Introduction:
Customer implementations are never the same, every time I think I have seen it all , someone deals me a blow to the nuts and brings me back to reality.
In a recent Citrix XenMobile deployment, customer asked to block access to MAM and MDM web pages for security reasons. Totally understandable as if no VDI integration is required with MAM page and no self-service required for MDM page, why would you have an open authentication page publicly available for all types of security attacks ( XSS, SQL Injection, Brute Forcing , .. ).
I knew starting point would be NetScaler rewrite or responder rules but I had no exact Idea on how to establish this without breaking XM functionality so I called my buddy Arjun at Citrix and he was kind enough to provide me with the required procedure to block MAM page which I will detail in a bit.
For MDM page I did a bit of research and found a Citrix article which is a bit old and applies for XM 9 so I thought I would give it a try and see how to move on from there. One consideration here was that SSL OFFLOAD is a must for MDM LB vServer while the default configuration from Citrix was SSL BRIDGE.
MDM page block worked using only SSL OFFLOAD for MDM LB vServer and with a minor change from the original article since XM 10 had a different URL for self-service/administration. The original article for blocking MDM page is found here Mobility Experts: Restrict XenMobile Device Manager Admin Web Console Access From Internet When Deployed in SSL Offload Mode and for configuring XenMobile 10 with SSL OFFLOAD follow this Citrix article XenMobile 10 MDM SSL Offload Configuration .
Configuration:
Blocking XenMobile 10 MAM Access Gateway page ( All credit goes to Arjun Muralidharan ) :
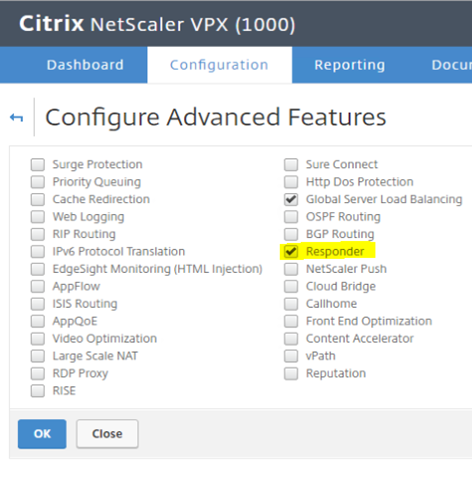
1- Enable Responder feature on NetScaler ( System – Settings – Configure Advanced Features ).
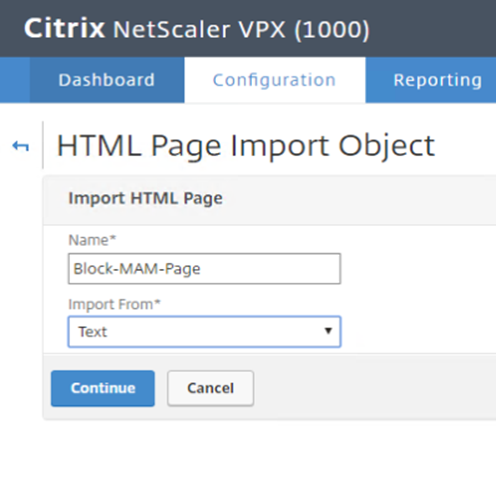
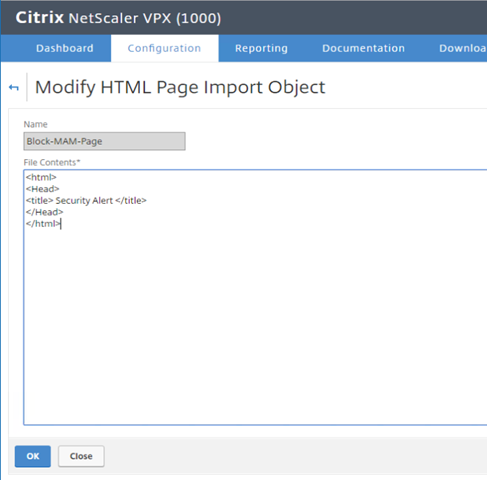
2- Create Responder HTML Page ( AppExpert – Responder – HTML Page Imports – ADD ).
3- In here you can put any HTML page content that you would like a user to see when trying to access the MAM AG web page. I would rather put no body here to throw script kiddies away so I will only put a header.
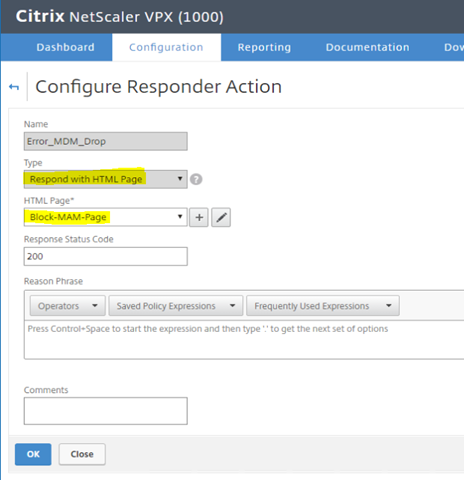
4- Create a Responder Action ( AppExpert – Responder – Actions – ADD ).
