Introduction
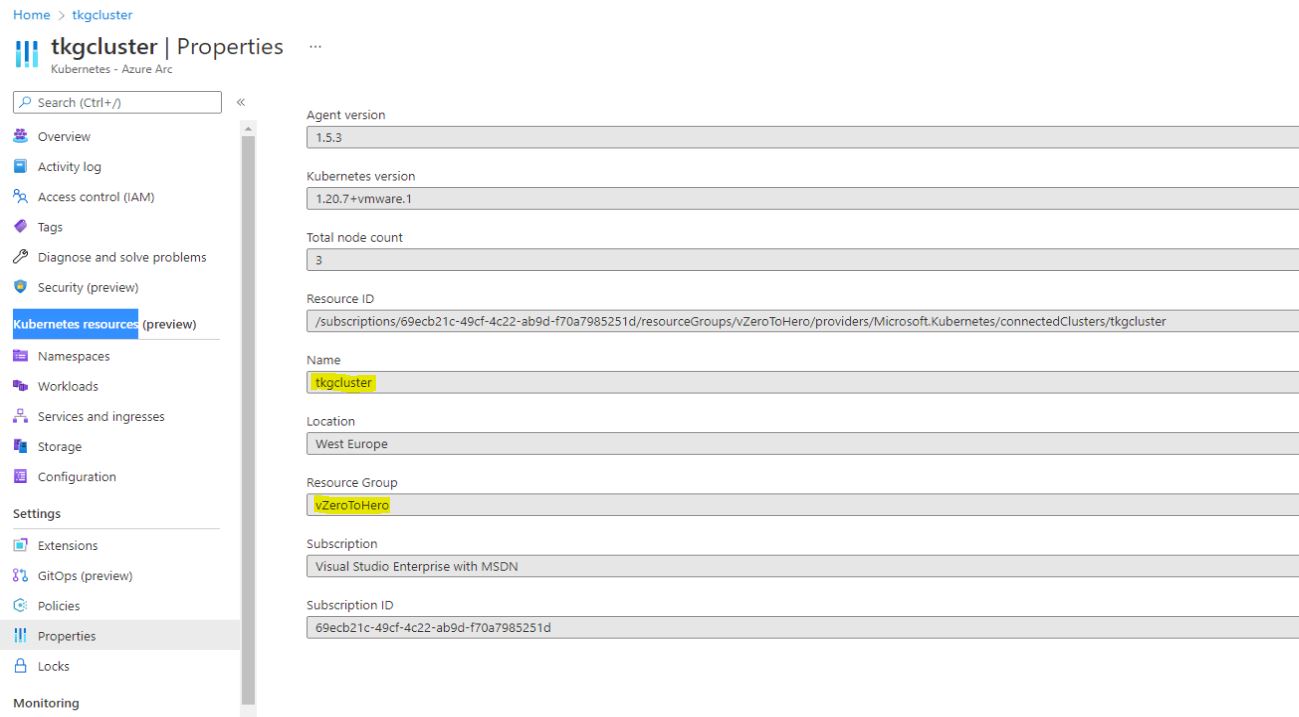
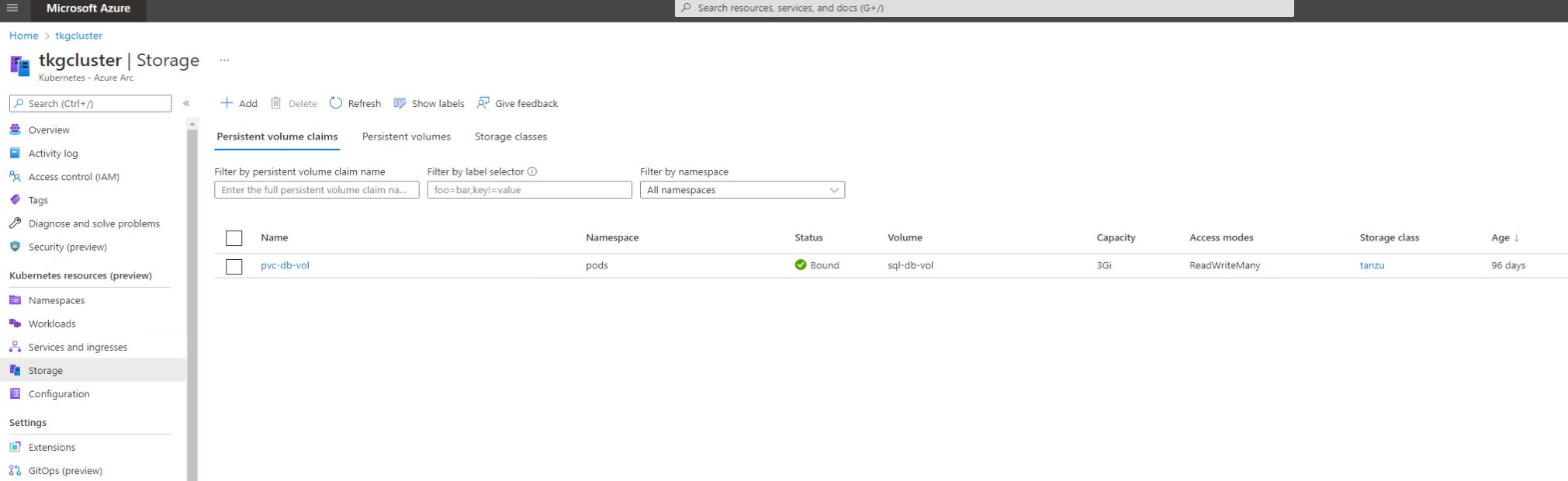
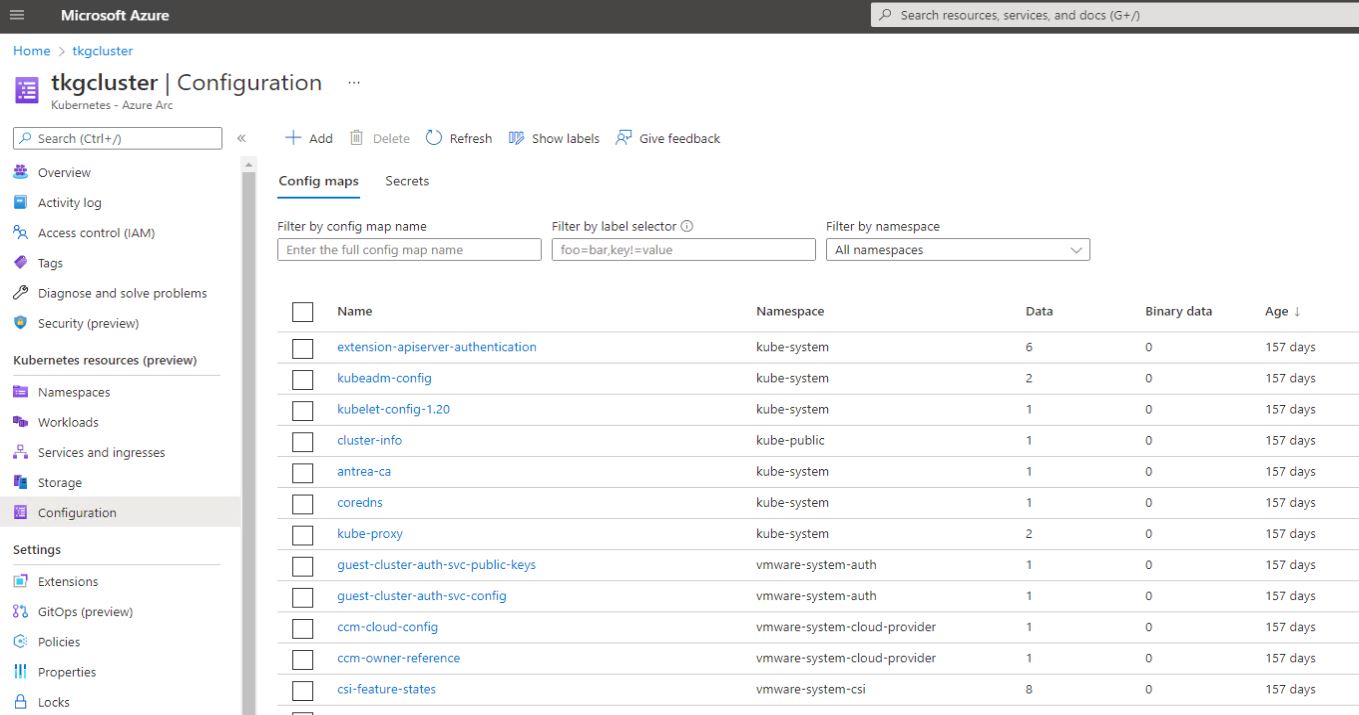
In our previous post Connect VMware Tanzu with Azure Arc , we connected VMware vSphere with Tanzu Kubernetes Grid Cluster to Microsoft Azure Arc which provided some features around tagging, inventory, logging, policy mgmt. and others but lacked visibility into the cluster workloads, namespaces, and other Kubernetes objects. Since then, Microsoft has enabled a preview feature named “Kubernetes Resources” which gives easy access to namespaces, pods, storage, configuration and services .
