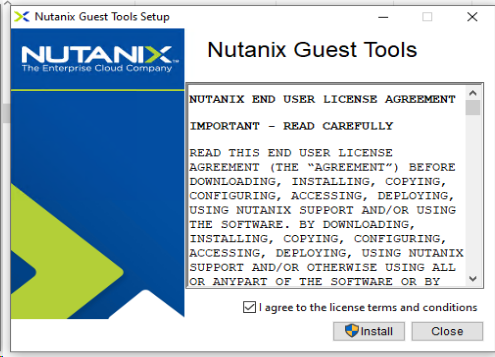
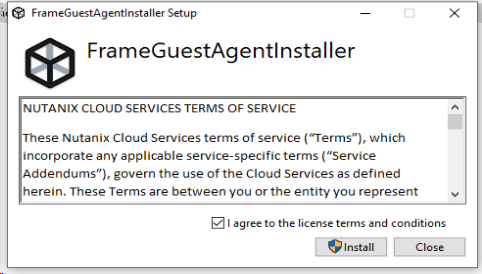
Step 3 : Install the Frame Guest Agent and Nutanix guest tools on Base Images:
Note that when the guest agent is installed, the Prism console to manage the VM is no longer viable due to an issue with the graphic drivers. Remote Desktop on the base image must be enabled before the guest agent is installed or you will lose access to the VM later on so just make sure that RDP remote access is enabled prior to the installation. Also make sure that you do not create any local user called “ Frame “ since this is required by the agent and will create a local user called Frame.
Step 4 : Optimize Base Images and install required applications:
After optimization and all software installation has been completed, make sure to sysprep the machine and take a snapshot prior to that just incase. Run the following :
Start-Process -FilePath "C:\Windows\System32\Sysprep\Sysprep.exe" -ArgumentList "/oobe /shutdown /generalize /unattend:C:\ProgramData\Frame\Sysprep\Unattend.xml" -Wait -NoNewWindow
Step 5 : Configure Prism Central/Element Service Accounts & Categories then add base Images to FrameRole category:
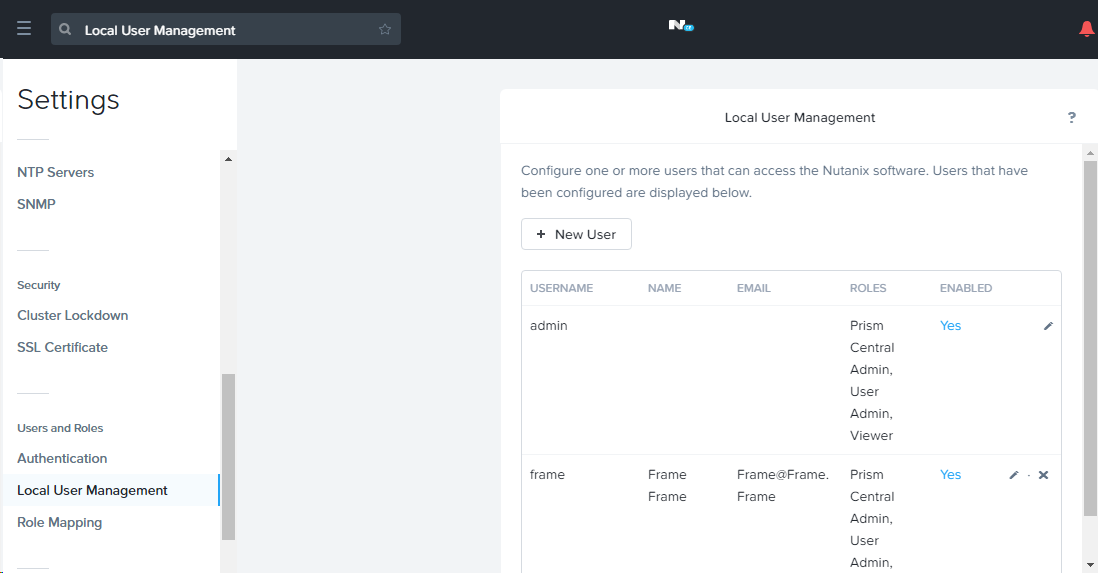
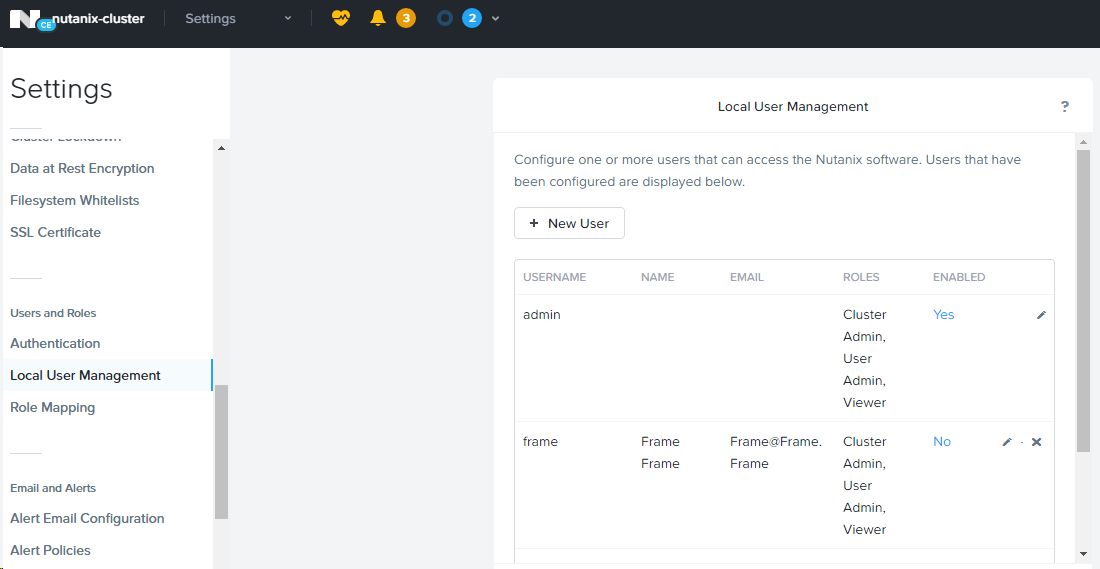
I have created a local admin on Prism Central and Prism Element that I will use as a service account integration for the cloud connectors instead of using the default admin account.
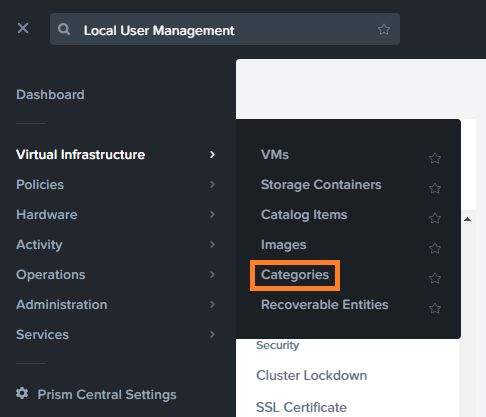
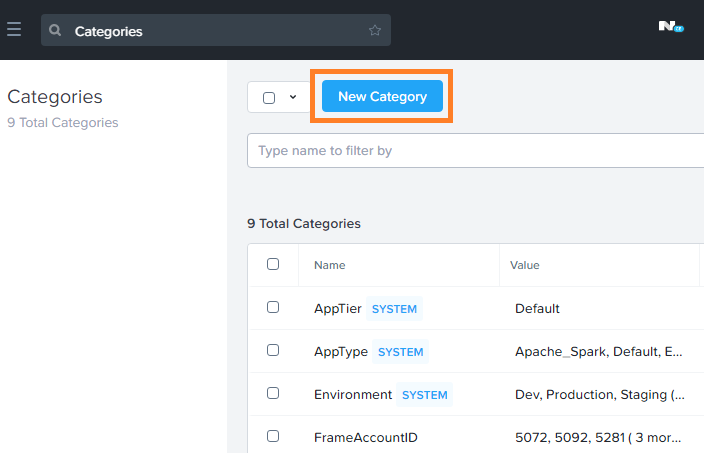
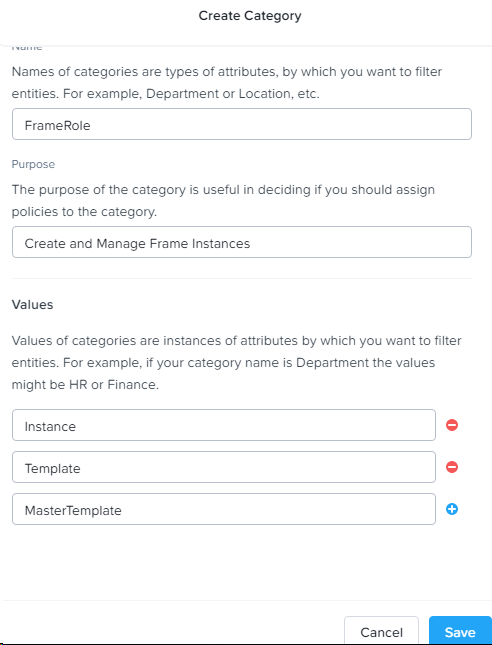
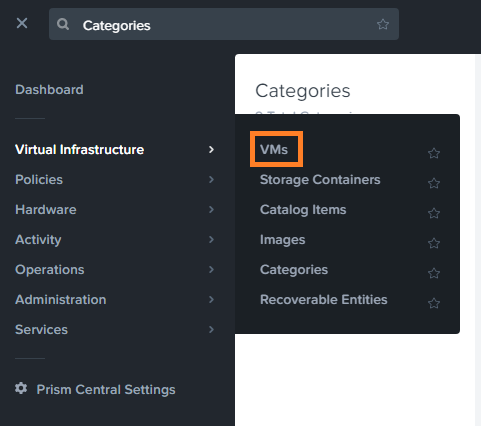
Navigate to Categories on Prism Central in order to create the required Frame categories and assigning the base images to the right category.
Step 6 : Integrate CCA’s with Nutanix Xi Frame organizations account portal:
Navigate back to the cloud connector IP address and enter the following information for your Prism Central.
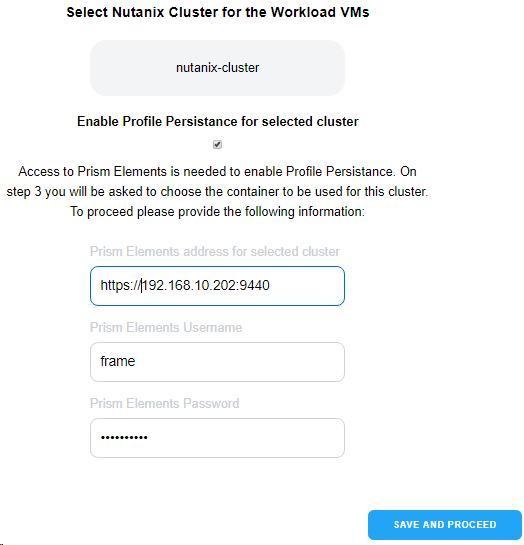
Choose the on-premises AHV cluster that will be hosting Xi Frame workloads. For the profile persistence that needs to connect to Prism Element for the chosen cluster, the created service account did not work despite it having the all the permissions, only the default admin account worked.
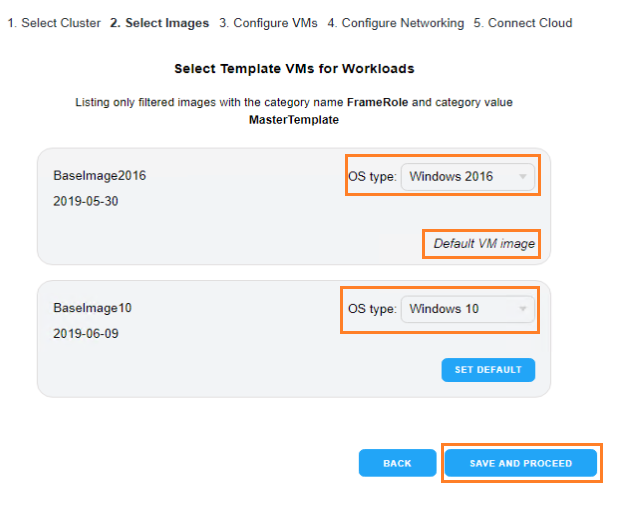
Select the OS type for every base image. Only base images part of the FrameRole: Master Template category will appear here that is why we configured it before continuing the setup of the CCA. Make sure you actually click on the box for every base image to be selected and set a default image.
