Introduction:
Norskale acquisition now Citrix Environment Management is by far the best purchase Citrix has made in years ( Until UniDesk App Layering Is Citrix Ready ). The only part missing from the VDI/SBC portfolio was a decent User Environment Management product native to Citrix that provided customers with an comprehensive EUC solution from a single vendor.
VMware knew they lacked in VDI/SBC core functionality against Citrix so simply enough they led with App Volumes and User Environment Manager which proved to be a winning move. Citrix responded with the acquisition of Norskale and UniDesk which are significant because both have technical advantages over App Volumes/UEM (CPU, Memory, IO optimizations) never the less are still behind in specific areas like profile management, application profiling, GP integration, User Layers (writable volumes), and management integration.
VMware also had the famous Optimization tool until at last Martin and the team from Citrix put an overnight effort to create one of their own “Citrix Optimizer” currently in technical preview but works perfectly which just makes absolute sense … No idea what took so long ! Thank you Martin Zugec ![]() .
.
Back to our subject, WEM should be implemented in every VDI environment, I pitch it for all customers as an integral part of the overall architecture, and as the product development progresses so will the use cases and ultimately adoption. Speed login times (10 seconds achievable), optimize/accelerate virtual desktops, granular policy control, no GPOs, no Login scripts, better security, and most importantly no requests to AD/GP team every time a change is required ![]() .
.
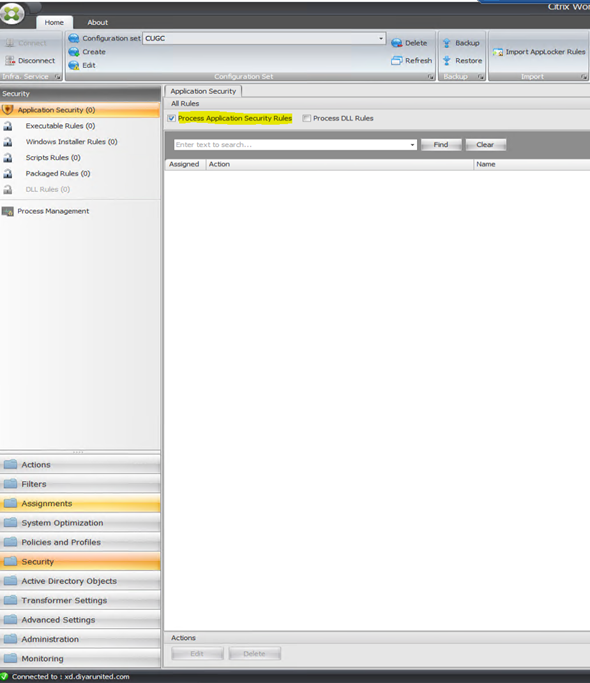
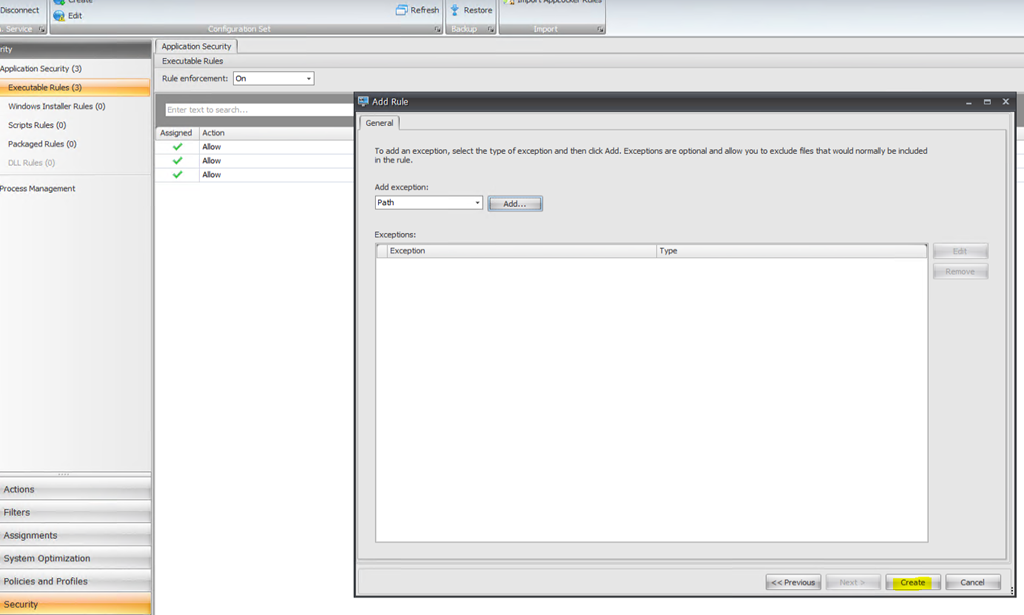
A new feature of WEM v-4-04-50 currently in technical preview simplifies and enhances the management of application security by utilizing Microsoft App Locker which can restrict files that users or groups are allowed to run based on executable files, scripts, Windows Installer files, dynamic-link libraries (DLLs), packaged apps, and packaged app installers. It can also run in audit (monitor) mode or prevent mode for every type of rule. WEM natively allows for process management as well thus making this a very strong application security tool.
App Locker was introduced back in Windows 7 for free by Microsoft allowing whitelisting/blacklisting of applications on both desktop and server. It is completely managed through group policy which makes management a bit of a hassle having to create only one rule at a time and assign to user/group with no ability to search or do bulk editing on top of having to manage/update group policy. An additional use case from an VDI/SBC perspective is the ability to install all software on base image and control user access to each (not the same as application masking because the OS/User still loads/sees the application).
