Part 2: Demystifying Citrix Cloud: Gateway Connector, Access Control, and SSO
Introduction:
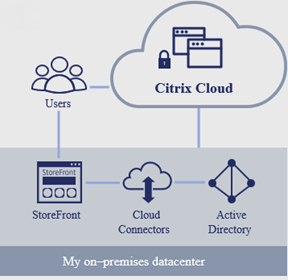
Citrix Cloud is a cloud-based control plane that is owned, configured, managed, and supported by Citrix and can be utilized by customers to provision services. This cloud plane is hosted on Microsoft Azure and customers pay using a subscription model depending on the service requested.
Citrix Cloud does not host customer workloads and follows a rigid security practice to ensure compliance with international security standards. It connects to any on-premises or cloud environment defined as Resource Location using a Cloud Connector Windows machines that only requires outbound 443 and supports proxy.
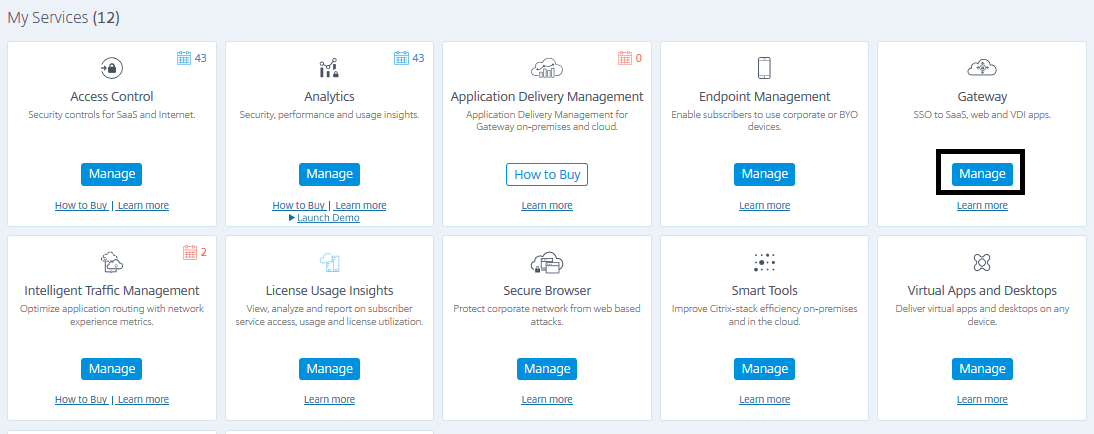
Citrix Cloud operates, maintains, and supports all infrastructure components required for any cloud service offered which range under different subscription models offering different services:
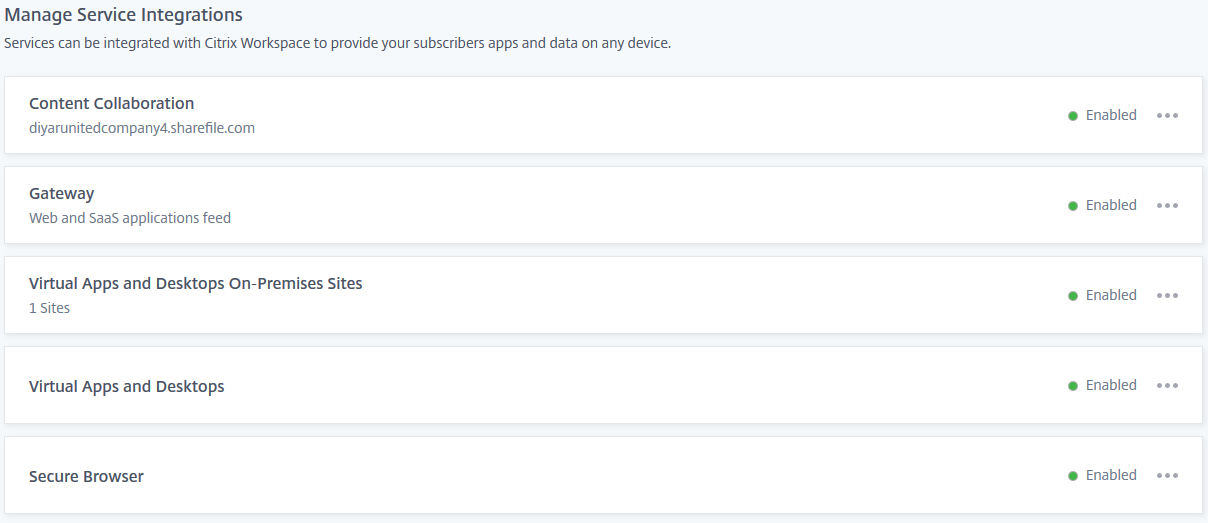
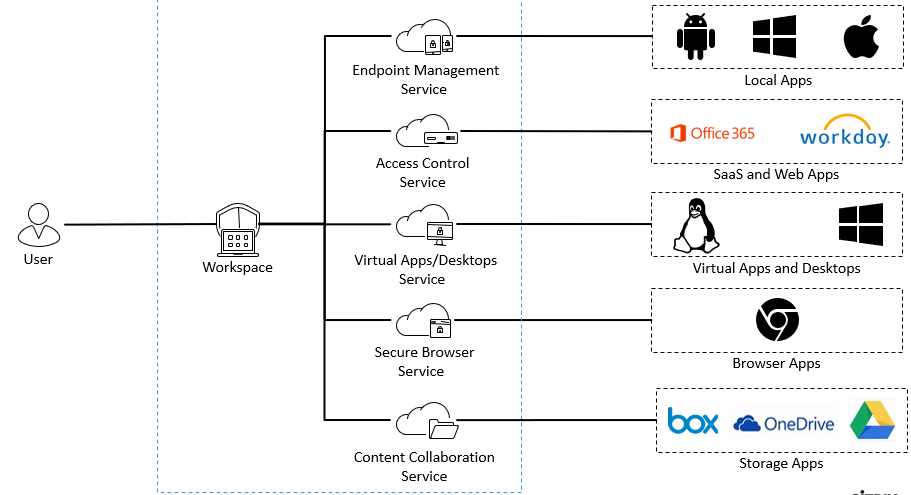
The power of Citrix Cloud comes from service integrations between all of the above under the Citrix Workspace umbrella which drastically enhances user experience by providing a single pane of glass portal having everything from virtual desktops to SaaS applications with SSO and security out of the box,
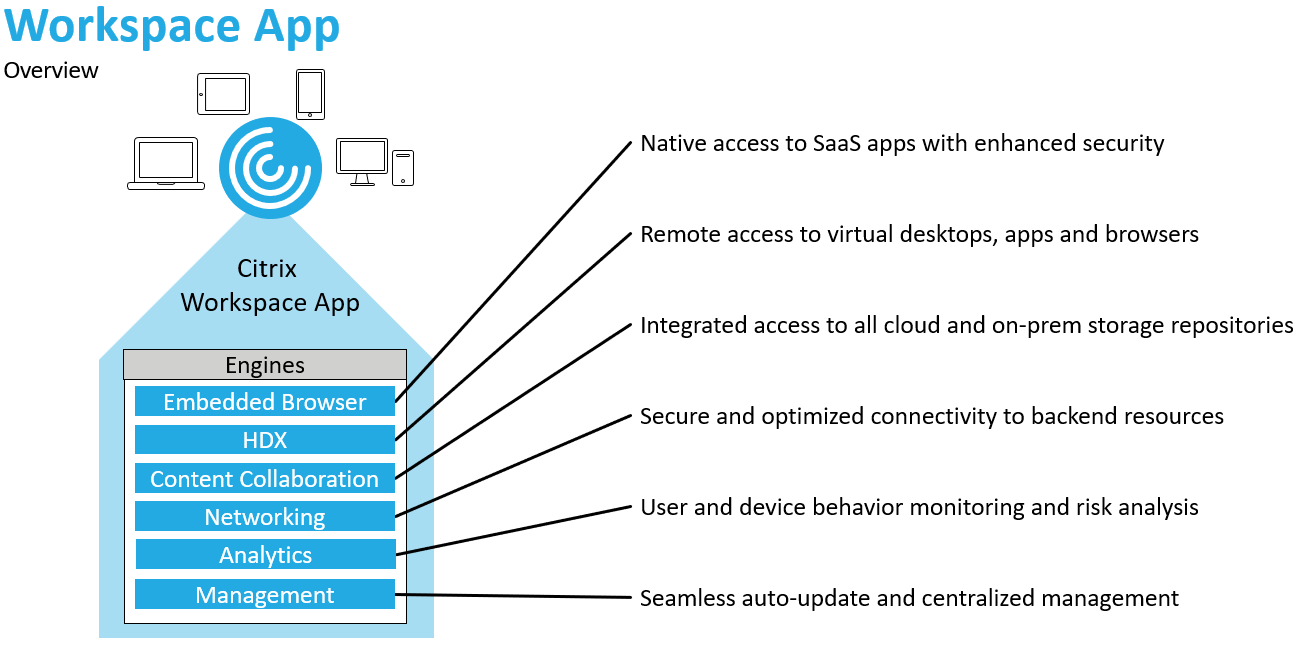
The power of correlation and integration of these services along side analytics delivers immense power which is only useful when consumed appropriately and this is where Citrix Workspace App comes into the picture. On a side note, if you want to piss someone at Citrix, just call Citrix Workspace App an update to receiver. Seriously don’t … !
Citrix Digital Workspace:
Citrix Workspace App is a revolutionary approach to digital workspace technology, allowing the end user to harness all the power of cloud services into a very simple easy to use portal that just includes everything a user requires to conduct business anytime, anywhere, and using any device in a secure manner.
Citrix Workspace App does include receiver features and is fully backward compatible never the less it is much more than Receiver and should never be labeled as a new receiver or an update for the same. Workspace App includes many engines under the hood that enable all cloud services to function under the same App with same experience, look, and feel for different types of devices without the need for additional clients or software.
The ability to pull analytics, enable content collaboration, provide internal or external SaaS apps tunneling with SSO, perform device management and secure web apps in a built-in secured chromium browser on top of more engines being added is second to none when it comes to delivering a unified digital workspace on any platform.
Just recently in our Q3 UAE Citrix User Group Community, we conducted a presentation and demo on Citrix Cloud services concentrating on Secure Gateway, Access Control, and Secure Browser. Many including me did not actually grasp the concept of integration and dependency between these cloud services which leads me today to try and demystify it. On a side note, as noted by Citrix Regional Director here in META, we definitely need more women in tech especially in our region.
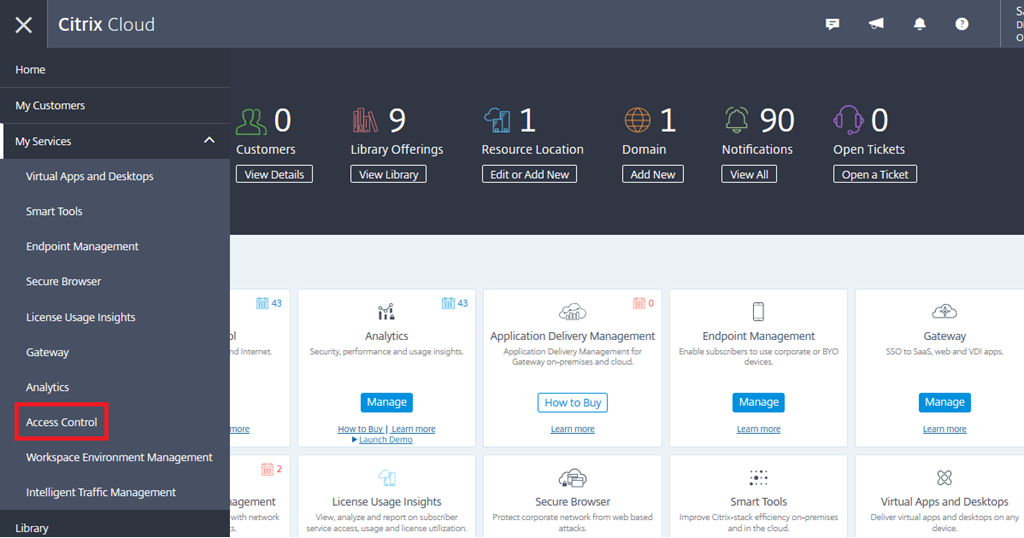
Lets start by defining what these services are and what are they intended to be used for in the context of a Citrix Digital Workspace:
-
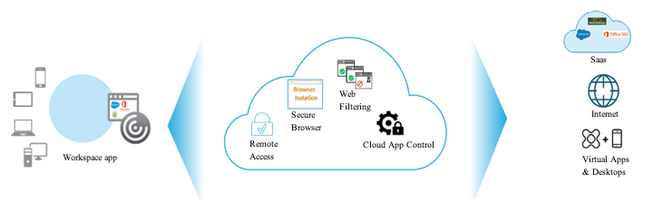
Citrix Access Control: enables administrators to apply security controls over published services such as SaaS web applications. Access Control can set enhanced security policies for SaaS apps. (For example, watermark, copy-paste restriction, and prevent downloads.), define access policy for website categories and websites to be blocked/allowed in a form of web filtering, define access policy for website categories and websites to be redirected to Secure Browser service, make policy changes to allow or block website access, and enable access in a secure browser service session, and understand users and websites activity in the context of SaaS apps and correlate it to defined policies.