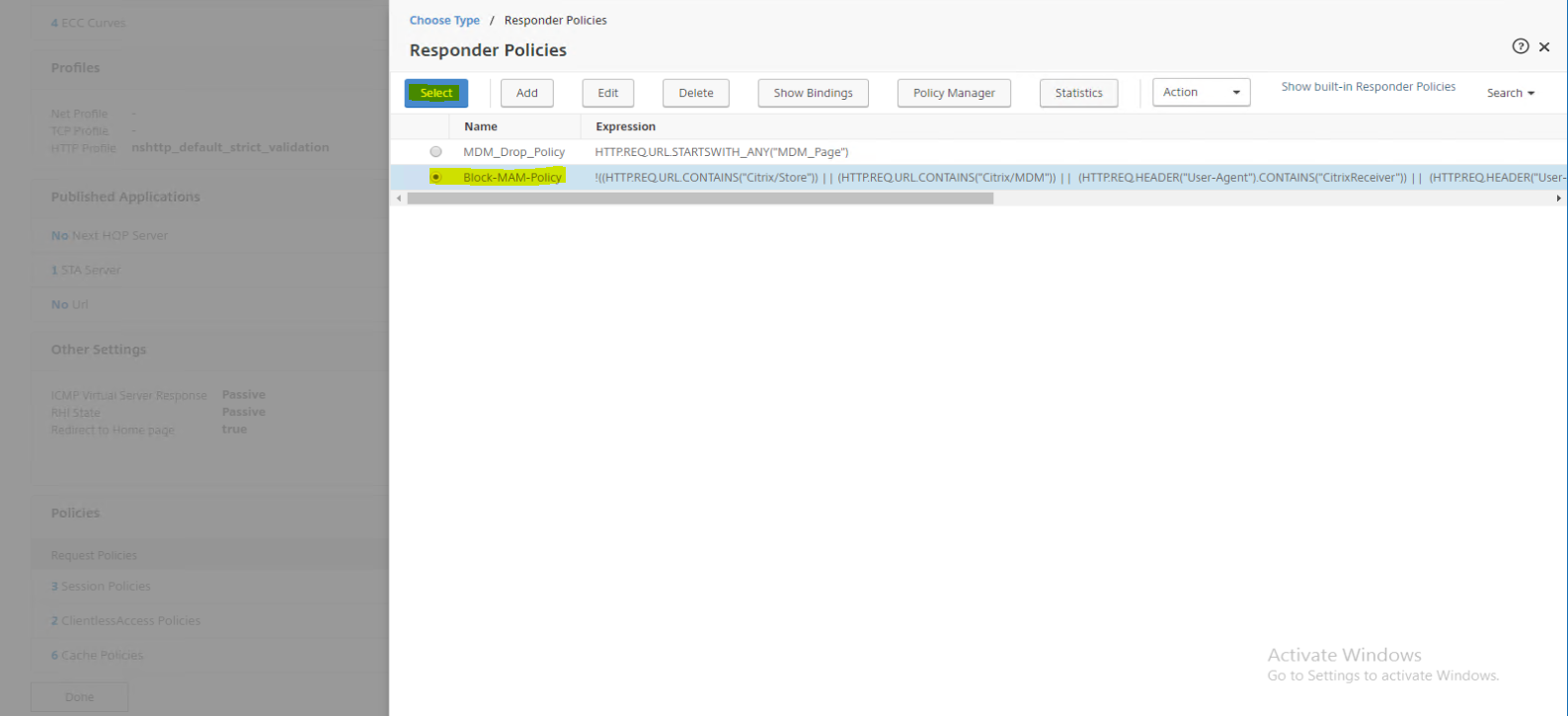
5- Create a Responder Policy( AppExpert – Responder – Policy – ADD ).