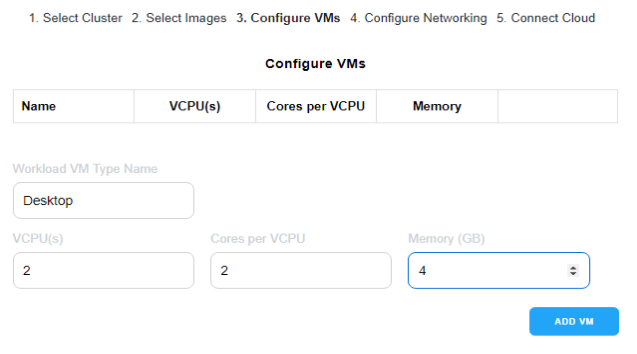
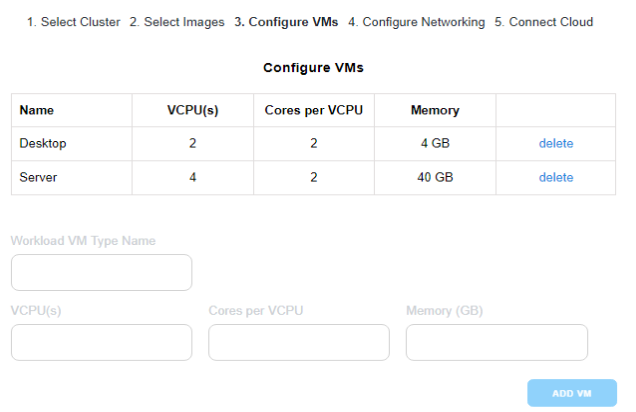
Here is where you add the available sizing for the pool creation later on so virtual desktops can be created based on the below sizing’s when provisioning the pool. Note that, as of now, the cloud connector settings cannot be changed after the wizard is finalized so make sure you add all of your sized options accordingly.
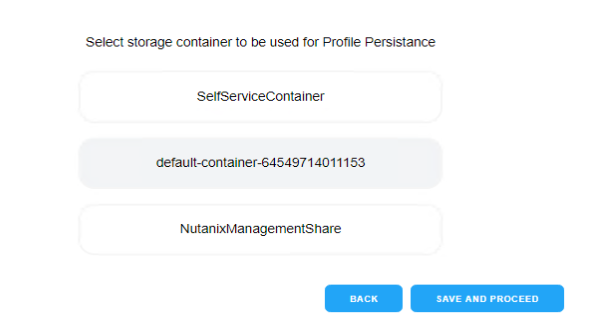
Choose the storage container that will hold the created virtual desktop workloads on the on-premises AHV cluster.
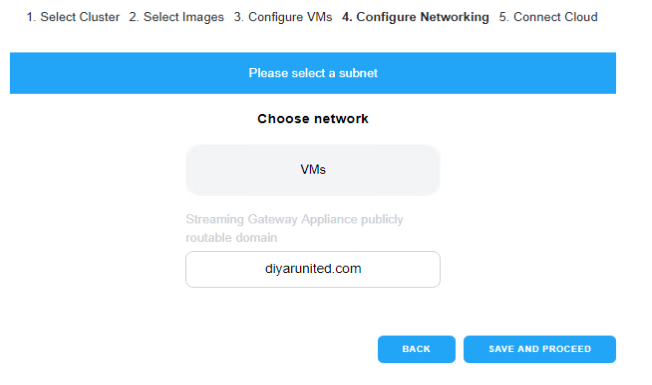
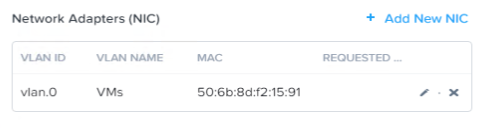
Choose the networks that the virtual workloads will be created on and if external access is required add the Streaming Gateway Appliance publicly routable domain.
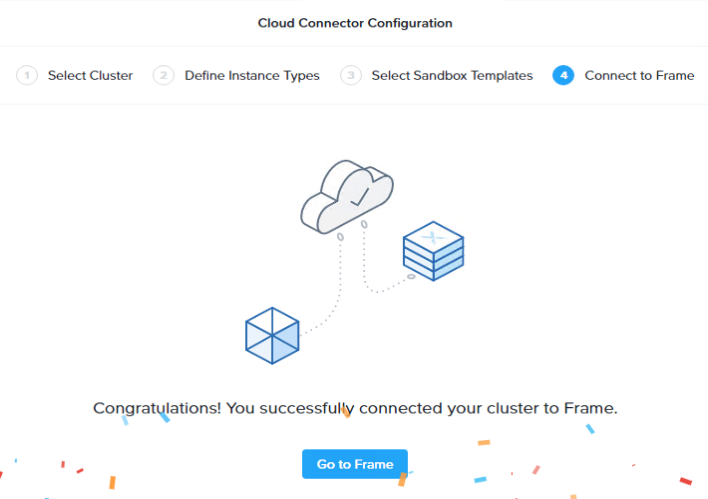
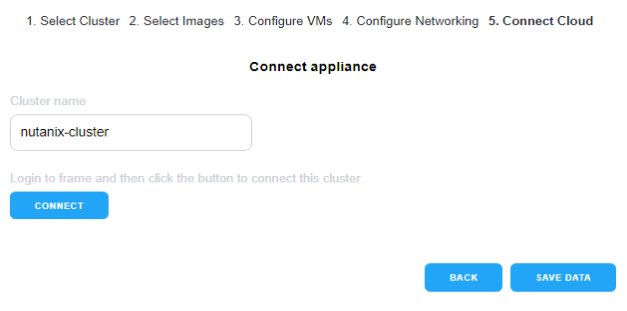
Very important at this stage that you login to mynutanix from the same browser being used to configure the CCA so that when it tries to connect to your Frame portal it auto-authenticates. If you write the cluster name but the connect button is greyed-out just press save-data then the connect button would be usable.
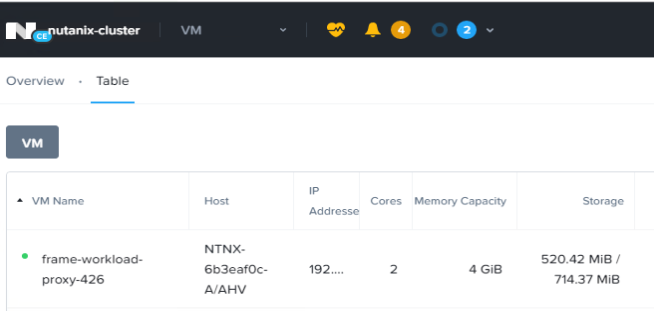
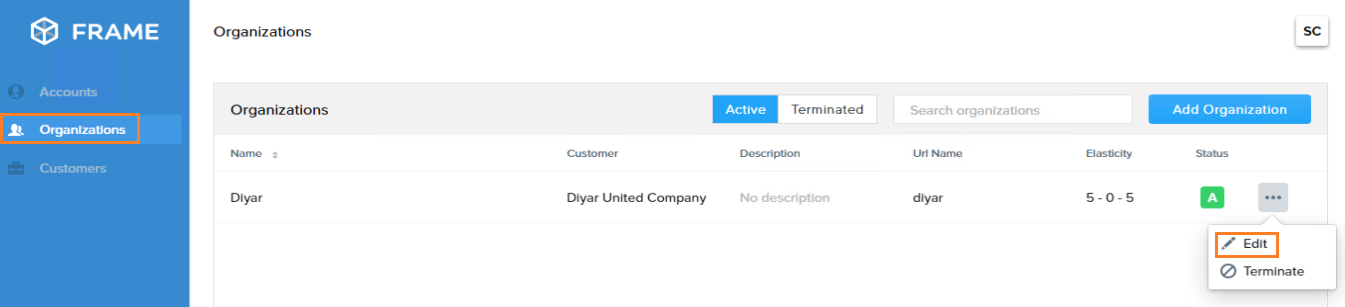
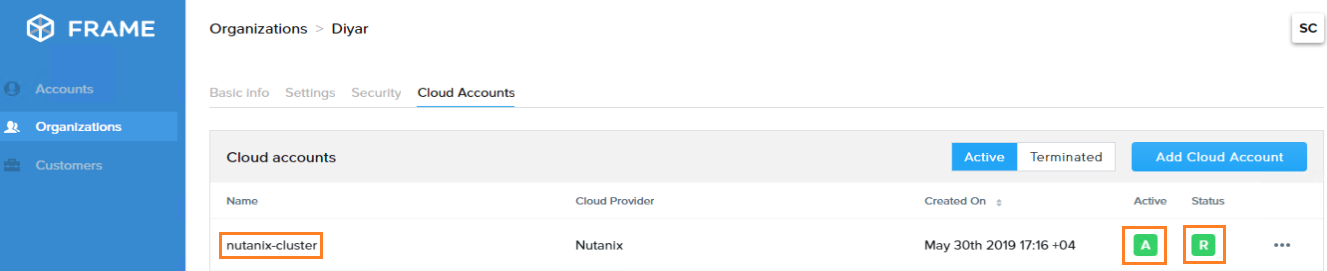
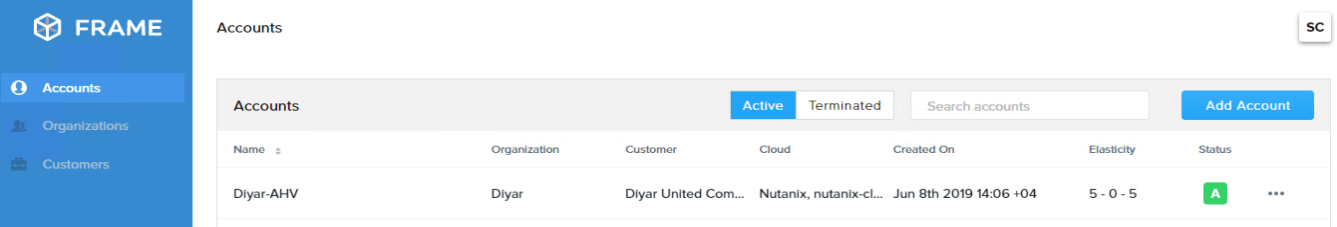
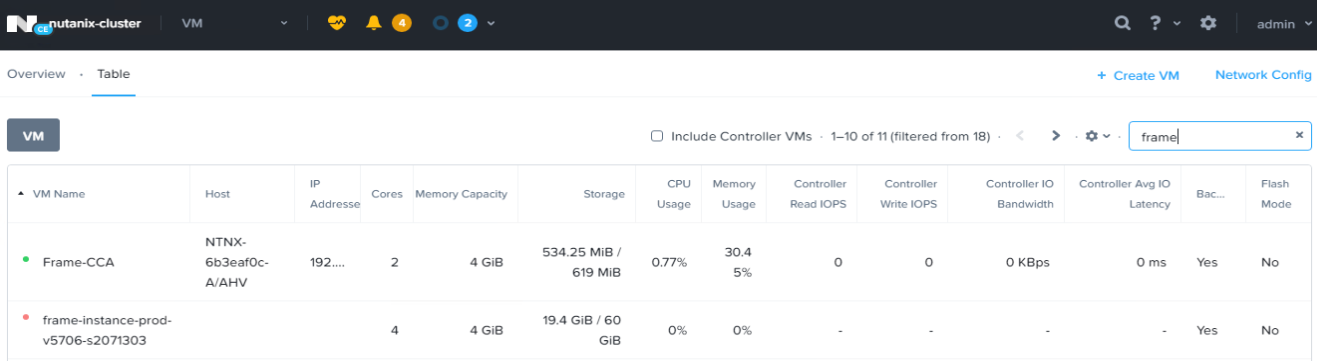
When connected, choose the organization that this Nutanix Xi Cloud Account will be added to and continue. Give it around 30 minutes and the following should be visible on the on-premises AHV cluster and on Frame portal.
