Introduction:
In this ever-changing Information Technology space, one needs to stay up to date or risk becoming obsolete. After the release of NSX-T Data Center 2.4, I decided to take a closer look at the product and see what the hype is all about especially what vendors like to call nowadays cloud native applications and how NSX-T fits into that picture.
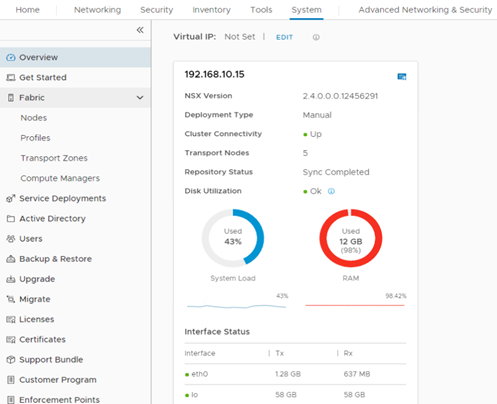
NSX-T 2.4 Data Center introduced very important features, two of which I found very pleasant, that is combining NSX-T Manger with controllers inside the same appliance and the ability to create an NSX-T Manager Cluster Natively.
The challenge in approaching different variations of products that have different architectures is not that easy and you find yourselves always mapping old concepts with new concepts which of course adds to the confusion.
In this small post, I would like to add small configuration snippets just to remind me of some of the NSX-T concepts and I will start with configuring BGP between NSX-T virtual switches networks and the physical network. I might be mistaken or not following best practices here so make sure you customize as per your needs and let me know to do the same.
Many amazing blogs exist our there detailing different NSX-T configurations yet I took a blind approach to my lab just to continually mess-up, fix it, and learn the hard way. I did ask many colleagues about different areas of the configuration and architecture which just shows the power of community.
Lab:
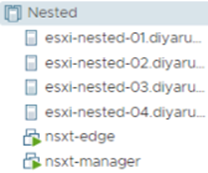
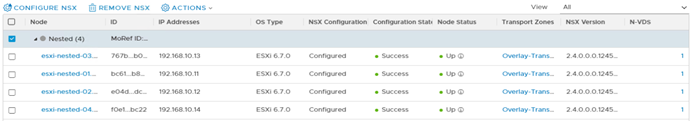
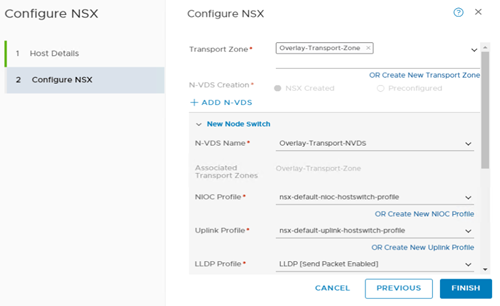
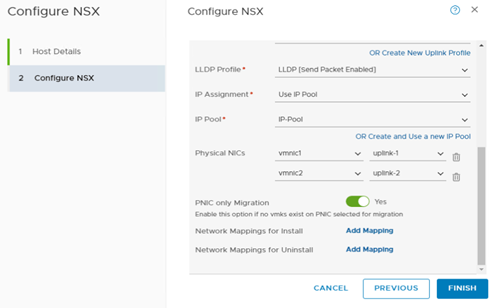
4 x ESXi 6.7u1 nested vSAN Cluster ( Fully updated ) with 2 free physical NICs for NSX-T N-VDS. I had to prep each server for NSX-T independently by “Configure NSX” for every host transport node under my vCenter and choosing the physical NIC mapping.
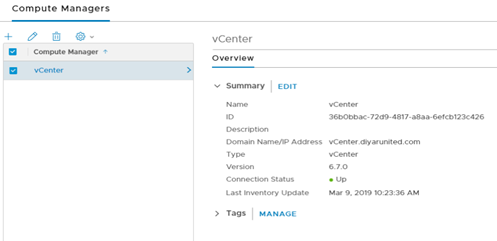
1 x vCenter 6.7u1 ( Fully Updated ).