HTTP.REQ.URL.EQ(“/vpn/index.html”)&& HTTP.REQ.HEADER(“User-Agent”).CONTAINS(“Mozilla”)
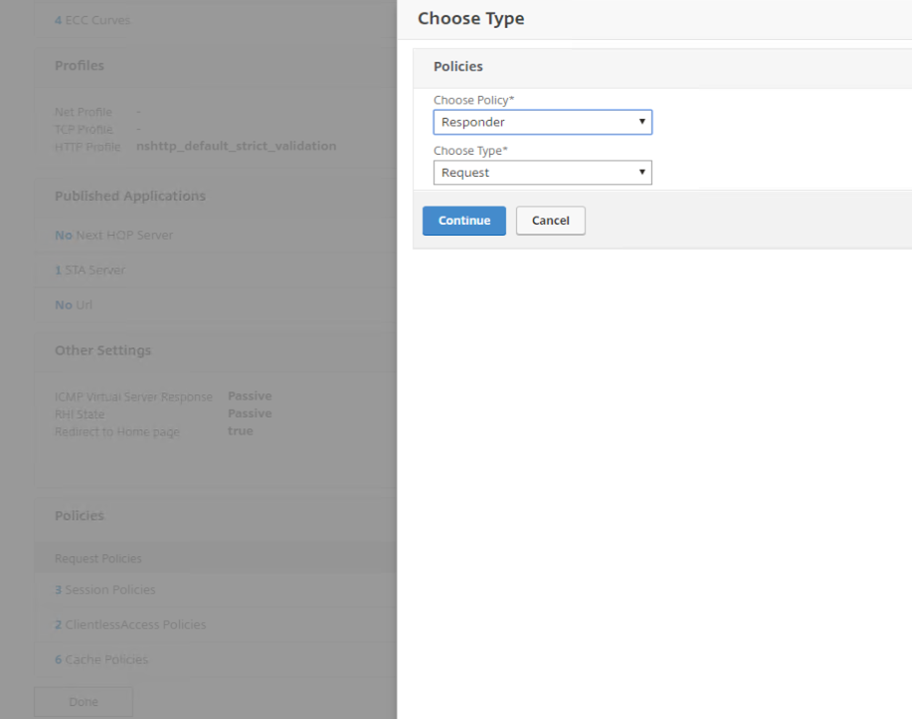
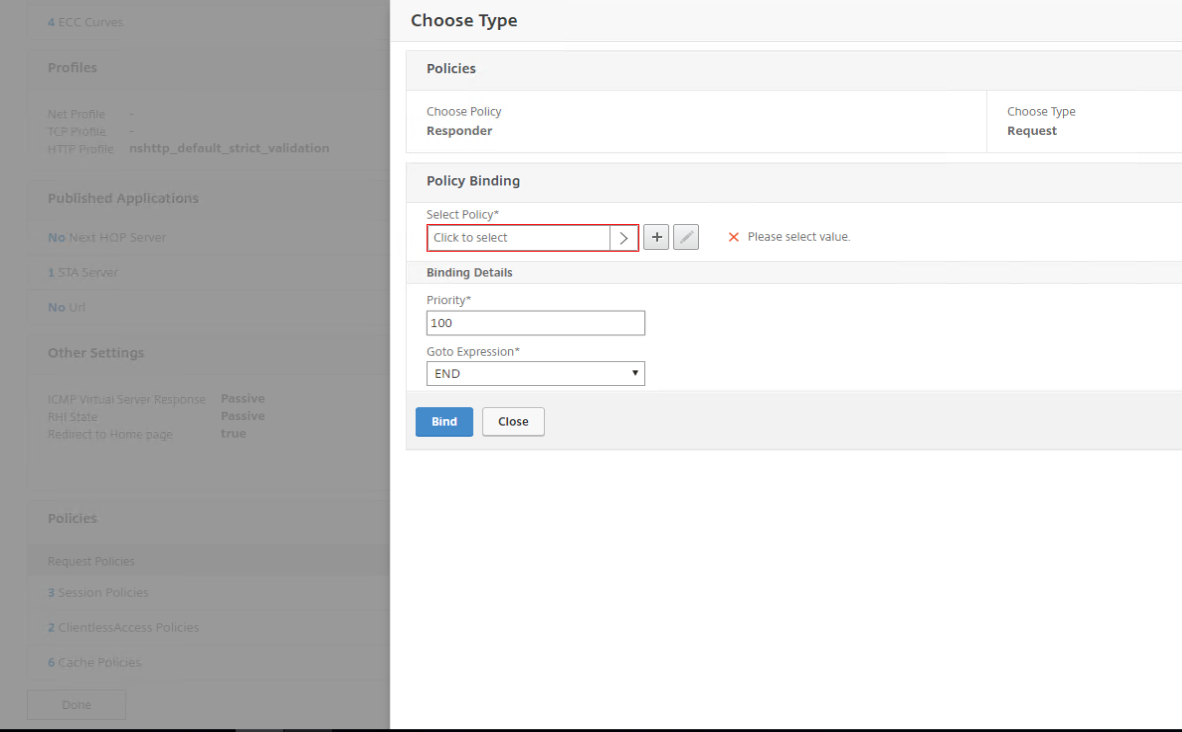
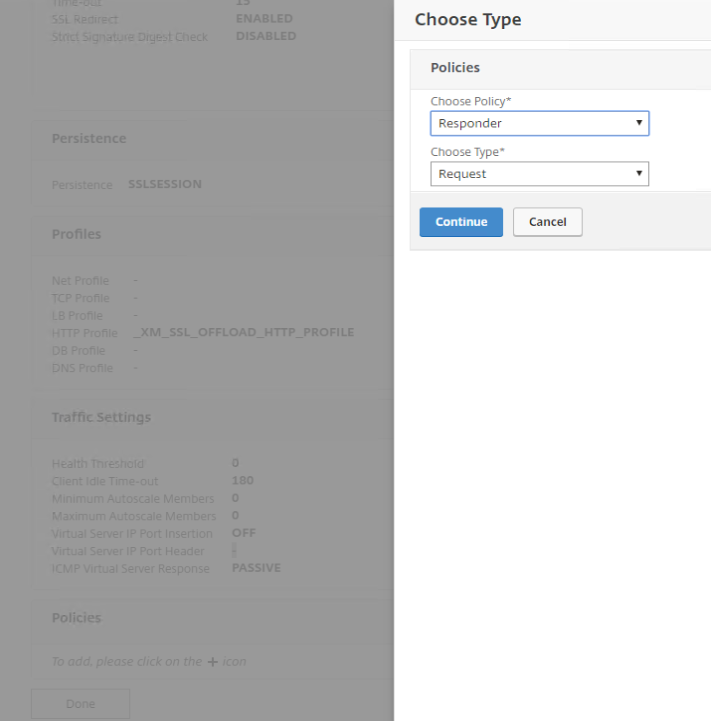
6- Assign Responder Policy to Access Gateway ( NetScaler Gateway – Virtual Servers – Edit MAM virtual server – Add Policy – Responder/Request – Select Policy & Bind – Save NS Config ).