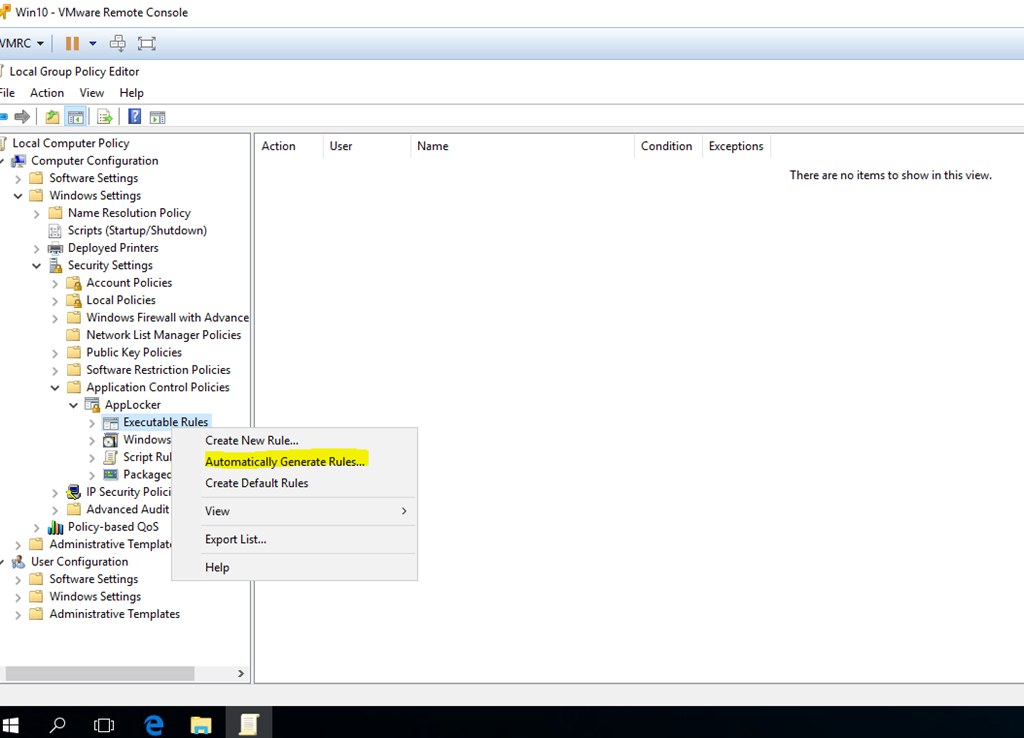
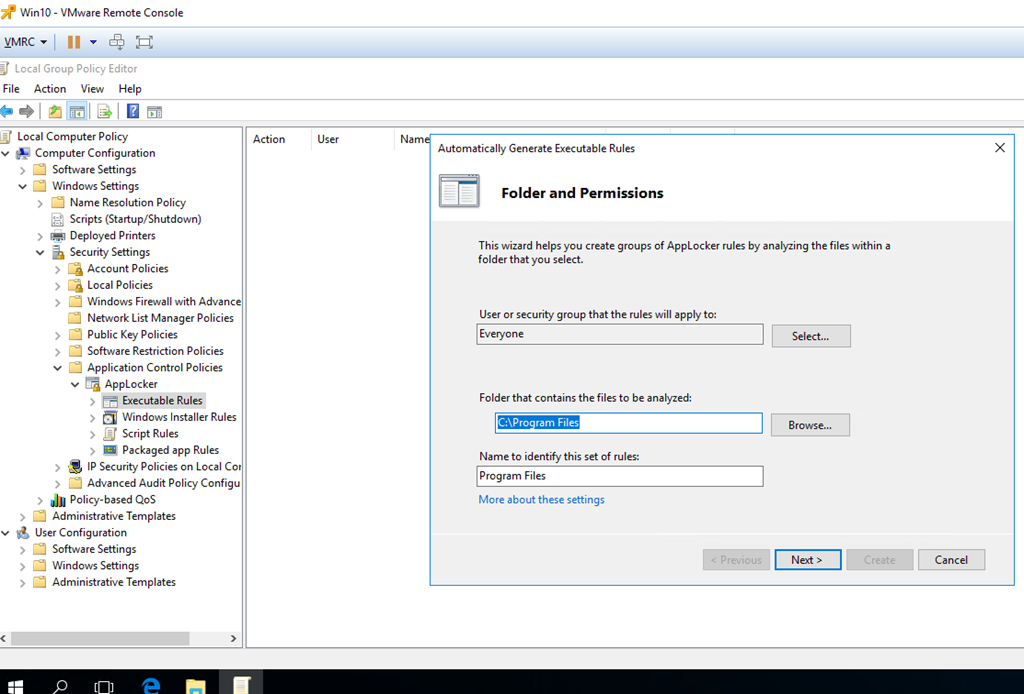
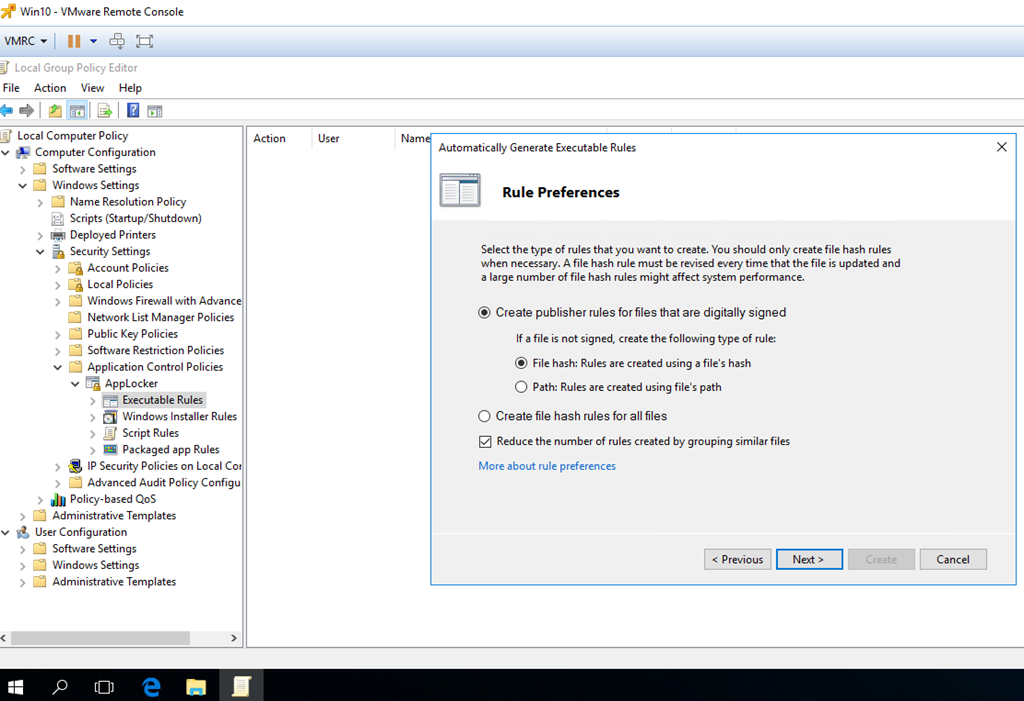
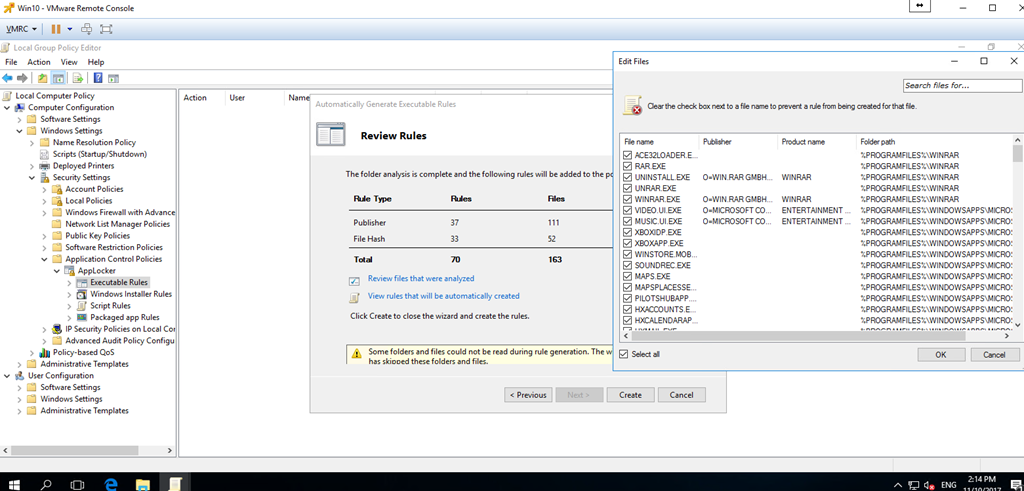
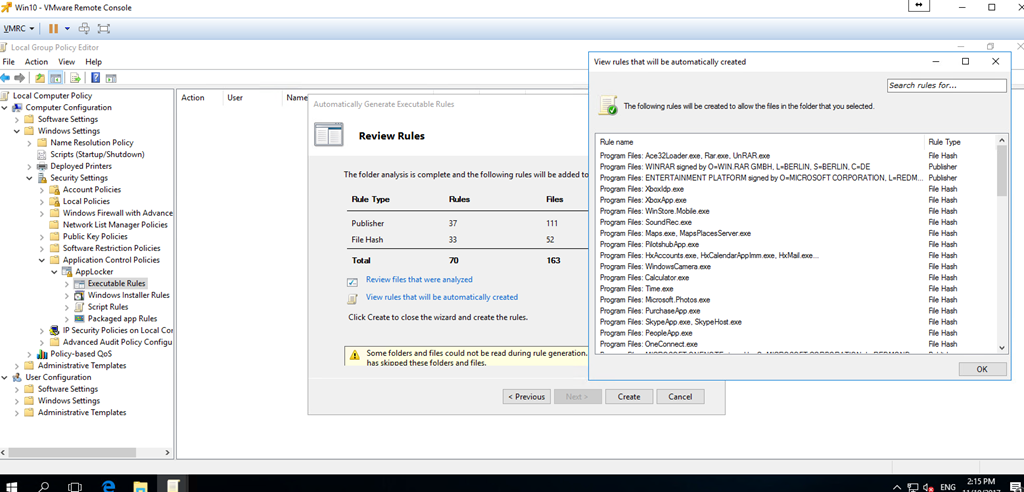
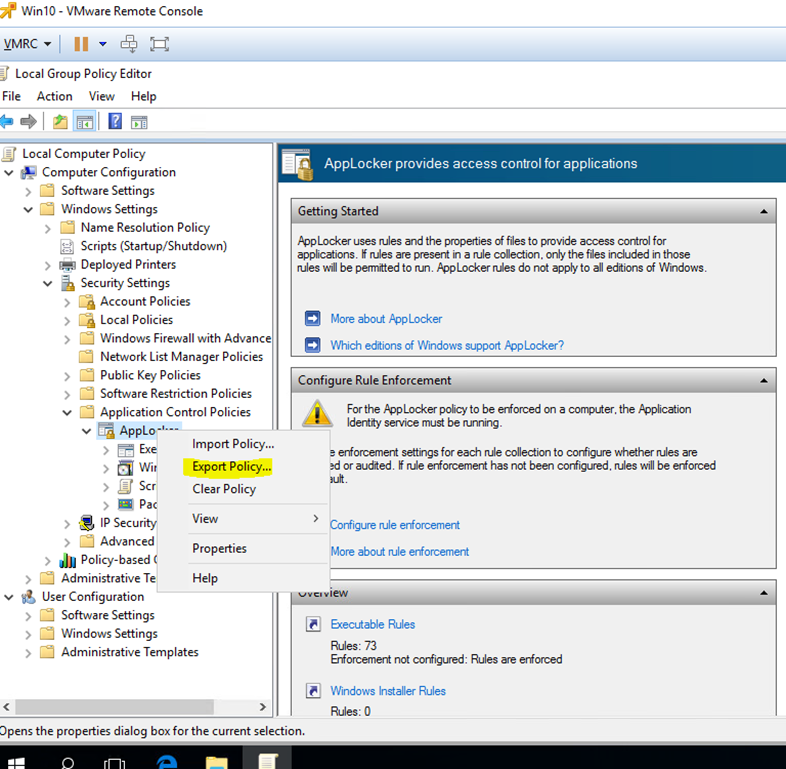
One small feature of App Locker not yet in WEM is the ability to automatically generate rules which scans a folder for different applications, packages, Installers, and Scripts then provide rules for each using digital signature, file hash, and file path. fear not as rules can be easily exported from group policy and imported into WEM. DLL rules can also be utilized but is a risky business because If you use DLL rules, a