1 x NSX-T Manager.
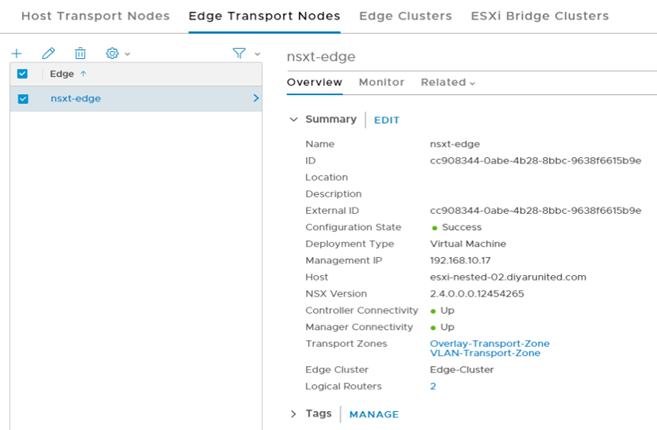
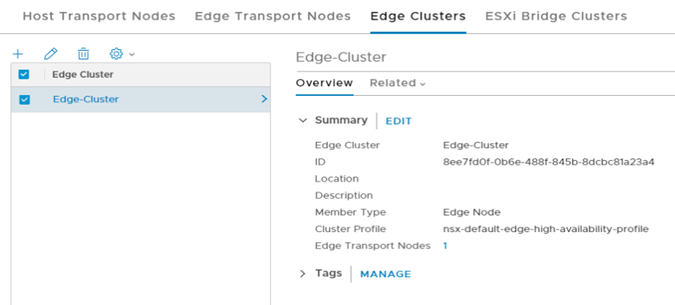
1 x NSX-T Edge Transport Node which is part of both Transport Zones since it needs to talk to the physical network when the Tier-0 Router is configured.
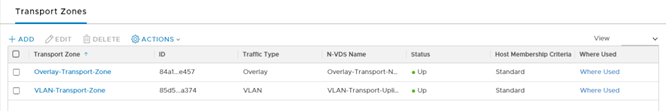
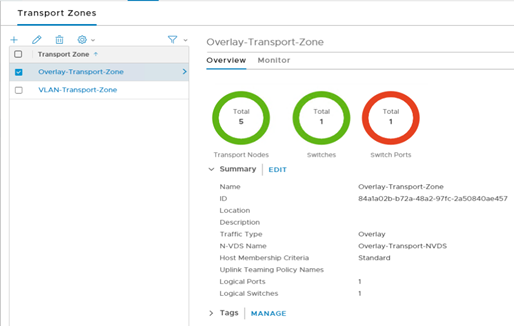
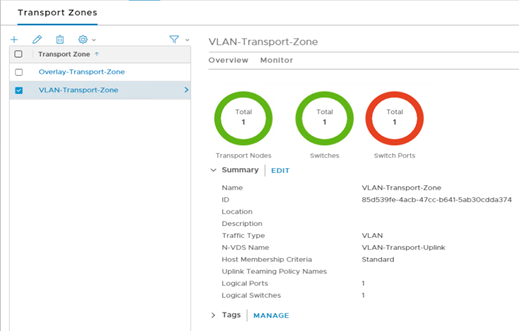
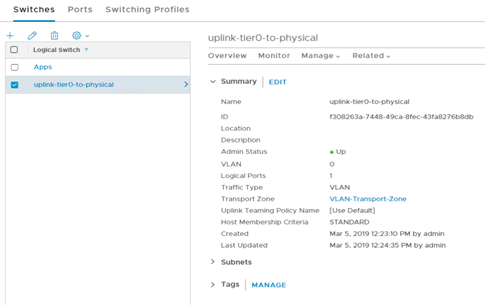
2 x Transport Zones. One for NSX-T virtual networks and one for physical uplink to my physical network. I have a flat network so the VLAN-Transport-Zone is on VLAN 0. I have used default profiles.