Access Control integrates with Gateway Service to provide Single Sign On experience for SaaS applications, with Analytics (Included license Only for Access Control) Service to provide monitoring to user activities, such as malicious, dangerous, or unknown websites visited, the bandwidth consumed, and risky download and upload behaviors, and with Secure Browser for redirecting risky URLs to protect internal networks.
Access Control is part of all Workspace Suite licensing options which would include Citrix Gateway service as well for SaaS SSO. For more in-depth architectural details on Access Control, visit this amazing post by the one and only Citrix Lead Architect Daniel Feller.
-
Citrix Gateway Service: “provides secure remote access solution with a diverse Identity and Access Management (IdAM) capabilities, delivering a unified experience into SaaS apps, heterogeneous Virtual apps and Desktops, and so forth”. The service is natively highly available, supports optimal gateway routing, and has many points of presence globally.
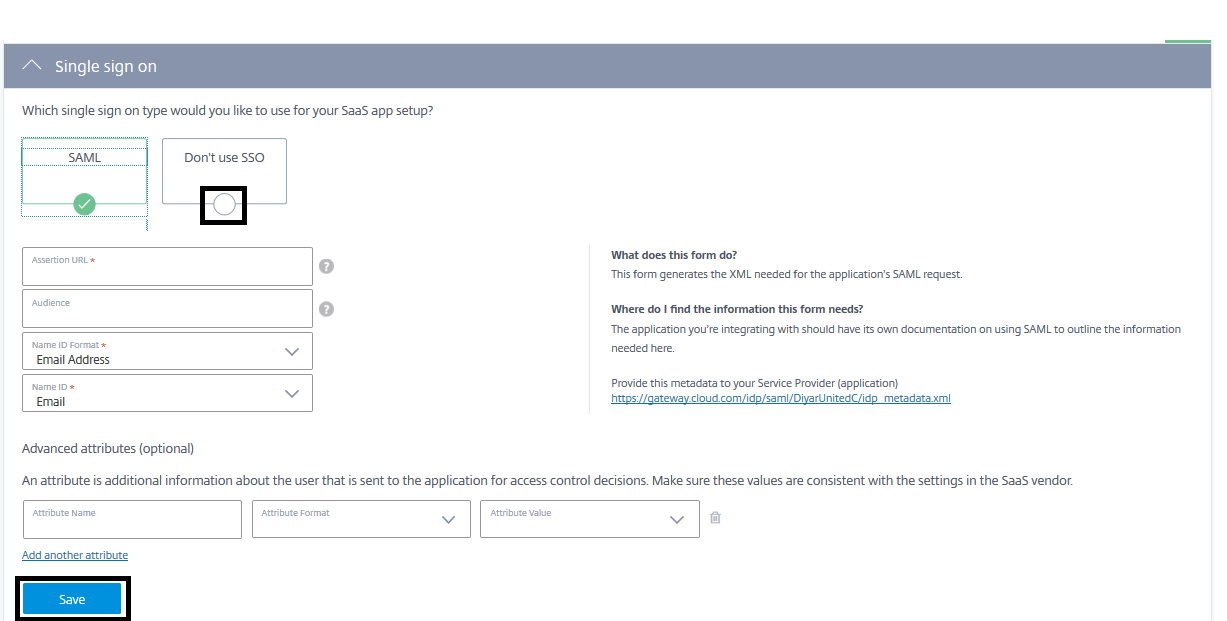
Gateway Service supports two very important featured which are HDX connectivity for Citrix Virtual Apps and Desktops “ICA Proxy” and secure access to SaaS applications with Single Sign On. It supports SAML integration for SaaS SSO and has more than a 100 pre-built SAML templates for well known SaaS applications which makes integration that much easier.
One very important feature being worked on for Citrix Gateway Service is tunneling application access with SSO for internal applications. This feature would require an Gateway Connector which is a prebuilt virtual appliance that is used to tunnel web app traffic securely by using only outbound 443.
Every user is allowed 1 GB data transfer per month and additional data MB can be purchased if required. Citrix seems to be confident that 1 GB as a baseline is enough for most workspace users, something that would vary based on type of workloads published. The service is provided with Citrix Virtual Apps and Desktops without access control and/or SaaS SSO and is provided with Citrix Workspace Suite all editions with access control and SaaS SSO which is required for enhanced security.
-
Citrix Secure Browser: “isolates web browsing to protect the corporate network from browser-based attacks. It delivers consistent, secure remote access to internet hosted web applications, with no need for user device configuration”.
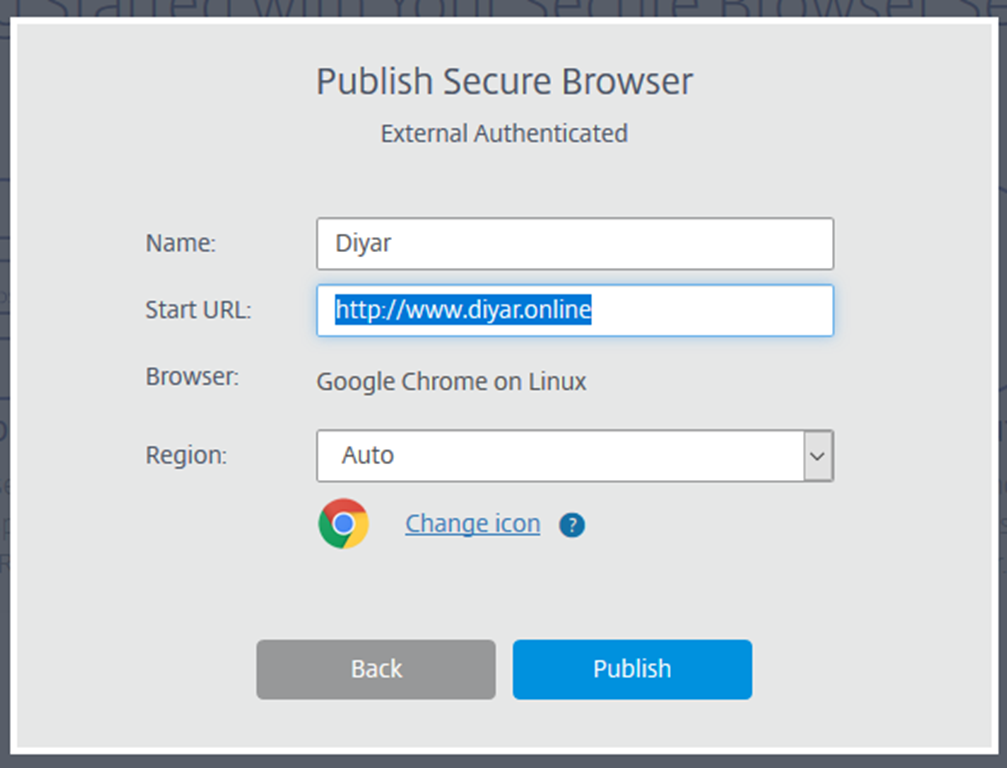
When launched, users are provided with an cloud hosted secure Linux based chrome browser which would prevent any malware from compromising your corporate network. The browser is hosted on Azure in multiple locations and normally choose the region closest to your end users, even more now auto region based on geolocation is available.
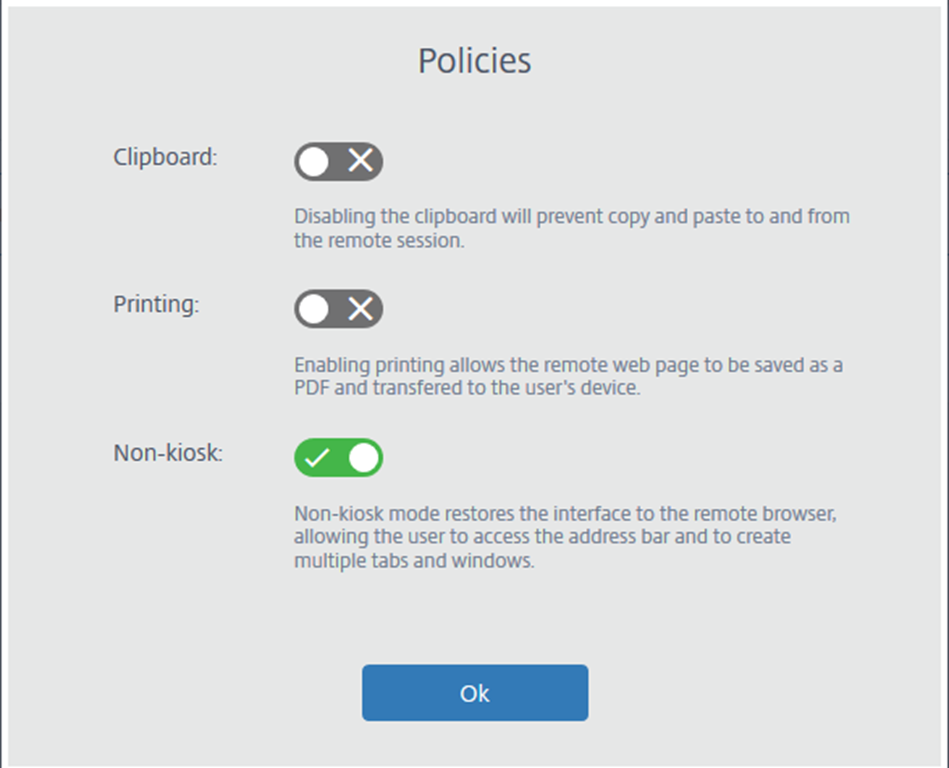
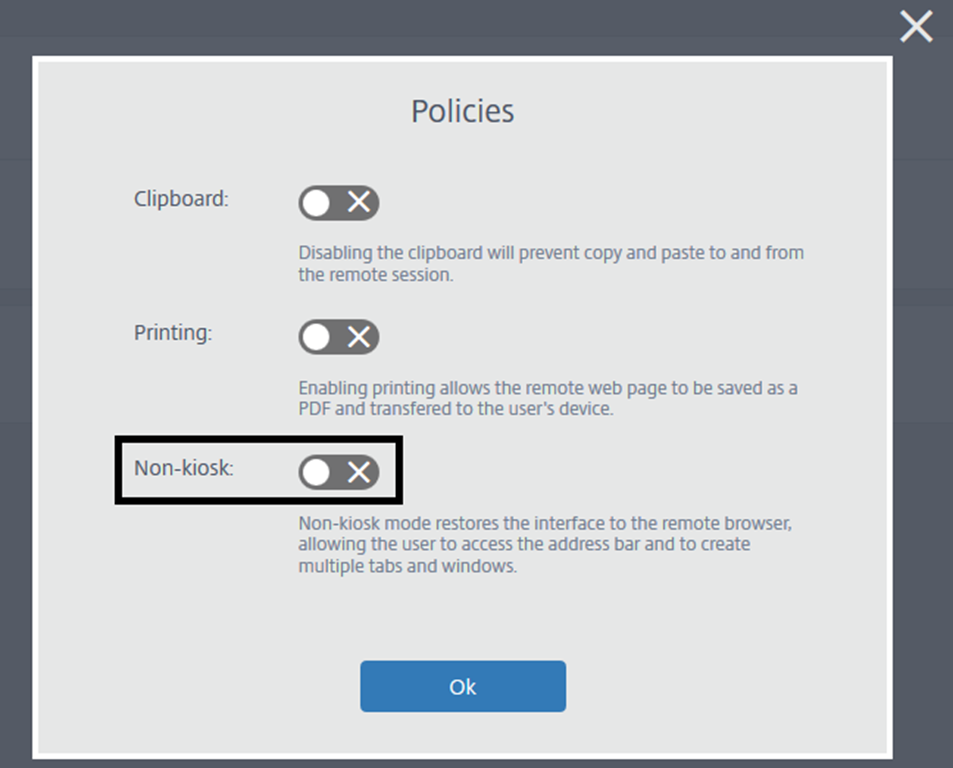
Clipboard, printing, kiosk-mode, and URL whitelisting are security features available when publishing URLs through the service. URLs can be published unauthenticated which means all users can access using a specific Brower URL without having to authenticate, while publishing authenticated websites means users have to authenticate either to local AD or Azure AD both of which require a cloud connector and resource location to be available.