DLL allow rule has to be created for each DLL that is used by all of the allowed apps and users may experience a reduction in performance if DLL rules are used.
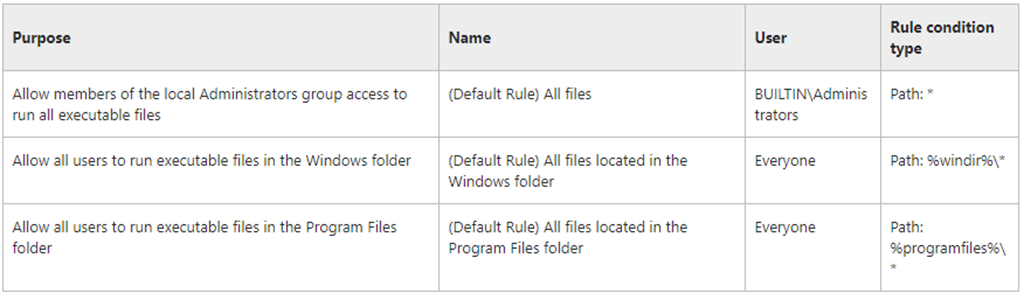
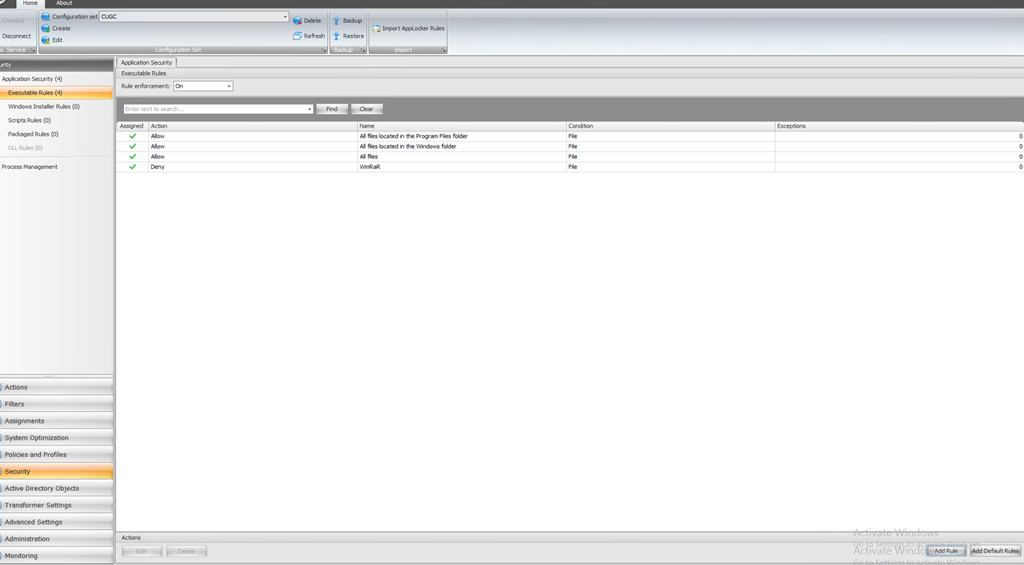
WEM App Security utilizes App Locker default rules that by default allow interaction with file system when it is enabled because without default rules when policies are enforced everything will stop being accessible. Note that Deny rules always takes precedence over Allow rules. We can create default rules then deny rules assigned to apps for certain users/groups and we can also use deny/allow rules with exceptions as well.
