Intro:
Citrix NetScaler HA on Microsoft Azure Ultimate Guide
Some time ago I wrote an article on how to Configure Multiple VIPs for Citrix NetScaler VPX on Microsoft Azure ARM “The Old Fashioned Way” in which I stated that an Azure feature exists in technical preview to configure multiple private and public IPs per NIC or multiple NICs with multiple private and public IPs for a single VM on Azure ARM. Couple of days ago the feature went GA and is now officially supported by Microsoft ( https://docs.microsoft.com/en-us/azure/virtual-network/virtual-network-multiple-ip-addresses-portal ).
Citrix acted fast and updated there documentation to reflect the same on both standalone and HA NetScaler deployments on Azure ARM ( https://docs.citrix.com/en-us/netscaler/11-1/deploying-vpx/deploy-vpx-on-azure/configuring-multiple-ips-for-vpx-in-standalone-mode.html ) while Brian from Citrix published a video demo on the same subject ( https://www.youtube.com/watch?v=NCzM2YXiXgk&feature=share ).
I felt it was a good move by Citrix to accommodate the same in a fast manner and actually support this type of deployment following in the footsteps of Microsoft because if you take a look at the old fashioned way this had to be done, it was messy to say the least and to make matters worse, AWS did not have this kind of single IP mode limitation and required different subnets with load balancers to accommodate multiple VIPs. Everyone knows Citrix lack in the area of adequate documentation, at least they do not give you the overall picture, ask Carl Stalhood and other active community members, and for this configuration specifically they only documented it using Azure PowerShell and did not explain how things have changed going forward.
Before diving into the actual configuration steps, lets take a look on what changed. Before an Azure VM could be assigned one NIC and that NIC could only accommodate one Private/Public IP with one NSG to apply Port Forwarding rules on L4. because of that, single IP mode for NetScaler had another limitation in which many ports including 80 & 443 the most well known ports out there for external services where reserved by NetScaler so they cannot be used. That meant that you could have only one IP that will host all NetScaler services and you can have one port only for every service. Now you might say fine you can use NSG, create different ports internally and port forward them through different NSGs to the IP/Port used on NetScaler, You Wish ![]() , unfortunately only one NSG can be assigned to a NIC thus a VM so ultimately the end result was that you can only publish 443 for one service for the whole NetScaler instance. Still in the before stage the solution to overcome this limitation is by creating multiple Azure public cloud IP addresses and from within the a new Azure load balancer direct traffic to the NetScaler VPX which will still have a single IP with each service having different port. To make it as clear as possible, NetScaler will still have one IP, each service on NetScaler ( LB or AG or CS) will have that same single IP but with different internal ports ( Not the reserved ones), Azure load balancer would have public IPs one for each service and this same load balancer can create different load balancing rules utilizing different IPs ( which NSG can NOT ) specifying that this public IP would go to this port and the same goes for other services each public azure IP would be bound to that port.
, unfortunately only one NSG can be assigned to a NIC thus a VM so ultimately the end result was that you can only publish 443 for one service for the whole NetScaler instance. Still in the before stage the solution to overcome this limitation is by creating multiple Azure public cloud IP addresses and from within the a new Azure load balancer direct traffic to the NetScaler VPX which will still have a single IP with each service having different port. To make it as clear as possible, NetScaler will still have one IP, each service on NetScaler ( LB or AG or CS) will have that same single IP but with different internal ports ( Not the reserved ones), Azure load balancer would have public IPs one for each service and this same load balancer can create different load balancing rules utilizing different IPs ( which NSG can NOT ) specifying that this public IP would go to this port and the same goes for other services each public azure IP would be bound to that port.