Also available in technical preview, integration with on-premises storefront to deliver secure gateway through local storefront page.
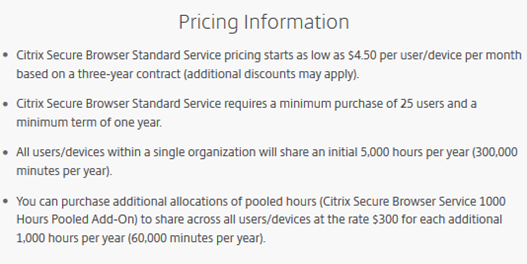
Citrix Secure Gateway is not part of Citrix Workspace and should be licenses/purchased separately which honestly adds to the confusion of Citrix cloud licensing.
Citrix Workspace offerings include the following services for your reference under standard, premium, and premium plus:
Deployment:
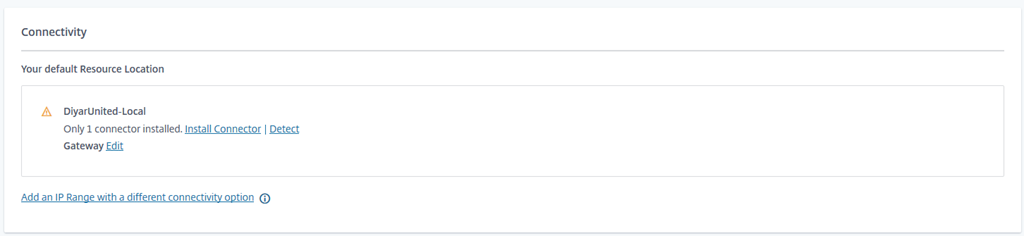
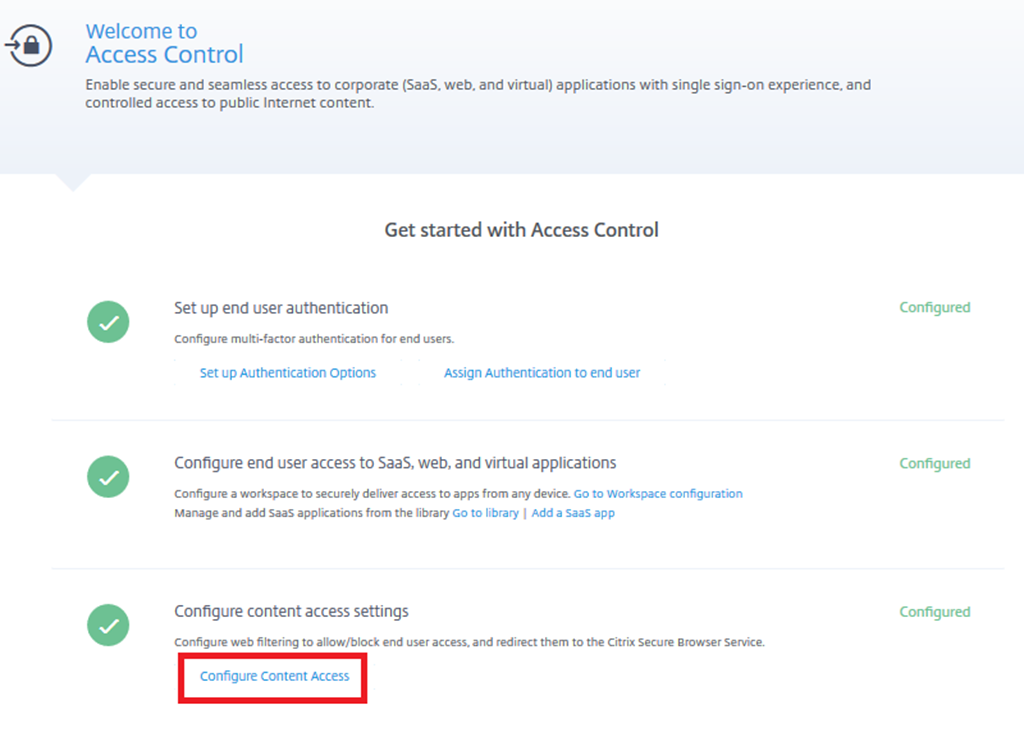
All three are very easy to configure, operate, and test given the ease of management and configuration introduced with Citrix Cloud. Lets go through the steps required to deliver these services. Make sure you have one resource location at least with two cloud connectors.
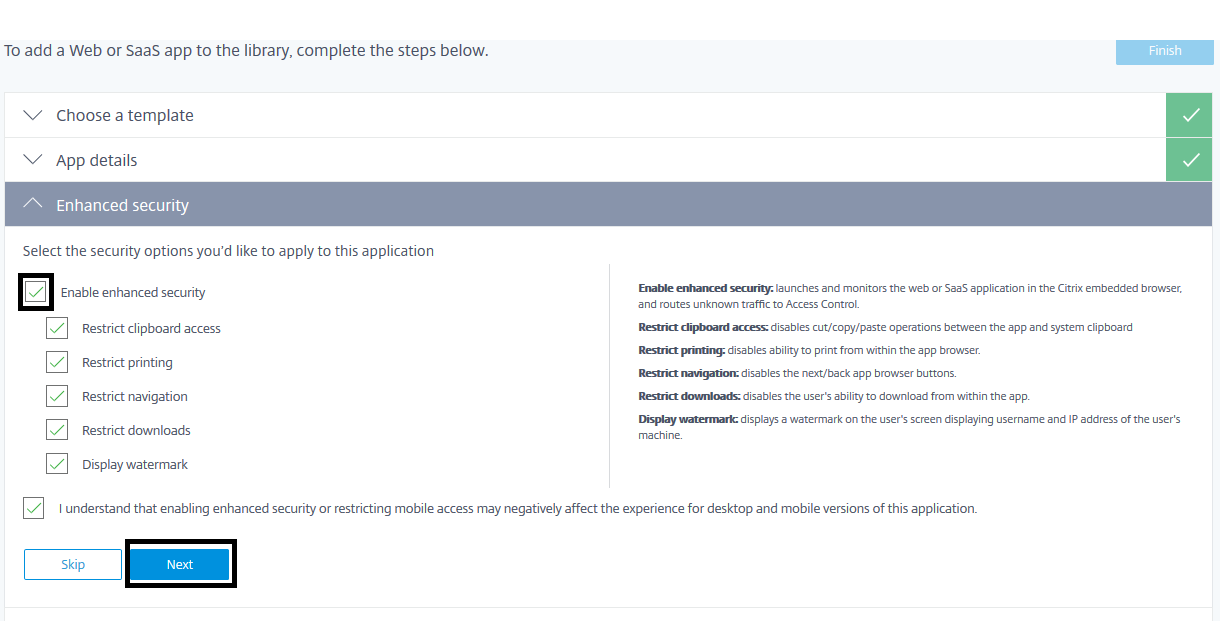
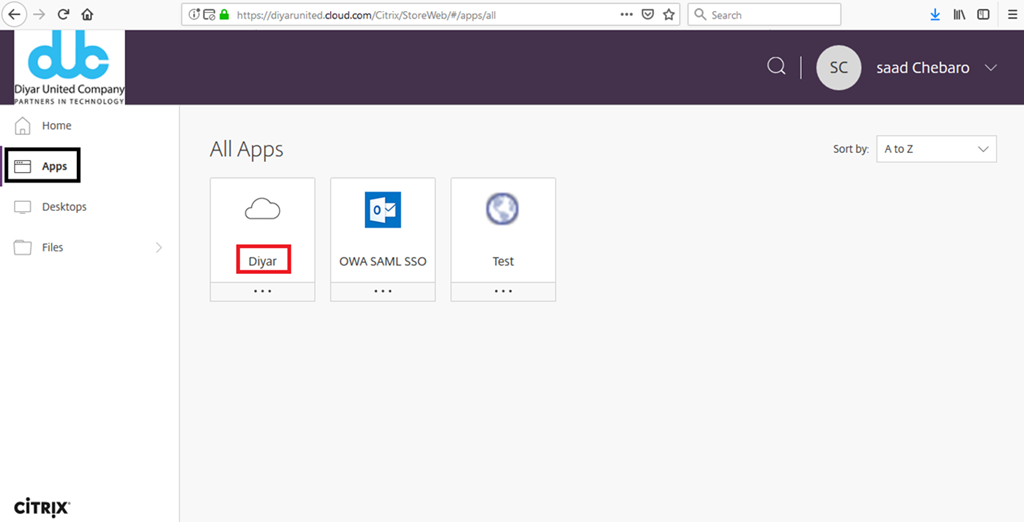
I will publish a web application and apply enhanced security for the same. Enhanced security requires the web app to be opened from within Workspace App so that these policies can be applied to the built-in secured chromium browser. I don’t have a SAML app as of now but most well known ones have templates published so should be very straight forward.
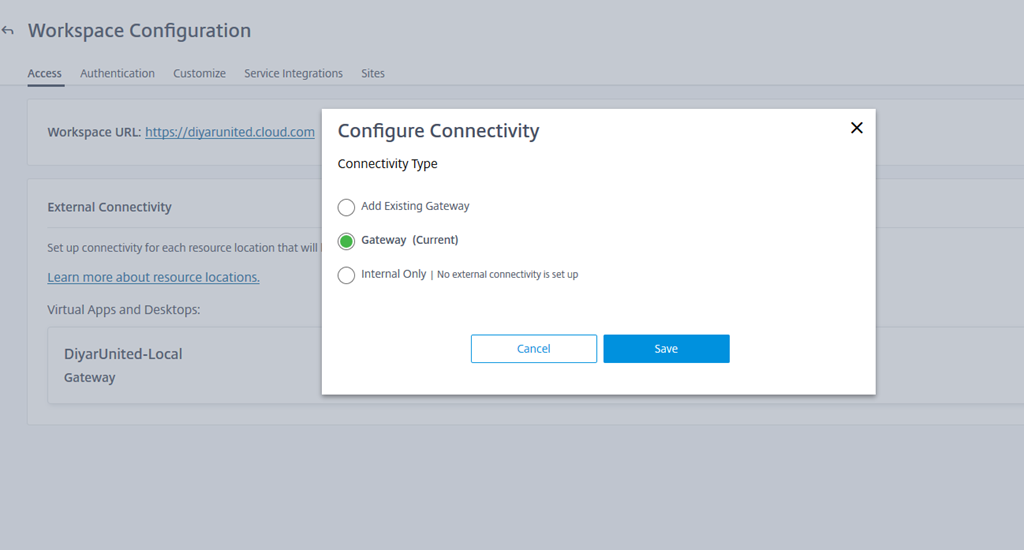
Gateway service has two functionalities at the moment, the first is very simple and does not require any kind of change or configuration which is ICA Proxy for Virtual Apps and Desktops, all is required is to tell the Virtual Apps and Desktops to use the Gateway Service and your Citrix provided cloud URL will be used for the same. Note here is that as of now, when you choose to use Citrix Gateway and you are using Citrix storefront, even internal connections will be tunneled through the gateway service.