Configure:
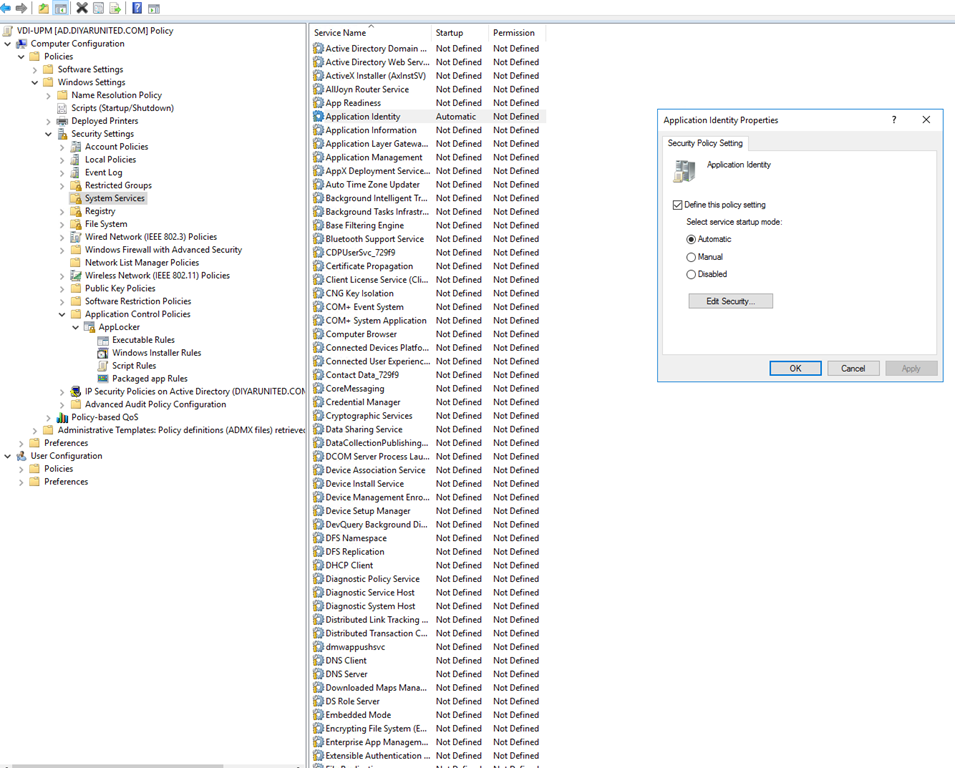
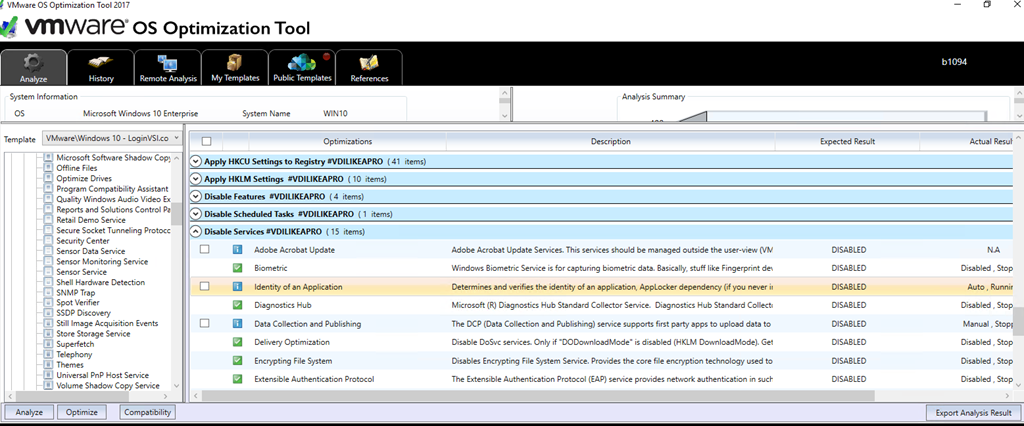
Step 1: Set “Application Identity” service to Automatic Start using Group Policy applying to virtual desktops. Note that Citrix Optimizer does not disable this service by default but VMware Optimizer Windows 10 LoginVSI template does so be careful.
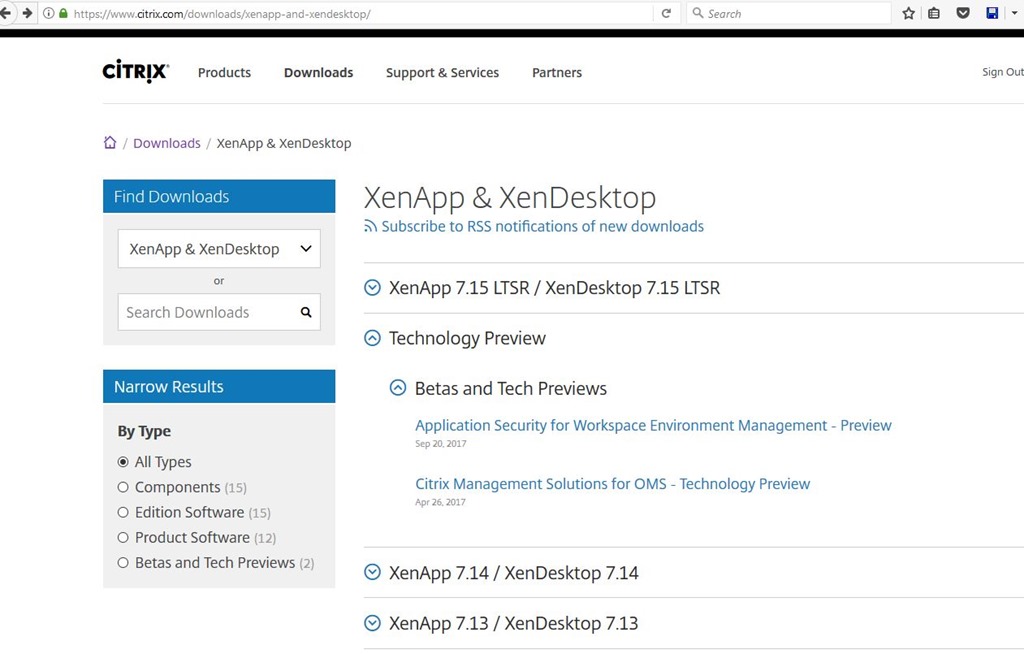
Step 2: Download and Install Citrix WEM Application Security technical preview v-4-04-50 . Follow CTA fellow members George Spiers and Christiaan Brinkhoff posts on how to install/configure WEM.