Now things have changed to the best because with the ability to add multiple Private/Public IPs on NetScaler, Single IP mode is not required anymore thus first we do NOT have any reserved ports and secondly public IPs do not require a load balancer in the middle to translate into private IPs as this is done automatically by Azure. This will allow us to host multiple services internally on the NetScaler with the port required 80/443/ or otherwise and instruct NSG to open those ports to the public if we choose to publish them. Note here that you still need a public IP to be associated with a private IP if you want to publish the service to the internet because remember One NSG can be assigned to a single NIC even if the NIC has multiple IPs, this means that if you open port 443 on this NSG and several public IPs are mapped to a single private IP, NSG does not know to whom it should forward the port 443 packets. If a single NSG has port 443 open and this NSG is assigned to a NIC with multiple private/public IPs, what happens is that we know for a fact each private/public IP can have only one same port for any given service so just opening that port on the NSG would open it to all private/public IPs associated with that NIC, ex. opening 443 would open port 443 for all public IPs associated with the NIC. If the service is not to be published to the internet , it is best not to associate a public IP with the private IP hosting that NIC so that this single NSG rule does not apply to it and causes you to publish a private 443 port service to the Web. Note that with no single IP mode and with multiple IPs, GSLB is now possible with NetScaler on Azure.
Now also we can assign multiple NICs with multiple Private/Public IPS per VM which would actually help in controlling published services because each NIC can have a different NSG thus different rules, I would say a best approach would be to assign two NICS to each NetScaler VM and assign one for internal use only and second for external use just like an on-premise environment with one leg to DMZ Nated outside and one leg to internal network. The default limit for private IPs per a network interface is 50 while the default limit for public IPs per a network interface is 60 dynamic and 20 static. Both of these default limitations can be extended if Azure team is contacted for the same. If the limits are not enough, adding more than a NIC is also applicable.
I doted what is on my mind going through this recent update and hope it was clear enough ![]() . Now lets jump into the actual configuration, I will configure a Single NIC with multiple Private/Public IPs and eventually publish a service on port 80. In my previous post on the old fashioned way, I did it purely with PowerShell but since Citrix already documented it in PowerShell, I am going to do it in full using Azure GUI. If time permits I will do a follow up post adding a second NIC with multiple Private/Public IPs as well which can as of now Only be done through PowerShell. Go over my previous post to configure prerequisites in terms of Resource Group, Virtual Network, and Subnets. Note that the first primary IP assigned to the newly created NetScaler would be the NetScaler Management IP NSIP and secondary IPs added can be assigned as Subnet IPs and Virtual IPs.
. Now lets jump into the actual configuration, I will configure a Single NIC with multiple Private/Public IPs and eventually publish a service on port 80. In my previous post on the old fashioned way, I did it purely with PowerShell but since Citrix already documented it in PowerShell, I am going to do it in full using Azure GUI. If time permits I will do a follow up post adding a second NIC with multiple Private/Public IPs as well which can as of now Only be done through PowerShell. Go over my previous post to configure prerequisites in terms of Resource Group, Virtual Network, and Subnets. Note that the first primary IP assigned to the newly created NetScaler would be the NetScaler Management IP NSIP and secondary IPs added can be assigned as Subnet IPs and Virtual IPs.
Configuration:
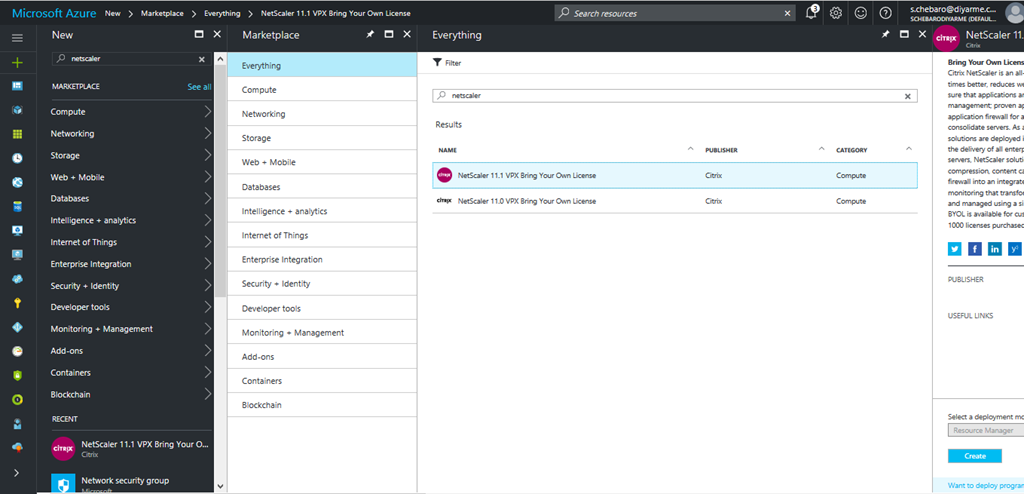
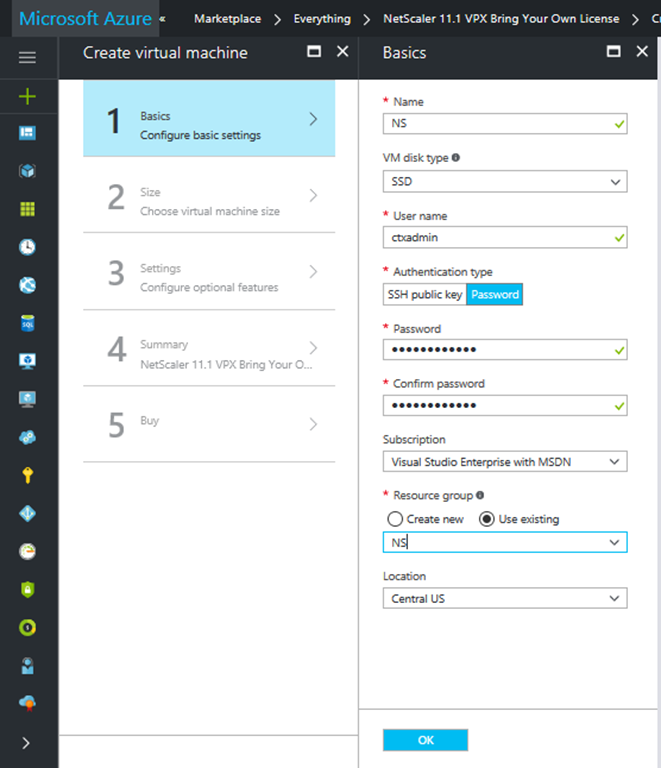
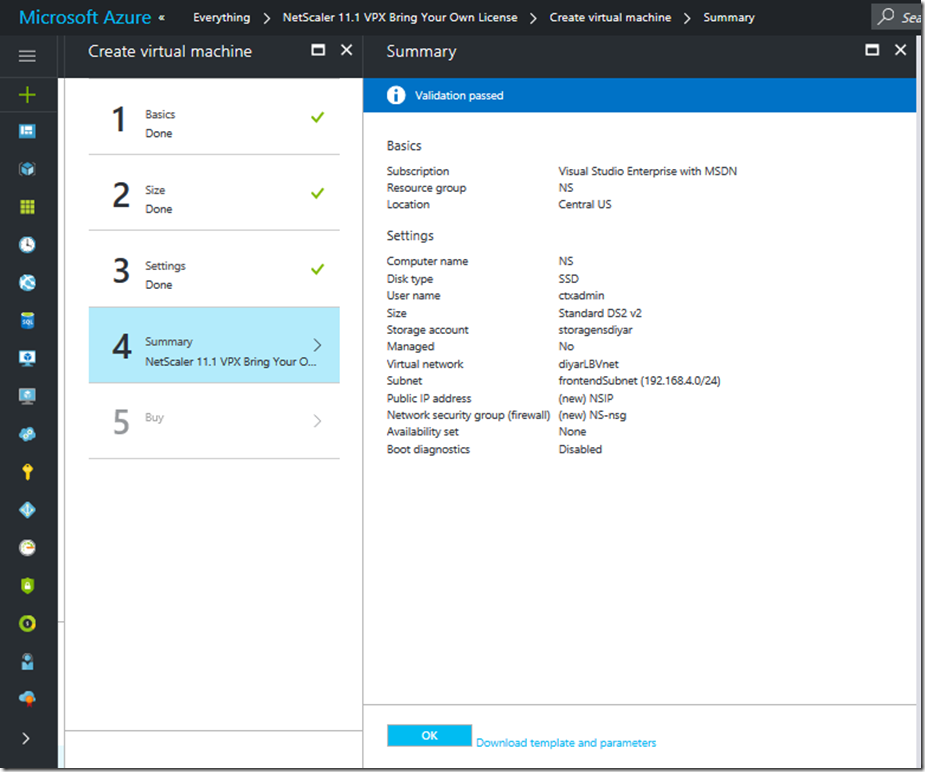
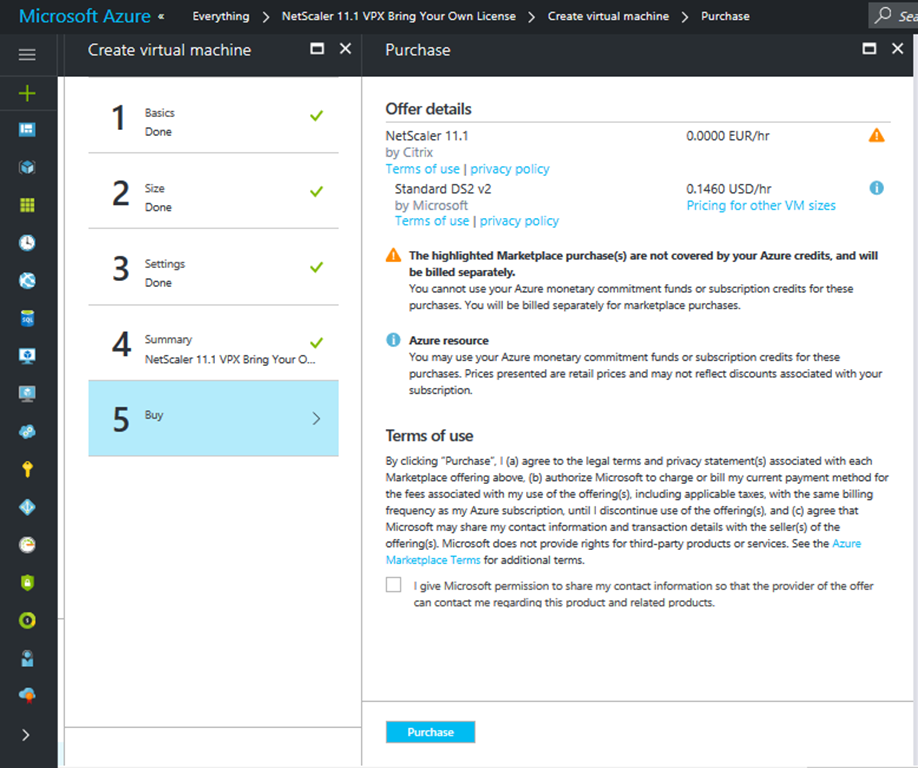
Create a new NetScaler 11.1 IaaS VM in Azure.
Make sure to use the Resource Group that already includes your virtual network and subnets.
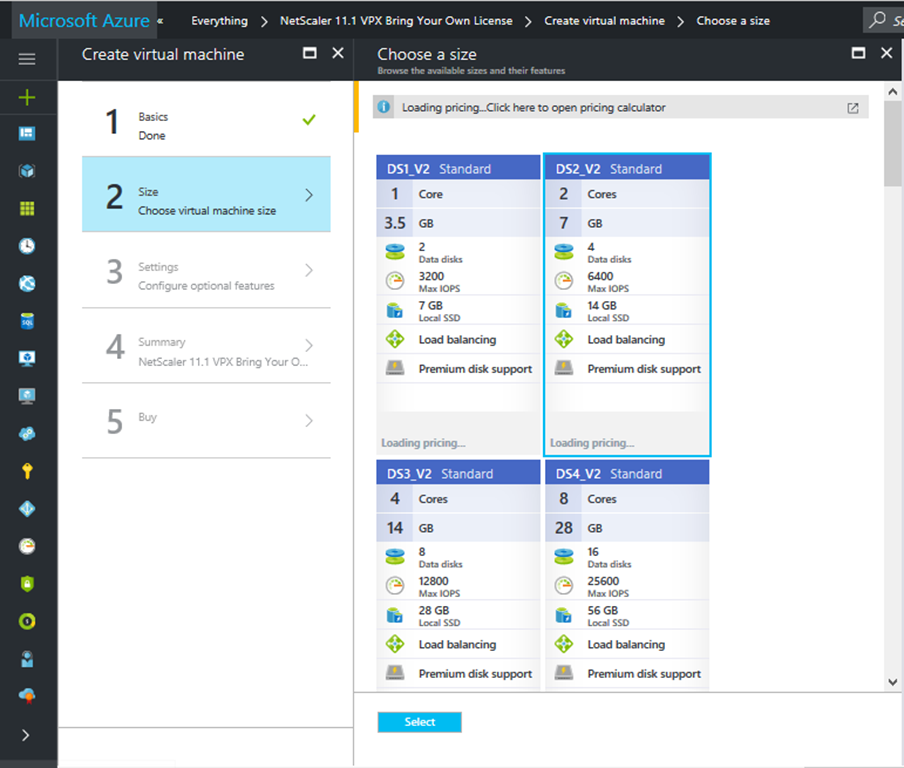
Choose the size depending on bandwidth requirements and make sure a minimum of 2 cores is selected.
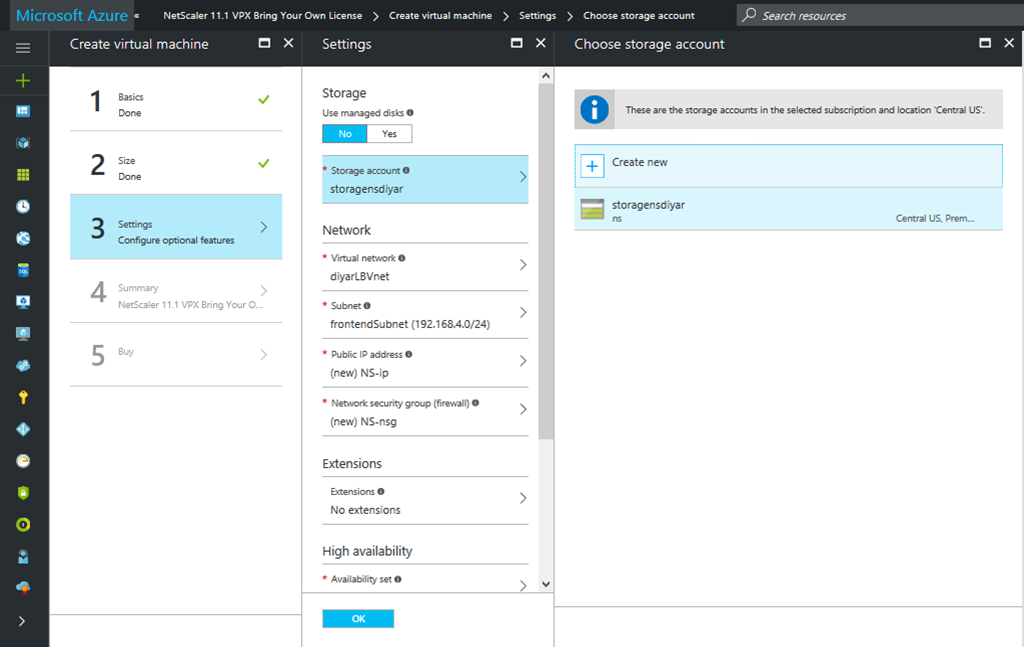
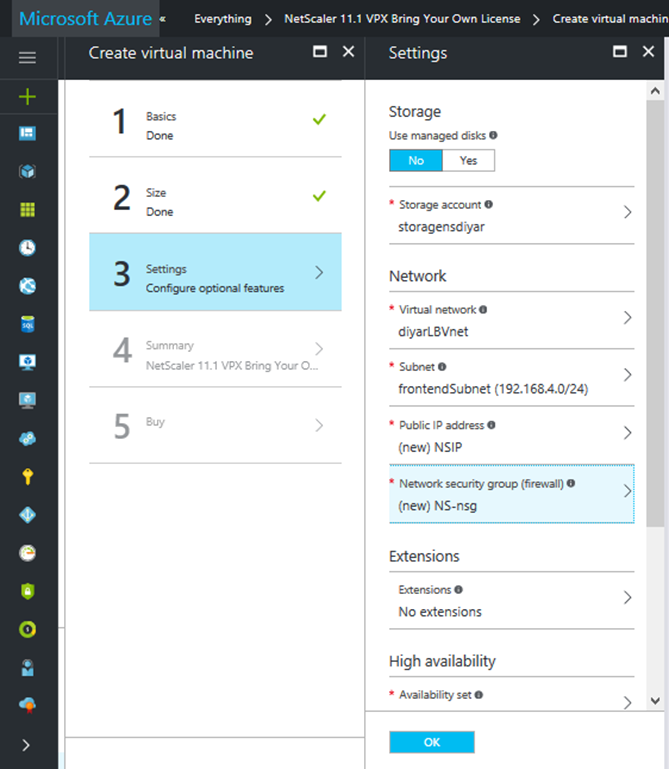
Existing or new storage account can be used.