7- Access URL for Testing ( https://mam.diyarunited.com ).
Notice the page is empty because in my HTML response I put no body and notice the header is as stated earlier in HTML response.
If you are using XenMobile as an IDP for ShareFile, the policy might block functionality so to solve the issue refer to a great post by Arnaud Pain:
XenMobile: Restrict MAM access, what about Sharefile with XMS as IDP?
Block XenMobile 10 MDM Self-Service and Administration Page:
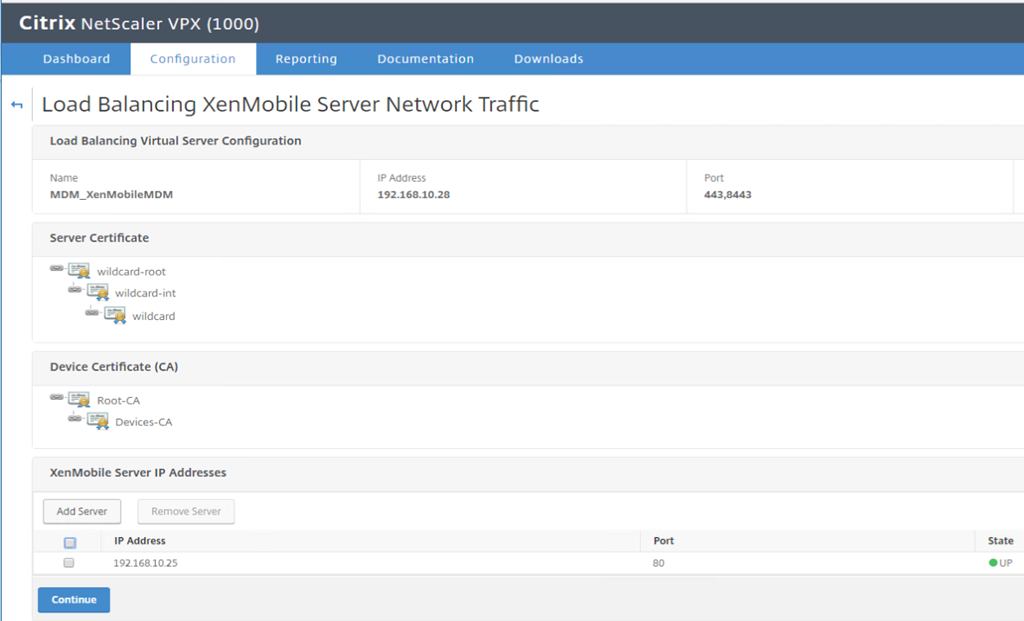
1- Change MDM LB virtual server to SSL OFFLOAD instead of default SSL BRIDGE. Note the following from Citrix:
Open Port 80 on XenMobile 10 using console ( Configuration – Firewall – Enable Port 80 ). Make sure port 80 is open between NetScaler Subnet IP NSIP and XM instances.
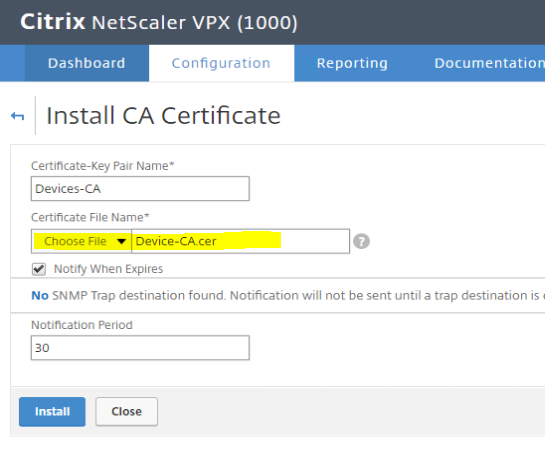
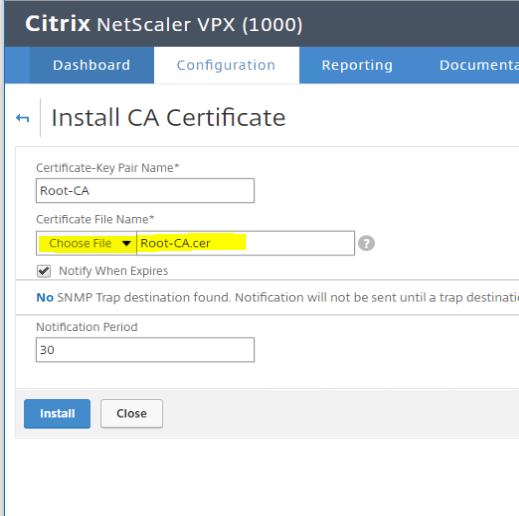
Export XenMobile CA certificate and separate Devices/Root CA certificates.