Step 7 : Create an Account with on-premises AHV Nutanix as Cloud Provider:
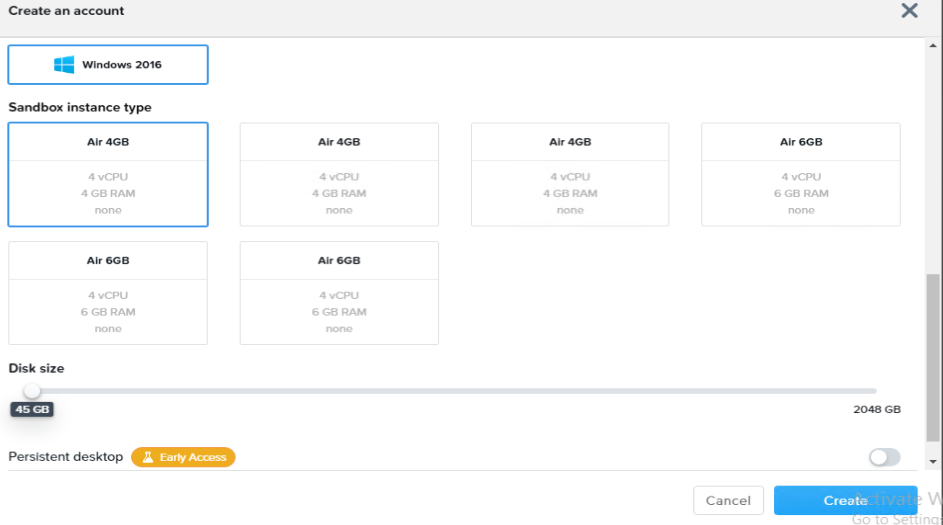
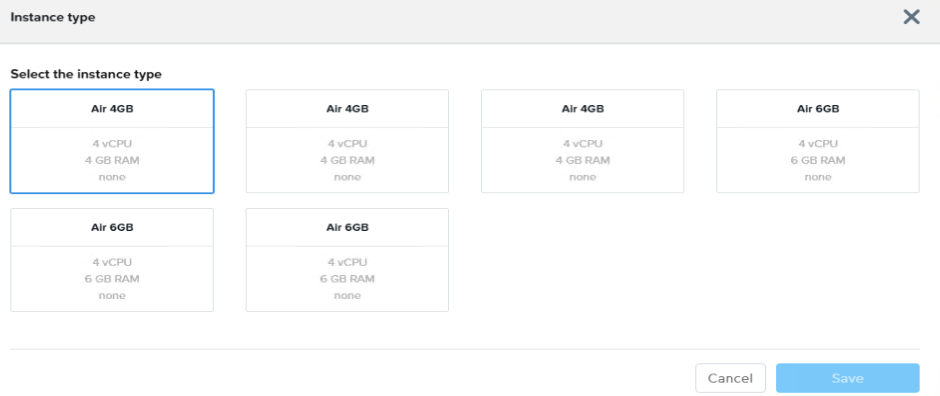
Here you should see the created Desktop and Server sizing templates configured earlier on the CCA but because I am showing an already configured account earlier, it is showing different namings for the sizing templates.
This would also create the base image for the account that will be used as a reference image for any virtual desktops created under this account and copied from the chosen base images when configuring the CCA. Give it some time then click on the account to be forwarded to the sandbox where Frame settings can be configured.
Step 8 : Configure Frame settings and Capacity.
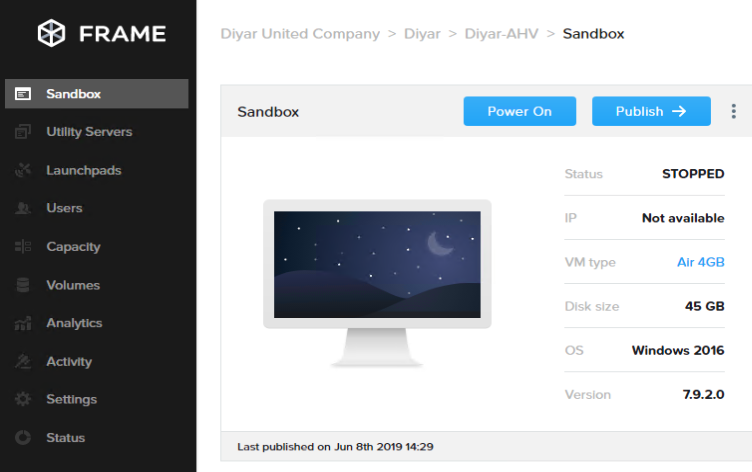
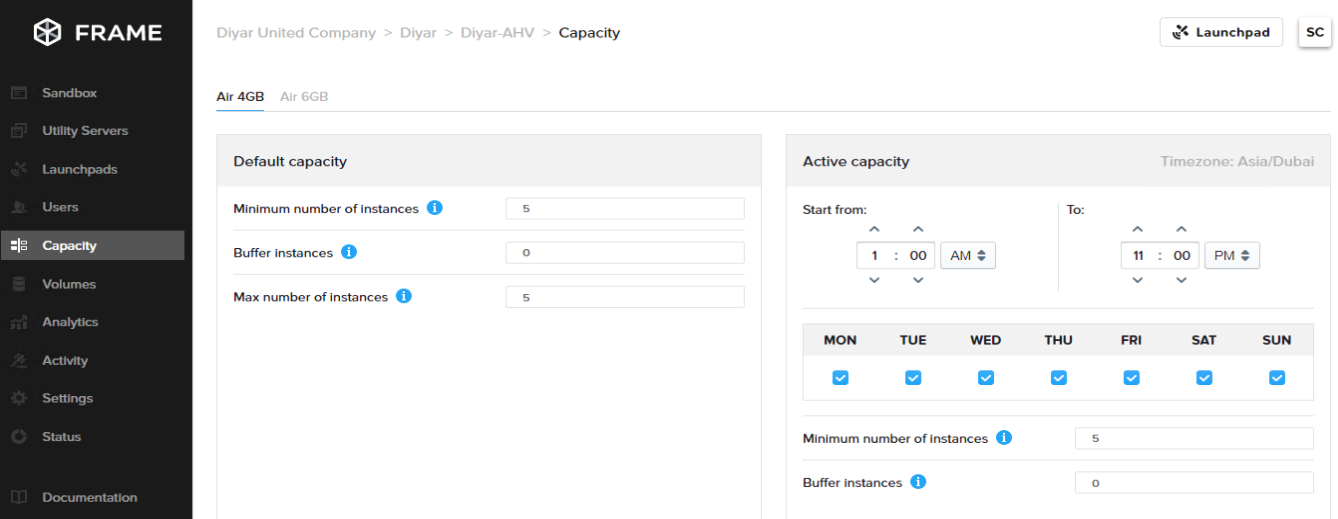
Here is where one would define the number of virtual desktops that would be provisioned under this sandbox for every template including power management and capacity management based on user requirements. The sandbox cannot be published and pool or catalog created unless capacity is configured.
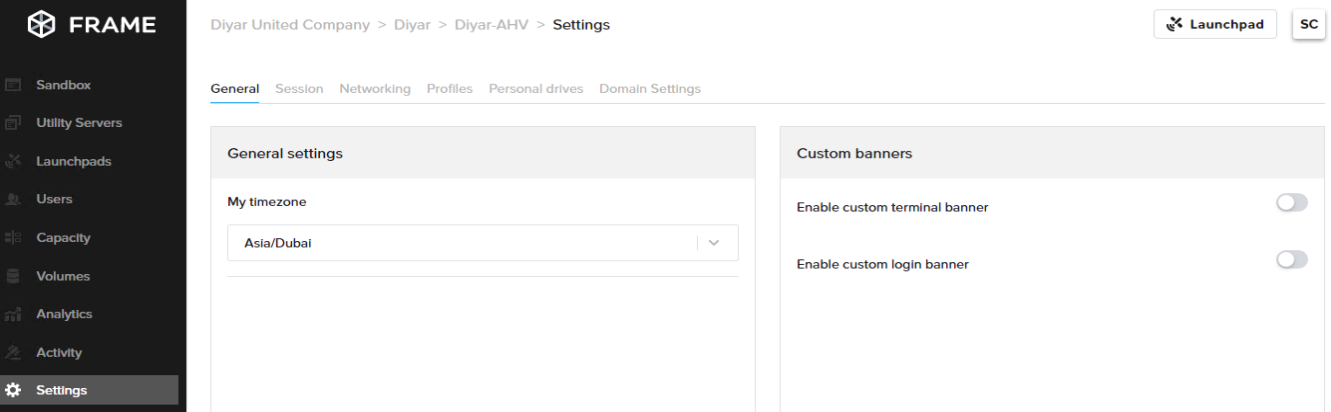
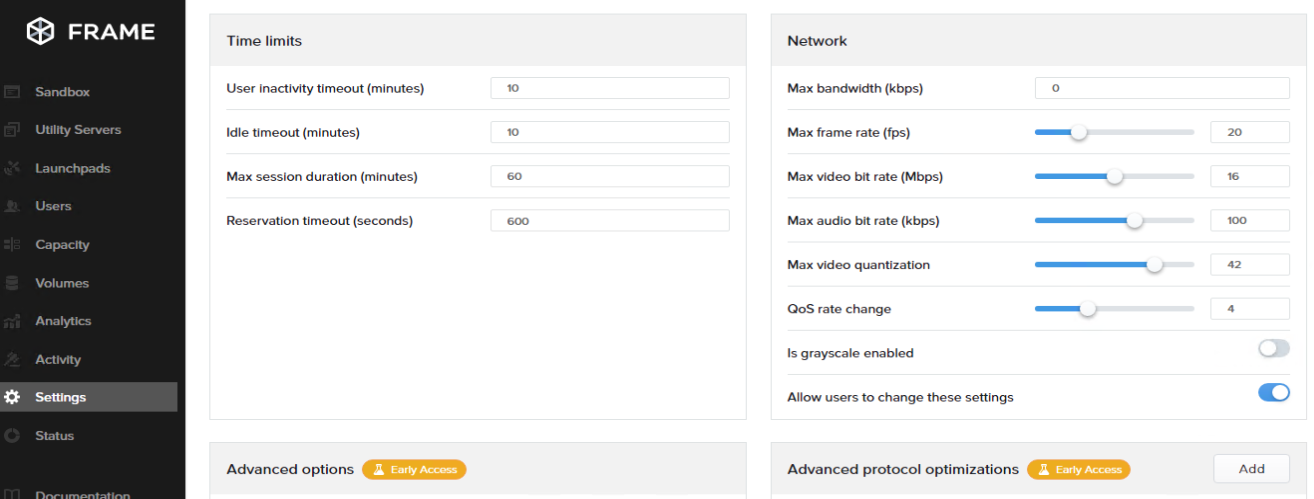
Settings is where session variables are configured along side other production or early access features. Meddling with these settings would impact performance and should be done in a controlled dev/test environment before pushing to production. Profile management requires domain join integration.