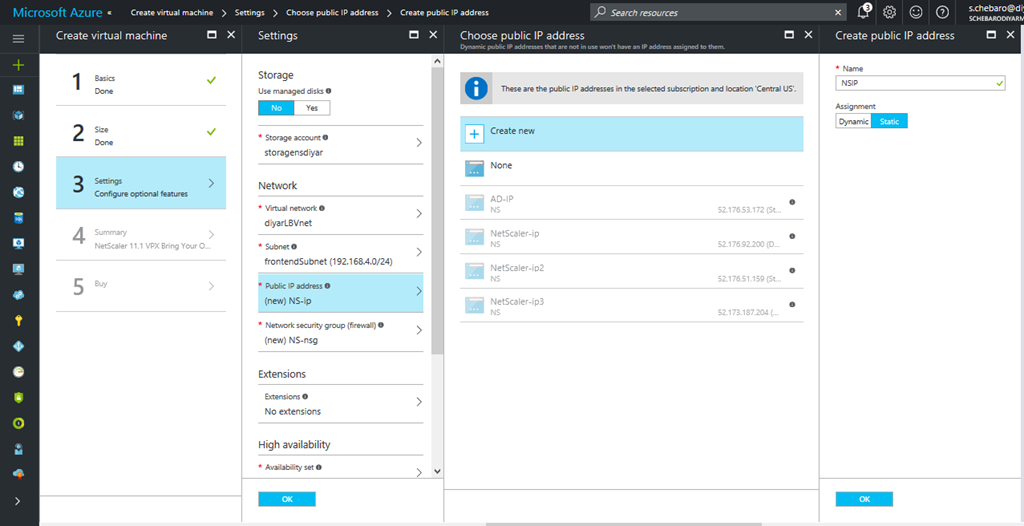
Make sure Virtual Network and Subnet are chosen correctly. Create a new public IP for NetScaler management IP NSIP “ this will be the primary IP” and make sure its Static.
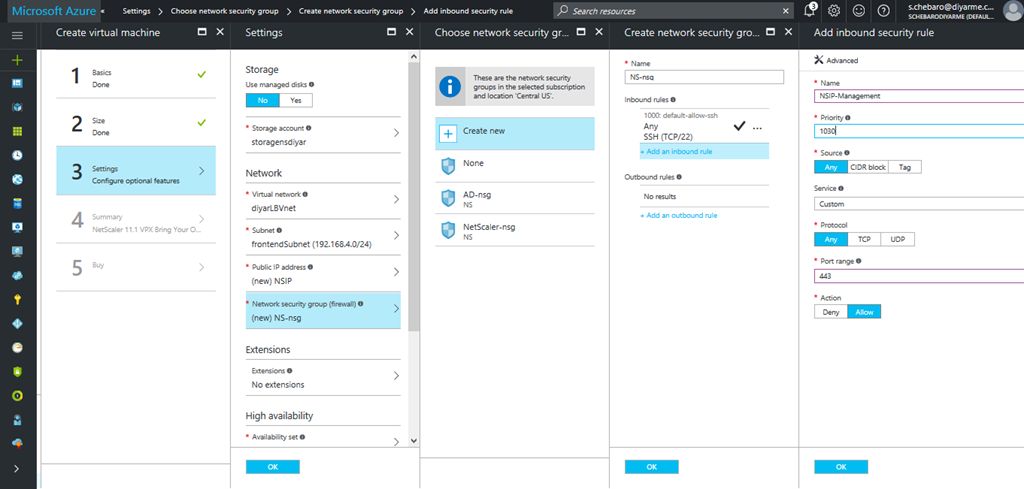
Create a new Network Security Group “NSG” , by default SSH 22 would be open for management, we will also open port 443 in order to access the NSIP externally and configure our NetScaler.
Add multiple private/public IPs for the NetScaler VPX instance. One Private/Public IP for NSIP , one Private IP for SNIP , one private/public IP for a test load balancer web server hosted on IaaS azure same vNet. I have a VM called “AD” which has default IIS added on port 80.
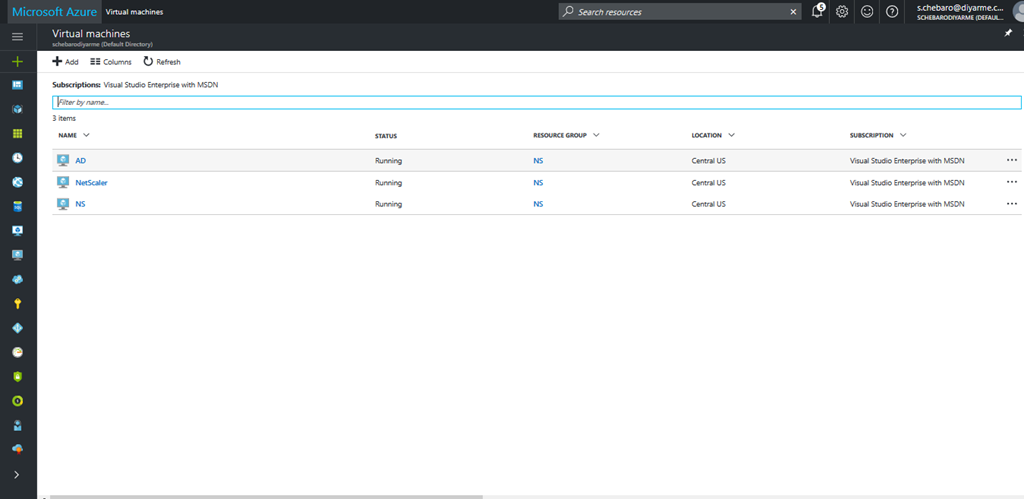
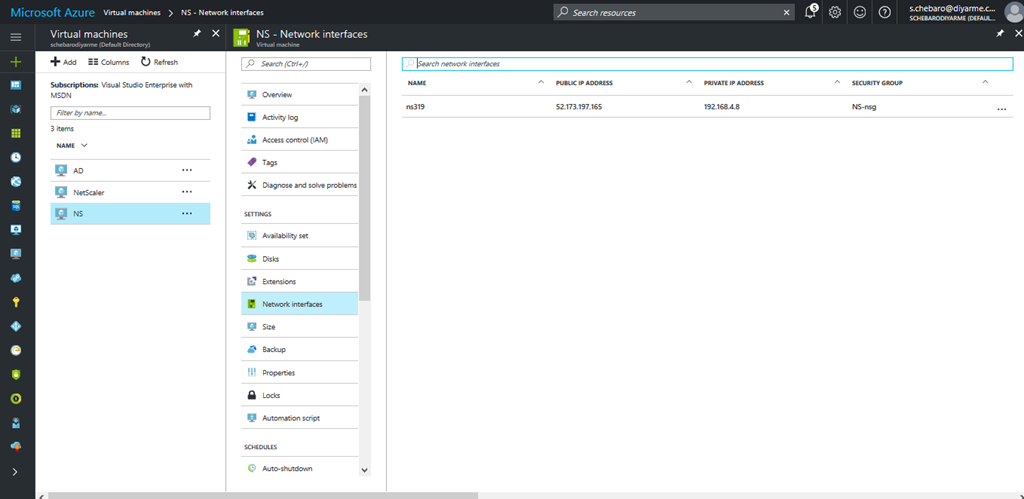
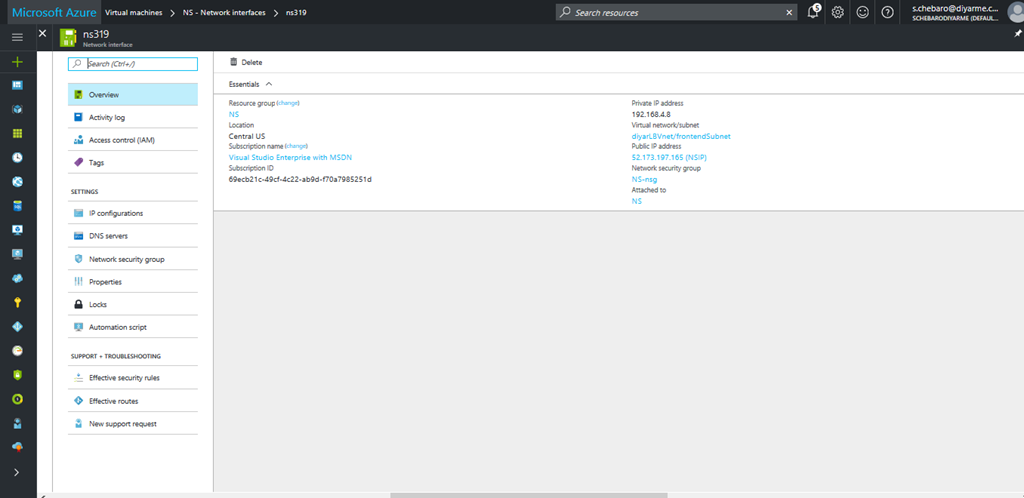
Go to recently created NetScaler “NS” in Virtual Machines tab on the left and navigate to Network Interfaces.