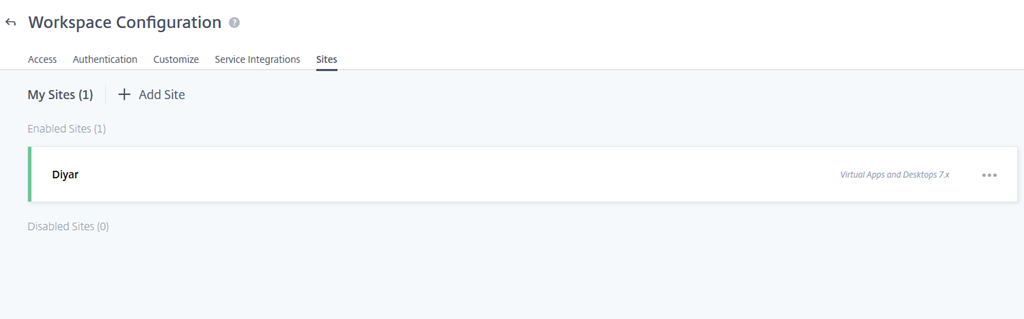
Note that another useful integration for Gateway Service is the ability to add local sites that do not have NetScaler Gateway and use the service to publish your on-premises resources to external users. This is very important for hybrid situation when shifting to Citrix Cloud and if you do not want to invest in NetScaler’s just for the purpose of access gateway.
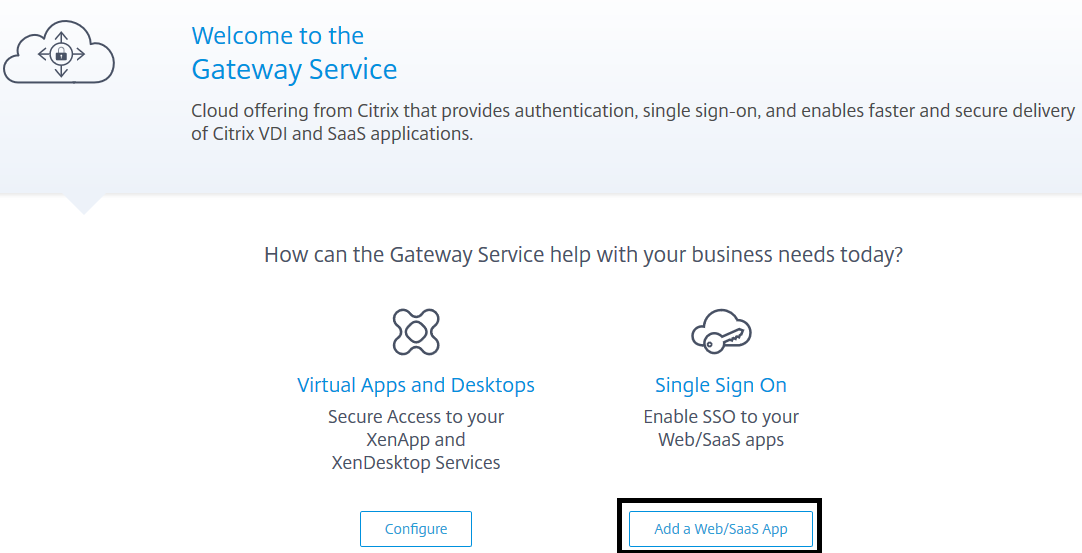
Now Back to publishing and securing applications through Gateway Service and Access Control Service:
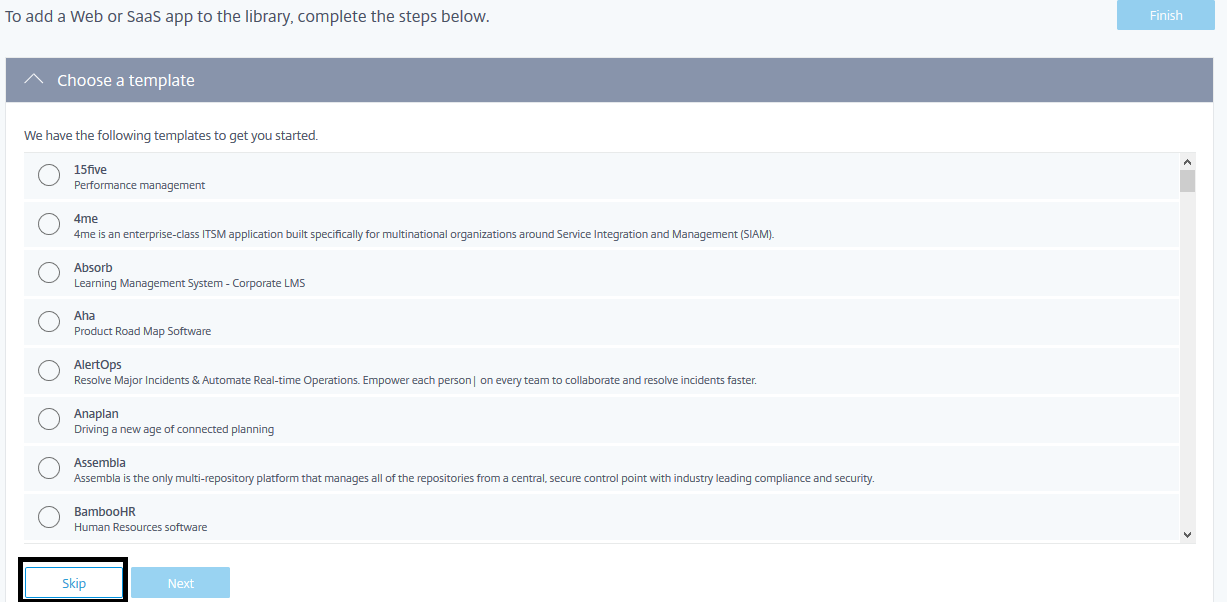
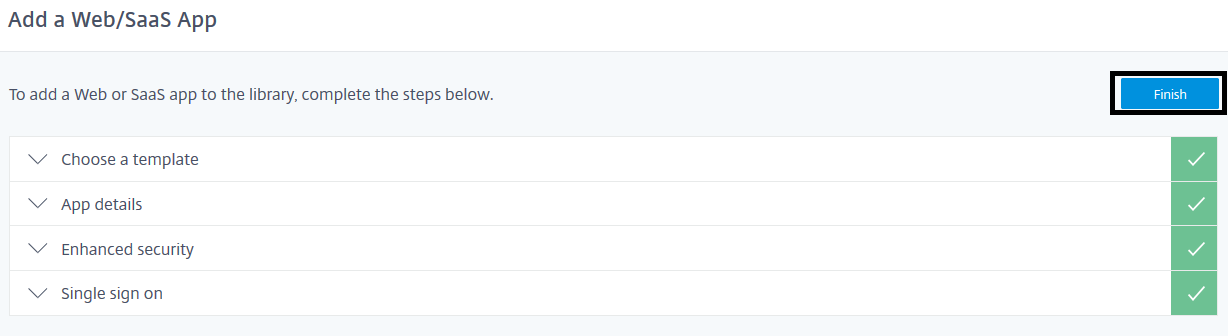
These templates make it very easy to integrate with SaaS applications for SAML SSO without having to do any manual work so highly recommended:
Choosing Inside my corporate network which would support internal applications SAML SSO is currently in technical preview and requires gateway connectors. Seems that those gateway connectors have an issue that has been seen by many others, I am in contact with Citrix for the same and will post something when its resolved to test how it would exactly work.
If you don’t have the Access Control Service enabled, this box will not show when publishing the application through Gateway Service.
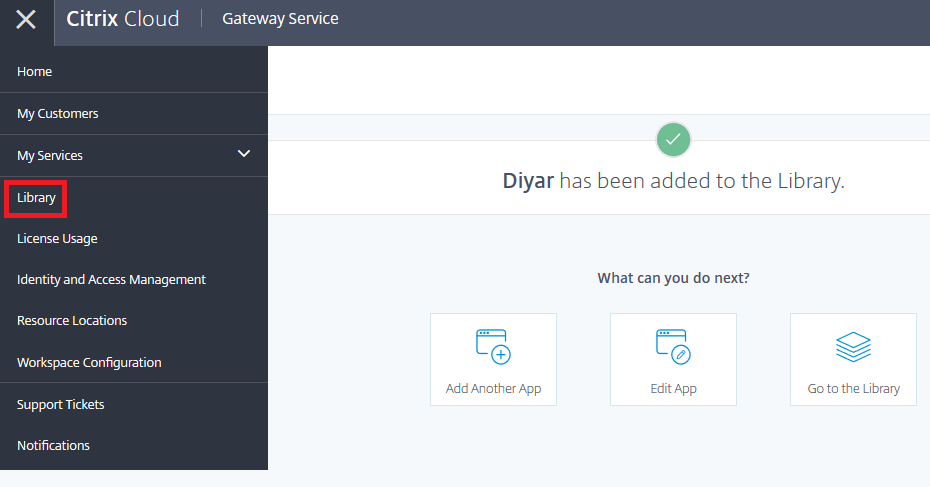
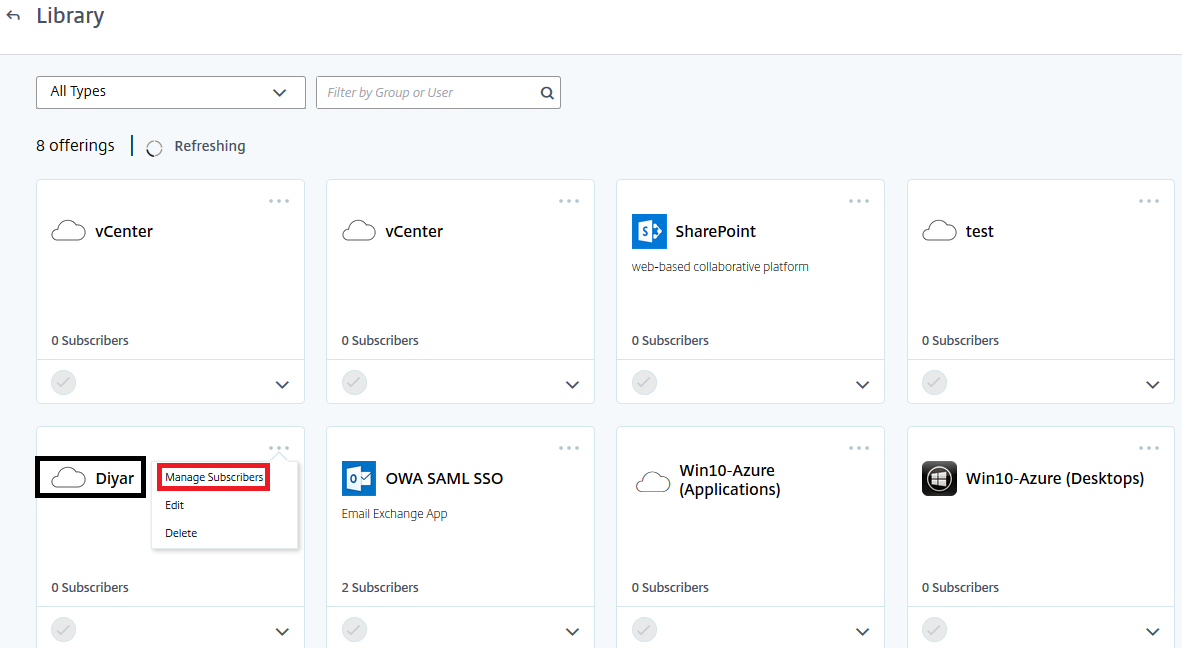
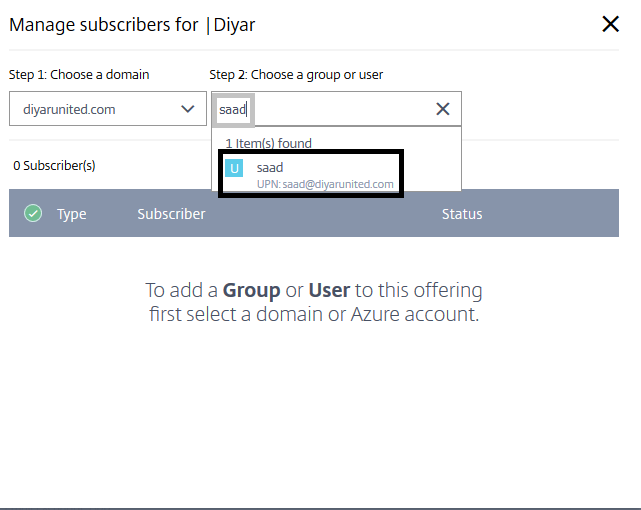
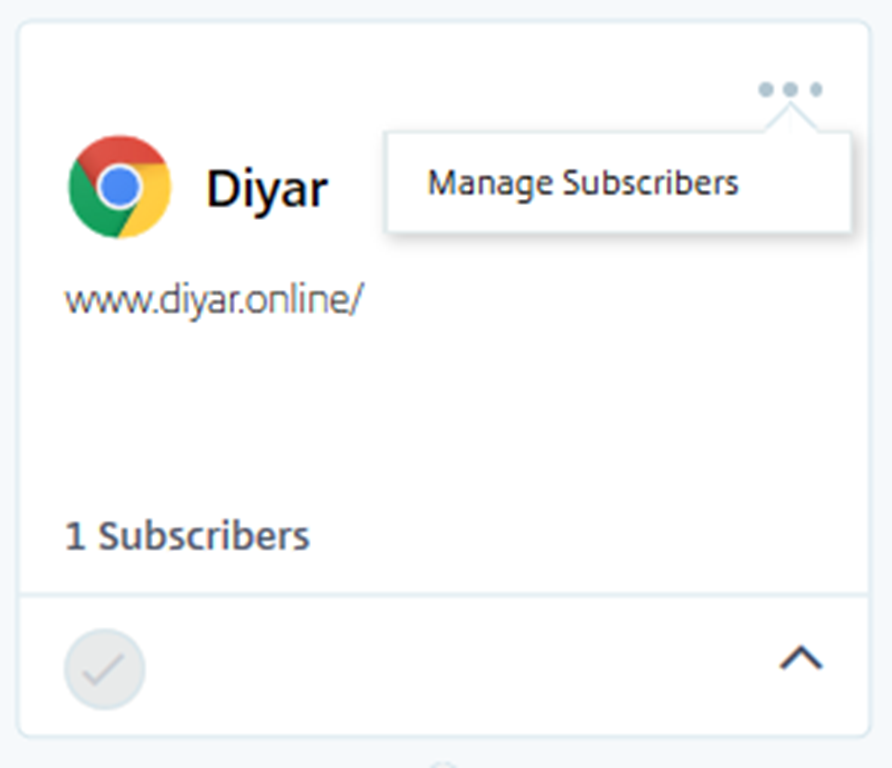
Granting access to applications is done from the Library tab which connects to all your domains through the cloud connector and allows you to assign access to users or groups.