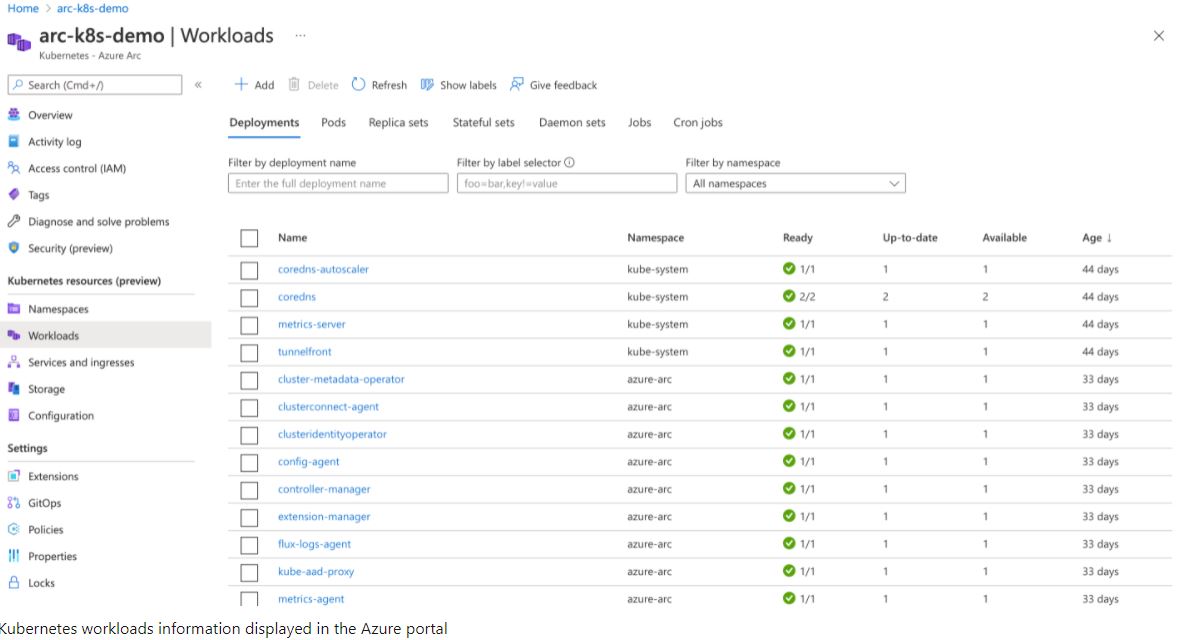
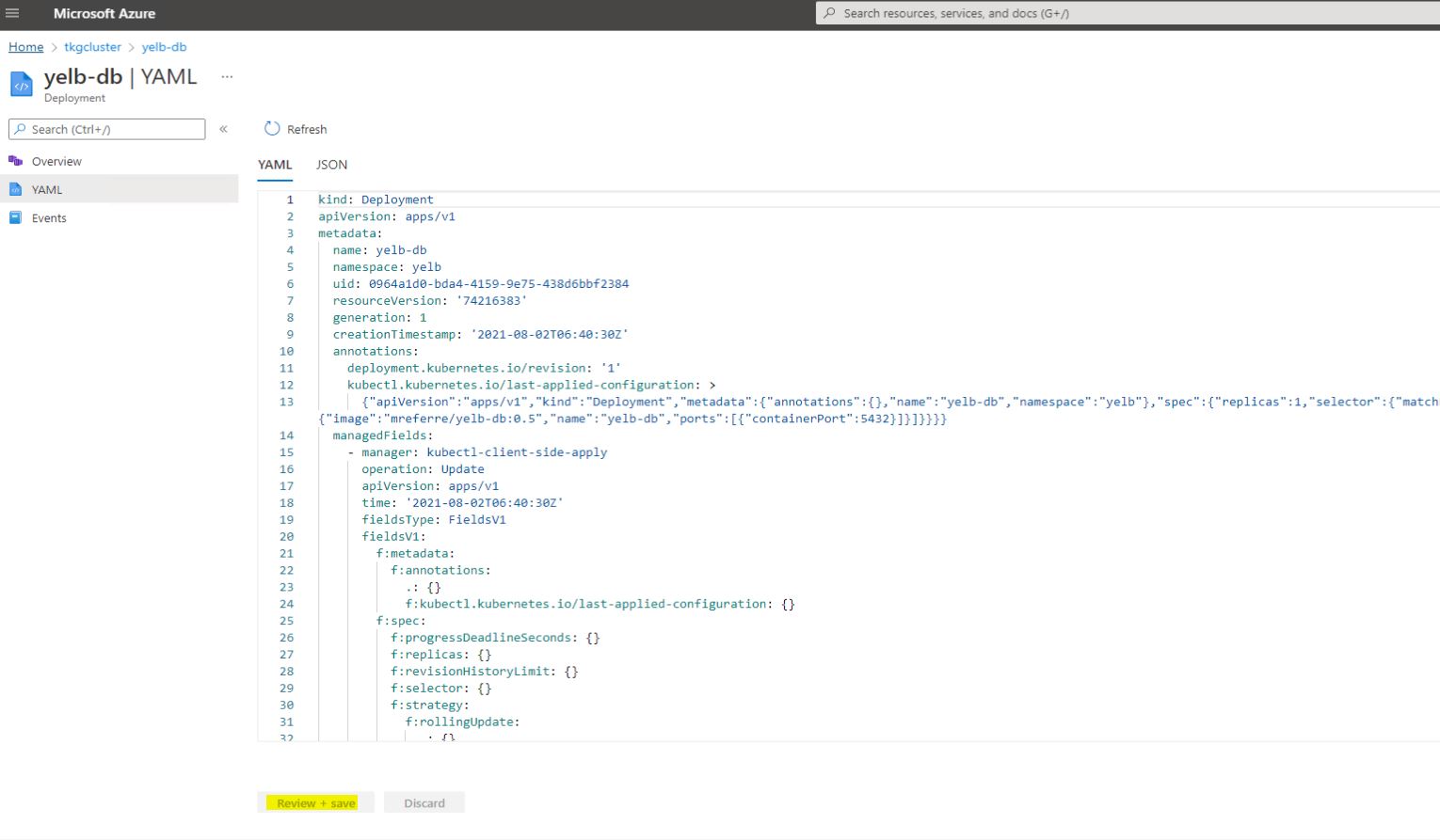
“The Azure portal includes a Kubernetes resource view for easy access to the Kubernetes resources in your Azure Arc-enabled Kubernetes cluster. Viewing Kubernetes resources from the Azure portal reduces context switching between the Azure portal and the Kubecttl command-line tool, streamlining the experience for viewing and editing your Kubernetes resources. The resource viewer currently includes multiple resource types, such as deployments, pods, and replica sets .”