Click on the interface
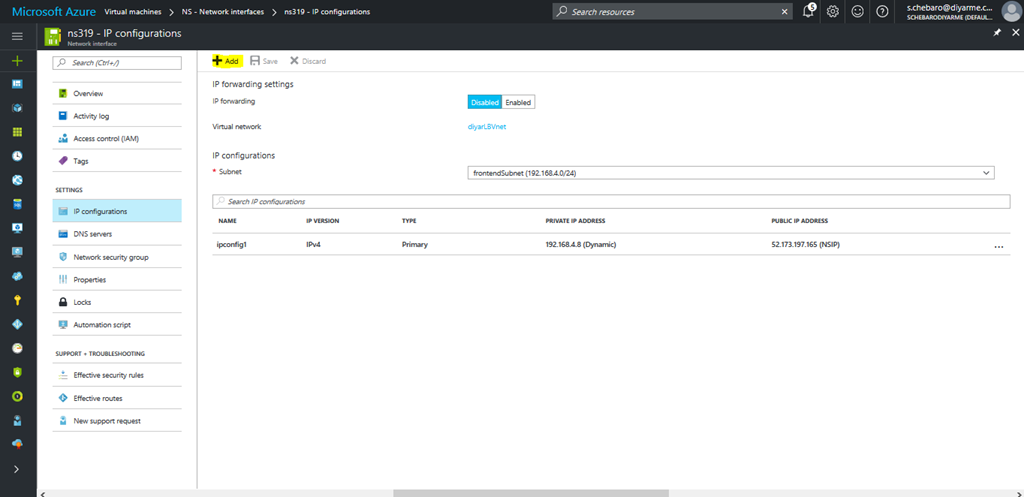
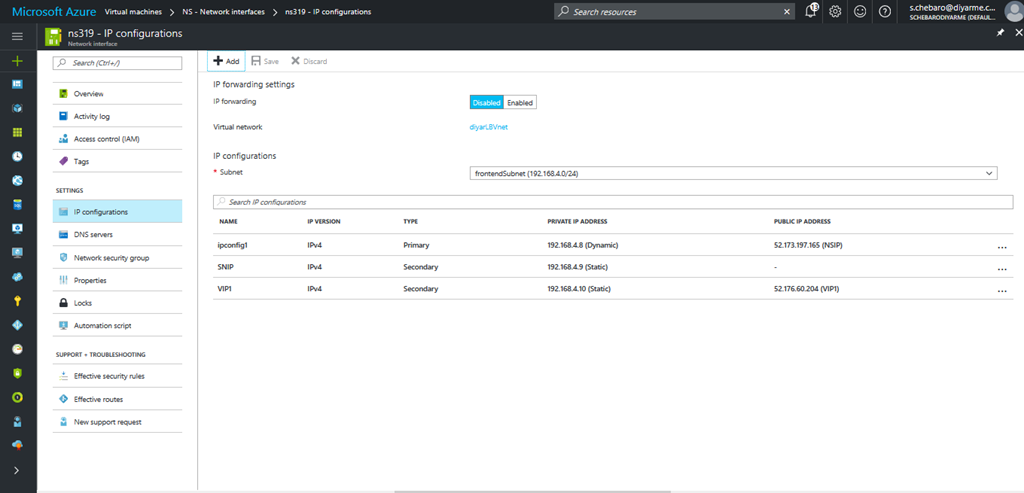
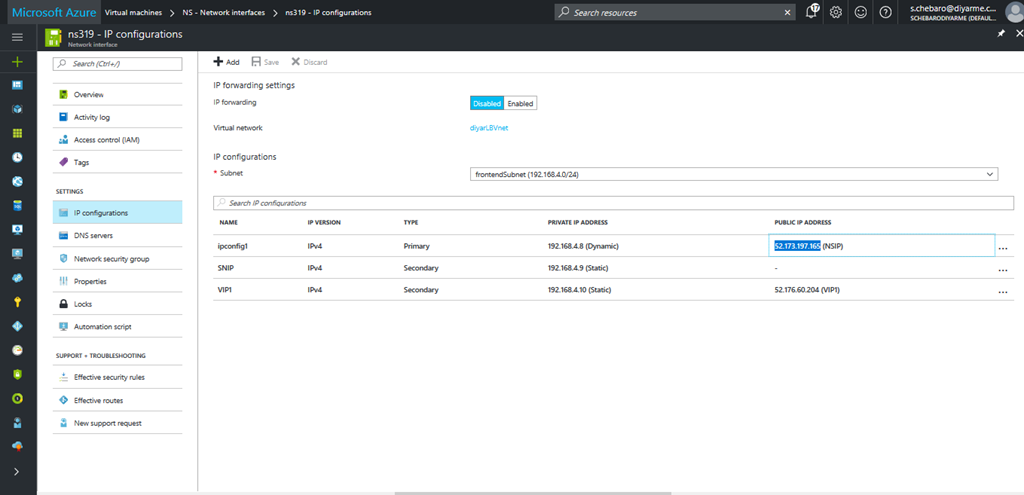
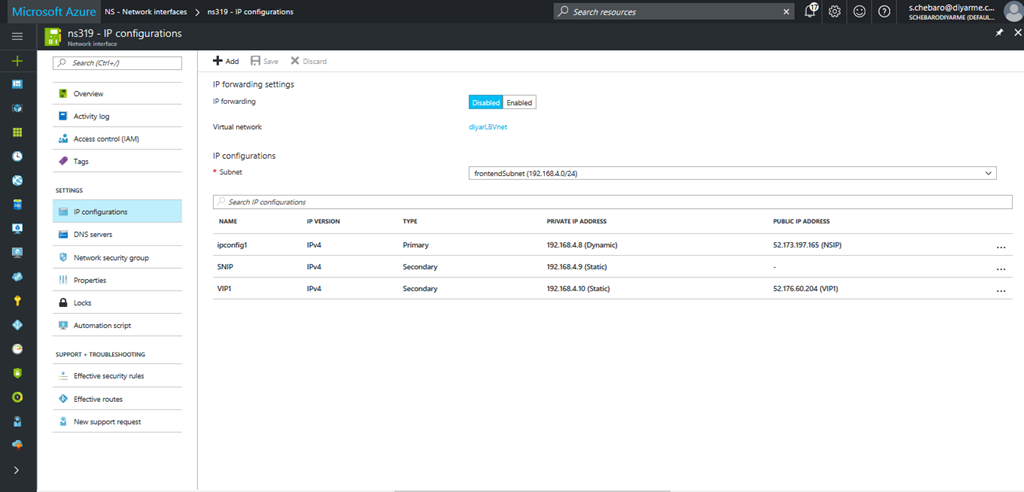
Navigate to IP Configurations. Note the Primary private/Public IP created by default when NetScaler was created earlier. Click on the ipconfig1 IP.
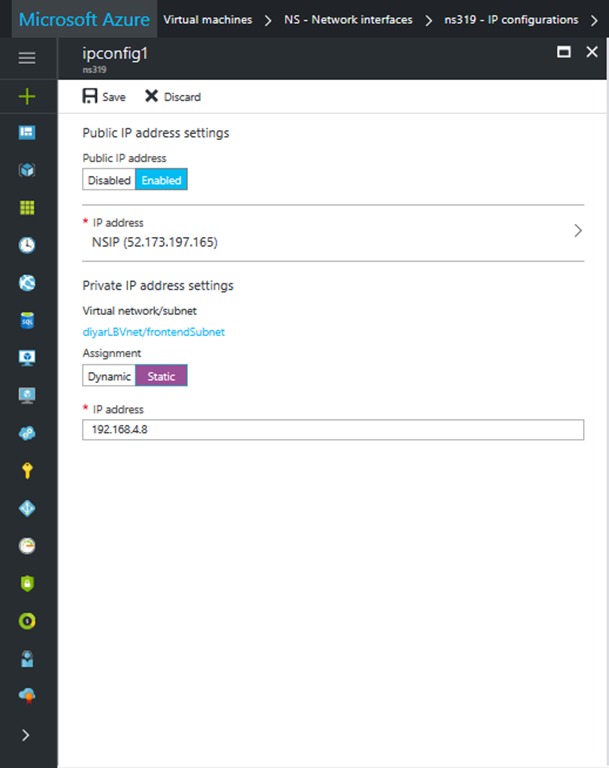
First make sure NSIP is in Static assignment and save. This would make sure that when NetScaler is restarted the internal IP is not going to change.
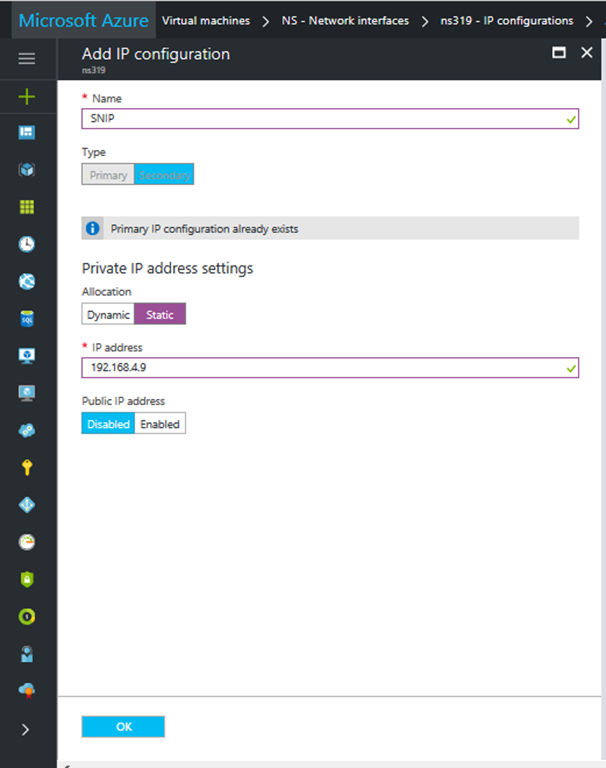
Click on Add. No need to add a public IP to the private IP of the NetScaler Subnet IP unless you want to use it for GSLB and require internet connectivity. Make sure Private IP is Static.
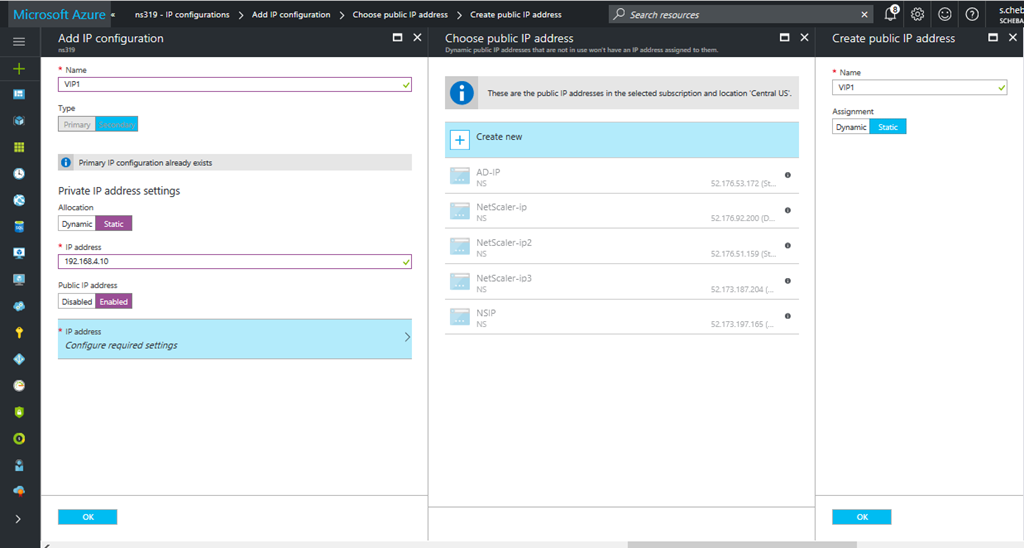
Click Add one more time to add another secondary private IP which will act as a VIP for the load balanced web server. Make sure a public IP is assigned Static and Private IP assigned static.