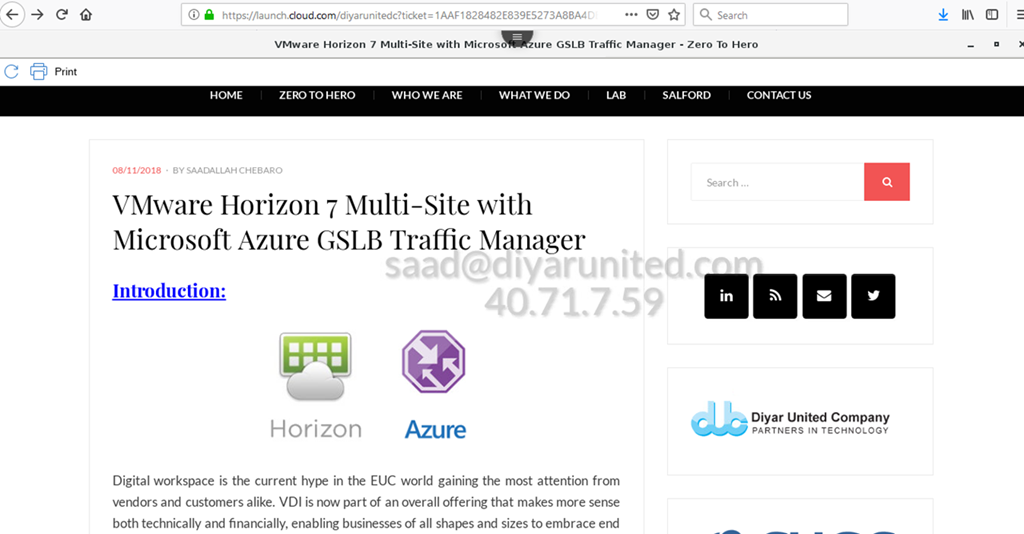
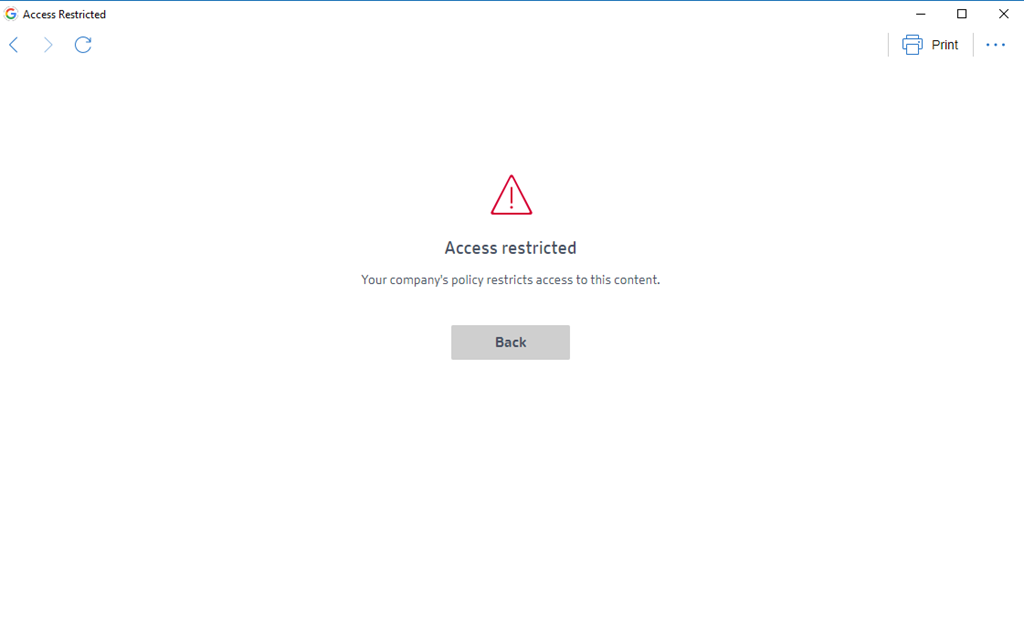
First test is conducted by accessing the application from web rather than workspace app and the result is you can see the watermark in the middle on top of all restrictions like copy,cut,paste, and download are restricted.
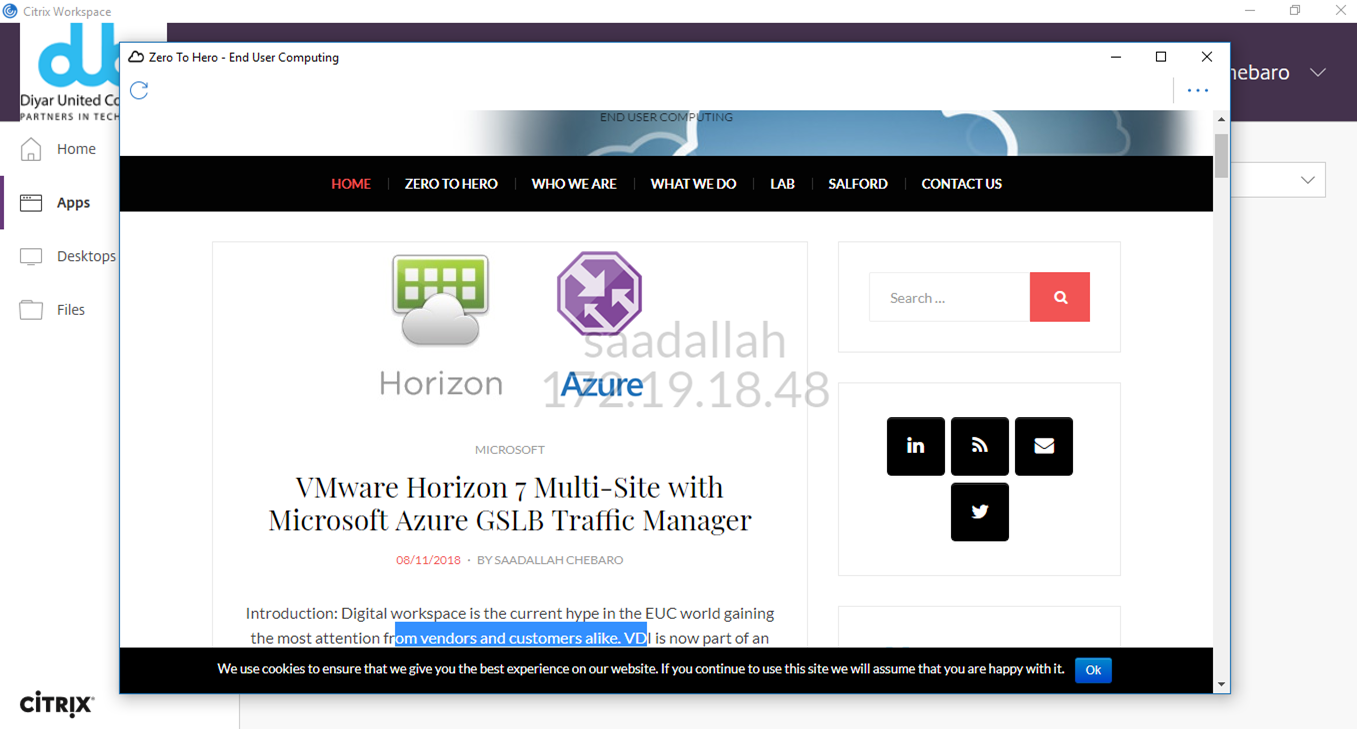
Testing from Workspace App shows the same restrictions are applying and shows the actual name in watermark rather than UPN.