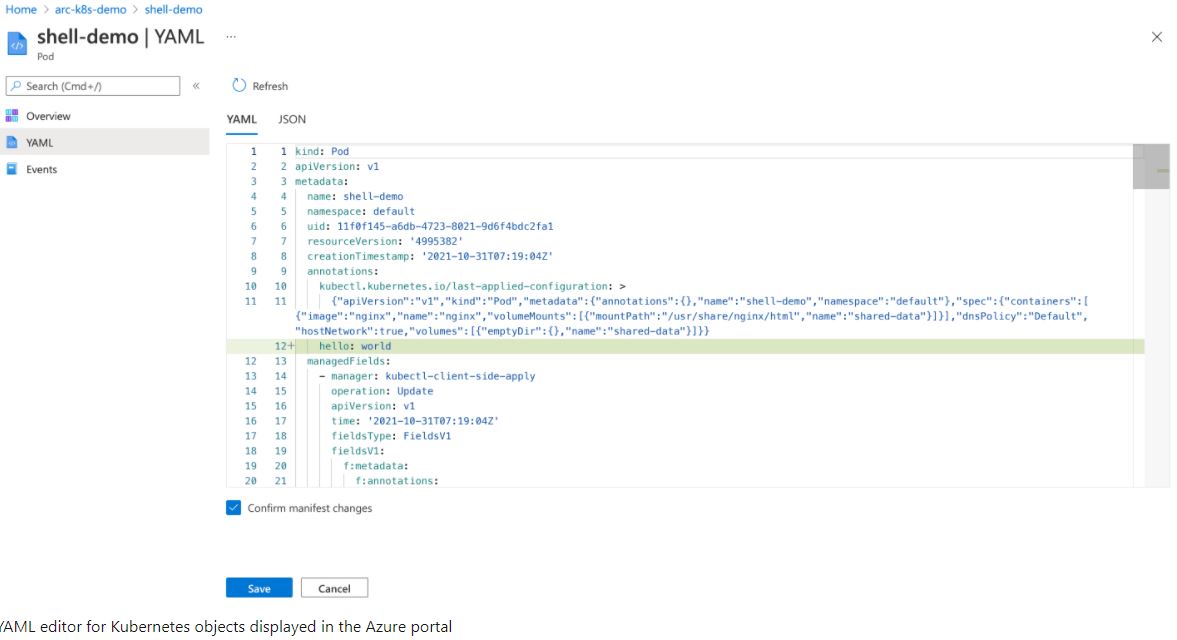
The Kubernetes resource view also includes a YAML editor. A built-in YAML editor means you can update Kubernetes objects from within the portal and apply changes immediately. That been said, a very good comment made by Microsoft is worth noting: Performing direct production changes via UI or CLI is not recommended and you should consider using Configurations (GitOps) for production environments. The Azure portal Kubernetes management capabilities and the YAML editor are built for learning and flighting new deployments in a development and testing setting .
Configure
The configuration steps are not specific to VMware Tanzu so should work for any Arc connected Kubernetes Cluster. The documentation can be found here Access Kubernetes Resources from Azure Portal .
- Install or upgrade Azure CLI to version >= 2.16.0 and <= 2.29.0
- Install the connectedk8s Azure CLI extension of version >= 1.2.0
az extension add –name connectedk8s
- If you’ve already installed the
connectedk8sextension, update the extension to the latest version:
az extension update –name connectedk8s
- An existing Azure Arc-enabled Kubernetes connected cluster using the following guide: Connect Tanzu with Azure Arc . Agents upgrade automatically never the less verify Upgrading your agents to version >= 1.5.3 at least .