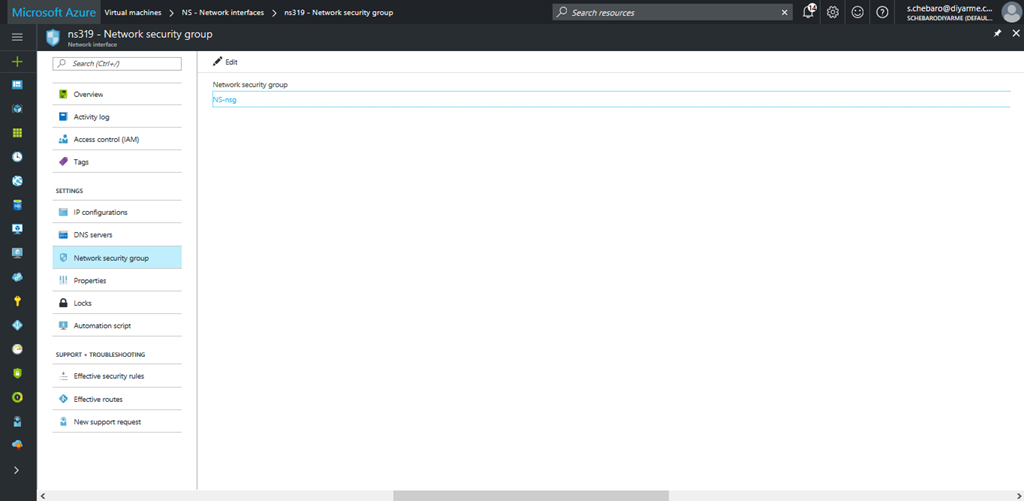
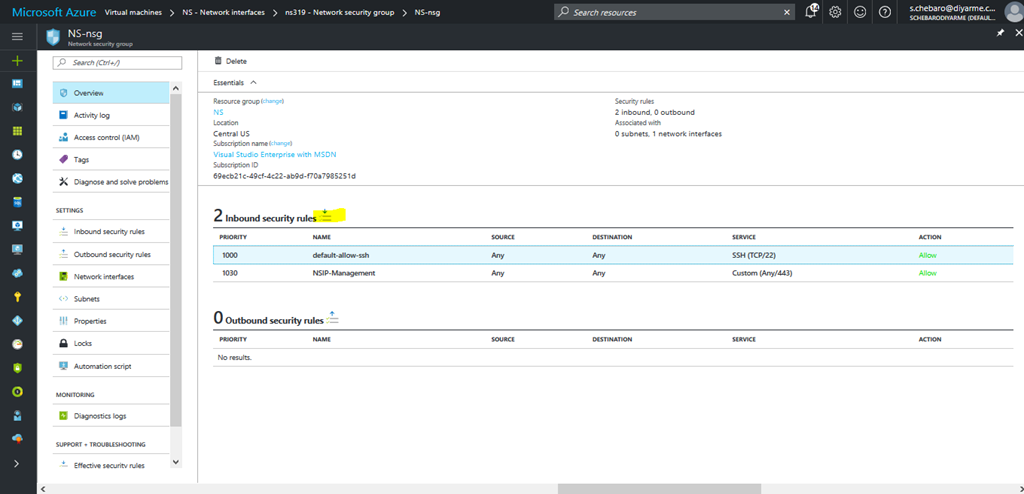
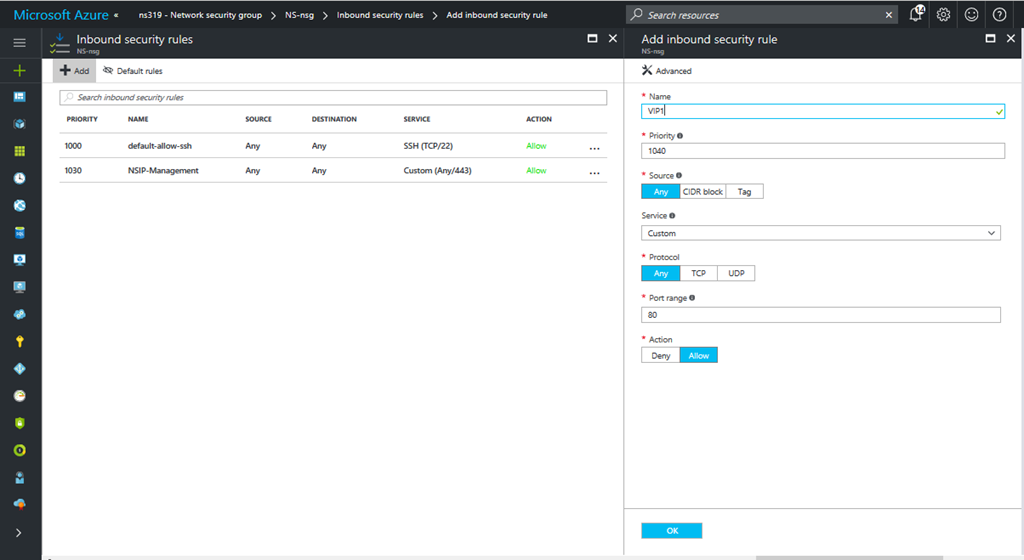
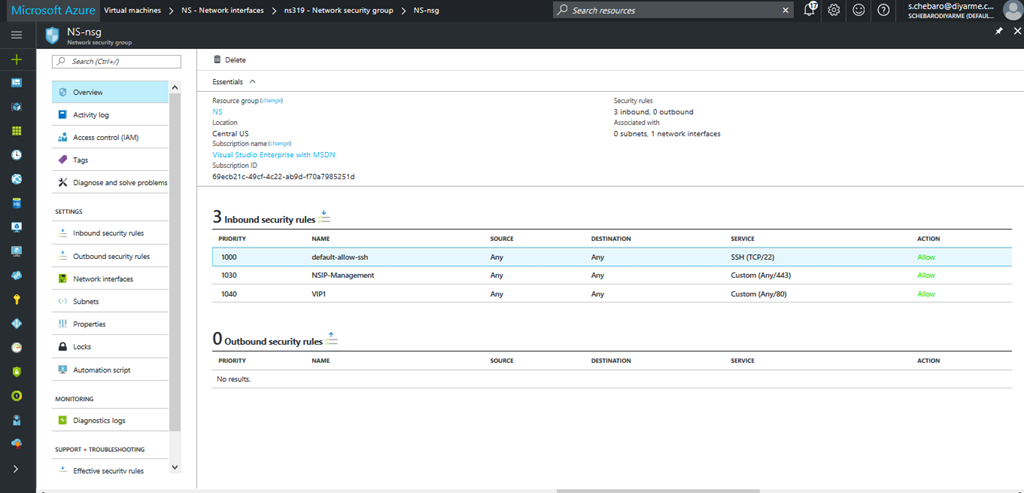
Navigate to Network Security Group and click on NS-nsg. Note that only one NSG can be associated with a NIC even with multiple IPs.
Click the button beside Inbound security rules to add.
Add an inbound allow rule for port HTTP 80 . Remember this will apply to all public IPs on this NIC so be careful on how you design and implement this if only one single NIC with multiple IPs is utilized. If you other services that need to be published, create an inbound rule with the required port to be opened.
Note that by Default, outbound security rules exist to the internet and between virtual networks so that is enough unless you have other restrictive requirements.