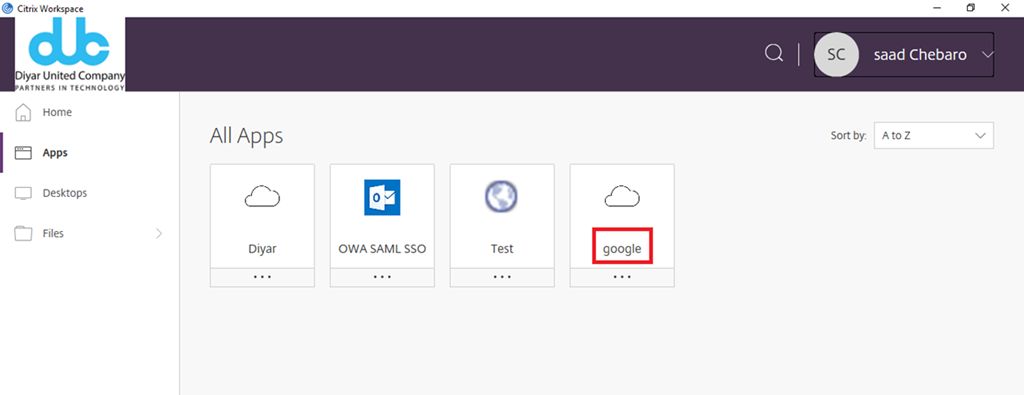
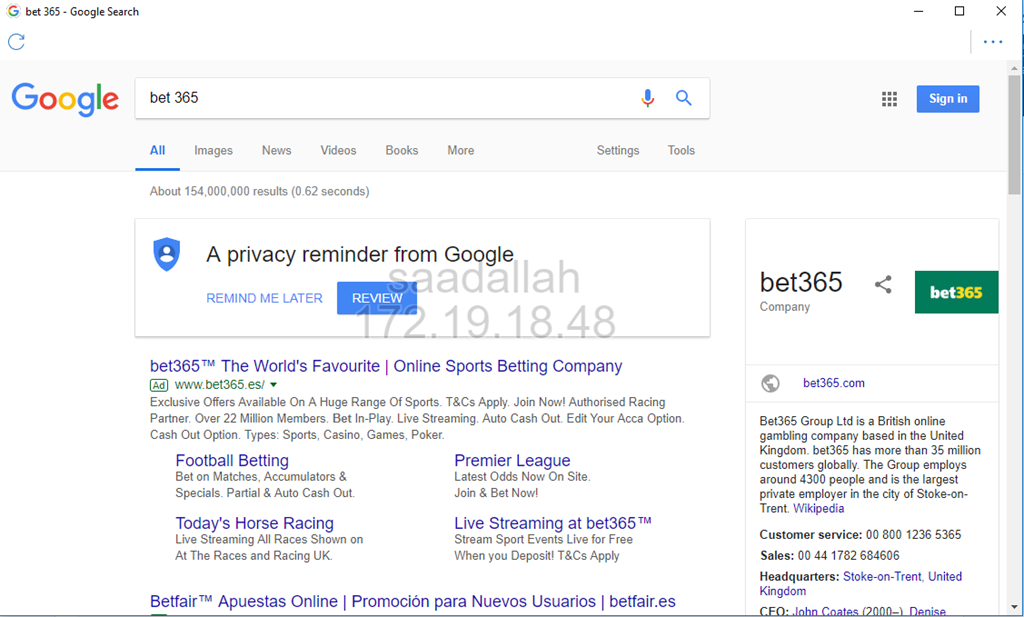
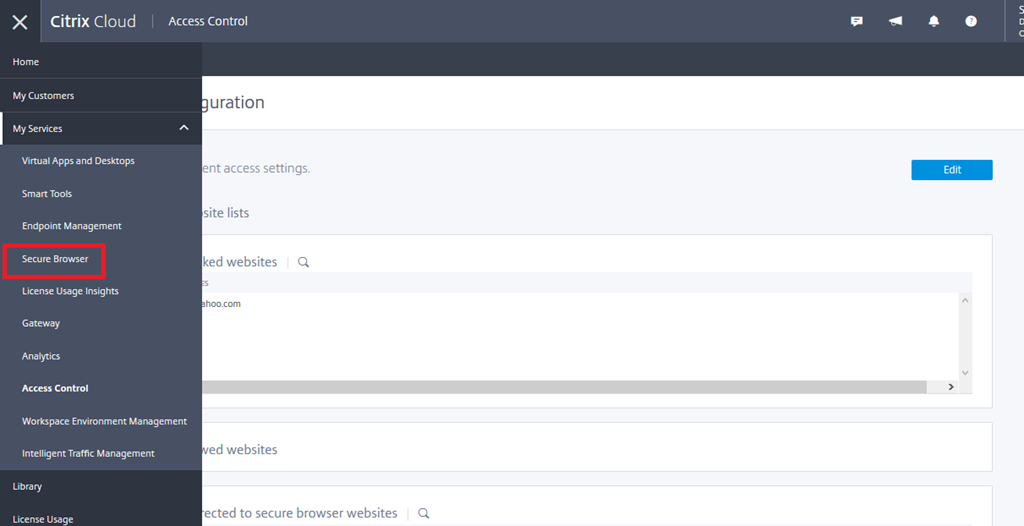
I have created a similar no SSO with enhanced security published website pointing to google.com . I am going to demonstrate web filtering and secure browser redirection using Access Control. Remember something very important which I didn’t until recently, Access Control restrictions only apply after the SaaS app is launched, so if I block search engines but I publish an app pointing to an search engine such as google here, the page would load but after that within the page, search engines would be blocked.
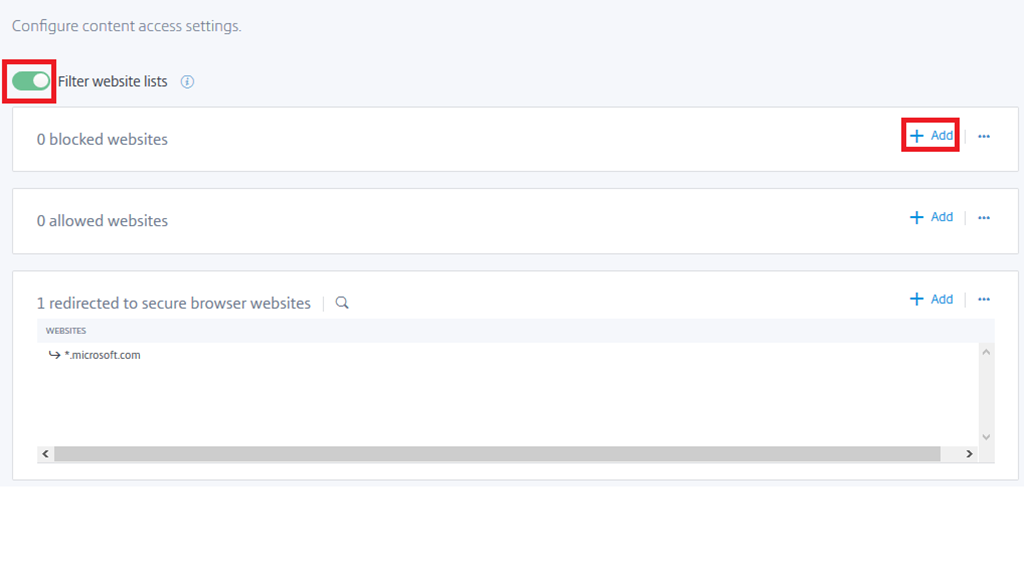
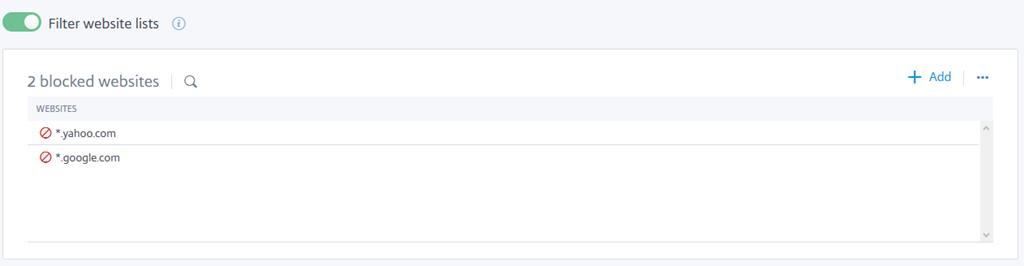
Enable Filter website lists and add manual websites to block from within the published app .
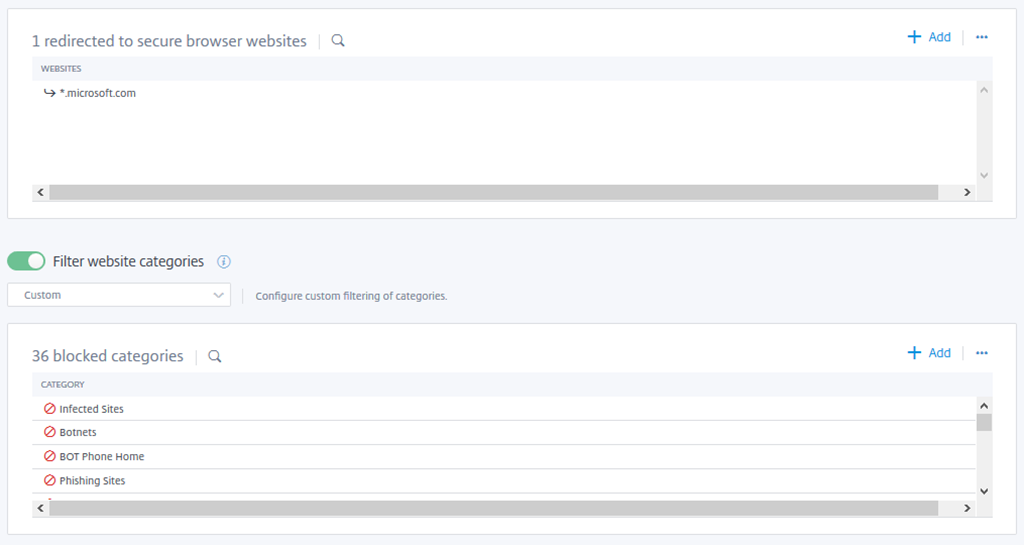
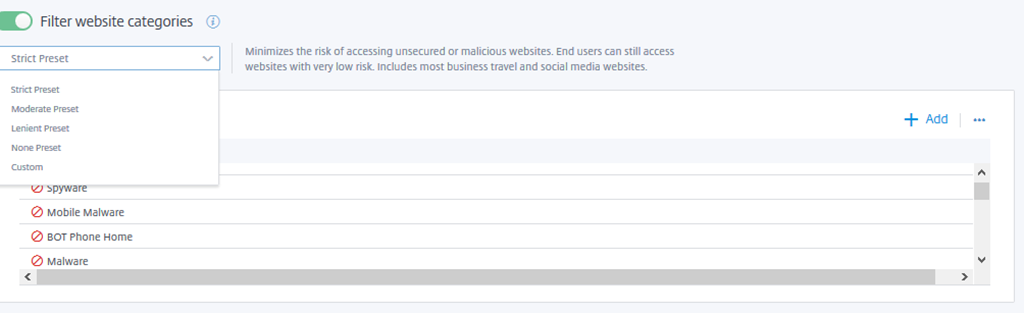
Here we choose to redirect these URLs to secure browser, in this example anything under Microsoft website should be opened automatically with Secure Browser. Website category filtering can be applied as well to block well known malicious sites, even presets are prebuilt templates by Citrix to be used for defining the level of security applied blocking website categories rather than choosing categories manually.
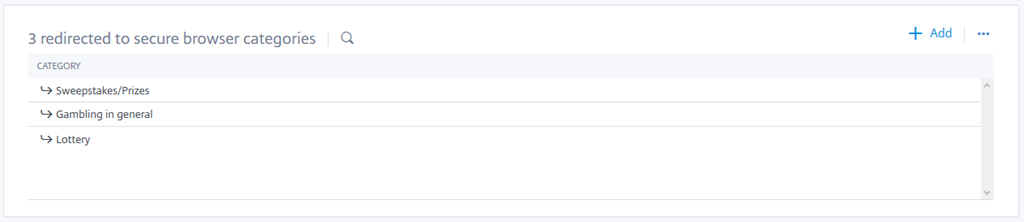
We can also choose to redirect websites under categories to Secure Browser rather than having to add all sites manually.