Step 3: Enable Process Application Security Rules in WEM security tab. Only enable Process DLL Rules if you know exactly what it does and can add all your apps related DLLs.
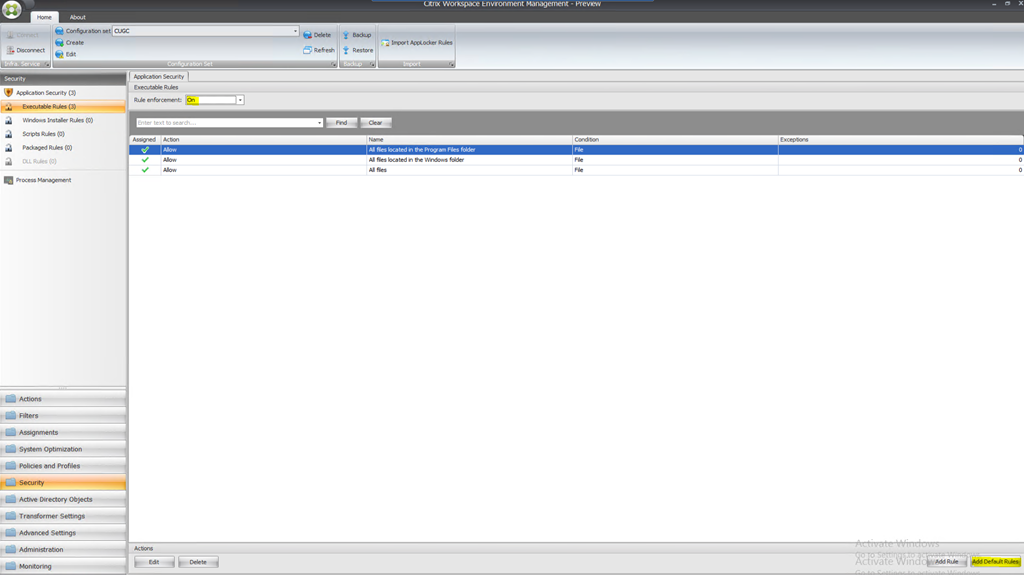
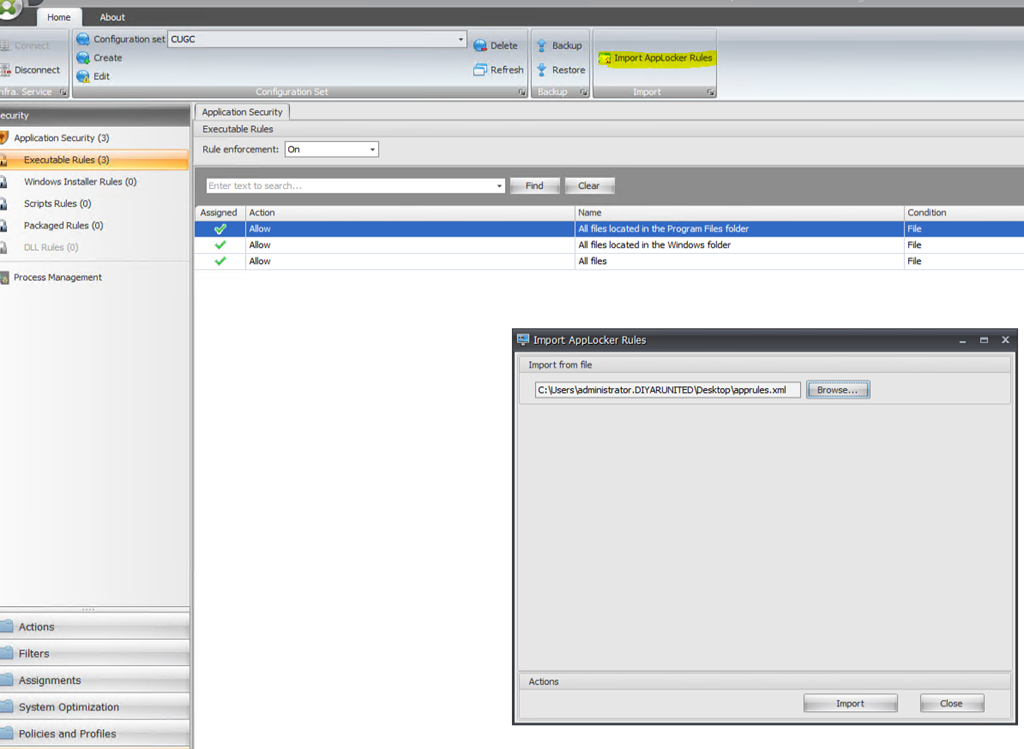
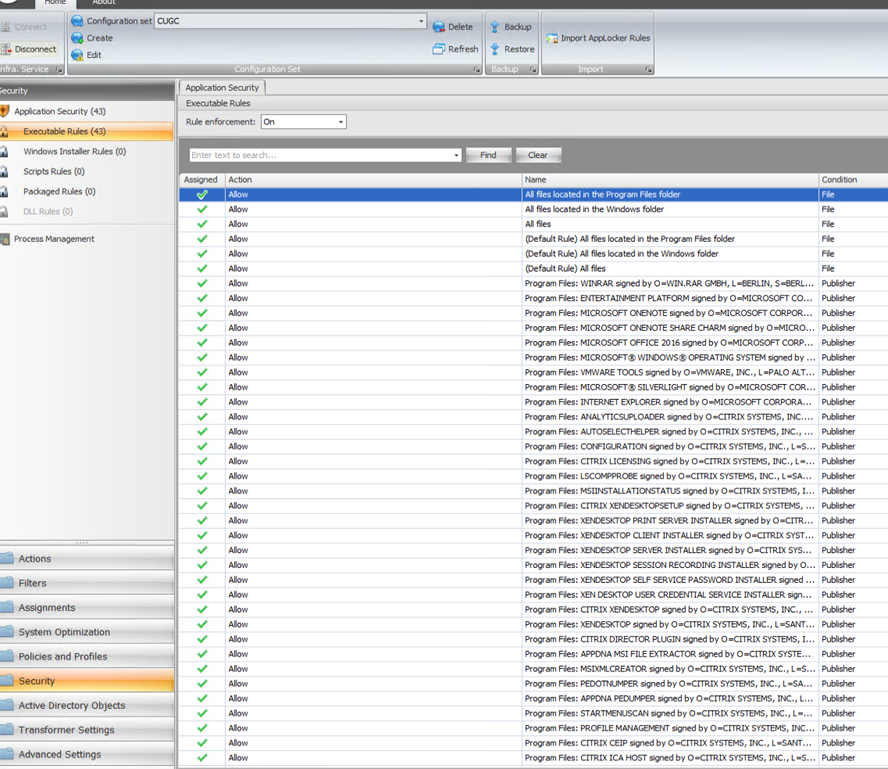
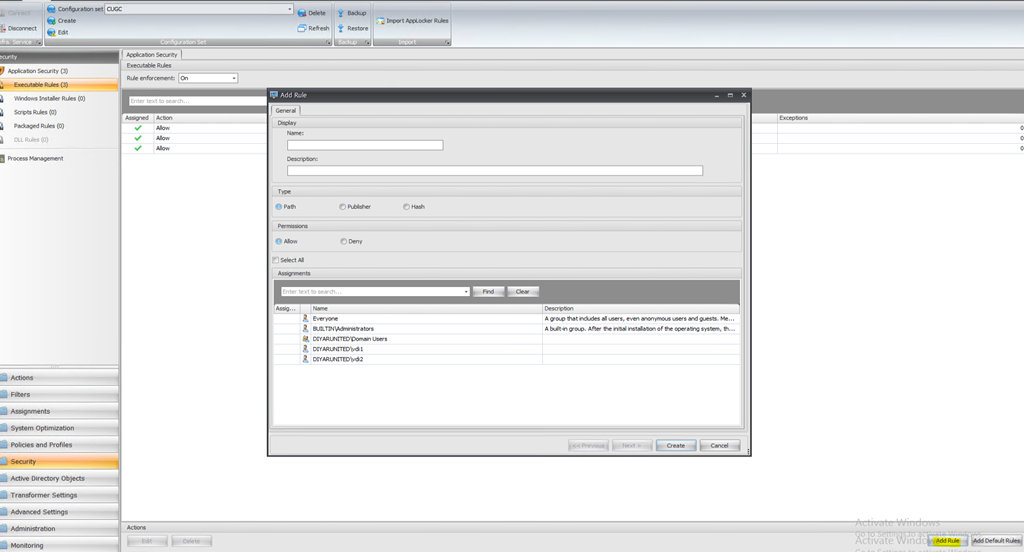
Step 4: In Executable Rules down in the right Add Default Rules and on the