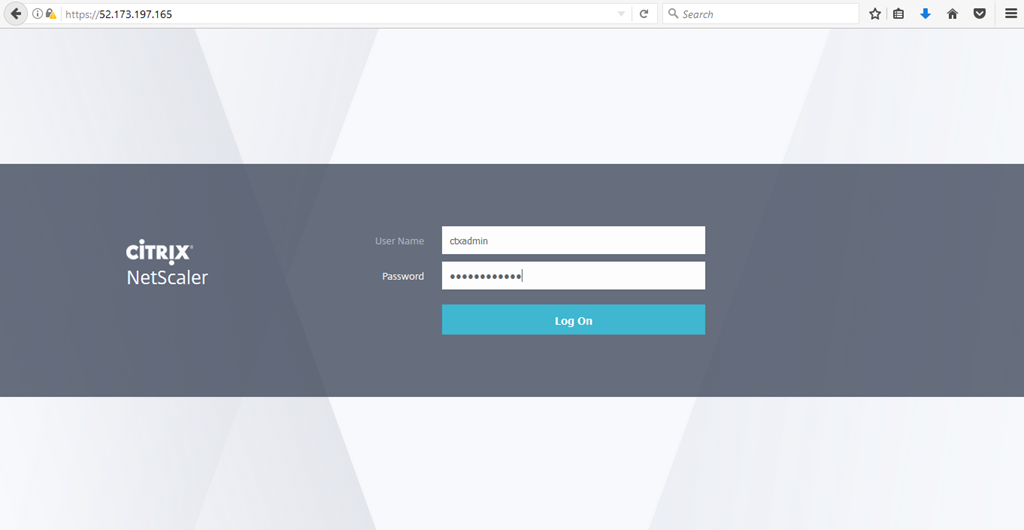
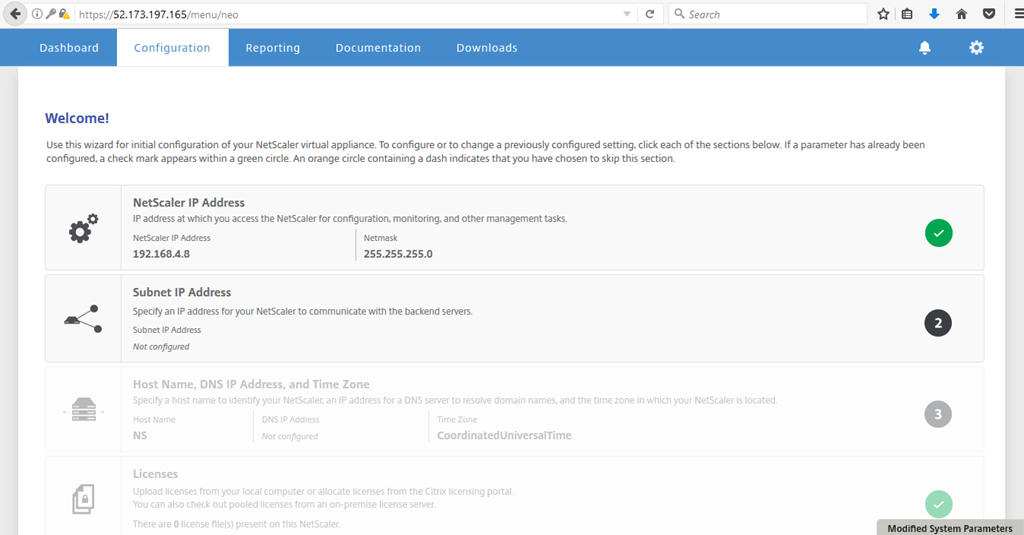
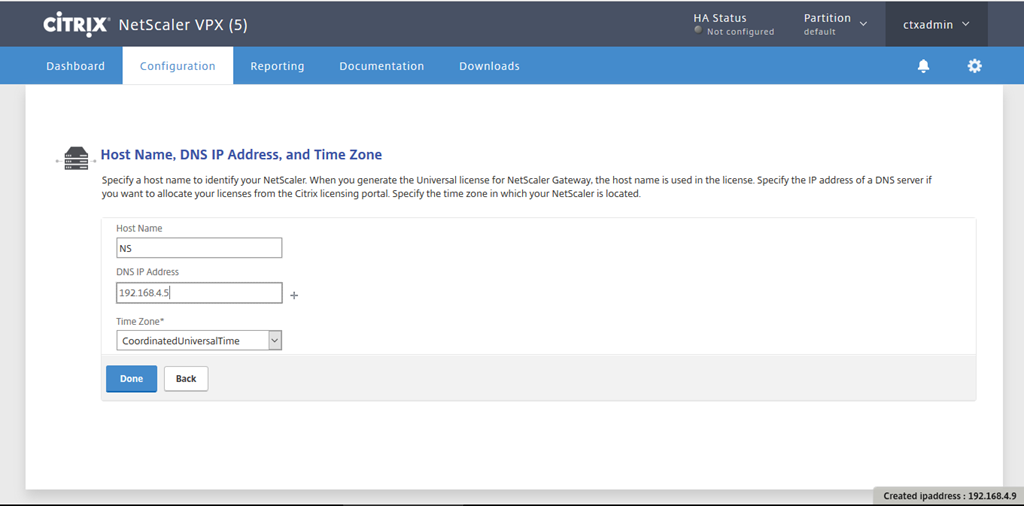
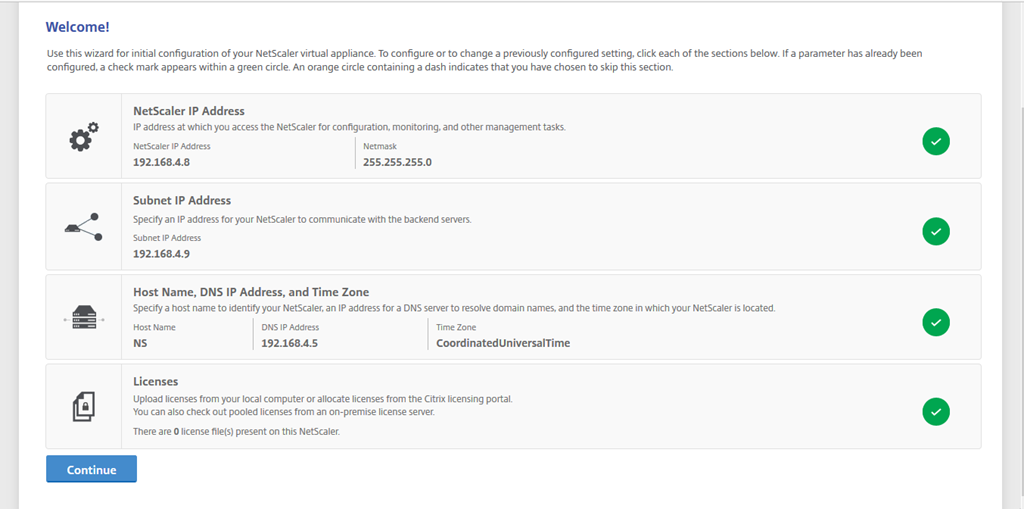
Note the public IP of the NetScaler management IP and browse it. If it is not reachable check the NSG port 443 is open as an inbound rule and source port range is “ * “ which means Any. Also check your virtual network settings and make sure a subnet Gateway is created.
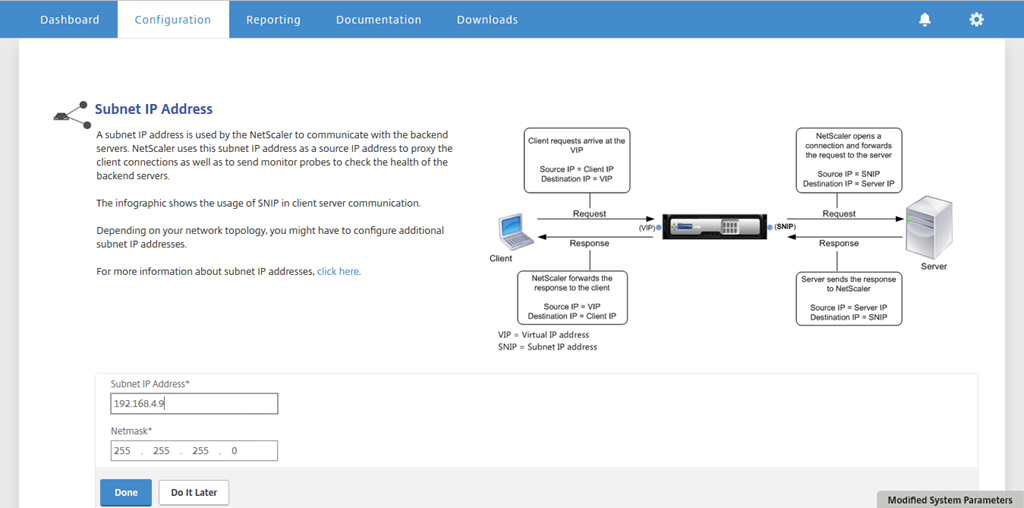
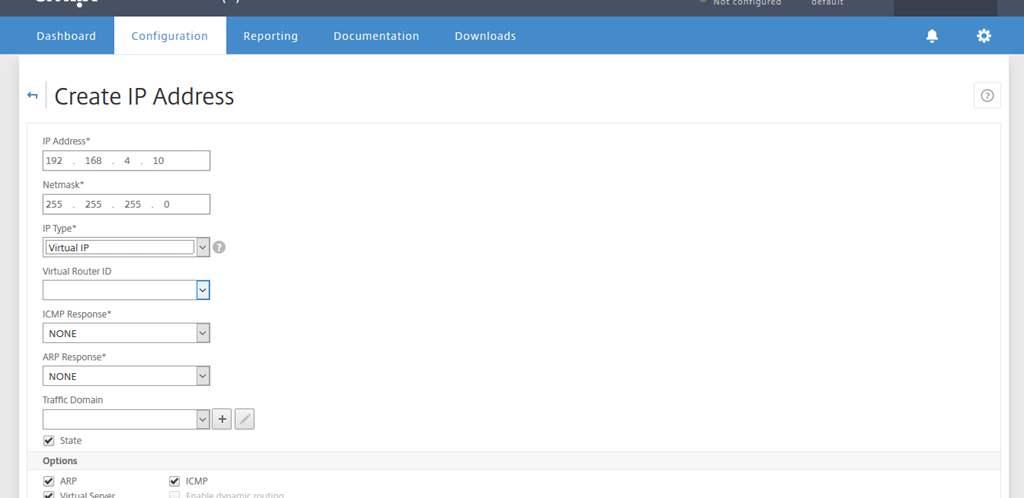
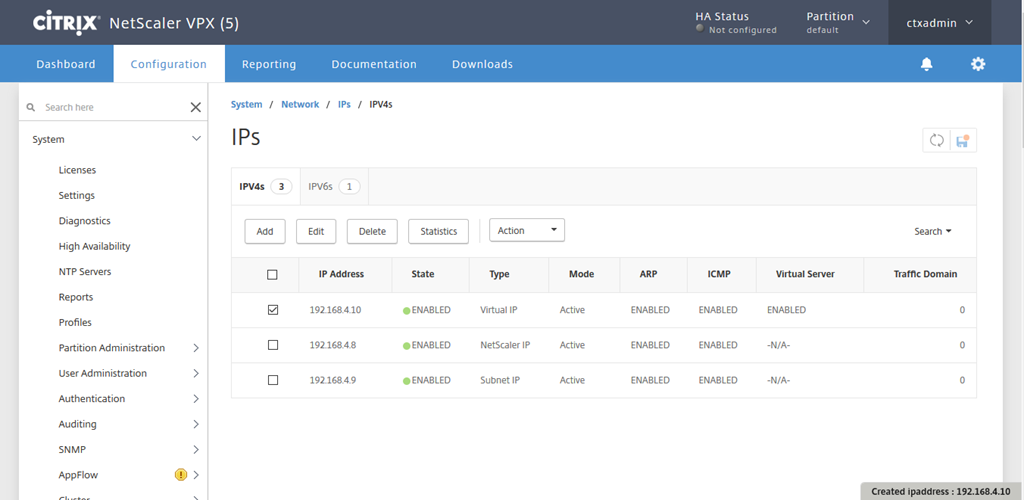
Add a subnet IP which was created earlier.