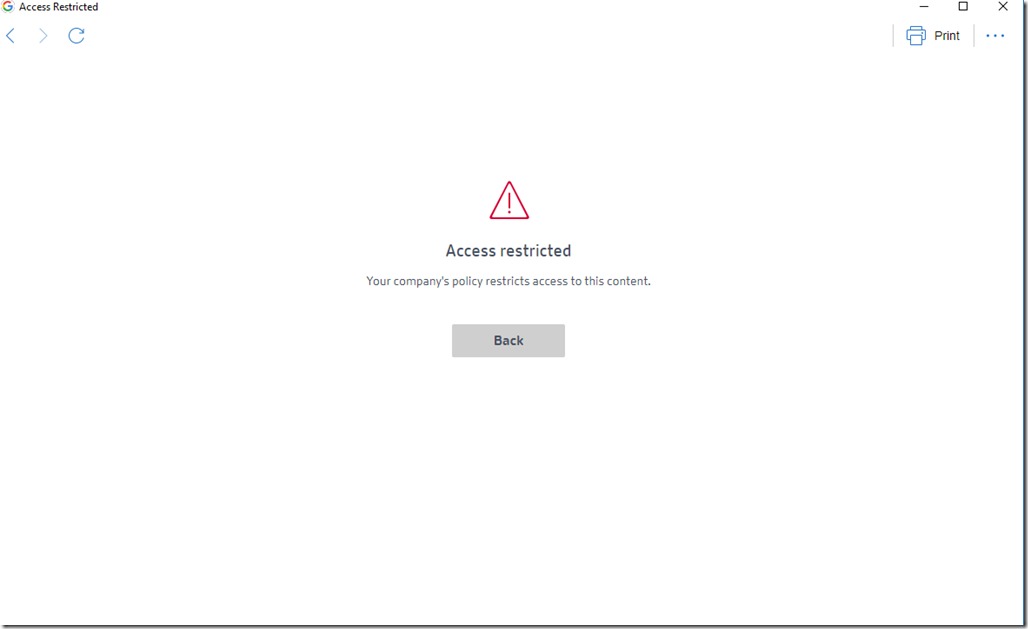
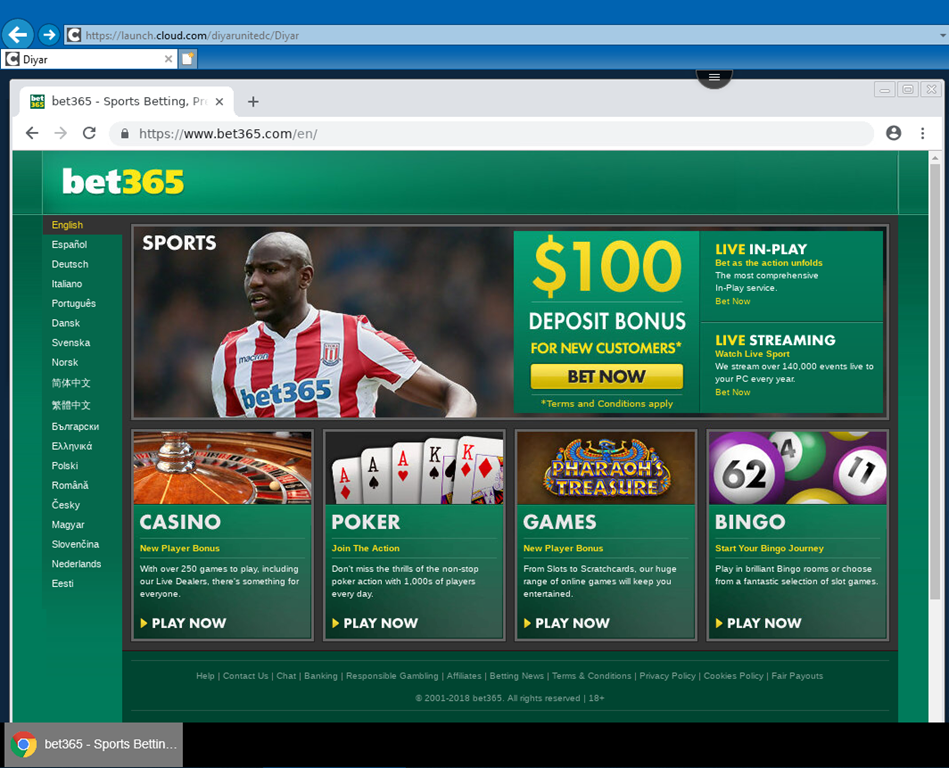
Gambling sites are blocked as per the category websites block list.
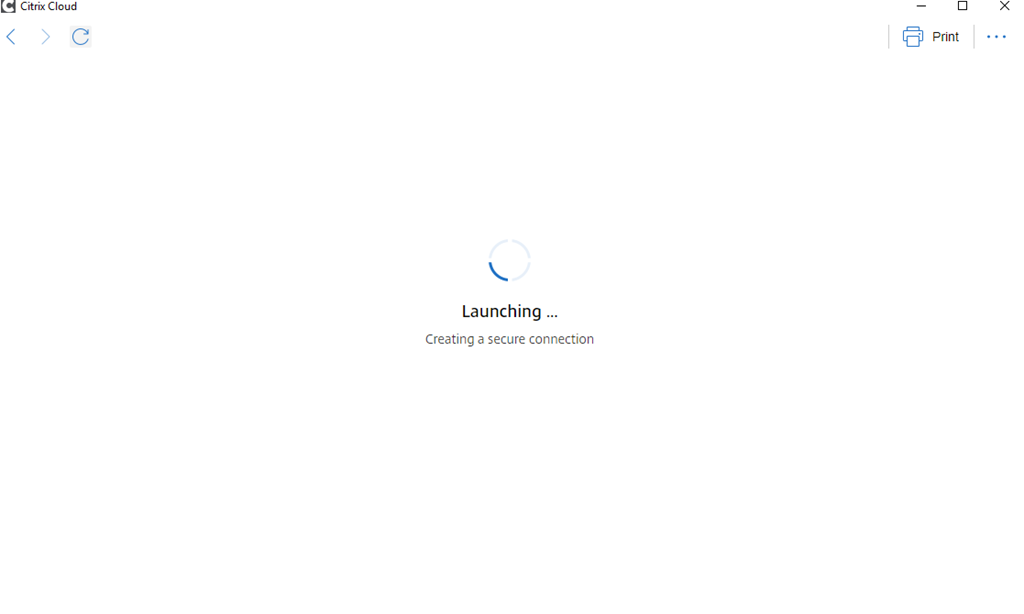
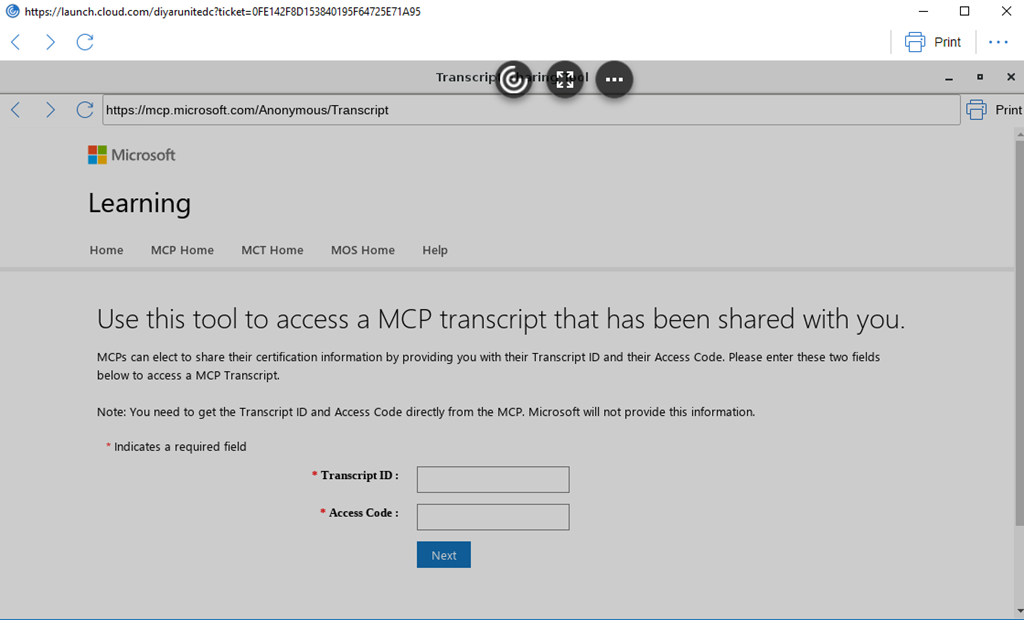
Any URL under *.Microsoft.com is going to be redirected to Secure Browser automatically as seen below for mcp.microsoft.com .
I have removed all category block and kept only the yahoo.com website block to make sure that single website blocking is also operational.
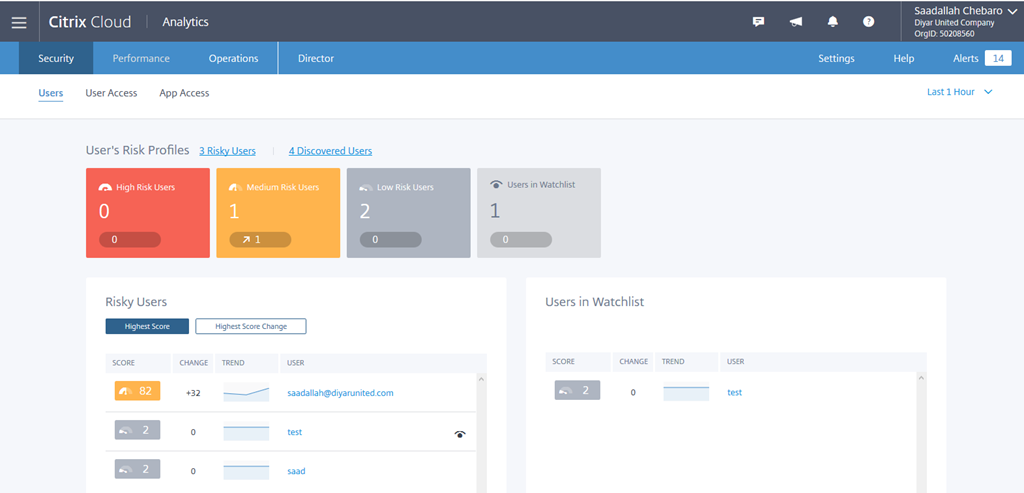
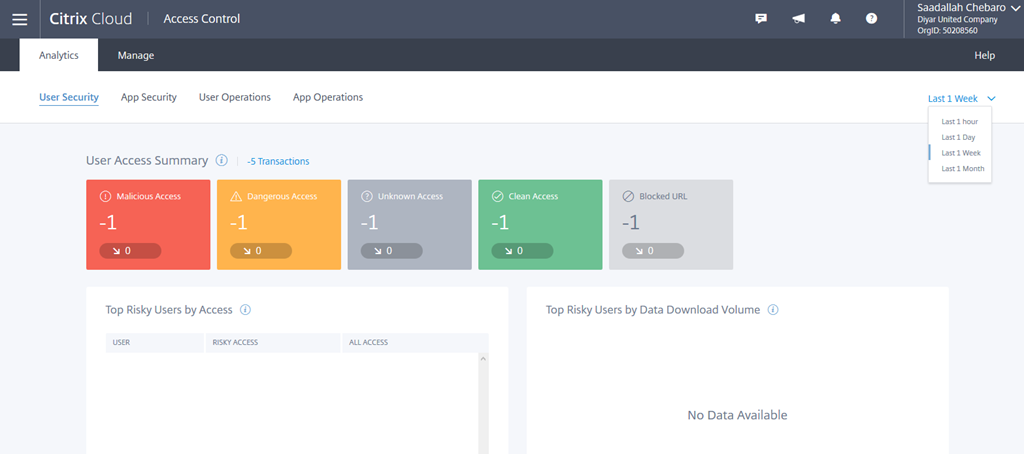
Access Control Analytics provides a holistic security overview on what Access Control has detected and acted upon in terms of User Security, App Security, User Operations, and App Operations. Note it may take some time for results to reflect in the portal.