- Enable the below endpoints for outbound access in addition to the ones mentioned under connecting a Kubernetes cluster to Azure Arc:
| Endpoint | Port |
|---|---|
*.servicebus.windows.net |
443 |
guestnotificationservice.azure.com, *.guestnotificationservice.azure.com |
443 |
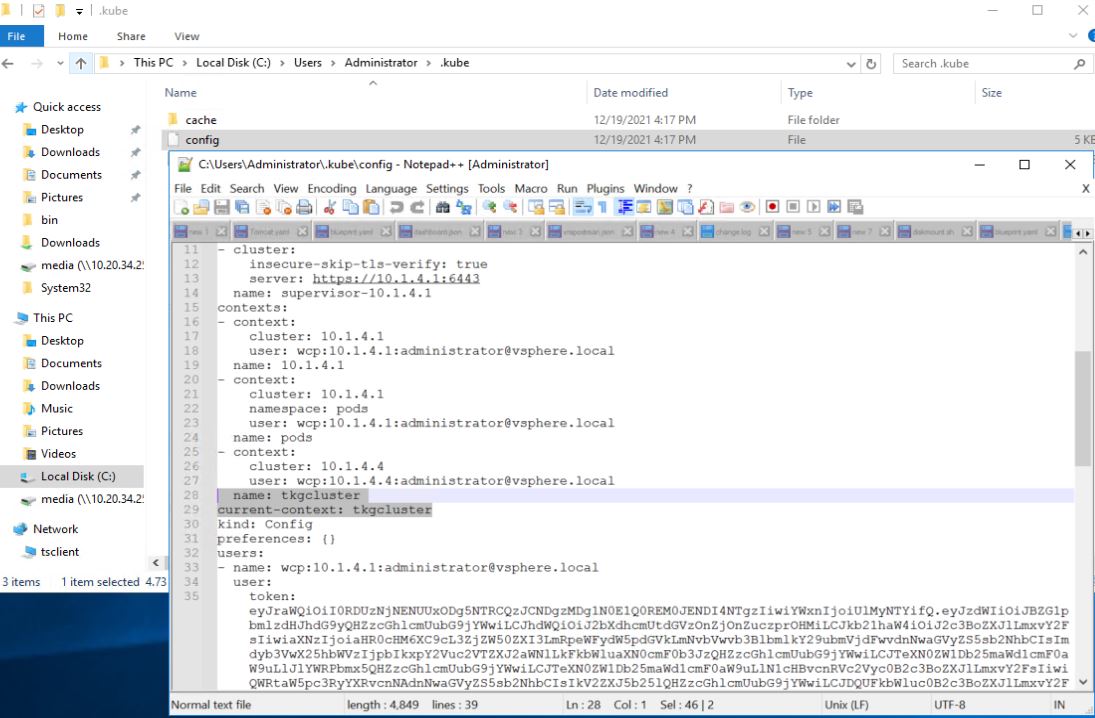
- Make sure that your kubeconfig file is pointing to your TKG cluster namespace context and that your are logged into your TKG cluster with admin privilages.
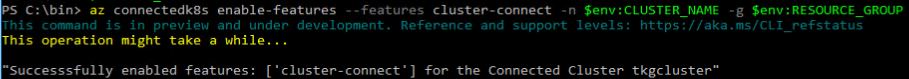
- Make sure you are connected to your Azure subscription and Enable the Azure Cluster Connect feature (I used PS variables but you can just enter the names):
az connectedk8s enable-features –features cluster-connect -n KUBERNETES_CLUSTER_NAME -g AZURE_RESOURCE_GROUP_NAME
- Now we need to create a service account with token authentication and provide the right level of permissions so that all objects are visible within Azure Arc. Create a service account user:
kubectl create serviceaccount admin-user
![]()
- Create a ClusterRoleBinding to grant the created service account permission on the cluster, I will use the cluster-admin role.