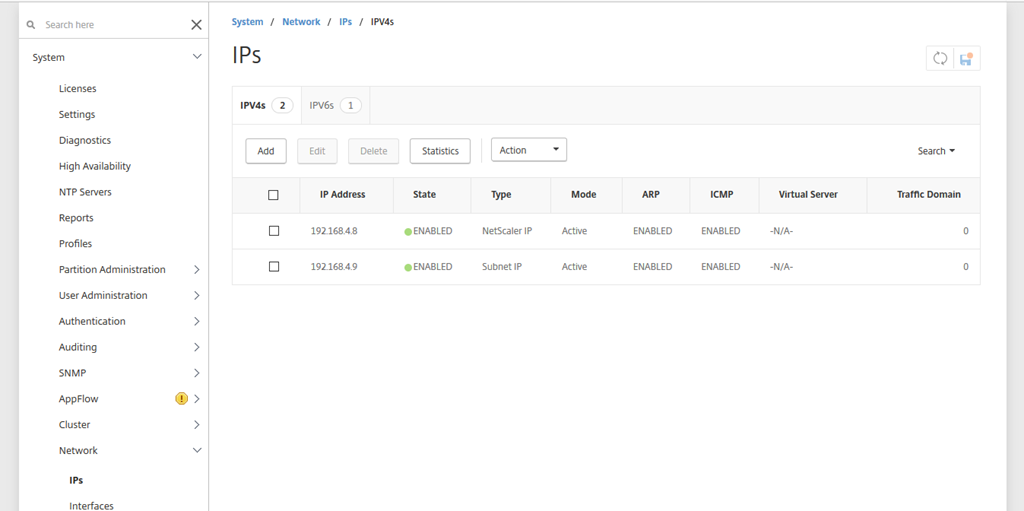
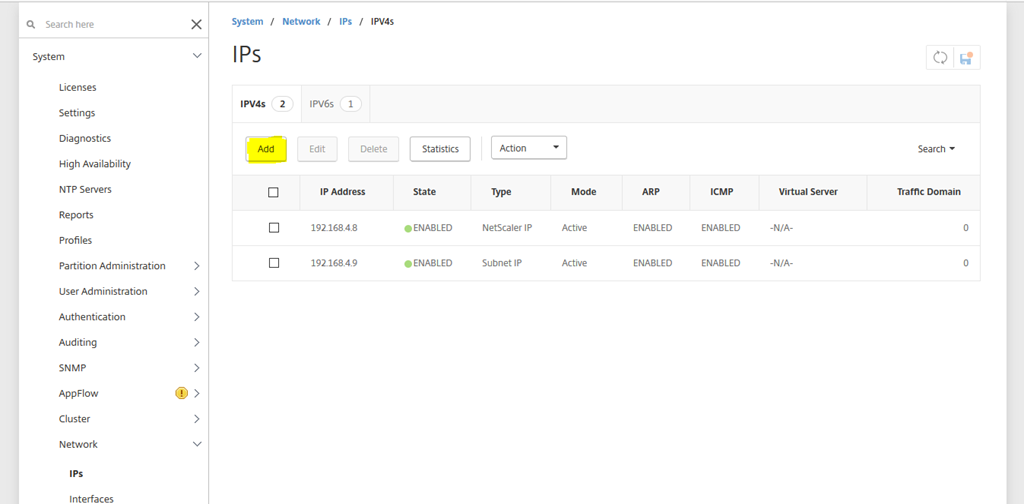
Navigate to Network, IPs and click on Add.
Add the VIP IP that was created earlier and any other secondary created private IPs.
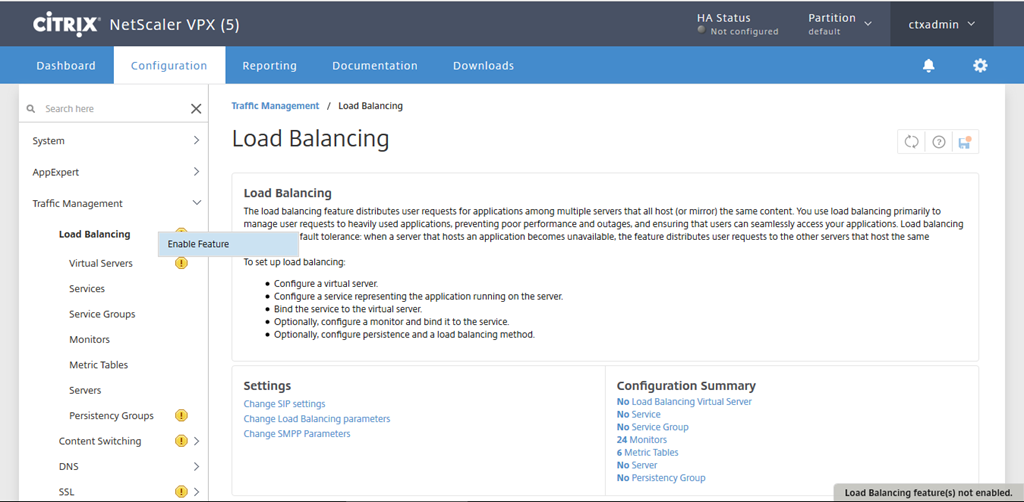
Enable Load Balancing.
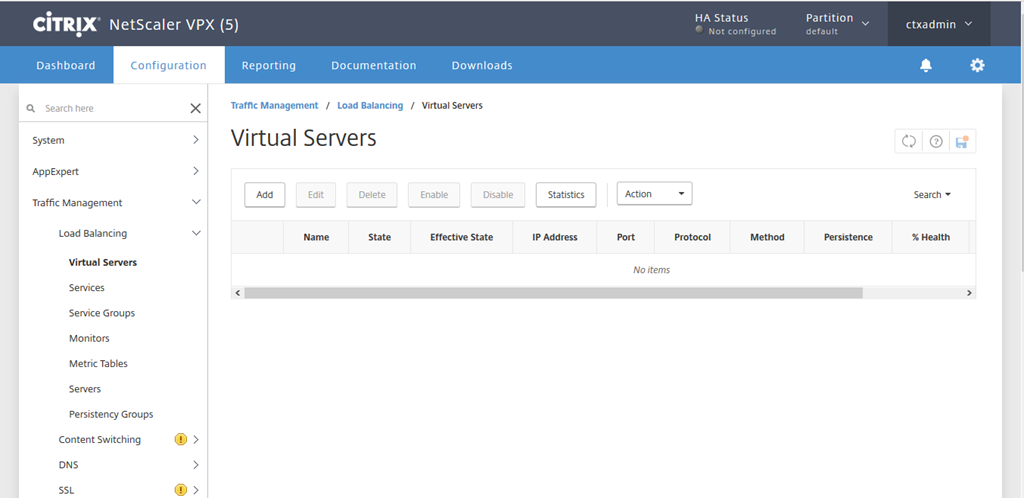
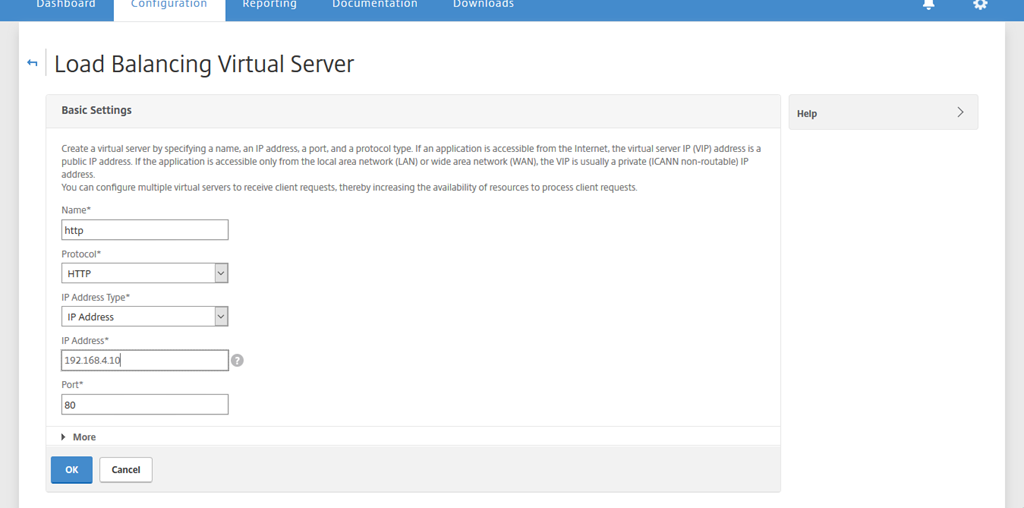
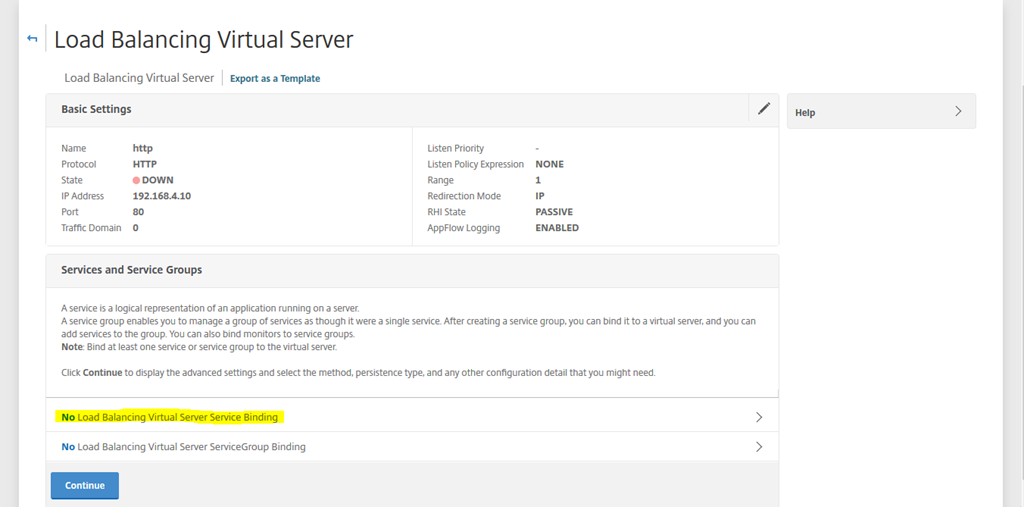
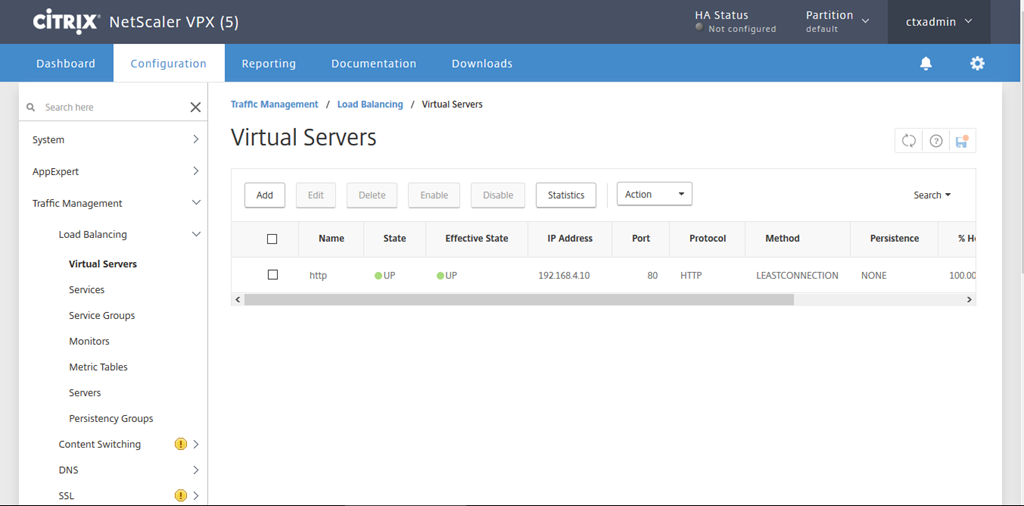
Navigate to Virtual Servers and click on Add. Create an HTTP port 80 Virtual Server using the VIP private IP created and added earlier.