Edit download .pem with NotePad++ , copy the first part of the certificate which is the Devices CA to a seperate .cer file called Devices-CA.cer and copy the second part which is the Root CA to a seperate .cer file called Root-CA.cer then import into NetScaler Root CA directory. Past each cert text part into a seperate text file and rename file extension to .cer incase this is something you have not done before.
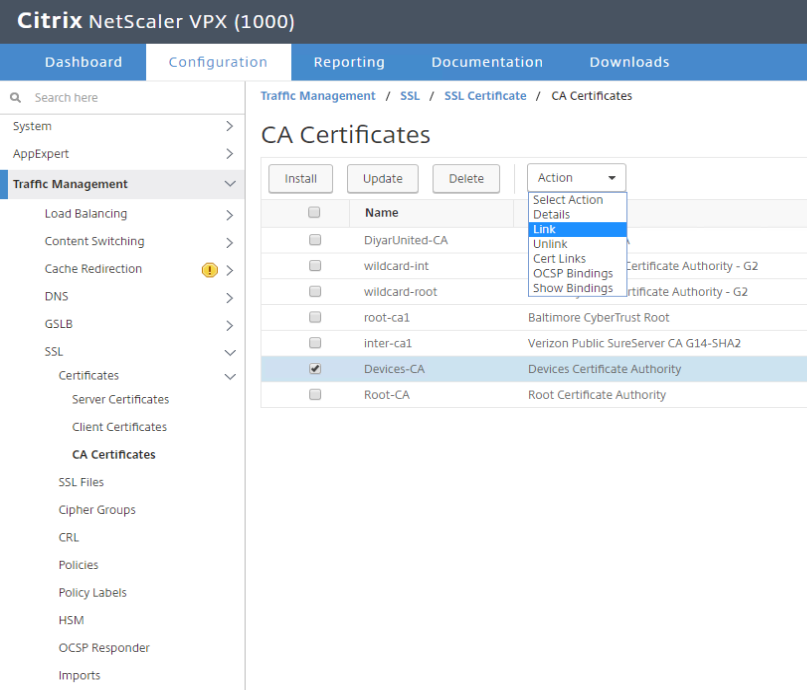
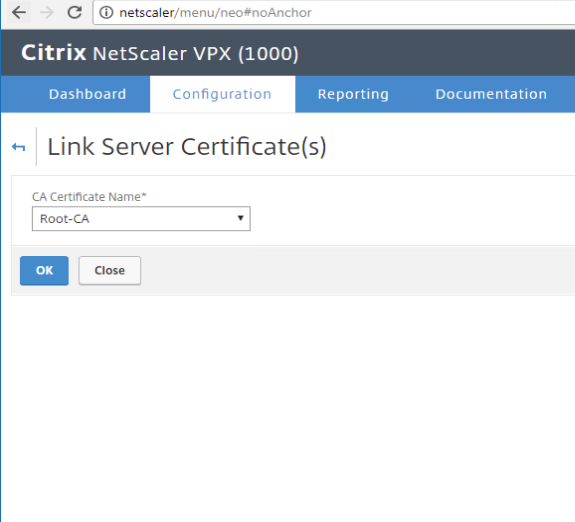
Import both certificates to NetScaler and link them accordingly ( Traffic Management – SSL – Certificates – CA Certificates – Install ).