kubectl create clusterrolebinding root-cluster-admin-binding –clusterrole=cluster-admin –user=admin-user
![]()
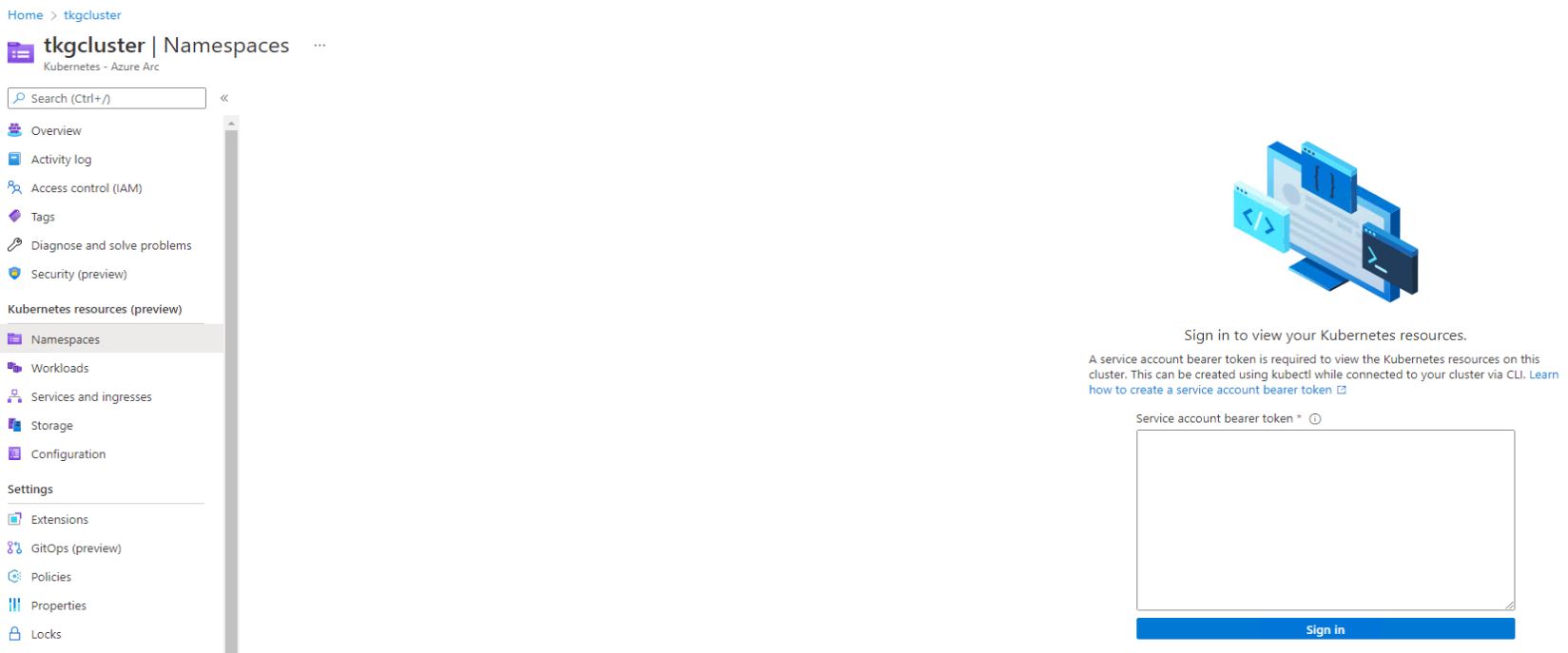
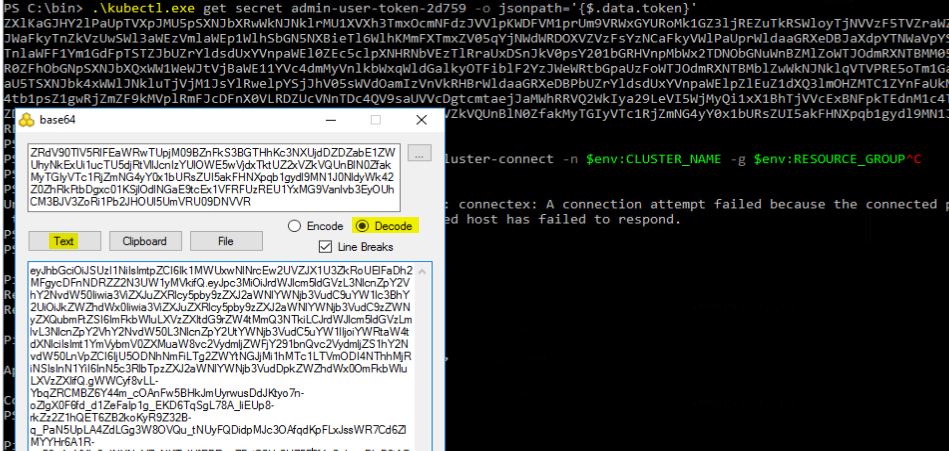
- Now we need to get the service token and decode it so that we can use it on the azure portal to authenticate to the Kubernetes cluster. Note the service account name generated in the first command to be used in the second one.
kubectl get serviceaccount admin-user -o jsonpath='{$.secrets[0].name}’
![]()
kubectl get secret admin-user-token-2d759 -o jsonpath='{$.data.token}’
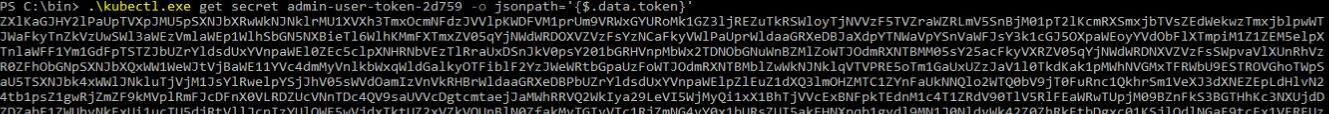
- Download Base64 and insert the above generated token then decode the same into text after which it will be pasted in the Azure portal to Sign-in.