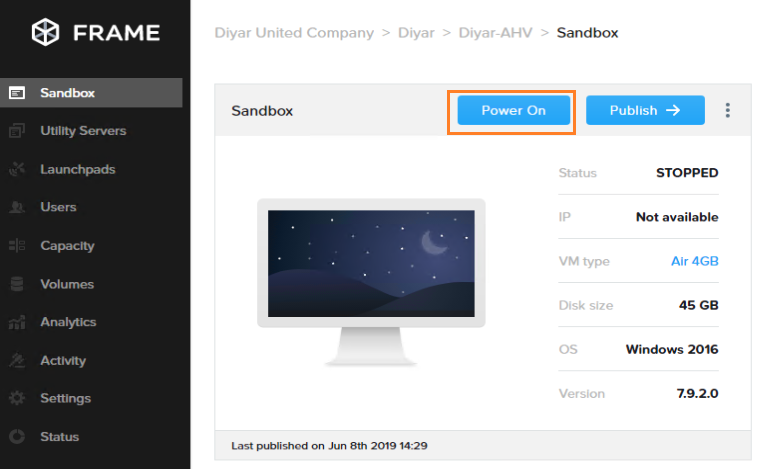
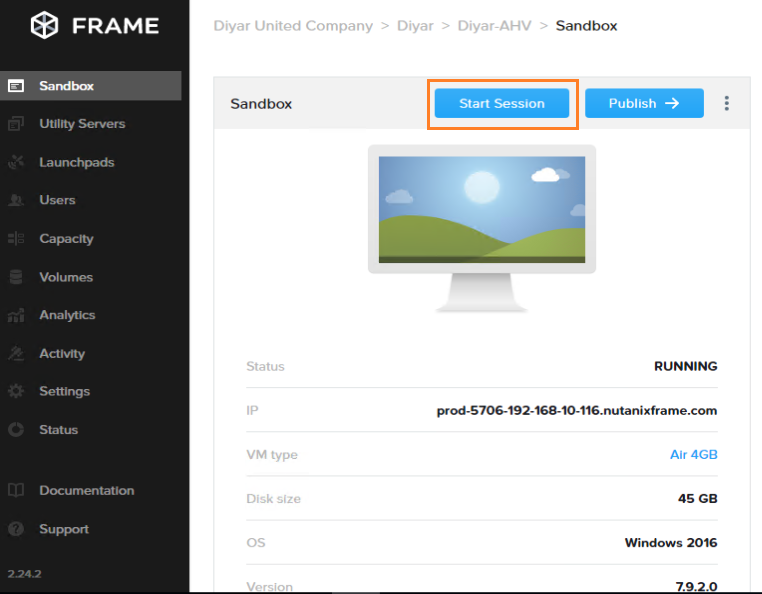
Step 9 : Power On sandbox base VM and verify functionality.
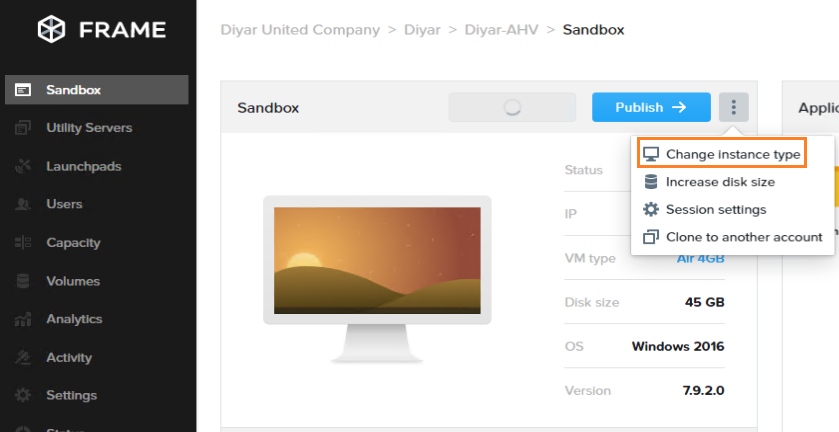
Until the base image for this account is powered on, note that you can change and shift between instance types that where added during the CCA configuration here.
Again here you would find the sizing’s and names that where added during the CCA configuration and that as of now cannot be changed after the CCA configuration is finalized.
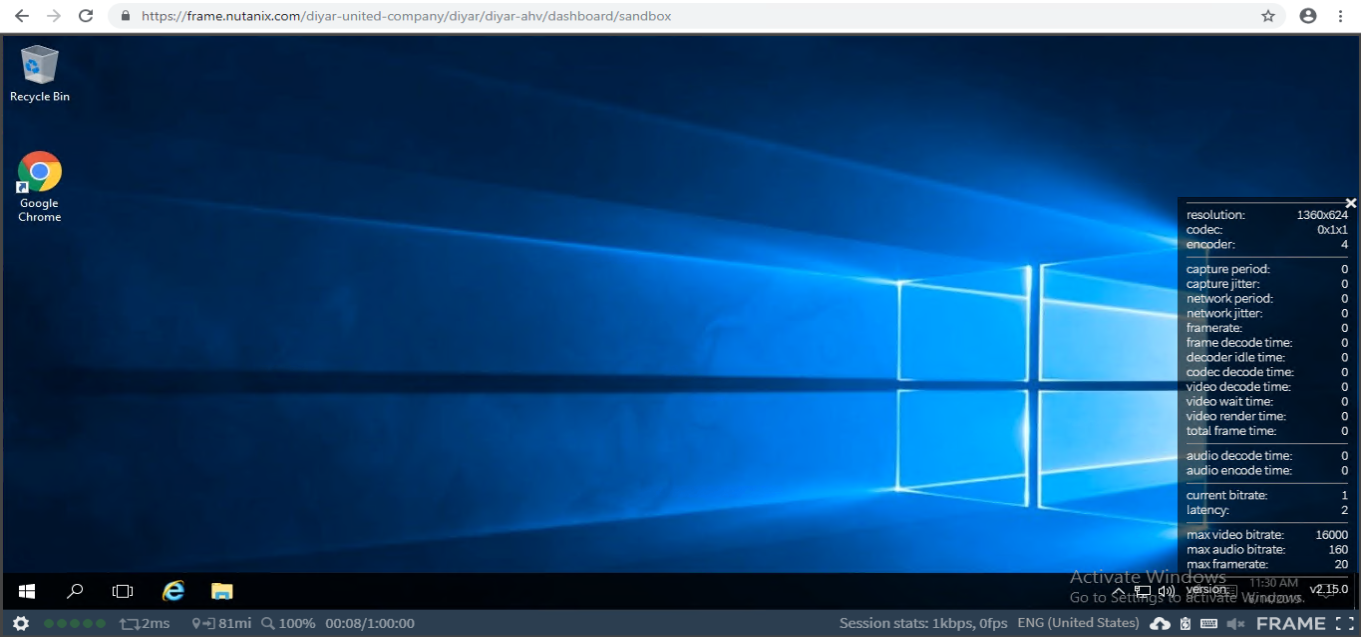
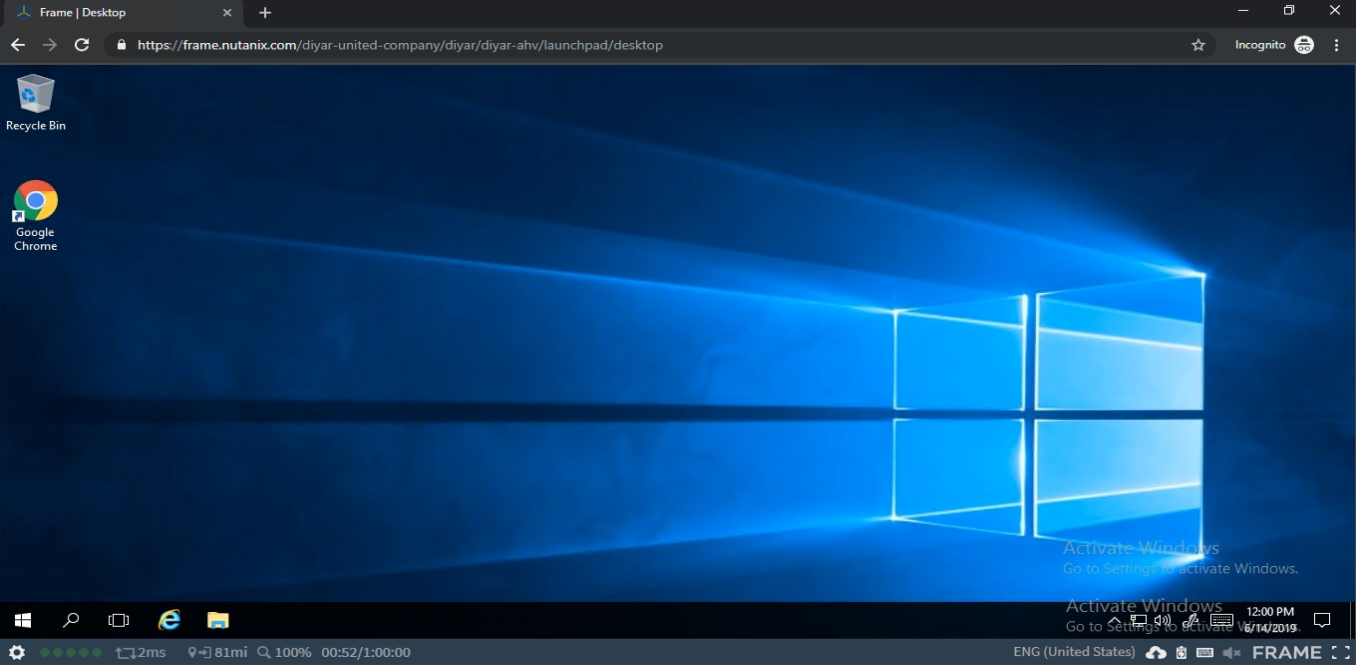
After the Base Image is powered on, lets connect to it using Xi Frame technology to make sure that everything is working fine from a guest agent perspective internally.
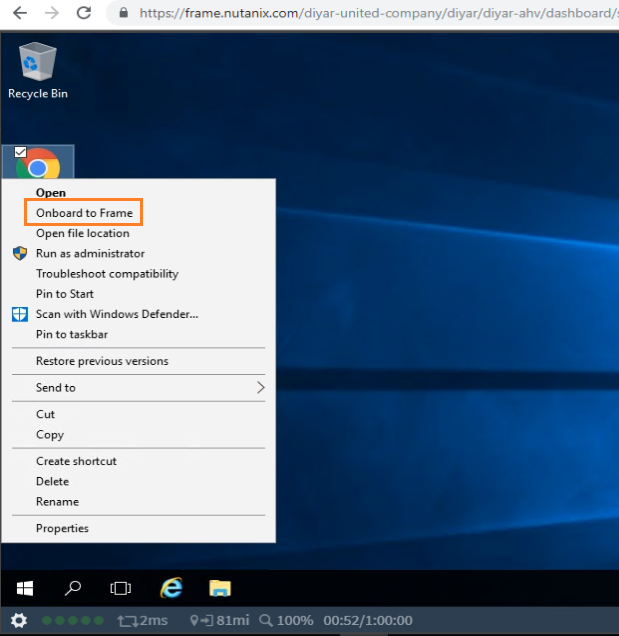
In order to publish independent applications rather than full session or full desktops, install the application here, right click, and click on Onboard to Frame. Now this is the base image for this account so all changes that will be pushed to users will have to be done from the sandbox.
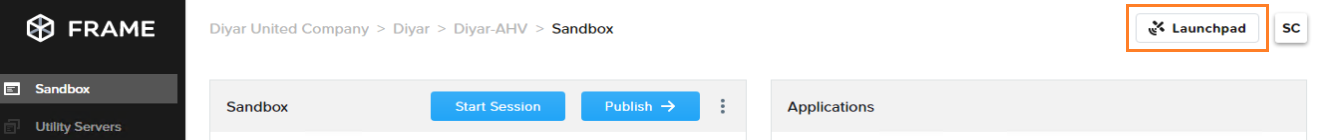
Step 10 : Publish Sandbox and create launchpads.