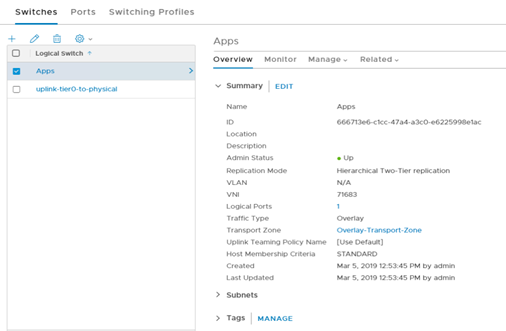
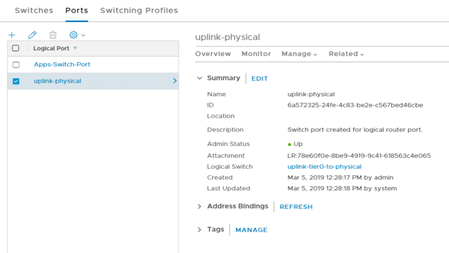
2 x Virtual Switches. One is on the Overlay Transport Zone for internal NSX-T virtual networks and the other is part of the VLAN Transport Zone which will act as the uplink to physical network.
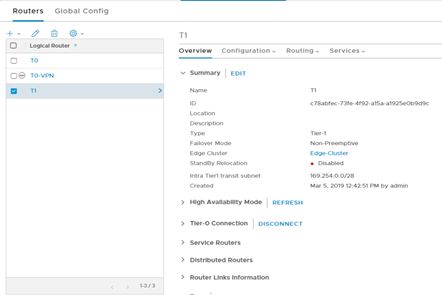
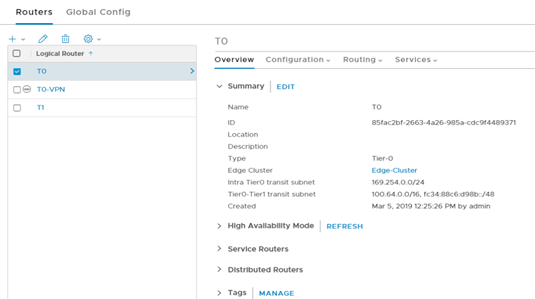
2 x Logical Routers. Tier-1 router for routing internal virtual switches and Tier-0 router for routing to external physical network.
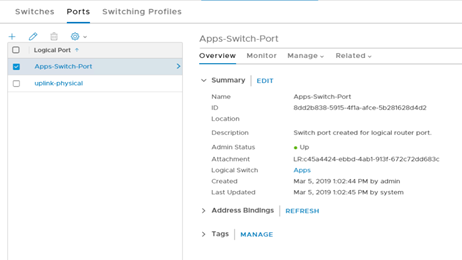
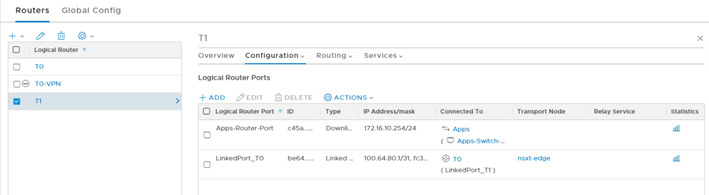
Tier-1 Router has 2 Logical ports, one for routing virtual switches and the second for connecting to the Tier-0 router which is created by default.
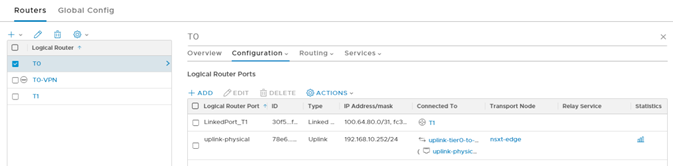
Tier-0 Router has 2 logical ports, one for connecting to the Tier-1 router which is created automatically and one for connecting to the physical network which will have the Tier-0 IP on the physical network subnet.