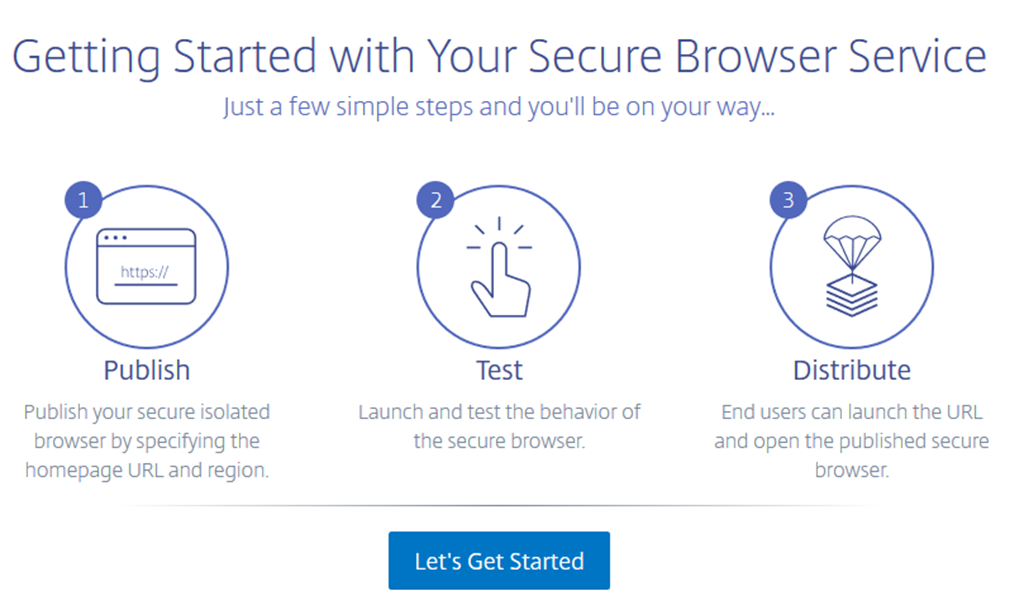
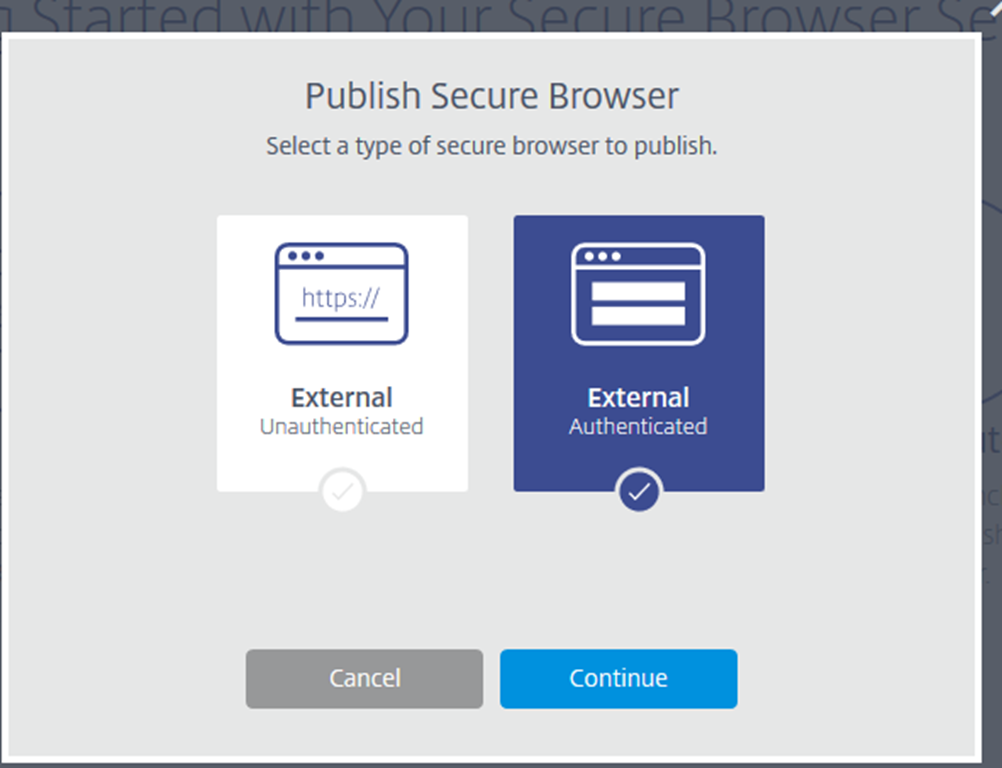
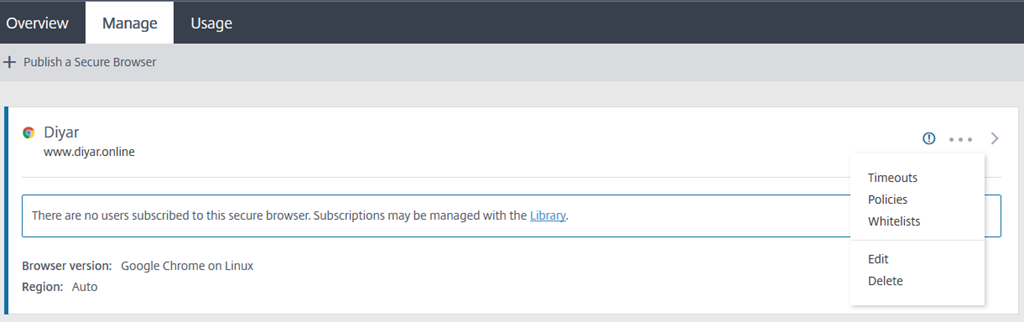
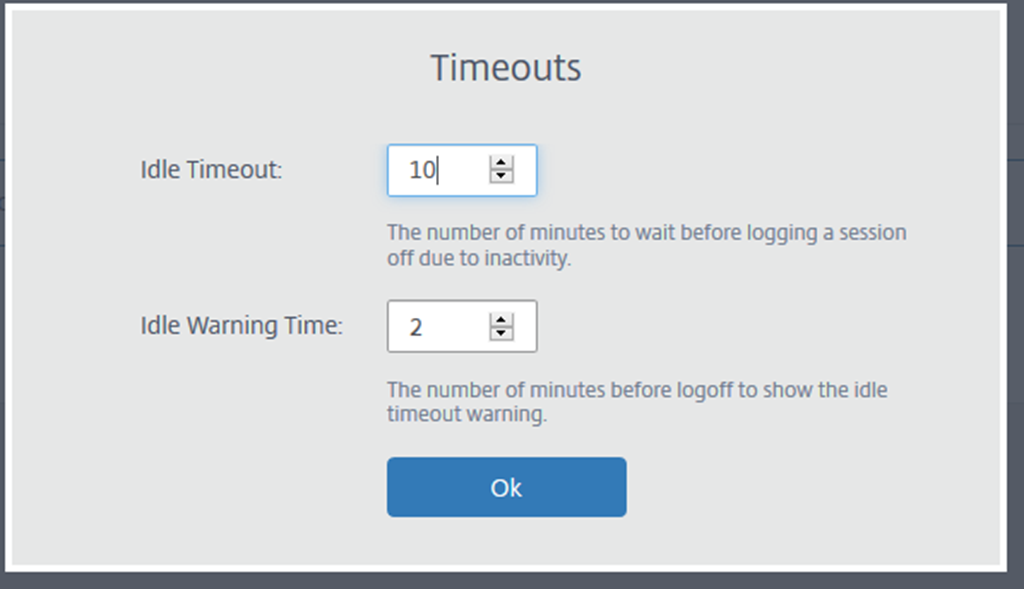
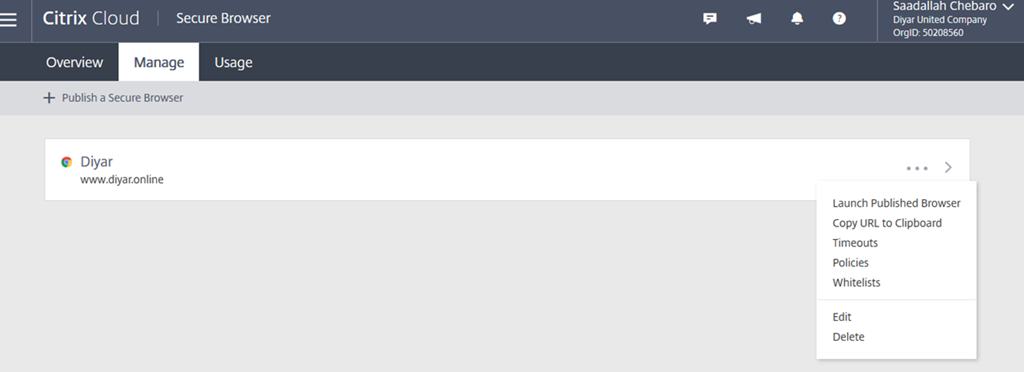
Secure browser publishing is even simpler, lets browse to Secure Browser Service and publish an authenticated website:
Unauthenticated means that all users will be able to see the published secure browser and access it. Authenticated means, users will need to be assigned access through Library.
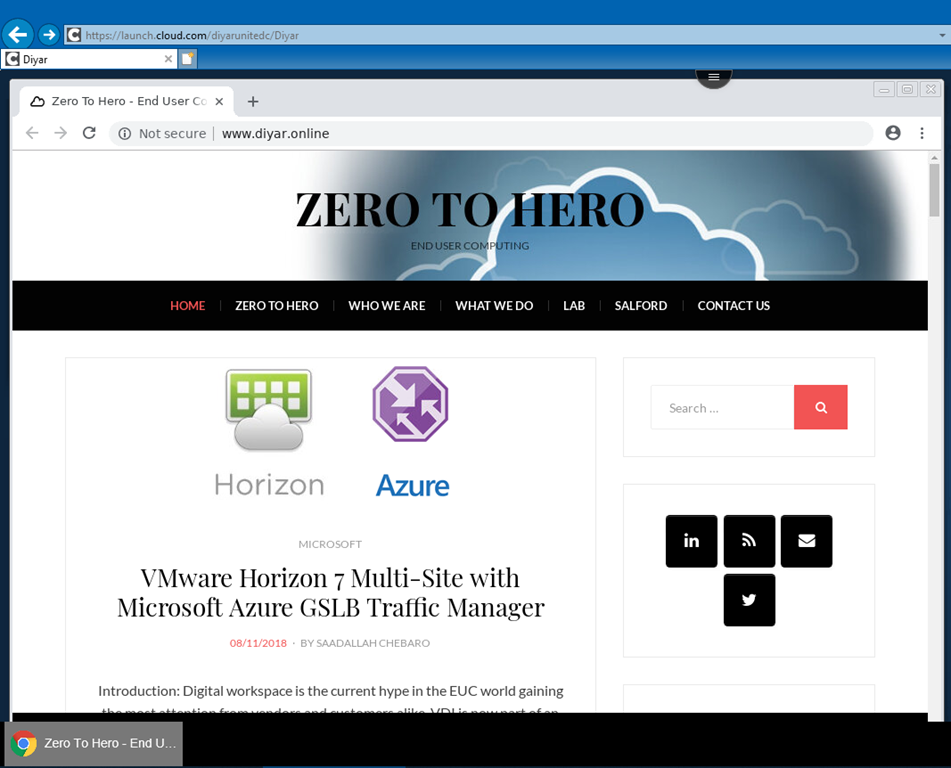
After access has been assigned for the secure browser using Library, users will be able to see the icon after they login to their workspace or an URL can be provided to them to open using any browser and get the embedded secure browser.
Access Control does not apply to Secure Browser and I can access betting sites. Another note here to Citrix is that, Secure Browser with Authenticated users seems to have mixed results as icons were taking too much time to appear and sometimes not authenticating users so if you notice that behavior do ping Citrix support.
A good practice here is to make sure that Secure Browser runs in Kiosk mode so that users cannot simply change the URL and browse openly.
Conclusion:
The shift from pure VDI to an integrated suite of EUC products forming what we now call as the digital workspace is changing the industry as we know it. Top that with the power of cloud introducing service integrations that analyze, correlate, and react making up the unified secure digital workspace of the future. Kudos to Citrix for embarking on this journey and allowing us, the community, to have a say on how things move forward.
May the Peace, Mercy, and Blessing of God Be Upon You