Verify
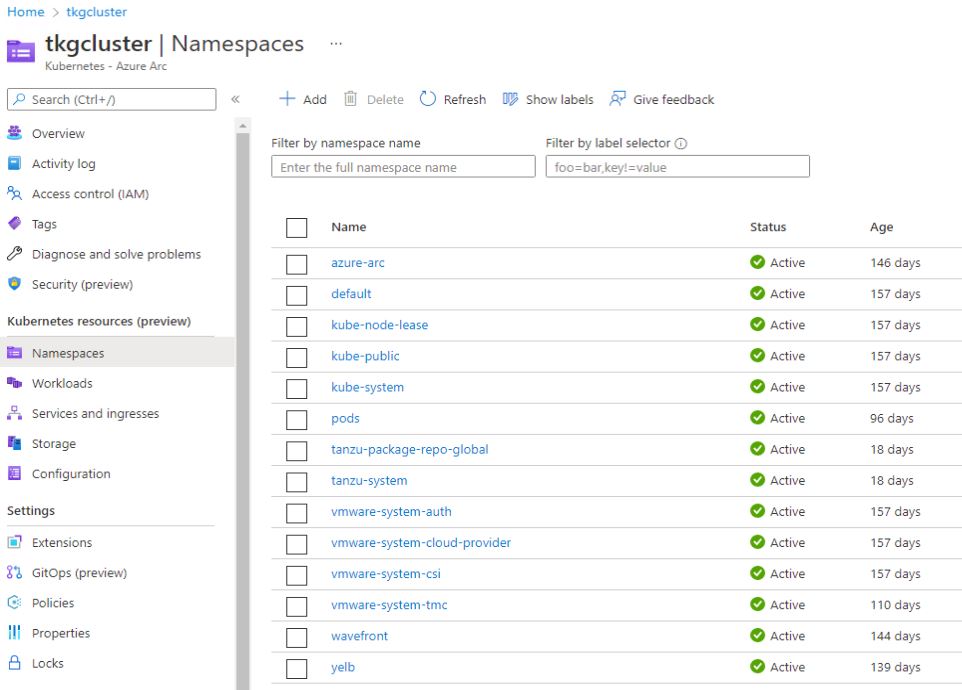
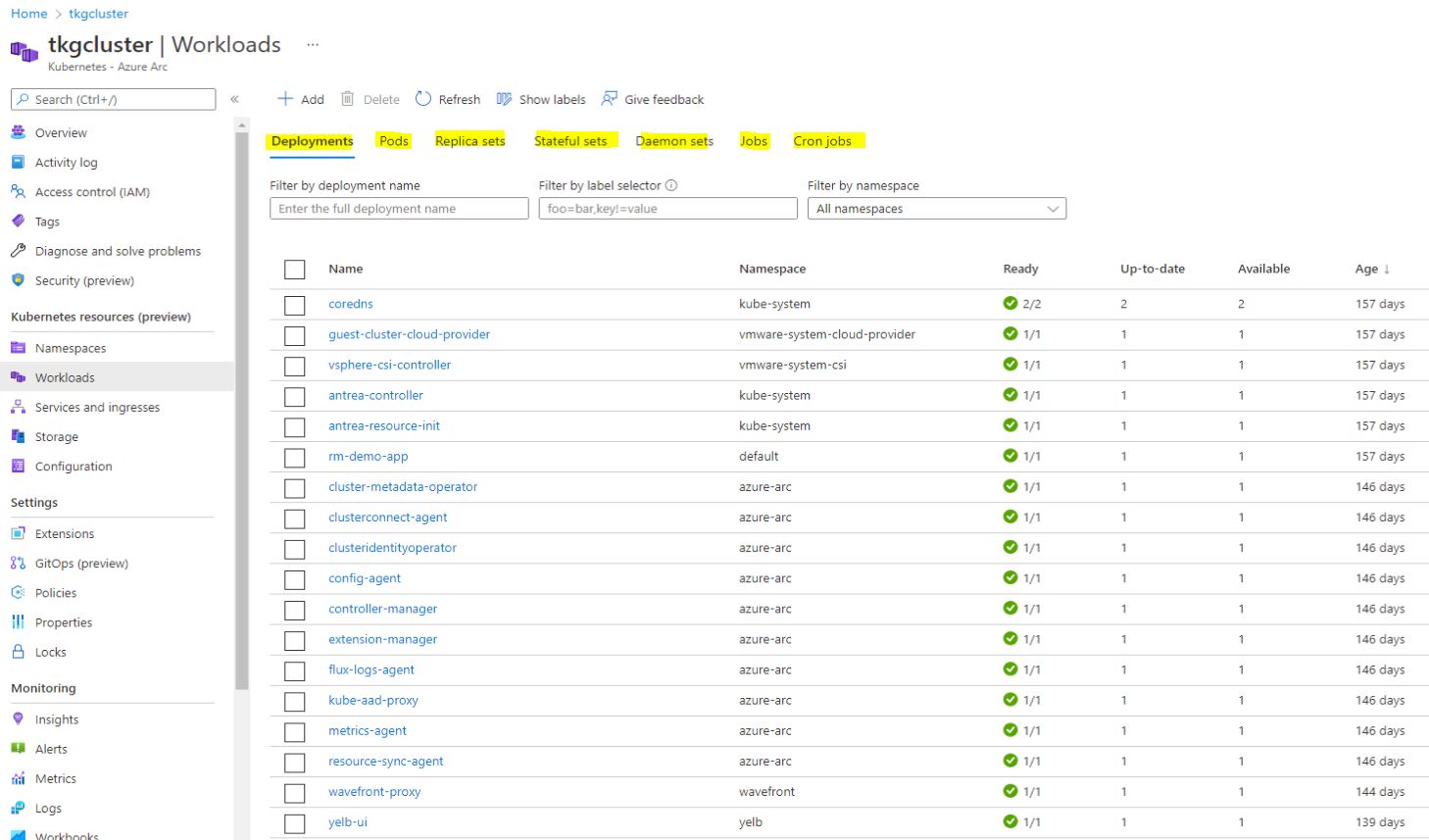
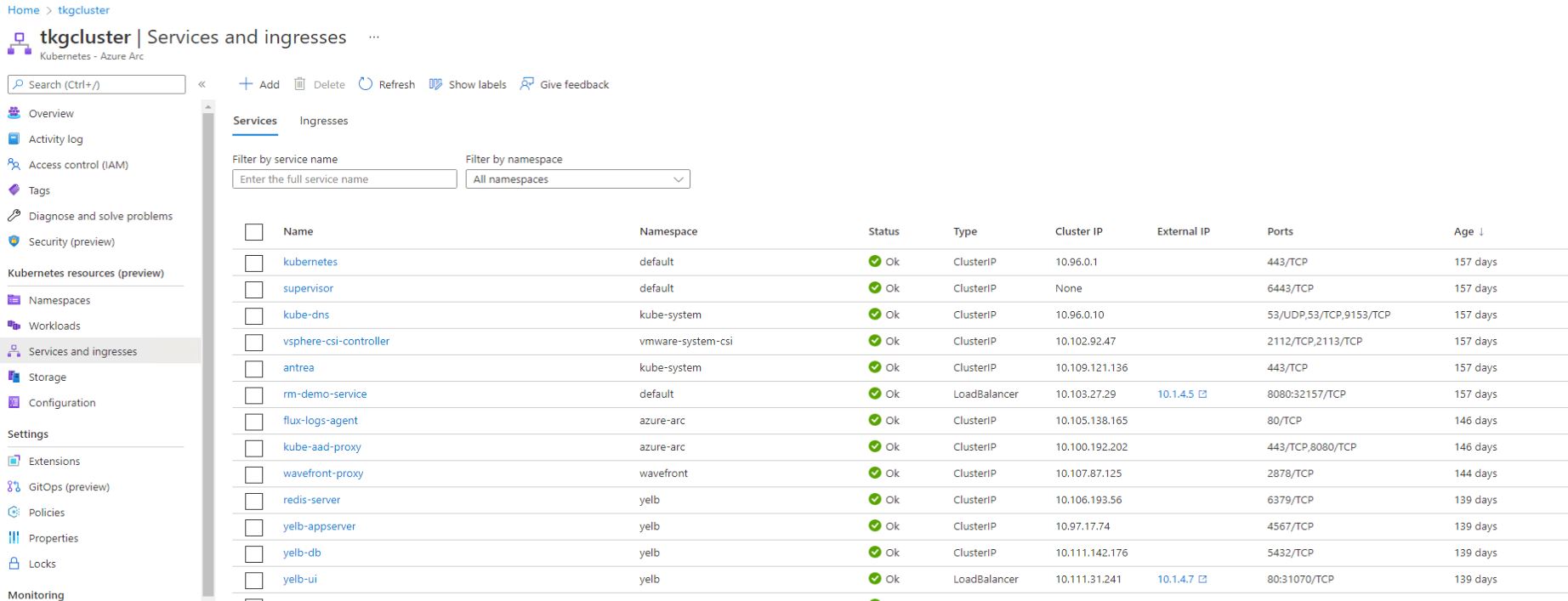
Now you can see namespaces, workloads, services, storage, and configuration including drill-down information on all. On top of being able to edit YAML files for workloads directly from the GUI.
Conclusion
As Multi-Cloud picks up especially for cloud native strategies, tools such as Azure Arc and VMware Tanzu Mission Control become more of a necessity rather than a luxury. I will be exploring some other integration points between vSphere with Tanzu and Microsoft Arc and afterwards start a series on Tanzu Mission Control which is a much more focused tool on Kubernetes rather than every other resource in the infrastructure. I hope this has been proof enough that vendor lock-in within the cloud native world is not a thing, that is by design not by choice 🙂 .
great article
Thanks Hesham .