Configuration:
Currently no routing is configured in the lab so the physical network cannot communicate with the virtual switch “Apps” I created routed on the Tier-1 router with a subnet of 172.16.10.0/24 .
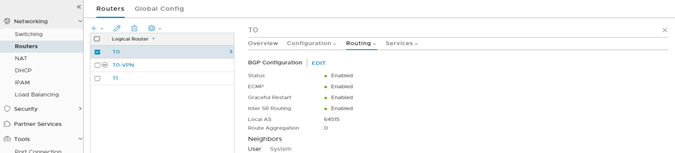
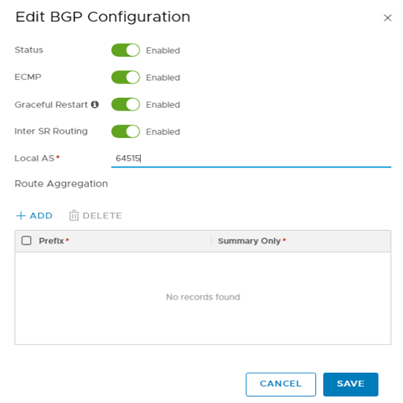
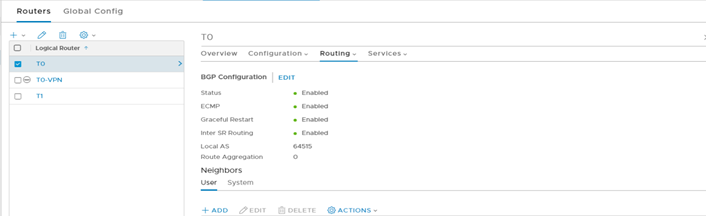
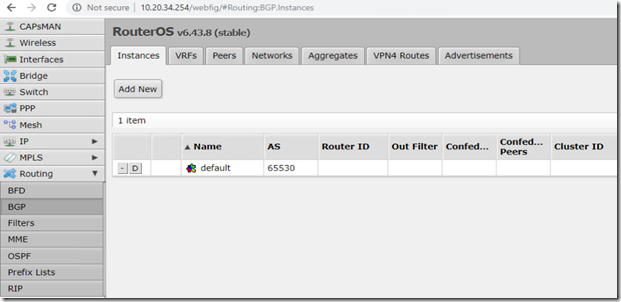
Step 1: Head over to Tier-0 Logical Router, Routing, BGP, and enable all BGP services with providing an Local AS. Since this is am external BGP so the Local AS numbers must be different. Also note that in NSX-T, no internal BGP needs to be configured between Tier-0 and Tier-1 so just enabling BGP on Tier-1 would do the needful.
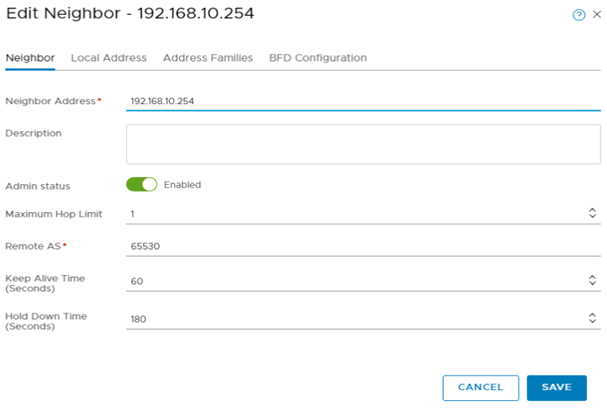
Click on ADD under Route Aggregation and lets add the IP of the gateway of the physical router and its Remote AS. This will be configured as the Local AS on the physical router which in my case is a MikroTik Router.