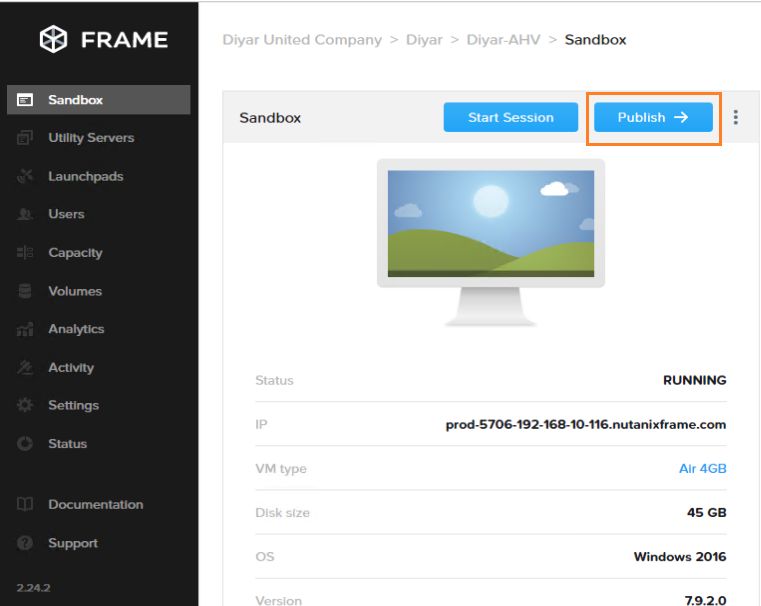
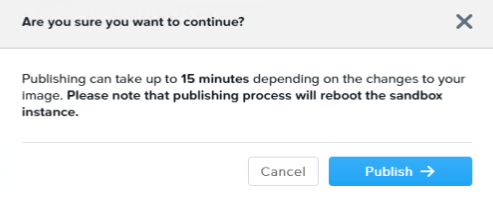
When ready to create the catalog based on the number of instances inputs in the capacity tab, click on Publish.
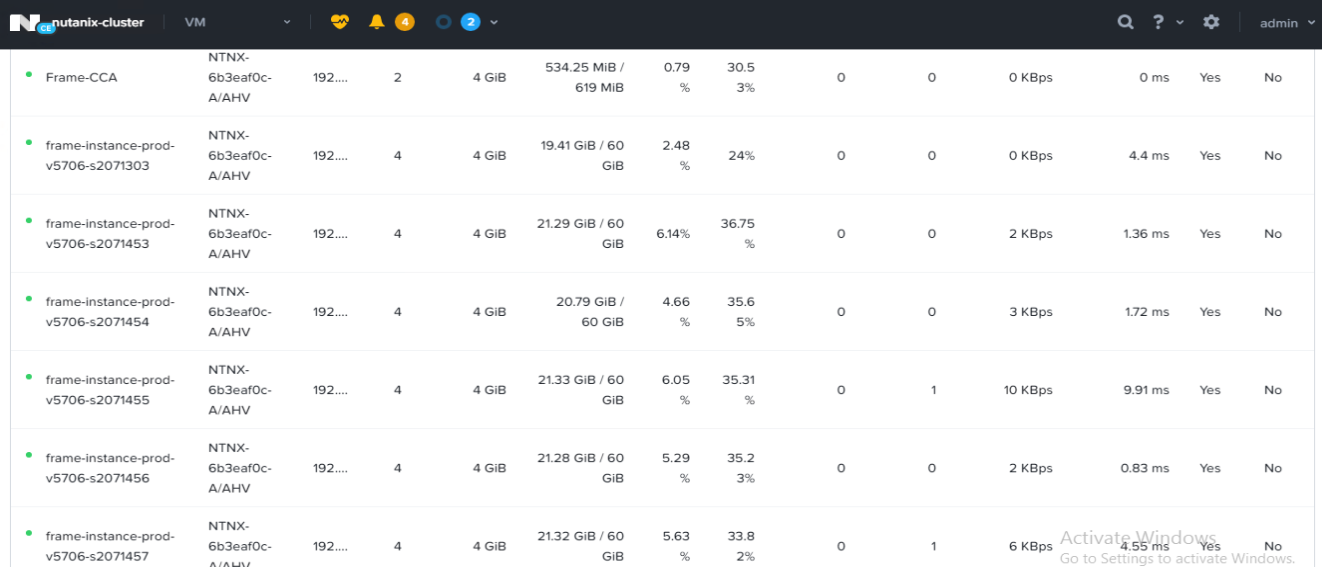
Give it around 30 minutes depending on your on-premises AHV cluster performance and sizing, the following should appear inside the cluster.
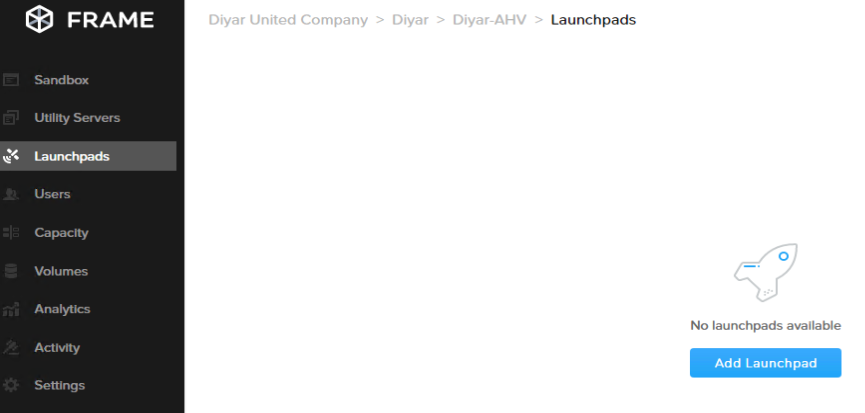
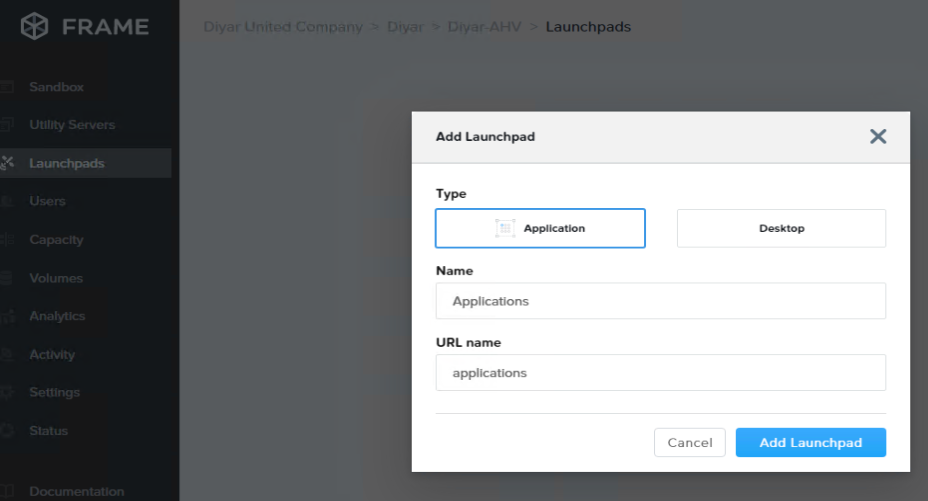
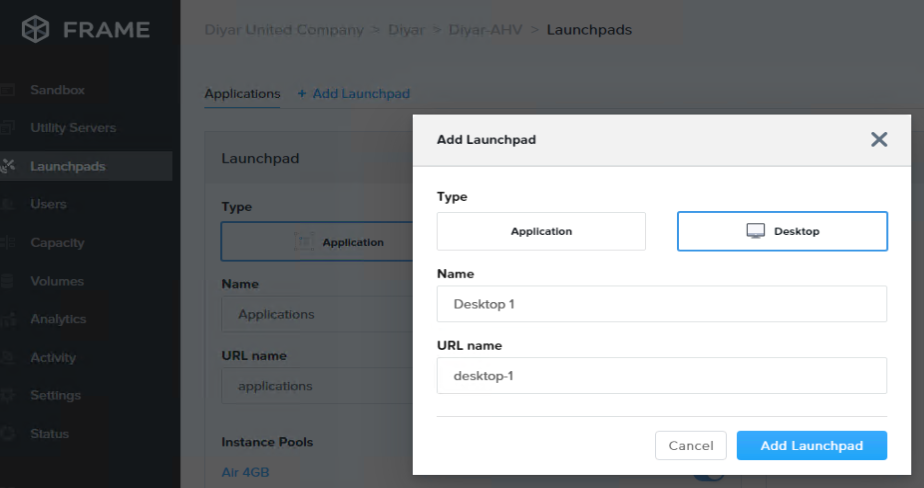
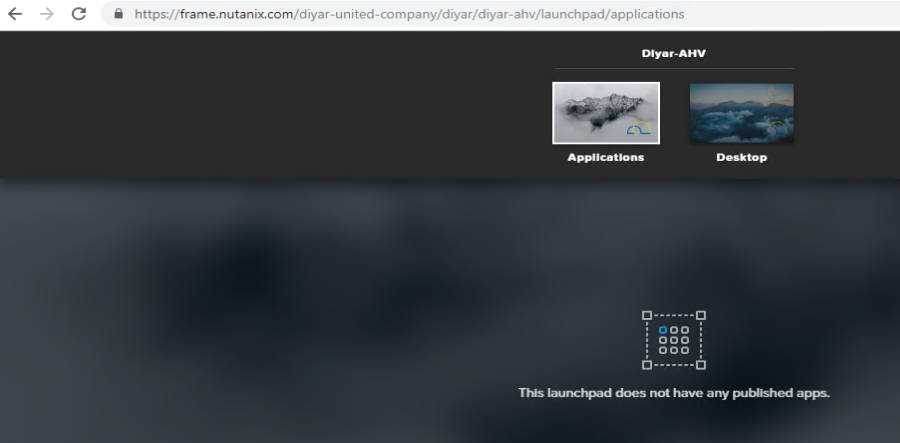
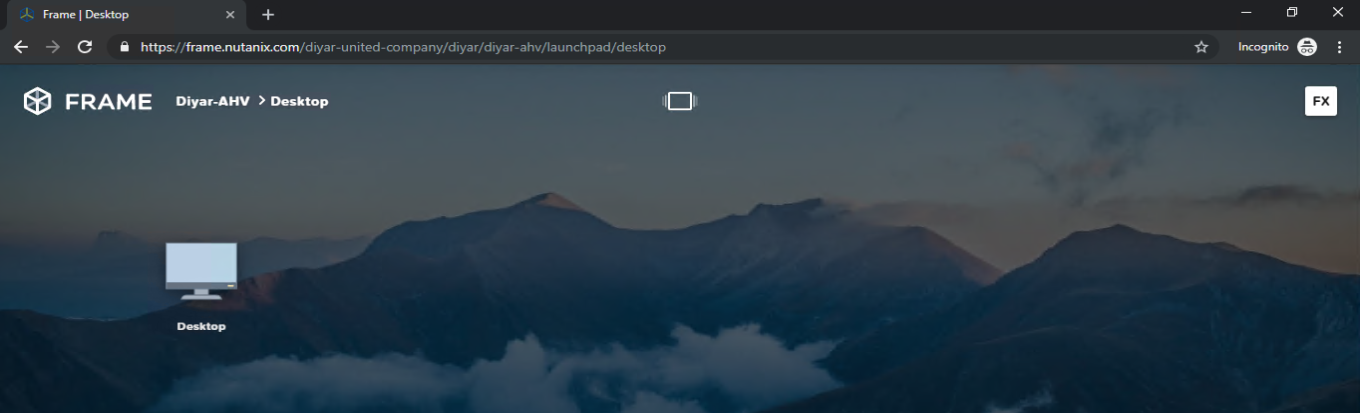
In order for users to connect to these virtual desktops, a launchpad needs to be created first which would be the launch URL for the user.