top set Rule Enforcement to On to enforce rules or Audit to monitor rules effect. Default Rules have the following permissions.
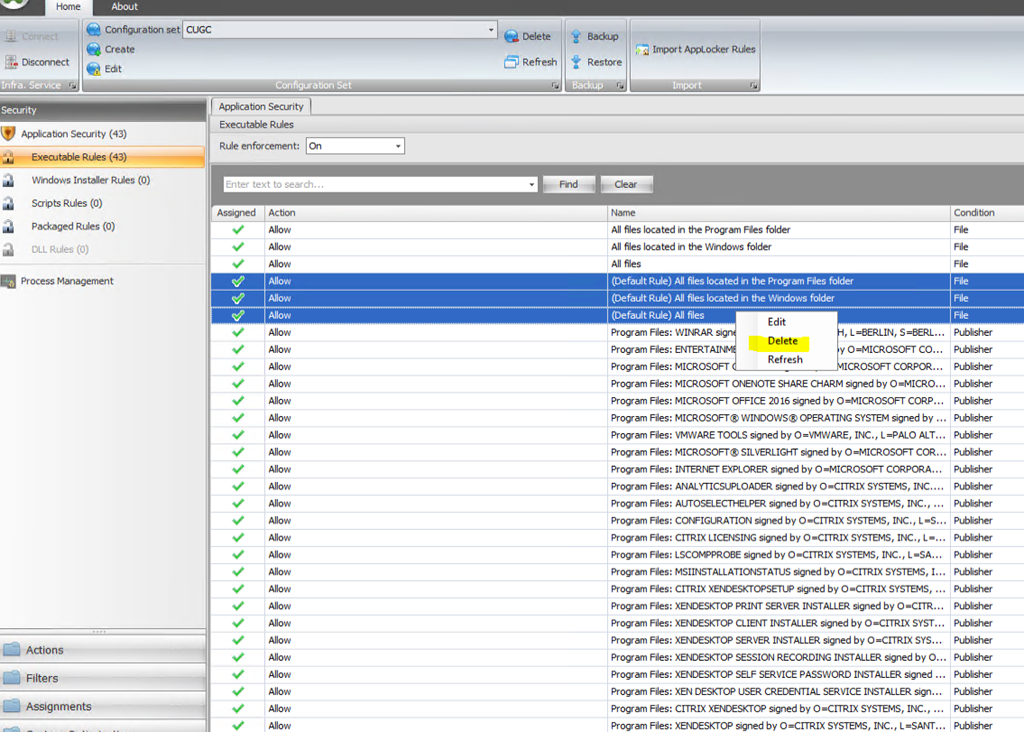
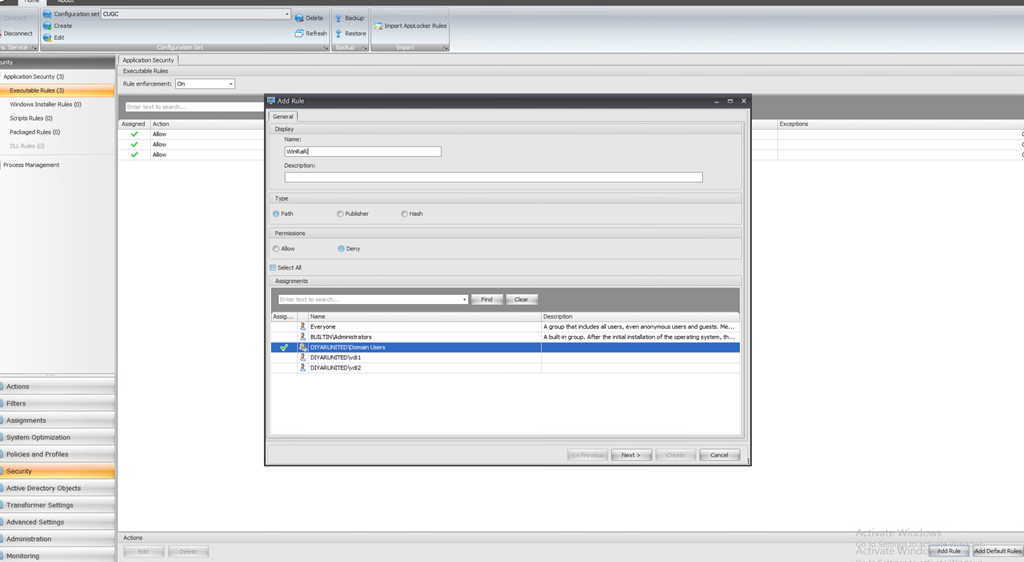
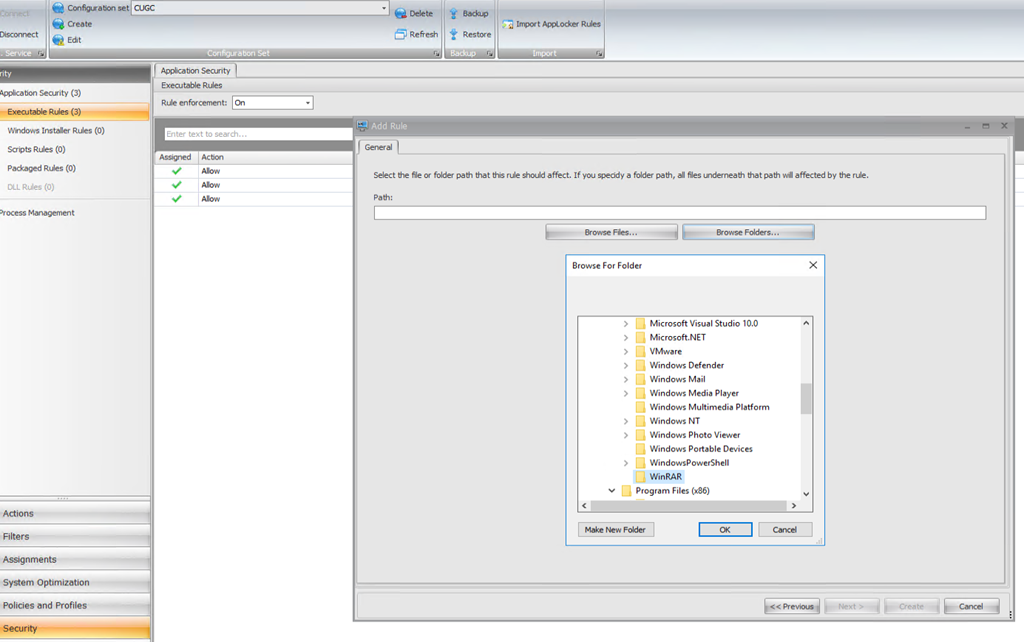
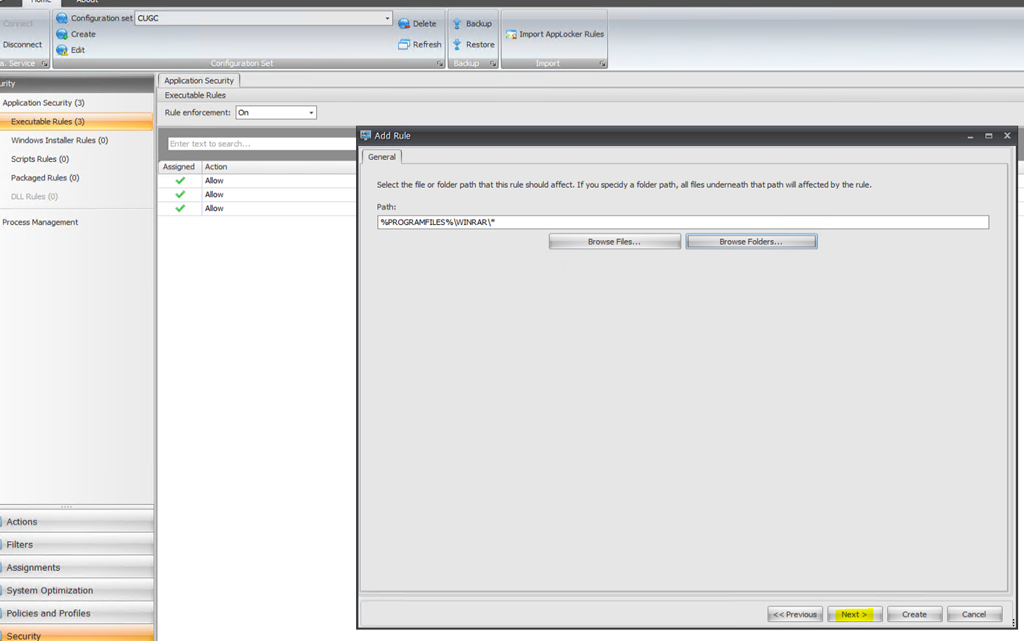
Step 5: Create Deny Rules for executable applications assigned to users/groups based on requirement. Rule can be by path, hash , or digital signature. We can run App Locker Local GP Automated Rules on base image to get all installed application details. Path is a bit risky because if the user runs the executable from a different location it would work so go for publisher or hash when possible. Automated policies can also be exported and imported to WEM to save some time and bulk edit can be used to set required permissions.