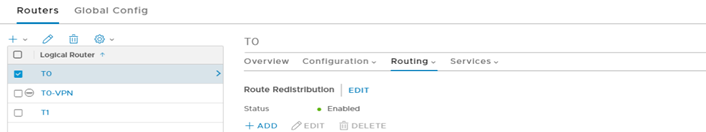
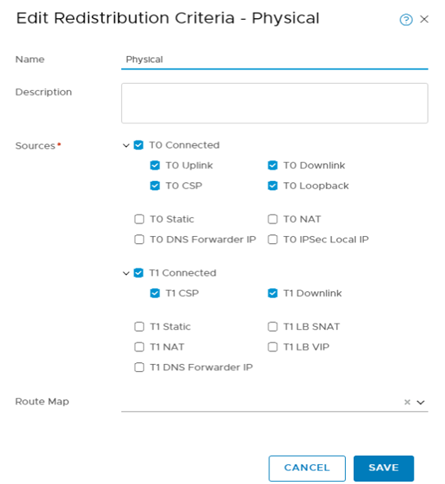
Step 2 : Head over to Tier-0 Logical Router, Routing, Route Redistribution, ADD.
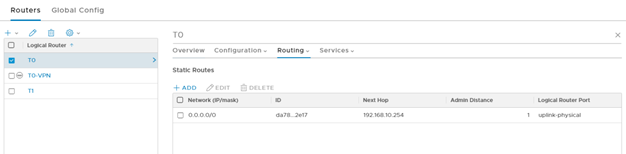
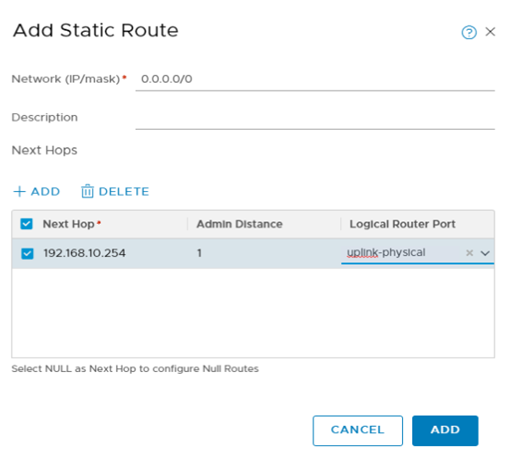
Add a static route on the Tier-0 router pointing to the physical network gateway IP.
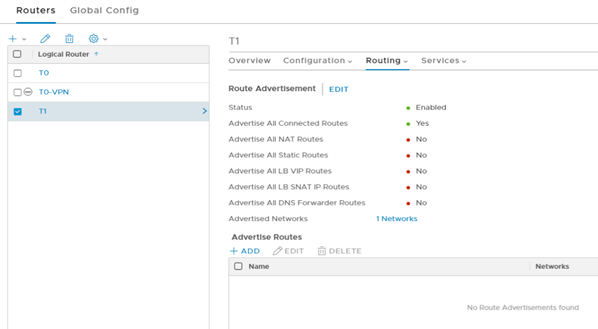
Step 3: Head over to Tier-1 Router, Route Advertisement, and enable Advertise all connected routes.
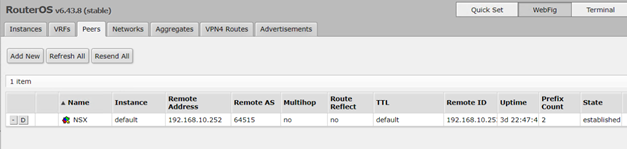
Step 4: Head over to your physical router and configure BGP. Make sure the Local AS is correct as specified in the Remote AS section of the Tier-0 Router configuration and add a Peer which will be the IP of the Tier-0 Router plus its Local AS number. Give it couple of seconds and it should show as established and we are able to ping the gateway IP of the virtual switch routed on the Tier-1 router for network “Apps” from a PC on the physical network.
You can also login to the NSX-T Edge VM and run “ show IP BGP “ to get the routes advertised and learned through BGP protocol.
Conclusion:
As soon as you grasp the different architecture terminology of NSX-T in comparison with NSX-V, it becomes easier to learn and implement. Dynamic routing is much easier to configure than NSX-V when all components are in place.
May the Peace, Mercy, and Blessing of God Be Upon You