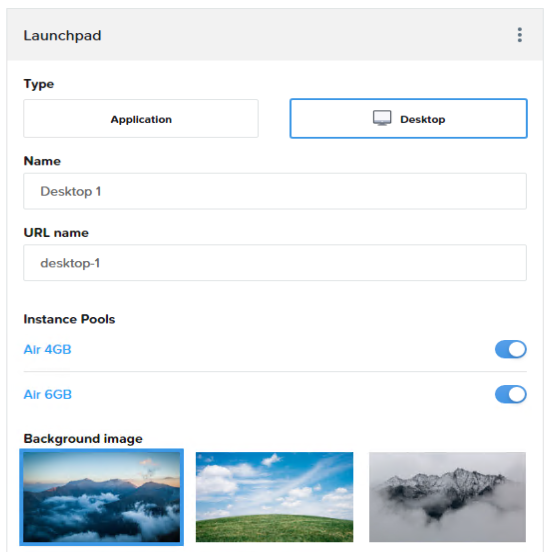
You can choose which virtual desktop template will the launchpad allow the user to access and set the background for the same.
Step 11 : Configure User Access permissions.
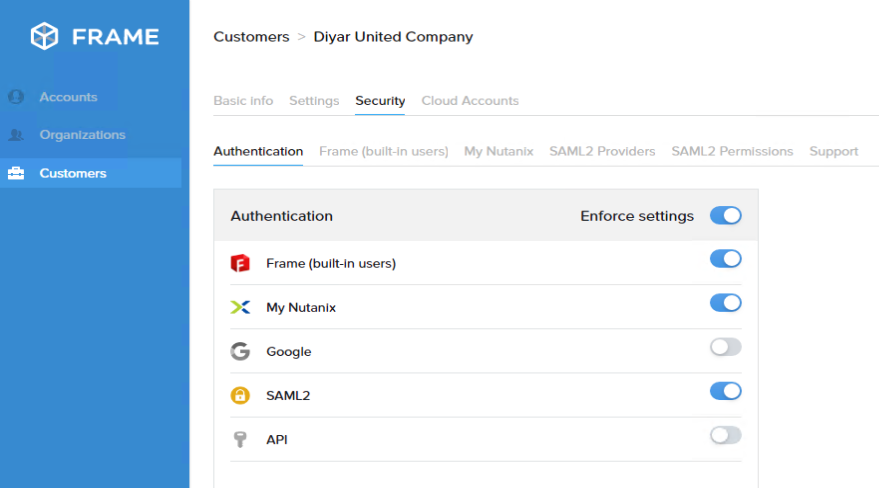
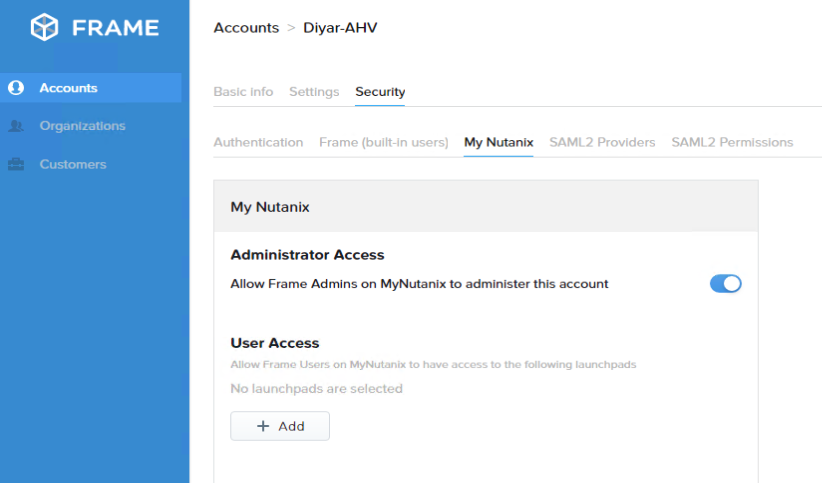
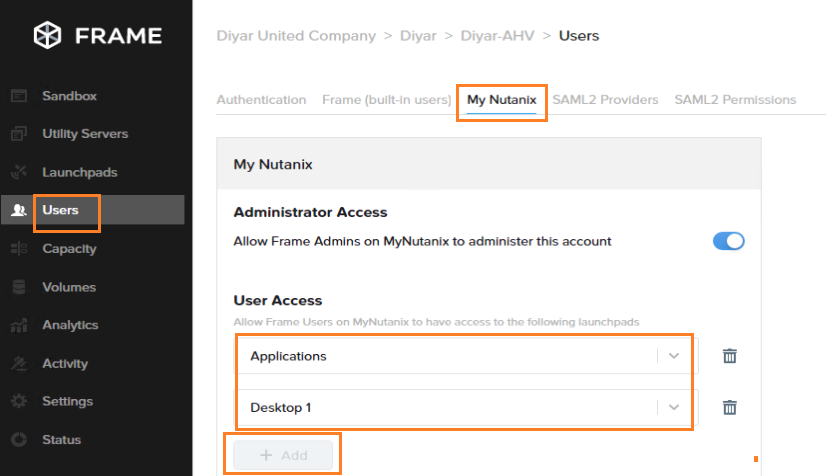
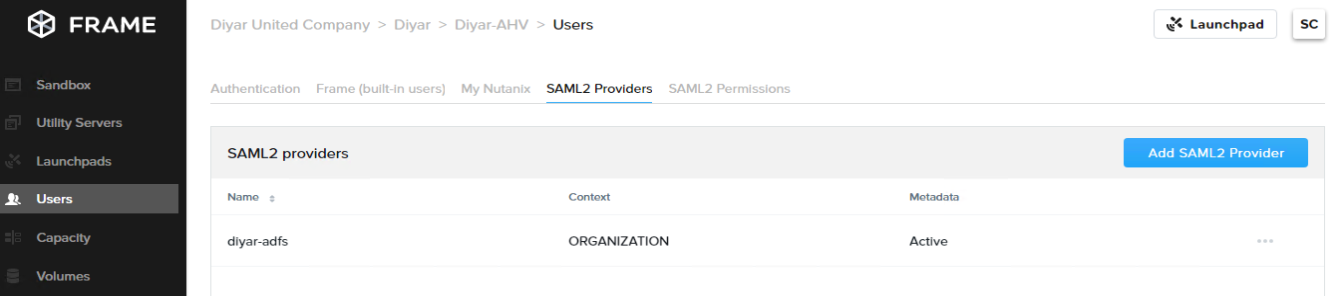
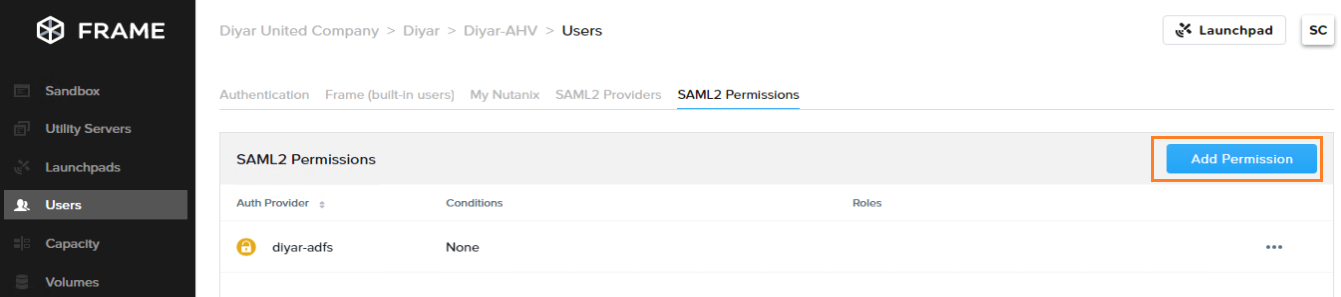
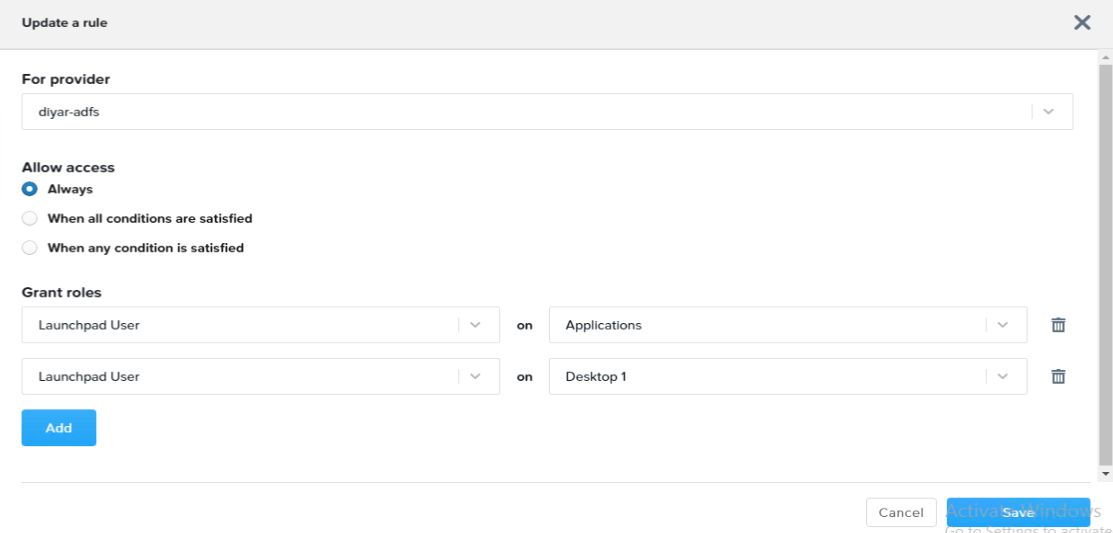
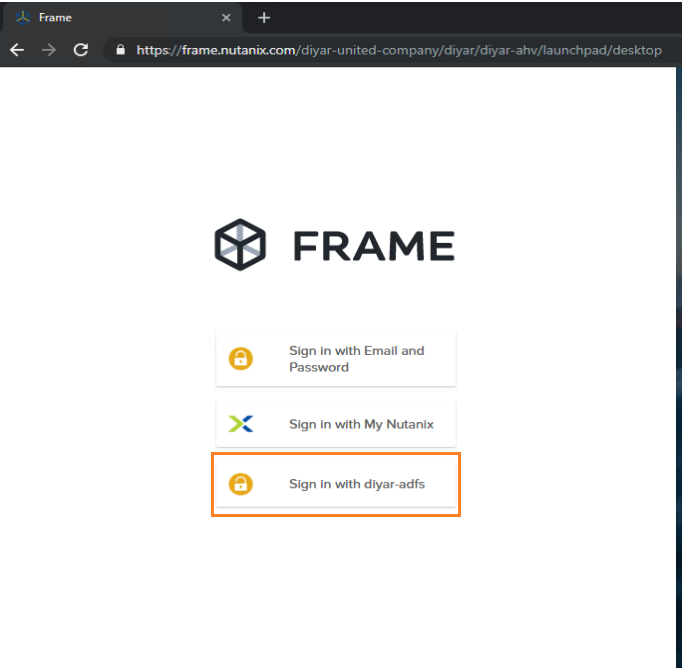
Xi Frame can integrate with a number of authentication providers to provide access to users such as the MyNutanix account, Frame (Built-in Users), Google, SAML2, and API. The options will appear as enabled or disabled based on what is configured in the customers tab first so you cannot change authentication options inside the sandbox but you can configure the already enabled security setting inside the account and sandbox.
If you want to utilize MyNutanix for example to provide users access to created Launchpads just navigate to Users then My Nutanix and add the created launchpads under User Access.