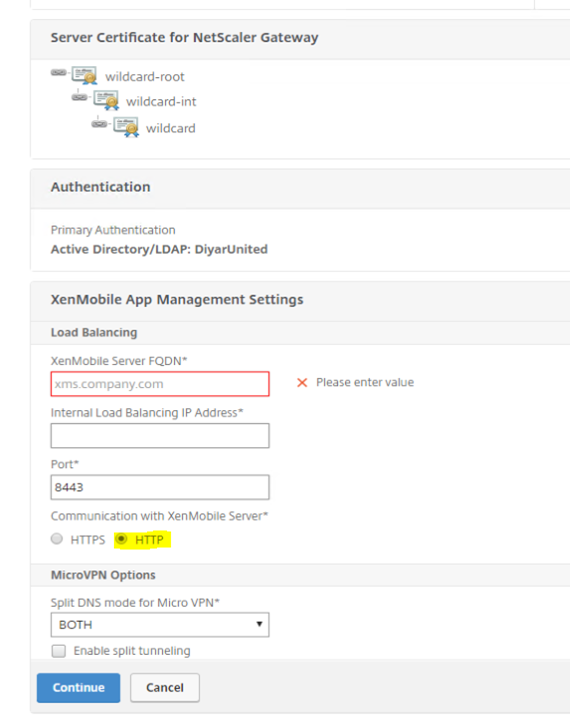
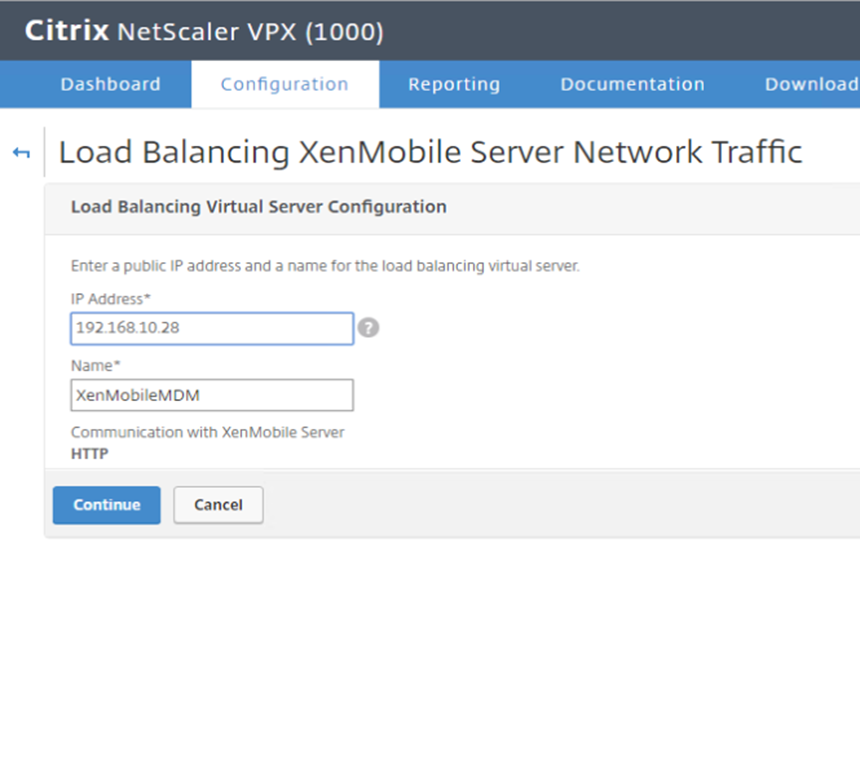
Now we need to reconfigure NetScaler MDM LB virtual servers for SSL OFFLOAD so we need to recreate MDM load balancing. Note if doing it through XenMobile Wizard , you need to recreate the while XM config including Gateway because initially gateway was created with HTTPS communication to XM so that cannot be changed by just deleting the XM LB and recreating it but rather the whole thing should be reconfigured with HTTP chosen as communication type for XM MDM.
When rerunning XM wizard on NS make sure to choose HTTP.
Choose Device Certificate CA that was upload to NS earlier from XM ( Devices-CA ).
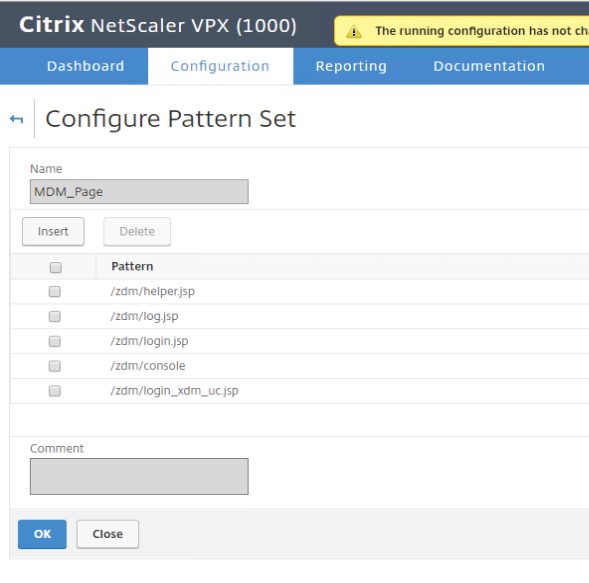
2- Create A Pattern Set ( AppExpert – Pattern Sets – Add ) .
/zdm/console
/zdm/login.jsp
/zdm/log.jsp
/zdm/helper.jsp
/zdm/login_xdm_uc.jsp
Note here that I have added /zdm/login_xdm_uc.jsp which is the new path for XenMobile 10 and is not present in Citrix article since it relates to XM 9.