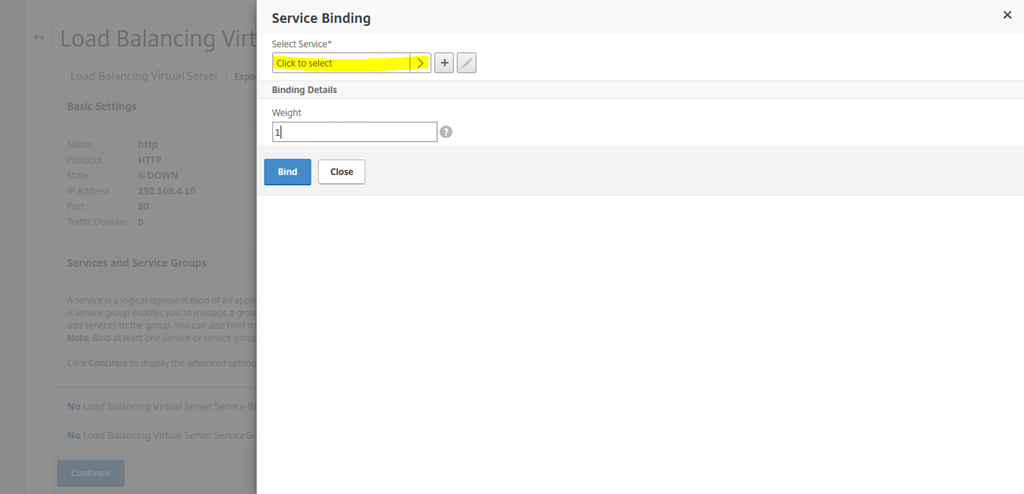
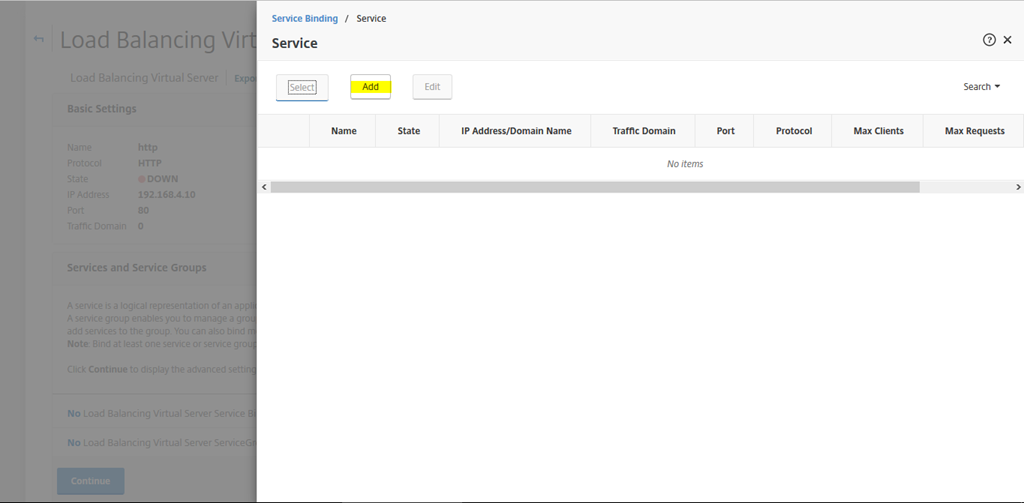
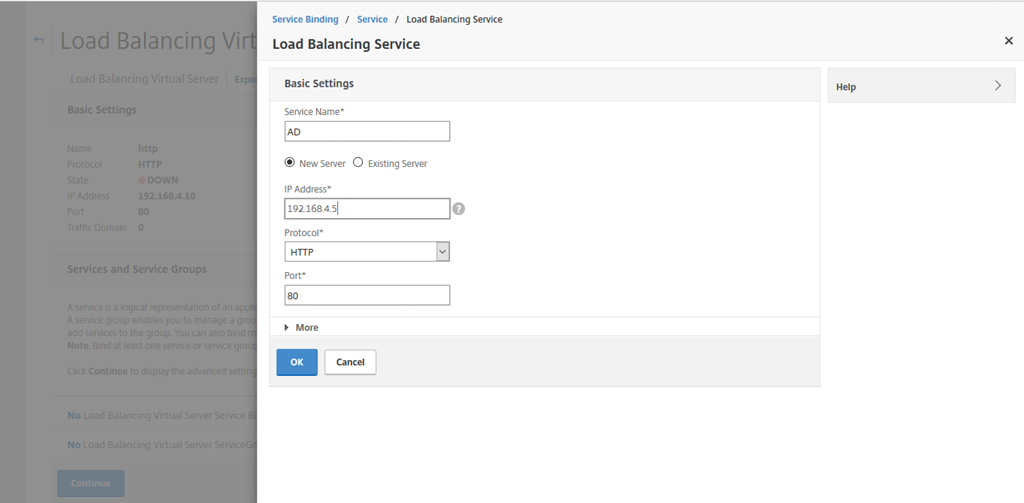
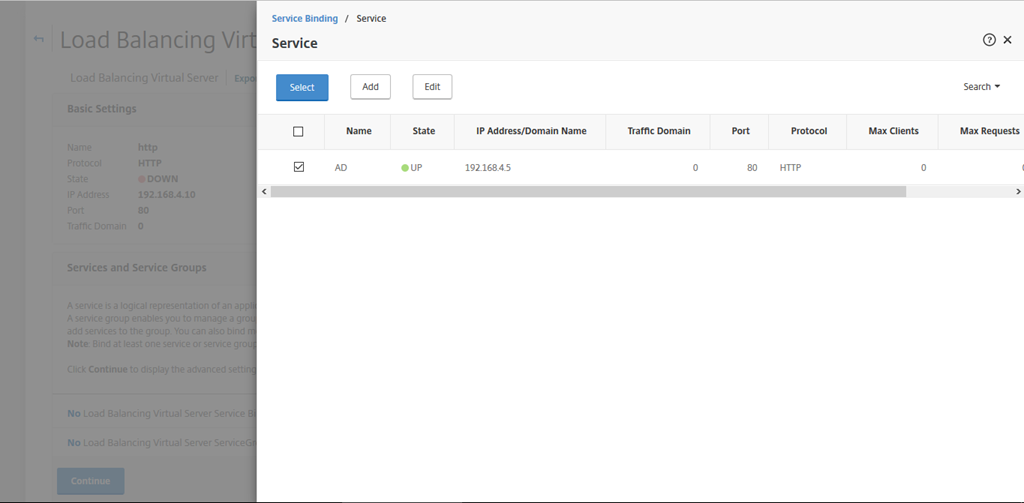
Bind the HTTP server which is hosting an IIS server. Note you can have this on any subnet within the same Azure virtual network.
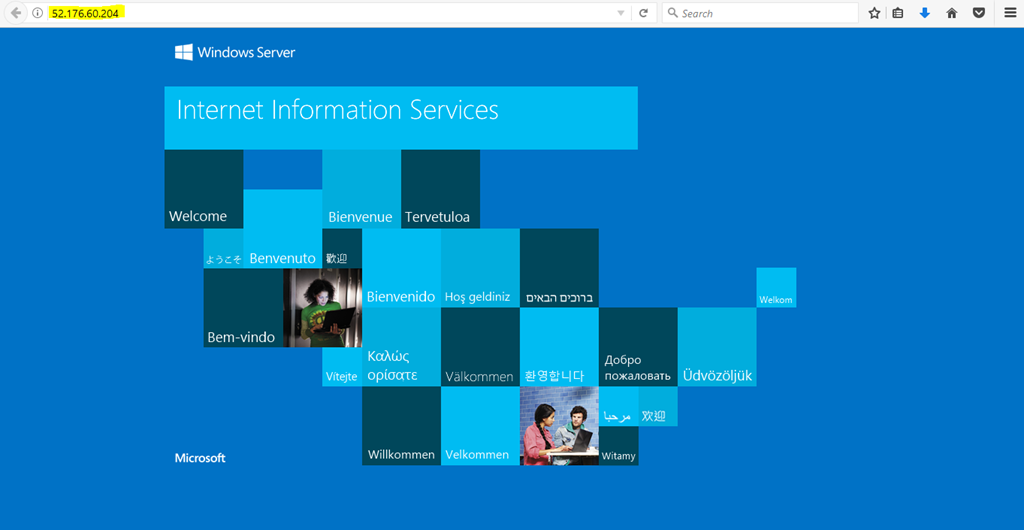
Note the public IP of the VIP and browse it.
Conclusion:
Remember anything added on Microsoft Azure is being charged, that been said this removes a lot of the earlier limitations and configuration hassle involved making it easier to configure NetScaler on Azure and more so supporting different NetScaler roles on the cloud. I will try to post adding a secondary NIC soon.
Citrix NetScaler HA on Microsoft Azure Ultimate Guide
Salam ![]() .
.
Waiting for Netscaler HA configuration with multiple IP 🙂