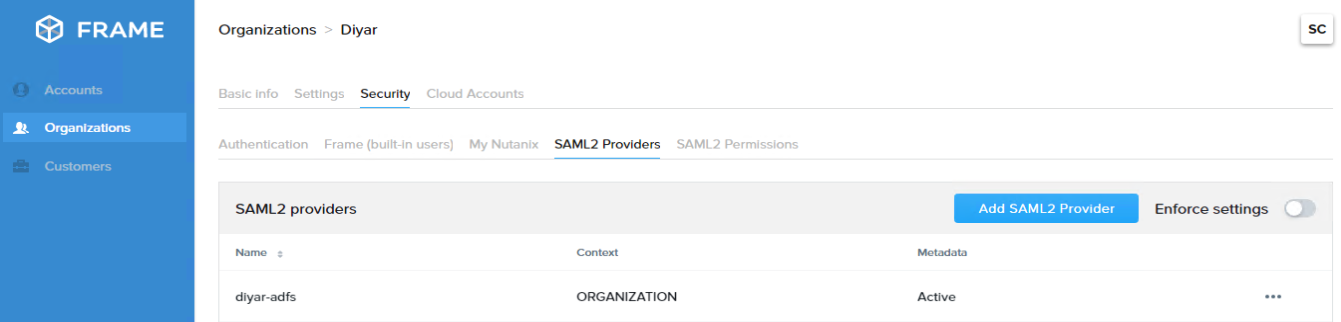
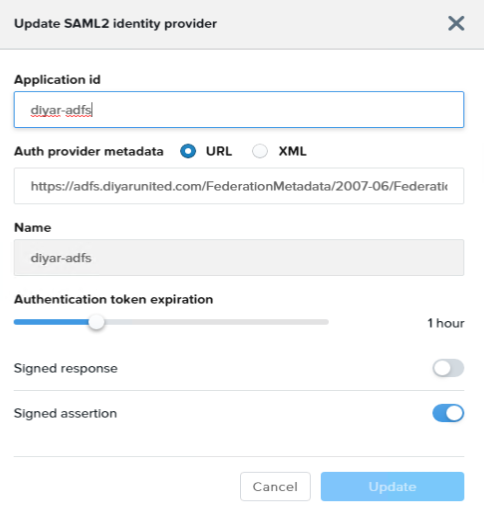
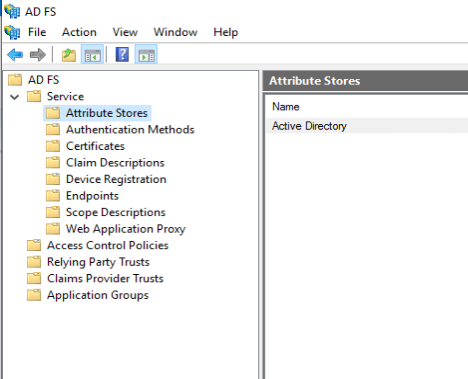
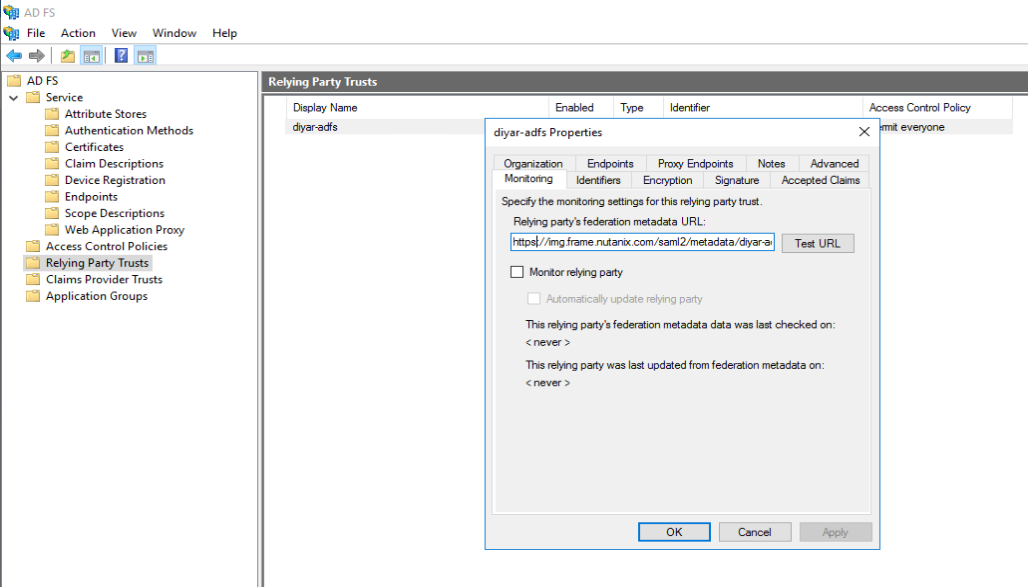
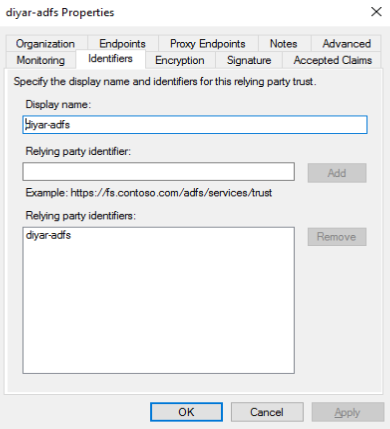
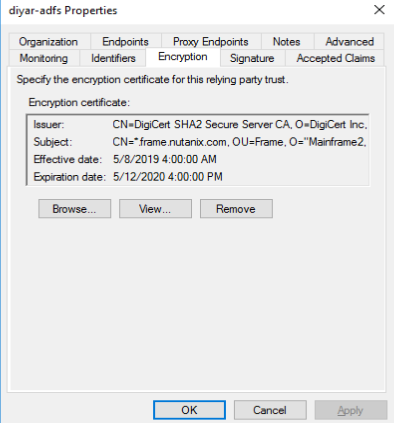
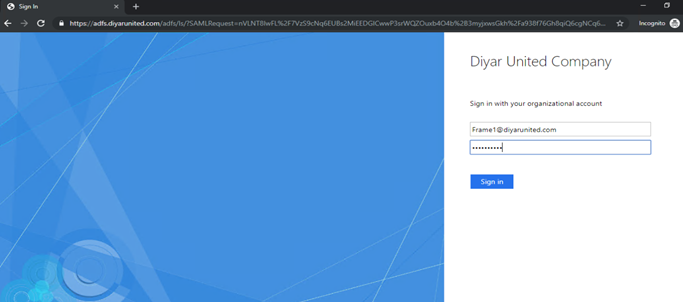
No enterprise doing on-premises VDI would go down that path of in-built Frame users to MyNutanix account users, at least most, so the viable option is integration with on-premises Active Directory which required an ADFS setup and SAML integration with Nutanix. I have added this under the organization account so it can be added to all created accounts in the future.
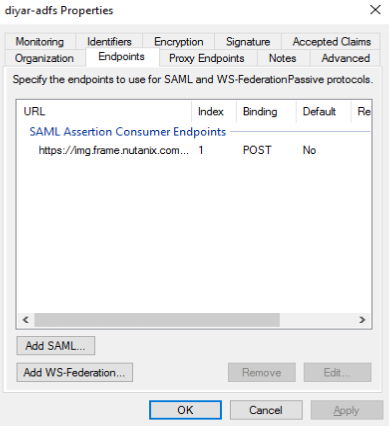
Just for your reference, the metadata URL is as follows: https://adfs.yourdomain.com/FederationMetadata/2007-06/FederationMetadata.xml , make sure that ADFS is published to the internet on TCP 443 so that its accessible to external users as well. Also make sure that the application id name matches the one configured in your ADFS. You can configure the same by following this guide:
The Nutanix metadata URL will not be accessible from ADFS directly when adding it so just download it and import manually when adding the relaying party. Use Permit Everyone with caution in tight security oriented organizations.
Step 12 : Test Virtual Desktops and Apps access internally.
As you can see, the URL includes the organization name, account name, and launchpad name so that is what needs to be provided to users. Let me open a new browser tab to login as a new AD user using ADFS integration and test Desktop access.
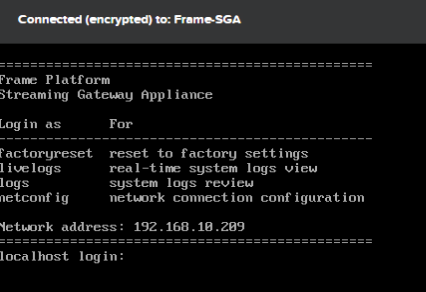
Step 13 : Create and Configure Xi Frame SGA (Gateway Streaming Appliance).
The download of the Frame SGA appliance including the deployment guide should come from Frame support so reach out to them as I am not sure it is publicly available so I will not risk posting the link.
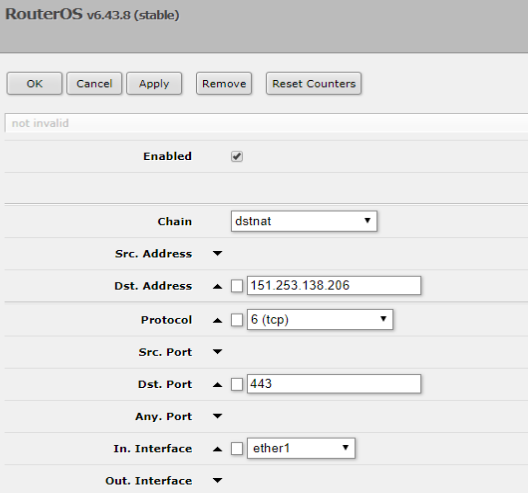
You will need a wildcard certificate for your public domain since Frame uses a wildcard *.domain.com to broker connections externally. You will also need a public IP that will be NATed to the IP of the SGAon TCP 443.
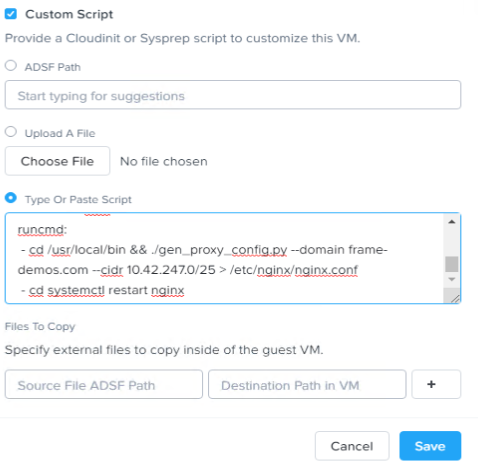
The configuration of the virtual appliance is done through a YAML template, copy and paste from the provided Frame support pdf does not work so I will provide the YAML structure here to make it easy for you not to have to rebuild the structure, just change your variables.
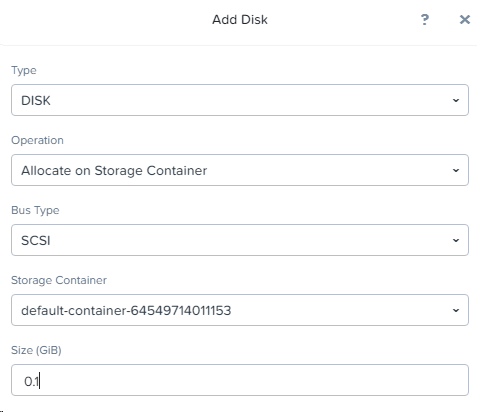
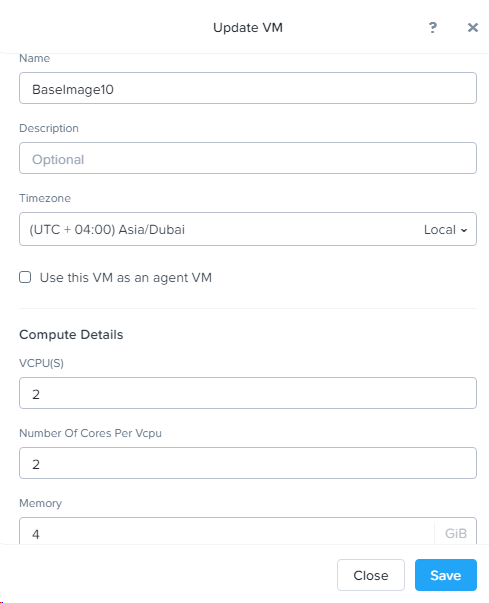
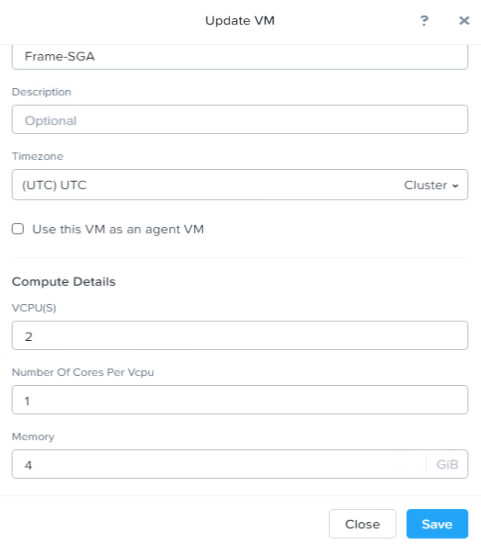
First create a VM with 2 virtual CPUs and 4 GB RAM while keeping the timing on UTC in order for this to be synced with Frame cloud control plane.