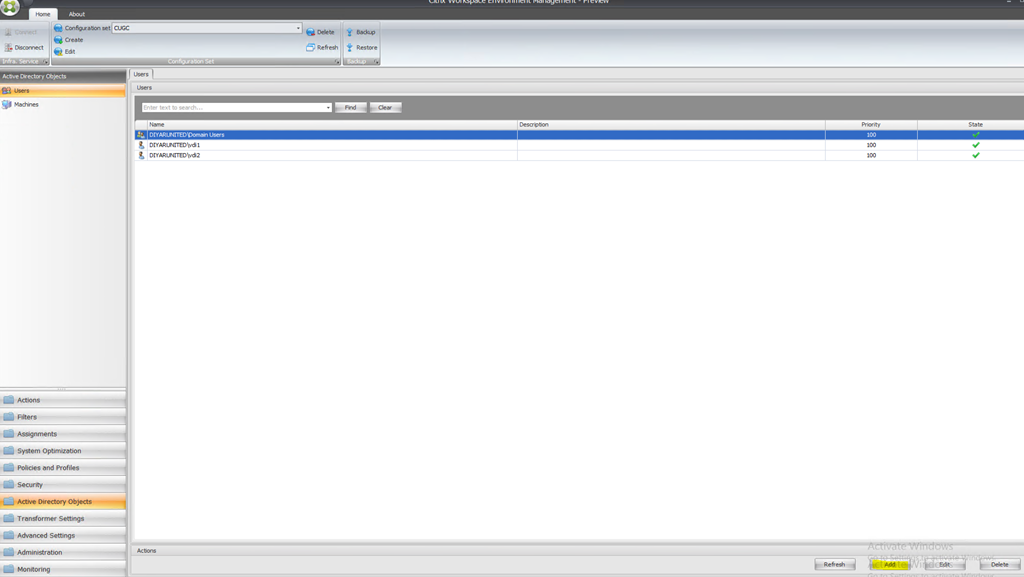
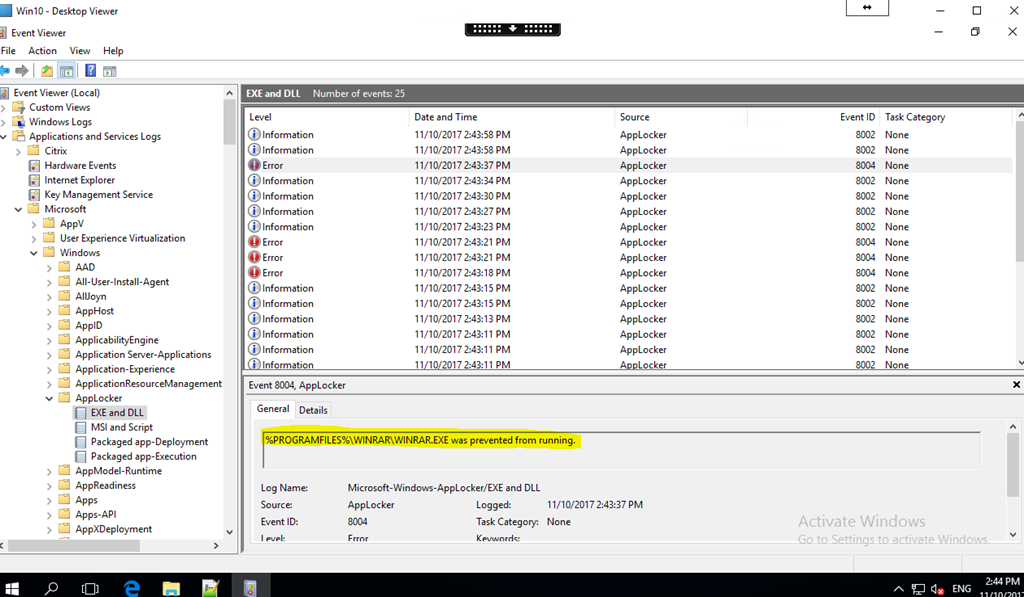
When imported rules to WEM, File/Path based entries did not get imported because they are invalid so will check on that with Citrix. Events can be monitored in Event Viewer | Microsoft | App Locker. Groups/Users to be assigned need to be added first in WEM Active Directory Objects. Bulk edit to assign groups/users or Allow/Deny is done by choosing the policies and right clicking to edit.
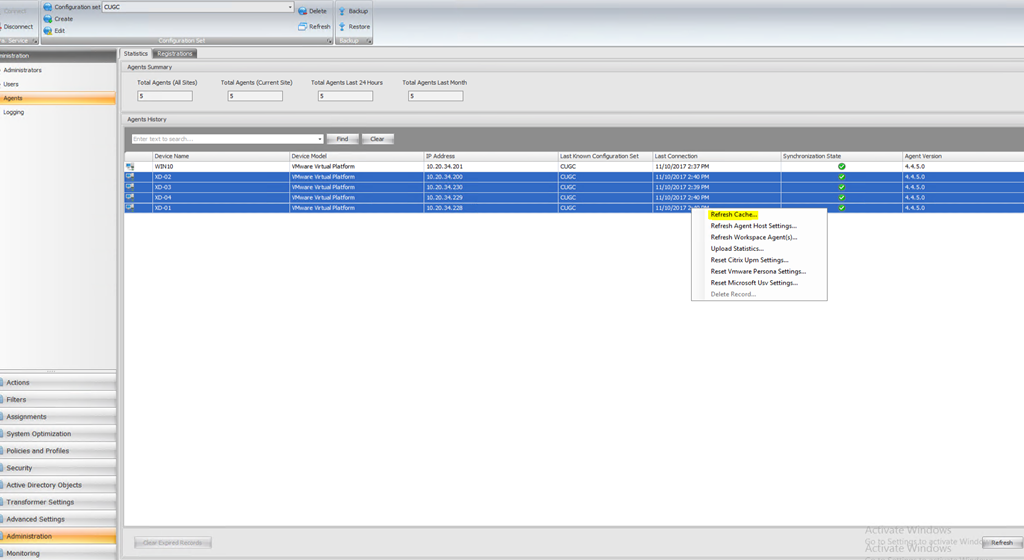
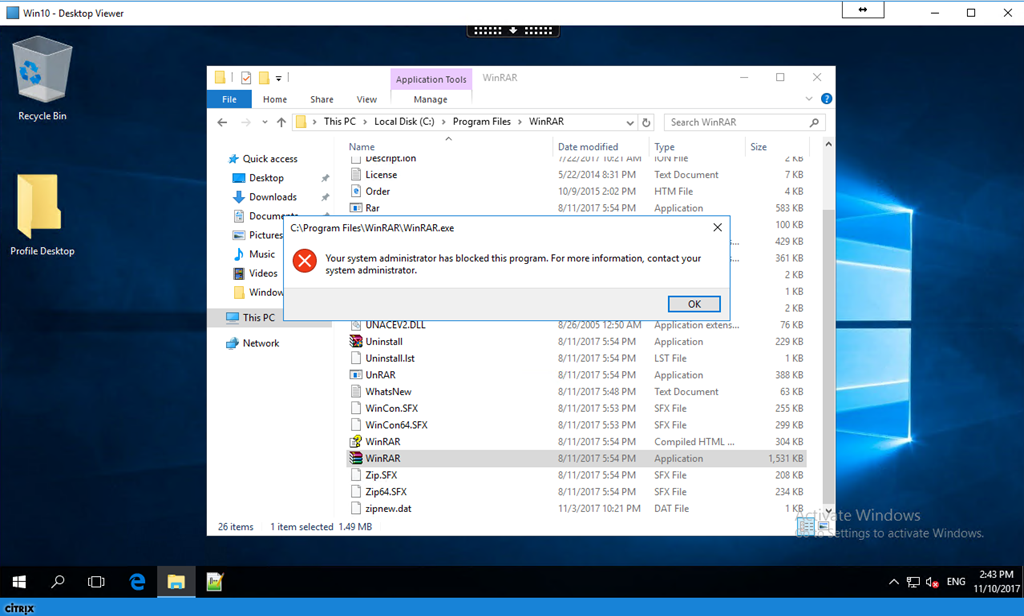
Step 6: Refresh cache on virtual desktops and try to open WinRAR, since we applied deny policy to domain users so no user can open any executable inside default WinRAR path.
Same applies to Windows Installer Rules, Scripts Rules, Packaged Rules, and DLL Rules. Make sure to add default rules and run in Audit mode for sometime after which determine what applications rules need to be applied for users/groups then turn to On mode for every section the create appropriate rules.
Citrix Workspace Environment Manager Application Security Tech Preview User Guide can be downloaded here.
Conclusion:
I really hope this feature makes it into production and Citrix keeps enhancing WEM features and stabilizing the product. I would like to see App profiling and GP Import into WEM asap on top of some minor issues solved like auto cache refresh and agent boot on logon.
Salam ![]() .
.