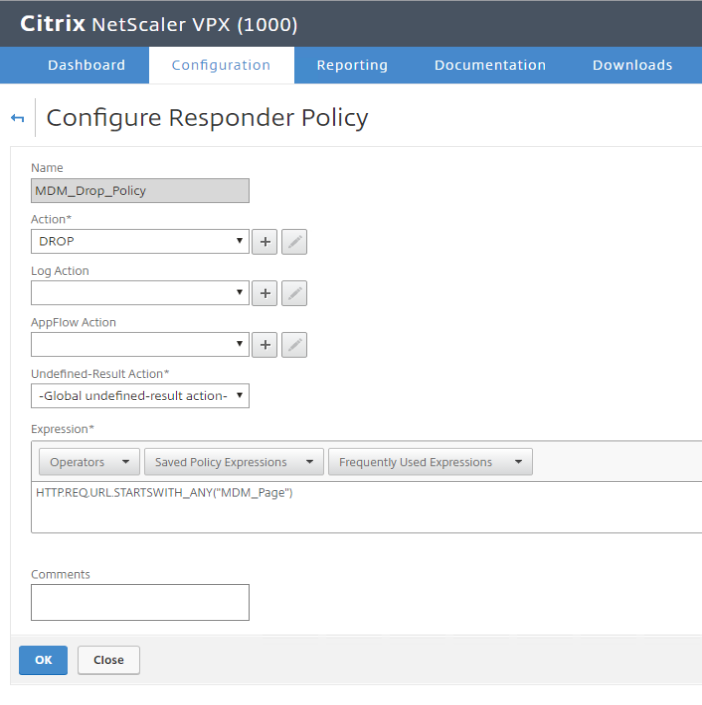
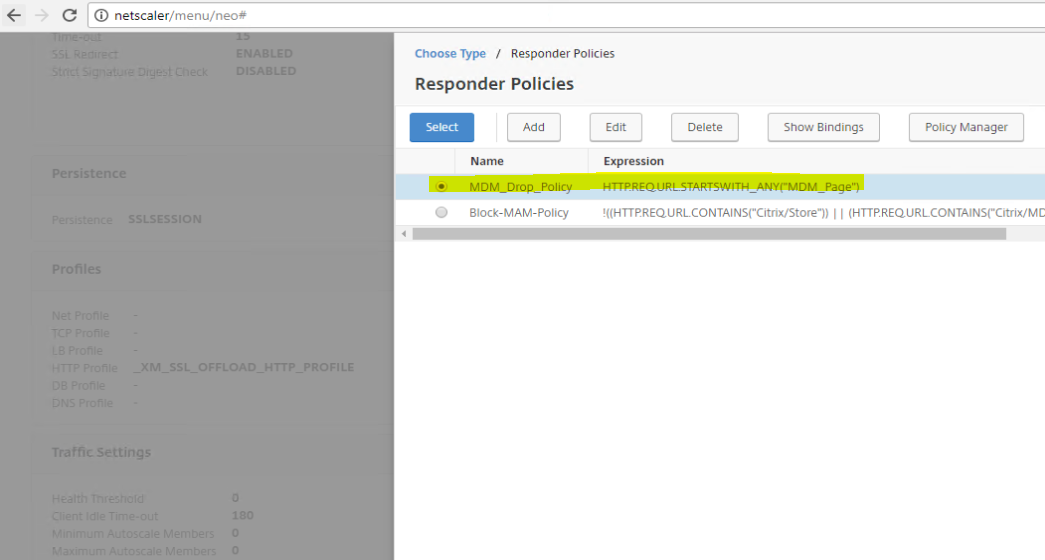
3- Create a Responder Policy ( AppExpert – Responder – Policies – Add ). MDM_Page is the name of the pattern set created earlier.
HTTP.REQ.URL.STARTSWITH_ANY(“MDM_Page“)
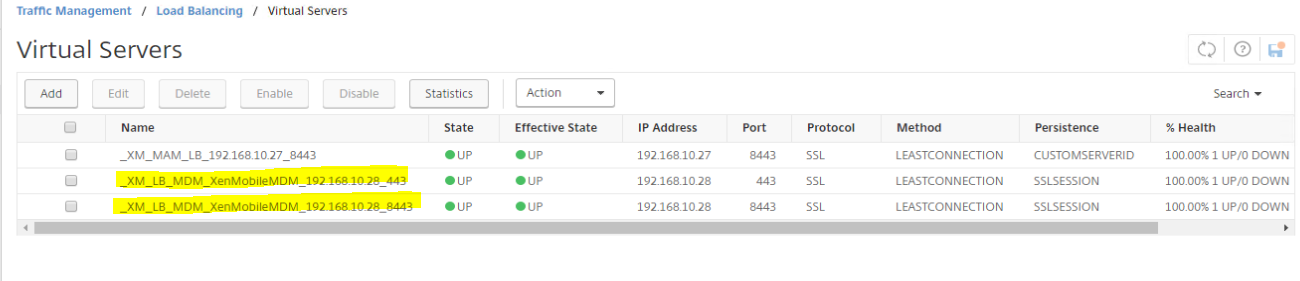
4- Add Responder policy to MDM LB vServers hosted on both 443 and 8443 to block both ( Traffic Management – Load Balancing – Virtual Servers – Edit MDM LB both 443 and 8443 – Policies – Responder/Request – Bind ).