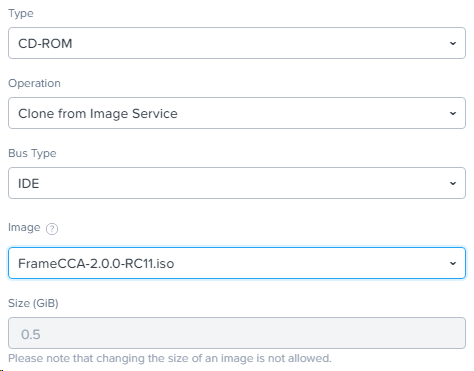
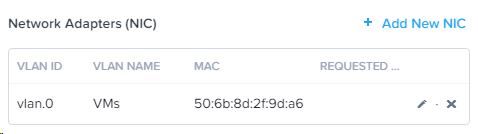
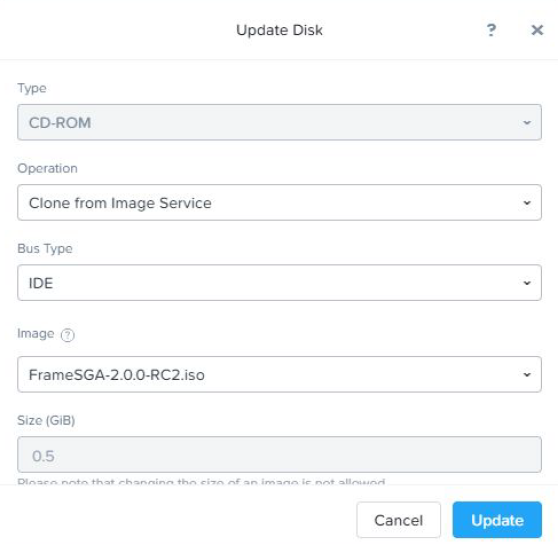
Attach the SGA ISO to the CD-ROM of the VM and add a NIC. Remember this appliance needs to be on the DMZ and TCP 443 opened internally and externally between the SGA and the created virtual workloads subnet.
Paste the YAML template content which will auto-configure the appliance as per the configured variables. There are four variables in the YAML file, The wildcard cert, the wildcard cert private key, the public domain, and the subnet that the virtual workloads are running on.
If you have a PFX that you would like to convert to PEM cert and PEM key (without password) just download OpenSSL-Win32:
-
Download “ openssl.cnf “ to c:\OpenSSL-Win32 and cmd: set OPENSSL_CONF=c:\OpenSSL-Win32\openssl.cnf
-
Copy the wildcard cert into the the folder C:\OpenSSL-Win32\bin
-
openssl pkcs12 -in wildcard.pfx -nocerts -out key.pem –nodes
-
openssl pkcs12 -in C:\OpenSSL-Win32\bin\wildcard.pfx -nocerts -out key.pem –nodes
-
openssl pkcs12 -in C:\OpenSSL-Win32\bin\wildcard.pfx -nokeys -out cert.pem
-
openssl rsa -in key.pem -out server.key
cert.pem is your certificate and server.key is your private key ( without a passphrase ). Open with YAML template with notepad++ and type the variables in the right location then paste into the VM custom script section. Here is a link to the YAML template structure https://1drv.ms/u/s!ArQVbrROC5SqmTIMGzmsyG22MrCY?e=DzvZob . Since you will be using a public certificate, make sure that the intermediate and root certs are included in the yaml file.
Run the VM and it should auto-configure, you can use netconfig as well to change into a static IP or just reserve DHCP.
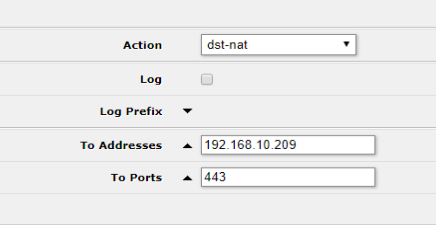
Now create a NAT from your public IP to the internal IP of the Frame SGA. Also don’t forget to open the firewall ports.
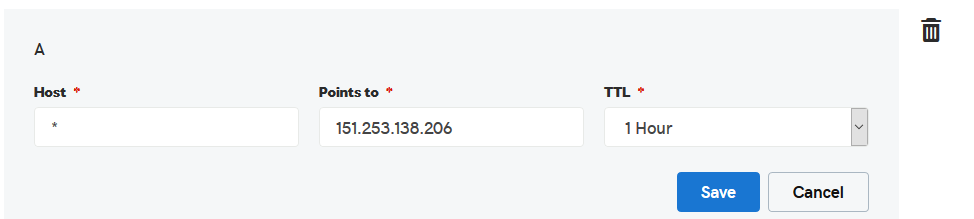
Finally we need to create an wildcard DNS record *.diyarunited.com in my case to point to the public IP that is NATed to the SGA.
That it, now contact Frame support to enable remote connectivity from their site and test the same to ensure that the configured YAML template has the correct configuration and external internet access is operational.
Step 14 : Play around with early access features such as domain-join and profile management.
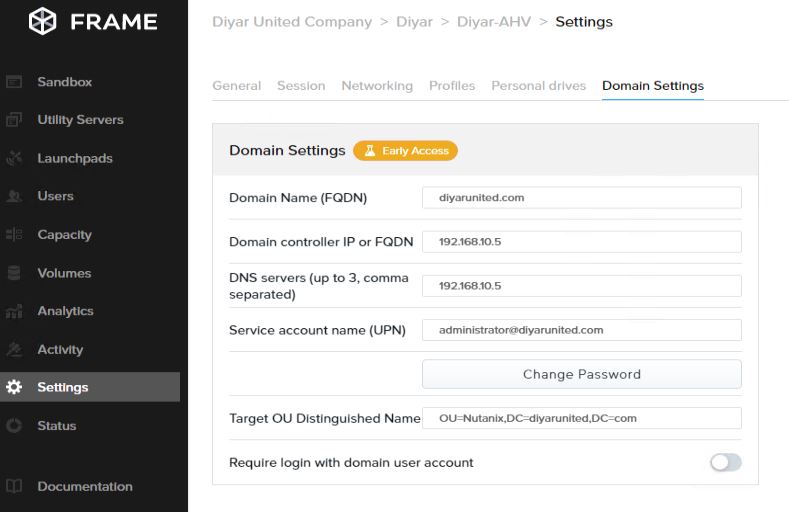
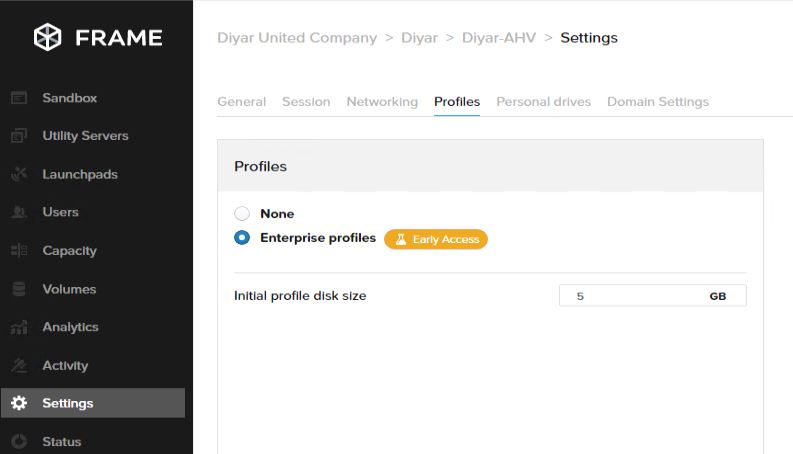
Faced some obstacles on the way in regards to domain join and profile management and working with Frame support on the same. Will post an update once everything is sorted out to showcase profile persistence.
Conclusion:
This is it in terms of backend configuration to get Xi Frame up and running with on-premises AHV, now time for some benchmarking tests which is going to be the challenging part.
Part 1: Nutanix Xi Frame On-Prem AHV: What Does it Mean to Citrix, VMware and The EUC Community !
Part 2: Deploy & Configure Xi Frame VDI on On-Premises AHV
Part 3: Enhance Nutanix Xi Frame User Experience Domain Settings Optimization On-premises AHV
Part 4: Configure Nutanix Xi Frame Enterprise Profiles For VDI On AHV
Part 5: Configure Nutanix Xi Frame Streaming Gateway Appliance for AHV VDI
May the Peace, Mercy, and Blessing of God Be Upon You




Awesome,
well explained
thanks
Thanks.
I’m curious about the need to use ADFS instead of Azure AD Connect (which is obviously much easier to setup and manage). ADFS is a solution to be avoided if possible, so I’m wondering why it’s there – am I missing something related to the architecture that prevents Azure AD Connect from being an alternative Domain-Join solution? Thanks for any insight – Anthony Murfet.
I posted too soon perhaps, I just noticed that there is a section: ” Integrate with Microsoft Azure AD” at “https://docs.frame.nutanix.com/user-management/customauth/azureAD.html” that I missed. Still wondering why you haven’t mentioned it. If a customer is using Office 365 would they need ADFS? or could they just used the SAML2 authentication option to sign-in with an on-premises AD account? Again, thanks – can’t help feeling I’m missing something here.
Hi, If you are integrating with Azure AD directly then you do not need ADFS but then again it is SAML authentication so you would need the SAML configuration as noted in the documentation, so if you are syncing your users from on-premises to Azure AD then integrating SAML auth from Frame to Azure AD , you would not need ADFS. If you want to authenticate directly from your on-premises or IaaS cloud based AD then you need ADFS to enable SAML integration with Frame. Hope this clears it up. Thanks.
Saadallah, I am thankful for the work you have done on this post. A valuable contribution. Currently there is very little conversation on this topic going on over in the Nutanix community area – are you aware of any place online where we can trade information with others? Cheers!
I am not aware of any but then again I am not part of any Nutanix groups, the whole announcement is still new so give it some time and when most of these early access features become available, definitely you will start to find Nutanix actively bringing this more to life for AHV customers but I think they don’t want to actively pitch as of now so that other vendors dont simply burn them since the product still needs these early access features be production ready to compete with enterprise VDI vendors.
GREAT !!!
Newbie for Frame and I’m trying to understand every details posted here. I’m a bit confused, can I access my frame account remotely? If my frame account was setup using Nutanix AHV Cluster?
Hi, If you deploy virtual desktops on your on-premises AHV and want to access it from outside the routed internal network where the virtual desktops are deployed you will need to deploy and configure the Xi Frame Gateway Streaming Appliance as documented in the post and email Frame support to enable the remote connectivity service for you. Another option would be to establish a VPN connection to the internal network and then launch a virtual desktop. Hope this clears it out. Thanks.
Great post all, i am trying to find some information on the YAML configuration as i was able to deloy SGA without it but failling when i am using the YAML configuration script.
Thank you
Yes I did face the same because YAML is all about structure and if you mess that up because of copy and paste then it would fail. Did you download the YAML file I uploaded and copied/pasted that from NotePad++ after you changed your network/cert settings ? Use the uploaded YAML file to maintain the structure and make sure in Notepad++ that all is okay before you copy/paste. BTW I have been told by Nutanix Frame team that the deployment is changing next week to a much simpler version so stay tuned.