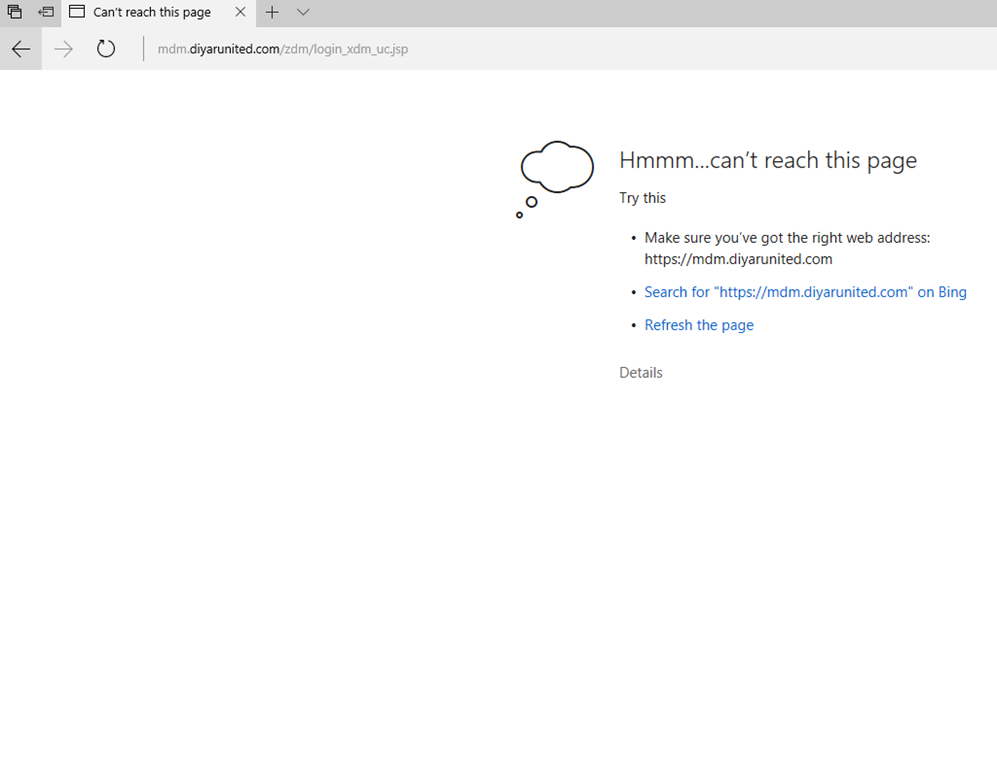
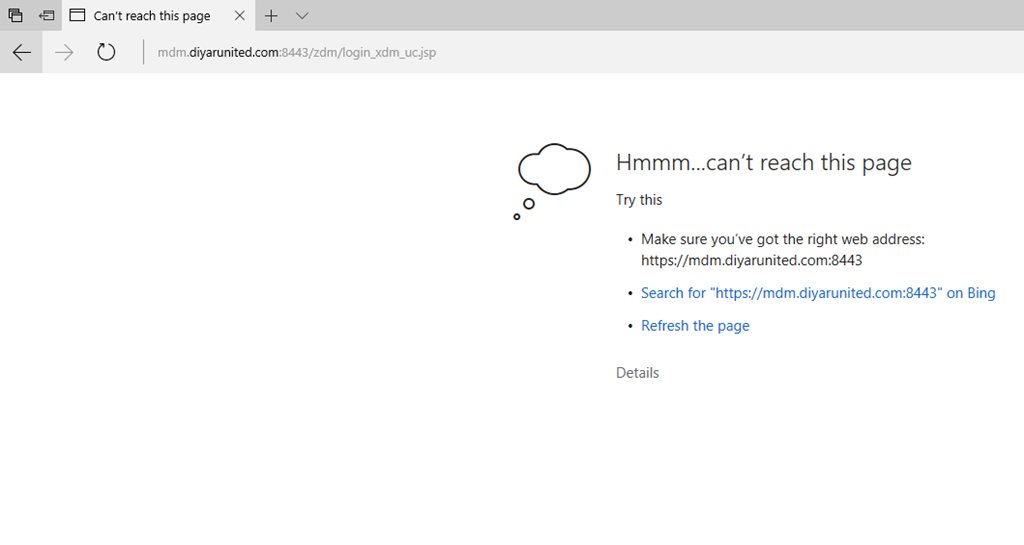
5- Test
Port 443 .
Port 8443 .
Salam ![]() .
.

Hi,
Thanks for this article.
I have tried the settings for MAM access, however it’s not working, I loose device connection with the responder Policy 🙁
Are you sure about the settings?
Thanks
ACB
Hi Anne-Carole,
I did get some feedback that this is breaking MAM connections for some users , I have written an update inside the post with a new expression which should work for everyone. Do let us know.
Thanks.
Hi Saadallah,
Tested and it works like a charm!
Hi
is there a way to do the same but if we are using SSL Bridge.
if not, do you know the justification.
kindly advice
thx
mohamed
Hi Mohamed,
No it is not possible because you cannot assign a responder policy to an LB vServer with SSL Bridge.
Thanks.